To display the configuration of Internet Key Exchange Version 2 (IKEv2) cluster policy, use the show crypto ikev2 cluster command in privileged EXEC mode
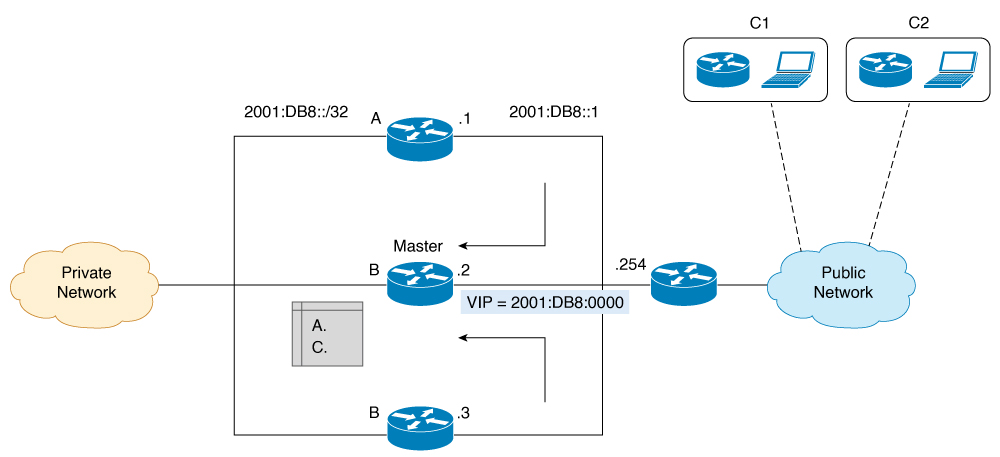
The following is sample output from the show crypto ikev2 cluster command for an HSRP primary gateway:
Device# show crypto ikev2 cluster
Role : CLB Primary
Status : Up
CLB Secondary : 2
Cluster IP : 2001:DB8::10
Hold time : 15000 msec
Overload limit : 80%
Codes : '*' Least loaded, '-' Overloaded
Load statistics:
Gateway Role Last-seen Prio Load IKE FQDN
-------------------------------------------------------------
2001:DB8::1 Primary -- 100 26.6% 3996
2001:DB8::2 Second 00:01.452 100 26.6% 3999
2001:DB8::3 Second 00:00.271 100 26.6% 4006

Note
|
The secondary server shares crypto load and system load details based on the configuration of the update message. These factors
help in identifying an LLG. These details are not static and therefore the load is not distributed equally or in a linear
manner.
|
The following is sample output from the show crypto ikev2 cluster command for an HSRP secondary gateway:
Device# show crypto ikev2 clusterRole : CLB Secondary
Status : Up
Cluster IP : 1:1:1::100
Hold time : 15000 msec
Hello-interval : 5000 msec
Update-interval: 6000 msec
Load statistics:
Gateway Last-Ack Prio Load IKE FQDN
------------------------------------------------------
1:1:1::2 00:02.671 100 51.0% 2793
To display the configuration of Internet Key Exchange Version 2 (IKEv2) cluster policy with additional details, use the show crypto ikev2 cluster details command in privileged EXEC mode.
Device# show crypto ikev2 cluster details
Gateway Priority In-neg Crypto CPU Mem Composite Prioritized
---------------------------------------------------------------------------------------
1:1:1::6 100 2.5% 17.4% 43% 20% 43.0% 43.0%
1:1:1::3 100 0.0% 17.5% 39% 23% 39.0% 39.0%
1:1:1::2 100 0.0% 17.0% 40% 18% 40.0% 40.0%
1:1:1::5 100 0.0% 18.9% 43% 17% 43.0% 43.0%
1:1:1::1 100 0.0% 16.3% 40% 19% 40.0% 40.0%
1:1:1::4 100 0.0% 16.3% 42% 16% 42.0% 42.0%
To display Internet Key Exchange Version 2 (IKEv2) security association (SA) statistics, use the show crypto ikev2 cluster stats command in privileged EXEC mode.
Device# show crypto ikev2 cluster stats
Gateway Priority In-neg Crypto CPU Mem Composite Prioritized
---------------------------------------------------------------------------------------
1:1:1::6 100 2.5% 17.4% 43% 20% 43.0% 43.0%
1:1:1::3 100 0.0% 17.5% 39% 23% 39.0% 39.0%
1:1:1::2 100 0.0% 17.0% 40% 18% 40.0% 40.0%
1:1:1::5 100 0.0% 18.9% 43% 17% 43.0% 43.0%
1:1:1::1 100 0.0% 16.3% 40% 19% 40.0% 40.0%
1:1:1::4 100 0.0% 16.3% 42% 16% 42.0% 42.0%


 Feedback
Feedback