|
Step 1
|
enable
|
Enables privileged EXEC mode.
|
|
Step 2
|
configure
terminal
Router# configure terminal
|
Enters global configuration mode.
|
|
Step 3
|
router
bgp
autonomous-system-number
Router(config)# router bgp 45000
|
Enters router configuration mode for the specified routing process.
|
|
Step 4
|
neighbor
{ip-address |
peer-group-name }
remote-as
autonomous-system-number
Router(config-router)# neighbor 192.168.2.1 remote-as 45000
|
Adds the IP address or peer group name of the neighbor in the specified autonomous system to the IPv4 multiprotocol BGP neighbor
table of the local router.
|
|
Step 5
|
address-family
ipv4
[unicast |
multicast |
vrf
vrf-name ]
Router(config-router)# address-family ipv4 unicast
|
Specifies the IPv4 address family and enters address family configuration mode.
-
The
unicast keyword specifies the IPv4 unicast address family. By default, the router is placed in address family configuration mode
for the IPv4 unicast address family if the
unicast keyword is not specified with the
address-family
ipv4 command.
-
The
multicast keyword specifies IPv4 multicast address prefixes.
-
The
vrf keyword and
vrf-name argument specify the name of the VRF instance to associate with subsequent IPv4 address family configuration mode commands.
|
|
Step 6
|
network
network-number
[mask
network-mask ] [route-map
route-map-name ]
Router(config-router-af)# network 10.2.2.0 mask 255.255.255.0
|
Specifies a network as local to this autonomous system and adds it to the BGP routing table.
|
|
Step 7
|
neighbor
{ip-address |
peer-group-name }
route-map
map-name {in |
out }
Router(config-router-af)# neighbor 192.168.2.1 route-map BLOCK in
Router(config-router-af)# neighbor 192.168.2.1 route-map SETMETRIC1 out
|
Applies a route map to incoming or outgoing routes.
-
In the first example, the route map named BLOCK is applied to inbound routes at Router E.
-
In the second example, the route map named SETMETRIC1 is applied to outbound routes to Router D.
|
Note
|
Two examples are shown here because the task example requires both these statements to be configured.
|
|
|
Step 8
|
Repeat Step 7 to apply another route map to the neighbor specified in Step 7.
|
|
|
Step 9
|
exit
Router(config-router-af)# exit
|
Exits address family configuration mode and enters router configuration mode.
|
|
Step 10
|
neighbor
{ip-address |
peer-group-name }
remote-as
autonomous-system-number
Router(config-router)# neighbor 192.168.3.1 remote-as 45000
|
Adds the IP address or peer group name of the neighbor in the specified autonomous system to the IPv4 multiprotocol BGP neighbor
table of the local router.
|
|
Step 11
|
address-family
ipv4
[unicast |
multicast |
vrf
vrf-name ]
Router(config-router)# address-family ipv4 unicast
|
Specifies the IPv4 address family and enters address family configuration mode.
-
The
unicast keyword specifies the IPv4 unicast address family. By default, the router is placed in address family configuration mode
for the IPv4 unicast address family if the
unicast keyword is not specified with the
address-family
ipv4 command.
-
The
multicast keyword specifies IPv4 multicast address prefixes.
The
vrf keyword and
vrf-name argument specify the name of the VRF instance to associate with subsequent IPv4 address family configuration mode commands.
|
|
Step 12
|
neighbor
{ip-address |
peer-group-name }
route-map
map-name {in |
out }
Router(config-router-af)# neighbor 192.168.3.1 route-map BLOCK in
Router(config-router-af)# neighbor 192.168.3.1 route-map SETMETRIC2 out
|
Applies a route map to incoming or outgoing routes.
-
In the first example, the route map named BLOCK is applied to inbound routes at Router E.
