配置並宣告獨立Nexus實現Intersight連線
下載選項
無偏見用語
本產品的文件集力求使用無偏見用語。針對本文件集的目的,無偏見係定義為未根據年齡、身心障礙、性別、種族身分、民族身分、性別傾向、社會經濟地位及交織性表示歧視的用語。由於本產品軟體使用者介面中硬式編碼的語言、根據 RFP 文件使用的語言,或引用第三方產品的語言,因此本文件中可能會出現例外狀況。深入瞭解思科如何使用包容性用語。
關於此翻譯
思科已使用電腦和人工技術翻譯本文件,讓全世界的使用者能夠以自己的語言理解支援內容。請注意,即使是最佳機器翻譯,也不如專業譯者翻譯的內容準確。Cisco Systems, Inc. 對這些翻譯的準確度概不負責,並建議一律查看原始英文文件(提供連結)。
目錄
簡介
本文檔介紹在Intersight中啟用和宣告獨立Nexus交換機以獲得增強型Cisco TAC支援所需的步驟。
必要條件
您必須在Intersight.com上擁有帳戶,Cisco NX-OS®申請無需許可證。如果需要建立新的Intersight帳戶,請參閱帳戶建立。
需求
思科建議您瞭解以下主題:
在獨立的Nexus交換機上,NXDC具有以下準則和限制:
- Cisco NX-OS必須運行版本10.2(3)F或更高版本
- 必須在正確的虛擬路由和轉發(VRF)下配置DNS
svc.intersight.com必須解決並允許在埠443上發起出站的HTTPS連線。可以透過openssl和curl進行檢查。網際網路控制訊息通訊協定(ICMP)要求被忽略。- 如果與
svc.intersight.com的HTTPS連線需要Proxy,可在Nexus交換機裝置聯結器(NXDC)配置中配置Proxy。有關代理配置,請參閱配置NXDC。
採用元件
本文中的資訊係根據以下軟體和硬體版本:
- Cisco Nexus N9K-C93240YC-FX2
- Cisco NX-OS 10.3(4a)M
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路運作中,請確保您瞭解任何指令可能造成的影響。
背景資訊
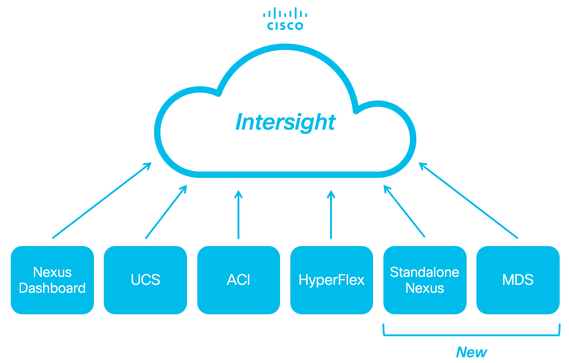
Cisco Intersight是一個雲運營平台,由高級基礎設施、工作負載最佳化和Kubernetes服務的可選模組化功能組成。有關詳細資訊,請訪問Intersight概述。
裝置透過嵌入每個系統的Cisco NX-OS映像中的NXDC連線到Intersight門戶。從Cisco NX-OS版本10.2(3)F開始,支援裝置聯結器功能,該功能為連線的裝置提供了一種安全方式,可使用安全的網際網路連線從Cisco Intersight門戶傳送資訊和接收控制指令。
連線優勢
Intersight連線可為基於Cisco NX-OS的平台提供以下功能和優勢:
- 透過快速問題解決自動收集
show tech-support details(RPR for the TAC Service Requests open) - 遠端按需收集
show tech-support details - 未來的功能包括:
- 根據遙測或硬體故障打開主動式TAC SR
- 單個show命令的遠端按需收集等
快速入門視訊
手動宣告NXOS裝置
連線驗證

注意:Ping響應被抑制(ICMP資料包被丟棄)。
要檢查傳輸層安全性(TLS)和HTTPS連線,請啟用bash並執行 openssl 和 curl 所需VRF中的命令(ip netns exec
建議)。
! Enable bash
config terminal ; feature bash ; end
! Verify TLS
run bash ip netns exec management openssl s_client -connect svc.intersight.com:443
! Verify https
run bash ip netns exec management curl -v -I -L -k https://svc.intersight.com:443
run bash ip netns exec management curl -v -I -L -k https://svc.intersight.com:443 --proxy [protocol://]host[:port]
使用OpenSSL使用者端的TLS驗證
使用OpenSSL,您可以檢查與svc.intersight.com:443的TLS連線。成功後,由伺服器檢索公共簽名證書並顯示證書頒發機構鏈。

