|
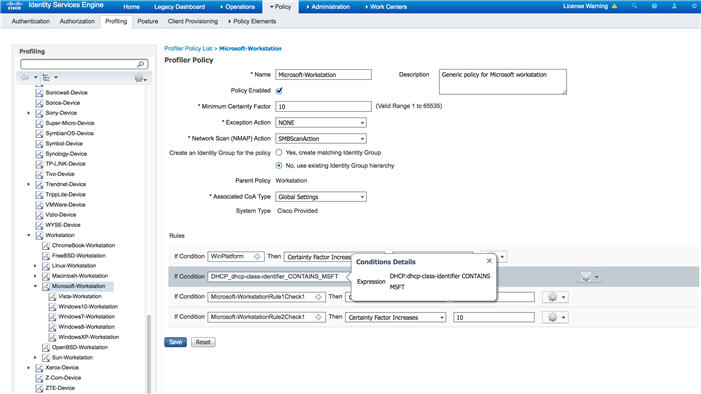
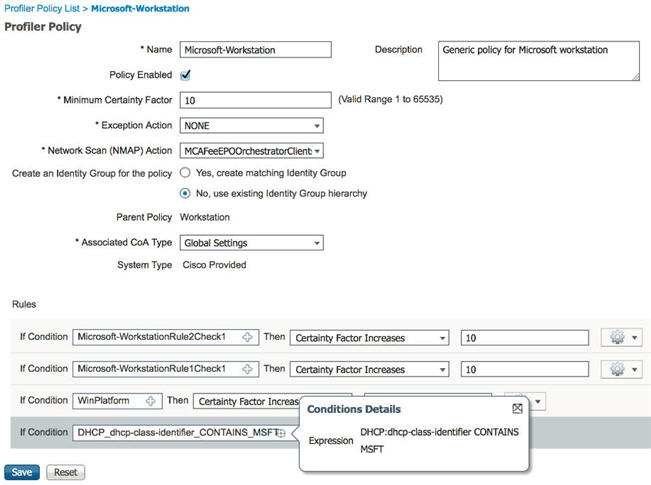
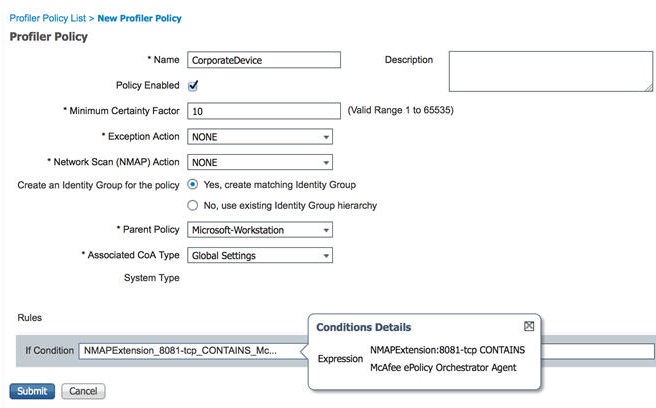
Name
|
Enter the name of the endpoint profiling policy that you want to create.
|
|
Description
|
Enter the description of the endpoint profiling policy that you want to create.
|
|
Policy Enabled
|
By default, the Policy Enabled check box is checked to associate a matching profiling policy when you profile an endpoint.
When unchecked, the endpoint profiling policy is excluded when you profile an endpoint.
|
|
Minimum Certainty Factor
|
Enter the minimum value that you want to associate with the profiling policy. The default value is 10.
|
|
Exception Action
|
Choose an exception action, which you want to associate with the conditions when defining a rule in the profiling policy.