-
In the second example, the route map named SETMETRIC2 is applied to outbound routes to Router D.
|
Note
|
Two examples are shown here because the task example requires both these statements to be configured.
|
|
|
Step 13
|
Repeat Step 10 to apply another route map to the neighbor specified in Step 10.
|
|
|
Step 14
|
exit
Router(config-router-af)# exit
|
Exits address family configuration mode and enters router configuration mode.
|
|
Step 15
|
exit
Router(config-router)# exit
|
Exits router configuration mode and enters global configuration mode.
|
|
Step 16
|
ip
route
prefix
mask
{ip-address |
interface-type
interface-number [ip-address ]} [distance ] [name ] [permanent |
track
number ] [tag
tag ]
Router(config)# ip route 0.0.0.0 0.0.0.0 192.168.2.1 50
Router(config)# ip route 0.0.0.0 0.0.0.0 192.168.2.1 50
Router(config)# ip route 0.0.0.0 0.0.0.0 192.168.3.1 40
|
Establishes a static route.
-
In the first example, a static route to BGP peer 192.168.2.1 is established and given an administrative distance of 50.
-
In the second example, a static route to BGP peer 192.168.3.1 is established and given an administrative distance of 40.
The lower administrative distance makes this route via Router B the preferred route.
|
Note
|
Two examples are shown here because the task example requires both these statements to be configured.
|
|
|
Step 17
|
Repeat Step 14 to establish another static route.
|
|
|
Step 18
|
route-map
map-name
[permit |
deny ] [sequence-number ]
Router(config)# route-map SETMETRIC1 permit 10
|
Configures a route map and enters route map configuration mode.
|
|
Step 19
|
set
metric
value
Router(config-route-map)# set metric 100
|
Sets the MED metric value.
|
|
Step 20
|
exit
Router(config-route-map)# exit
|
Exits route map configuration mode and enters global configuration mode.
|
|
Step 21
|
route-map
map-name
[permit |
deny ] [sequence-number ]
Router(config)# route-map SETMETRIC2 permit 10
|
Configures a route map and enters route map configuration mode.
|
|
Step 22
|
set
metric
value
Router(config-route-map)# set metric 50
|
Sets the MED metric value.
|
|
Step 23
|
exit
Router(config-route-map)# exit
|
Exits route map configuration mode and enters global configuration mode.
|
|
Step 24
|
route-map
map-name
[permit |
deny ] [sequence-number ]
Router(config)# route-map BLOCK deny 10
|
Configures a route map and enters route map configuration mode.
|
|
Step 25
|
end
Router(config-route-map)# end
|
Exits route map configuration mode and enters privileged EXEC mode.
|
|
Step 26
|
show
ip
route
[ip-address ] [mask ] [longer-prefixes ]
|
(Optional) Displays route information from the routing tables.
-
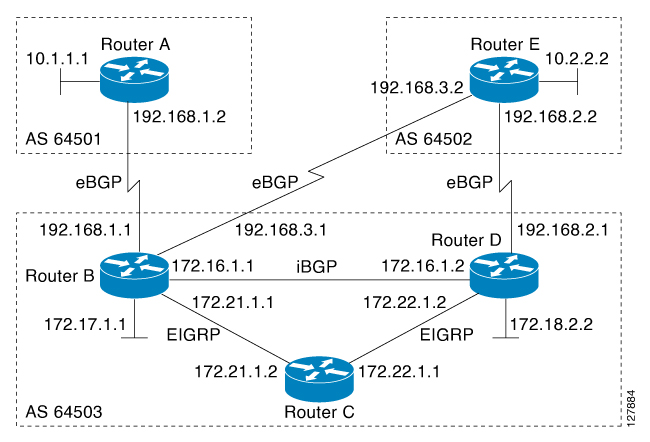
Use this command at Router E in the figure above after Router B and Router D have received update information containing
the MED metric from Router E.
-
Only the syntax applicable to this task is used in this example. For more details, see the
Cisco IOS IP Routing: BGP Command Reference.
|
|
Step 27
|
show
ip
bgp
[network ] [network-mask ]
Router# show ip bgp 172.17.1.0 255.255.255.0
|
(Optional) Displays the entries in the BGP routing table.
-
Use this command at Router E in the figure above after Router B and Router D have received update information containing
the MED metric from Router E.
-
Only the syntax applicable to this task is used in this example. For more details, see the
Cisco IOS IP Routing: BGP Command Reference.
|







 Feedback
Feedback