注意:下一個示例在VRF管理中執行openssl s_client命令。 取代ip netns exec
建構中所需的。
Switch# run bash ip netns exec management openssl s_client -connect svc.intersight.com:443
CONNECTED(00000004)
depth=2 C = US, O = Amazon, CN = Amazon Root CA 1
verify return:1
depth=1 C = US, O = Amazon, CN = Amazon RSA 2048 M01
verify return:1
depth=0 CN = us-east-1.intersight.com
verify return:1
---
Certificate chain
0 s:CN = us-east-1.intersight.com
i:C = US, O = Amazon, CN = Amazon RSA 2048 M01
1 s:C = US, O = Amazon, CN = Amazon RSA 2048 M01
i:C = US, O = Amazon, CN = Amazon Root CA 1
2 s:C = US, O = Amazon, CN = Amazon Root CA 1
i:C = US, ST = Arizona, L = Scottsdale, O = "Starfield Technologies, Inc.", CN = Starfield Services Root Certificate Authority - G2
3 s:C = US, ST = Arizona, L = Scottsdale, O = "Starfield Technologies, Inc.", CN = Starfield Services Root Certificate Authority - G2
i:C = US, O = "Starfield Technologies, Inc.", OU = Starfield Class 2 Certification Authority
---
Server certificate
-----BEGIN CERTIFICATE-----
MIIGfzCCBWegAwIBAgIQD859tBjpT+QUyVOXqkG2pzANBgkqhkiG9w0BAQsFADA8
MoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0Kg
UlNBIDIwNDggTTAxMB4XDTIzMDQwNTAwMDAwMFoXDTI0MDUwMzIzNTk1OVowIzEh
MB8GA1UEAxMYdXMtZWFzdC0xLmludGVyc2lnaHQuY29tMIIBIjANBgkqhkiG9w0B
AoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0Kn
BDM+MCNnvmgNDlGnU6/t1jOC780QpKXr2ksbGC0FzHfMvNjEk9kMCUe179dummrs
pOOFzvIrJGqYvkIXT5WLtiU9aP3+VSEWQO1kTeDHoDfLLJLON42cKjskYt0jCTwE
poKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0KI
elf3tYBhuQK3y4DoSqg1/gptnUOlNwSqMu4zXjI7neGyHnzjsPUyI8qilXbPS9tV
KoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0Kw
HwYDVR0jBBgwFoAUgbgOY4qJEhjl+js7UJWf5uWQE4UwHQYDVR0OBBYEFM7X7s7c
NoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0Kp
Z2h0LmNvbYIac3ZjLXN0YXRpYzEuaW50ZXJzaWdodC5jb22CGioudXMtZWFzdC0x
LoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0K1
Y3MtY29ubmVjdC5jb22CE3N2Yy51Y3MtY29ubmVjdC5jb22CDmludGVyc2lnaHQu
Y29tghJzdmMuaW50ZXJzaWdodC5jb20wDgYDVR0PAQH/BAQDAgWgMB0GA1UdJQQW
MBQGCCsGAQUFBwMBBggrBgEFBQcDAjA7BgNVHR8ENDAyMDCgLqAshipodHRwOi8v
YoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0KI
BgZngQwBAgEwdQYIKwYBBQUHAQEEaTBnMC0GCCsGAQUFBzABhiFodHRwOi8vb2Nz
coKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0Ku
cjJtMDEuYW1hem9udHJ1c3QuY29tL3IybTAxLmNlcjAMBgNVHRMBAf8EAjAAMIIB
fgYKKwYBBAHWeQIEAgSCAW4EggFqAWgAdwDuzdBk1dsazsVct520zROiModGfLzs
3oKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0K5
CSFqTpBjlOdOLQ4YuQIhAO10VDrLJMM+9EtOwmZd8Q1MRHJlOlr2VWmOTF6GGkCV
AHUAc9meiRtMlnigIH1HneayxhzQUV5xGSqMa4AQesF3crUAAAGHUp9iOwAABAMA
RjBEAiAFPPLvt7TN7mTRnQZ+FZLGR/G04KQqSjYuszDNPArT3wIgf/sQbQqNjCk7
joFUuL9cEPYfNm7n1nZIFIRAK6UqwG0AdgBIsONr2qZHNA/lagL6nTDrHFIBy1bd
LoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0K8
MXtts5t/C5lYw5peGAIgK0eFmxTptEfMkBZti39vepUxb5meDvKaZdtXVvFpkCMw
DQYJKoZIhvcNAQELBQADggEBANl6HKZ9P6AIufr7qdNCcW+DXClY6dqX1KN0sCh+
UoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0KM
z5R1VV+81gN2HHiuUsEOFwHDbbhiGBJiJteFm0blpruKHennx8HQYfC7bup4N5JH
YoKXXrXrkESkWgbQadlEo3H545Zsix+mu83r7Gmv5L3+WFKzfUmLgeB2+z1Dk0Kb
LKFl6c+EN0Y76YaCV8doujG3qD/bO9VDx7dhvbSEECYuzbYyPDGnb7Drmhny0Eki
smLUZ3TVcCvPc+1dE/jrbBzPeIY7jGr8eL7masFCuZZn2lM=
-----END CERTIFICATE-----
subject=CN = us-east-1.intersight.com
issuer=C = US, O = Amazon, CN = Amazon RSA 2048 M01
---
No client certificate CA names sent
Peer signing digest: SHA256
Peer signature type: RSA
Server Temp Key: ECDH, P-256, 256 bits
---
SSL handshake has read 5754 bytes and written 442 bytes
Verification: OK
---
New, TLSv1.2, Cipher is ECDHE-RSA-AES128-GCM-SHA256
Server public key is 2048 bit
Secure Renegotiation IS supported
Compression: NONE
Expansion: NONE
No ALPN negotiated
SSL-Session:
Protocol : TLSv1.2
Cipher : ECDHE-RSA-AES128-GCM-SHA256
Session-ID: 66D0B69FAA7EB69FAA7EC54C9764966ED9A1289650B69FAA7EB69FAA7E9A5FD5ADE
Session-ID-ctx:
Master-Key: B69FAA7E45891555D83DFCAEB69FAA7EB69FAA7EA3A99E7689ACFB69FAA7EAD7FD93DB69FAA7EB1AF821
PSK identity: None
PSK identity hint: None
SRP username: None
TLS session ticket lifetime hint: 86400 (seconds)
TLS session ticket:
0000 - 36 12 b2 36 b3 53 07 29-54 ac 56 f0 06 83 4f b1 6..6.S.)T.V...O.
0010 - 49 35 51 40 22 07 bd 7e-59 d7 7e 44 29 ff c6 2a I5Q@"..~Y.~D)..*
0020 - ec bc 11 e1 d3 5d 69 e8-7a d2 f1 c2 08 f6 5b 8f .....]i.z.....[.
0030 - 2c 5b 5e 50 e3 e2 8f e7-c4 44 8f e4 6d 45 d2 64 ,[^P.....D..mE.d
0040 - 93 98 f5 e8 b0 f7 1d 00-26 4b 88 ea 2d 7d 42 58 ........&K..-}BX
0050 - 05 9f 71 3a fe ac f0 15-a5 5c 1d 74 74 bf 32 1b ..q:.....\.tt.2.
0060 - d8 a8 23 84 08 cc f9 3e-54 ..#....>T
Start Time: 1707515659
Timeout : 7200 (sec)
Verify return code: 0 (ok)
Extended master secret: yes
---
HTTPS可達性驗證
要檢查HTTPS連線,請將curl命令與-v verbose flag(顯示是否使用Proxy)一起使用。