The default is NONE. The exception actions are defined in the following location: Policy > Policy Elements > Results > Profiling > Exception Actions.
|
|
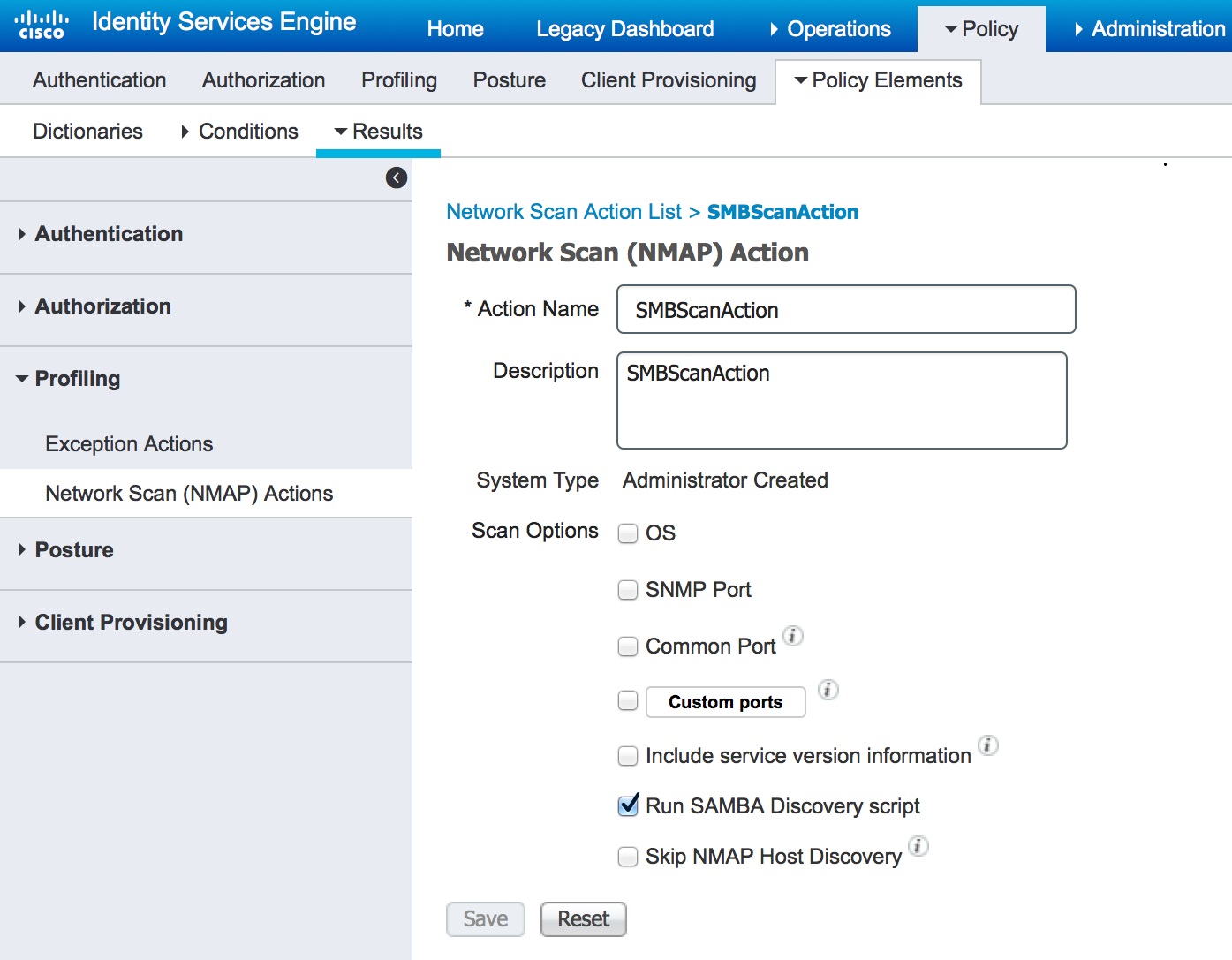
Network Scan (NMAP) Action
|
Choose a network scan action from the list, which you want to associate with the conditions when defining a rule in the profiling
policy, if required.
The default is NONE. The exception actions are defined in the following location: Policy > Policy Elements > Results > Profiling > Network Scan (NMAP) Actions.
|
|
Create an Identity Group for the policy
|
Check one of the following options to create an endpoint identity group:
-
Yes, create matching Identity Group
-
No, use existing Identity Group hierarchy
|
|
Yes, create matching Identity Group
|
Choose this option to use an existing profiling policy.
