Tenants Overview
A tenant is a logical container for application policies that enable an administrator to exercise domain-based access control. A tenant represents a unit of isolation from a policy perspective, but it does not represent a private network. Tenants can represent a customer in a service provider setting, an organization or domain in an enterprise setting, or just a convenient grouping of policies.
 Note |
To manage tenants, you must have either |
Three default tenants are pre-configured for you:
-
common—A special tenant with the purpose of providing "common" services to other tenants in ACI fabrics. Global reuse is a core principle in the common tenant. Some examples of common services include shared L3Outs, DNS, DHCP, Active Directory, and shared private networks or bridge domains. -
dcnm-default-tn—A special tenant with the purpose of providing configuration for Cisco NDFC fabrics.When using Nexus Dashboard Orchestrator to manage Cisco DCNM fabrics, you will use the default
dcnm-default-tnthat is preconfigured for you and allows you to create and manage the following objects:-
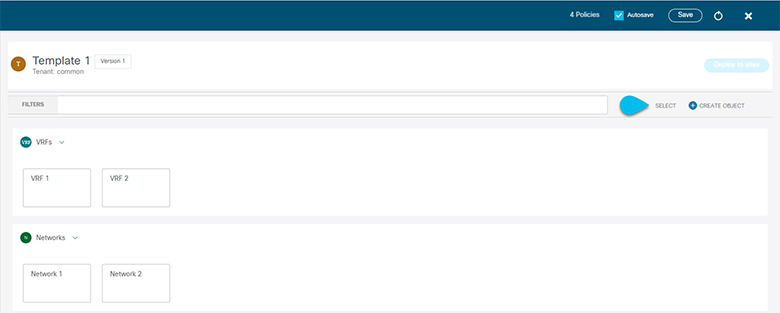
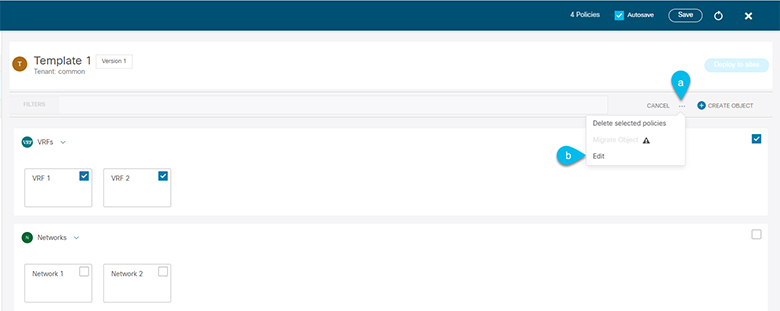
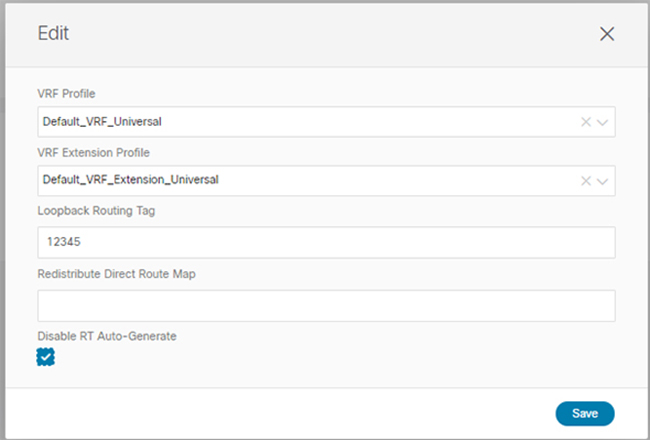
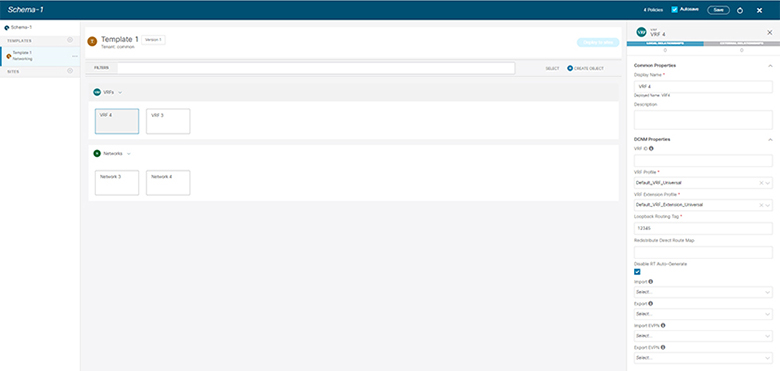
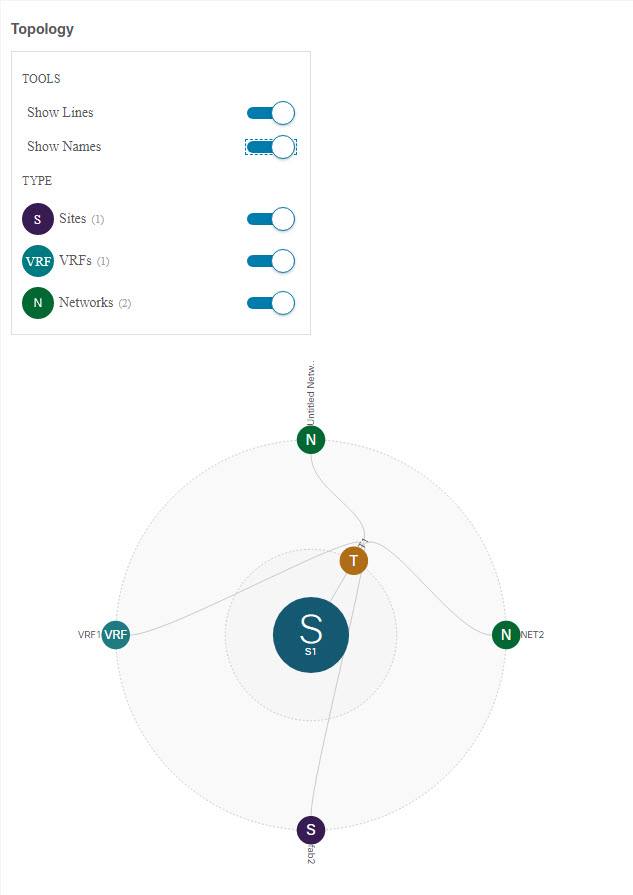
VRFs
-
Networks
-
-