This option creates a matching identity group for those endpoints and the identity group will be the child of the Profiled
endpoint identity group when an endpoint profile matches an existing profiling policy.
For example, the Xerox-Device endpoint identity group is created in the Endpoints Identity Groups page when endpoints discovered
on your network match the Xerox-Device profile.
|
|
No, use existing Identity Group hierarchy
|
Check this check box to assign endpoints to the matching parent endpoint identity group using hierarchical construction of
profiling policies and identity groups.
This option allows you to make use of the endpoint profiling policies hierarchy to assign endpoints to one of the matching
parent endpoint identity groups, as well as to the associated endpoint identity groups to the parent identity group.
For example, endpoints that match an existing profile are grouped under the appropriate parent endpoint identity group. Here,
endpoints that match the Unknown profile are grouped under Unknown, and endpoints that match an existing profile are grouped
under the Profiled endpoint identity group. For example,
-
If endpoints match the Cisco-IP-Phone profile, then they are grouped under the Cisco-IP-Phone endpoint identity group.
-
If endpoints match the Workstation profile, then they are grouped under the Workstation endpoint identity group.
The Cisco-IP-Phone and Workstation endpoint identity groups are associated to the Profiled endpoint identity group in the
system.
|
|
Parent Policy
|
Choose a parent profiling policy that are defined in the system to which you want to associate the new endpoint profiling
policy.
You can choose a parent profiling policy from which you can inherit rules and conditions to its child.
|
|
Associated CoA Type
|
Choose one of the following CoA types that you want to associate with the endpoint profiling policy:
|
|
Rules
|
One or more rules that are defined in endpoint profiling policies determine the matching profiling policy for endpoints, which
allows you to group endpoints according to their profiles.
One or more profiling conditions from the policy elements library are used in rules for validating endpoint attributes and
their values for the overall classification.
|
|
Conditions
|
Click the plus [+] sign to expand the Conditions anchored overlay, and click the minus [-] sign, or click outside the anchored
overlay to close it.
Click Select Existing Condition from Library or Create New Condition (Advanced Option) .
Select Existing Condition from
Library: You can define an expression by
selecting Cisco predefined conditions from the policy elements
library.
Create New Condition (Advanced
Option): You can define an expression by
selecting attributes from various system or user-defined
dictionaries.
You can associate one of the following with the profiling conditions:
Choose one of the following predefined settings to associate with the profiling condition:
-
Certainty Factor Increases: Enter the certainty value for each rule, which can be added for all the matching rules with respect
to the overall classification.
-
Take Exception Action: Triggers an exception action that is configured in the Exception Action field for this endpoint profiling
policy.
-
Take Network Scan Action: Triggers a network scan action that is configured in the Network Scan (NMAP) Action field for this
endpoint profiling policy.
|
|
Select Existing Condition from Library
|
You can do the following:
-
You can choose Cisco predefined conditions that are available in the policy elements library, and then use an AND or OR operator
to add multiple conditions.
-
Click the Action icon to do the following in the subsequent steps:
-
Add Attribute or Value: You can add ad-hoc attribute or value pairs
-
Add Condition from Library: You can add Cisco predefined conditions
-
Duplicate: Create a copy of the selected condition
-
Add Condition to Library: You can save ad-hoc attribute/value pairs that you create to the policy elements library
-
Delete: Delete the selected condition.
|
|
Create New Condition (Advance Option)
|
You can do the following:
-
You can add ad-hoc attribute/value pairs to your expression, and then use an AND or OR operator to add multiple conditions.
-
Click the Action icon to do the following in the subsequent steps:
-
Add Attribute or Value: You can add ad-hoc attribute or value pairs
-
Add Condition from Library: You can add Cisco predefined conditions
-
Duplicate: Create a copy of the selected condition
-
Add Condition to Library: You can save ad-hoc attribute/value pairs that you create to the policy elements library
-
Delete: Delete the selected condition. You can use the AND or OR operator
|


 from the
from the  Feedback
Feedback