infra—The Infrastructure tenant that is used for all internal fabric communications, such as tunnels and policy deployment. This includes switch to switch and switch to APIC communications. Theinfratenant does not get exposed to the user space (tenants) and it has its own private network space and bridge domains. Fabric discovery, image management, and DHCP for fabric functions are all handled within this tenant.When using Nexus Dashboard Orchestrator to manage Cisco NDFC fabrics, you will always use the default
dcnm-default-tntenant.
Tenant Policies Templates
This section provides a number of tenant templates that are supported for on-premises ACI fabrics managed by Cisco APIC. For additional information, see the Cisco Nexus Dashbaord Orchestrator Configuration Guide for ACI Fabrics.
Add Users to NDFC Tenant
This section describes how to add users to the existing default dcnm-default-tn tenant which you will use when creating schema templates for your NDFC configurations.
Before you begin
You must have a user with either Power User or Site Manager read-write role to manage tenants.
Procedure
|
Step 1 |
Log in to your Nexus Dashboard and open the Nexus Dashboard Orchestrator service. |
||
|
Step 2 |
Select the |
||
|
Step 3 |
Provide tenant details. The tenant's Display Name is used throughout the Orchestrator's GUI whenever the tenant is shown. However, due to object naming requirements on the APIC, any invalid characters are removed and the resulting Internal Name is used when pushing the tenant to sites. The Internal Name that will be used when creating the tenant is displayed below the Display Name textbox.
|
||
|
Step 4 |
Click Save to finish adding the tenant. |

 Feedback
Feedback