附註:若要檢查啟用或停用Proxy的影響,您可以新增選項--proxy [protocol://]host[:port]或--noproxy [protocol://]host[:port]。
該構造ip netns exec
用於執行所需VRF中的捲曲;例如,用於VRF管理的ip netns exec management。
run bash ip netns exec management curl -v -I -L -k https://svc.intersight.com:443
run bash ip netns exec management curl -v -I -L -k https://svc.intersight.com:443 --proxy [protocol://]host[:port]
# run bash ip netns exec management curl -v -I -L -X POST https://svc.intersight.com:443 --proxy http://proxy.esl.cisco.com:80Connected to proxy.esl.cisco.com (10.201.255.40) port 80
Trying 10.201.255.40:80... ** CONNECT tunnel: HTTP/1.1 negotiated * allocate connect buffer * Establish HTTP proxy tunnel to svc.intersight.com:443 > CONNECT svc.intersight.com:443 HTTP/1.1 > Host: svc.intersight.com:443 > User-Agent: curl/8.4.0 > Proxy-Connection: Keep-Alive >< HTTP/1.1 200 Connection establishedHTTP/1.1 200 Connection established < snip >
設定
宣告裝置位於 intersight.com
為了在Intersight中宣告一個新目標,請完成上述步驟。
在Nexus裝置上
發出Cisco NX-OS命令show system device-connector claim-info。

注意:對於NX-OS 10.3(4a)之前的版本,請使用「show intersight claim-info」命令

注意:Nexus生成的宣告資訊對映到以下Intersight宣告欄位:
序列號= Intersight宣告ID
Device-ID安全令牌= Intersight 領款申請代碼
# show system device-connector claim-info
SerialNumber: FDO23021ZUJ
SecurityToken: 9FFD4FA94DCD
Duration: 599
Message:
Claim state: Not Claimed此處報告的Duration以秒為單位。
在Intersight門戶上

註:注意:Cisco Intersight裝置宣告功能在EMEA地區不可用。這些步驟僅適用於北美地區。
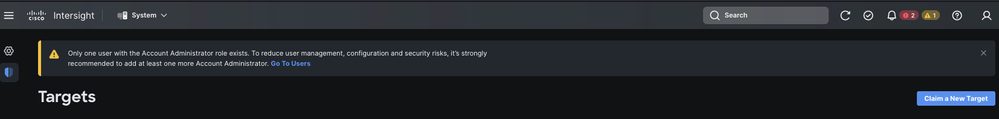
1. 在10分鐘內以「帳戶管理員」、「裝置管理員」或「裝置技術人員」許可權登入Intersight。
2. 從Service Selector下拉選單中選擇System。
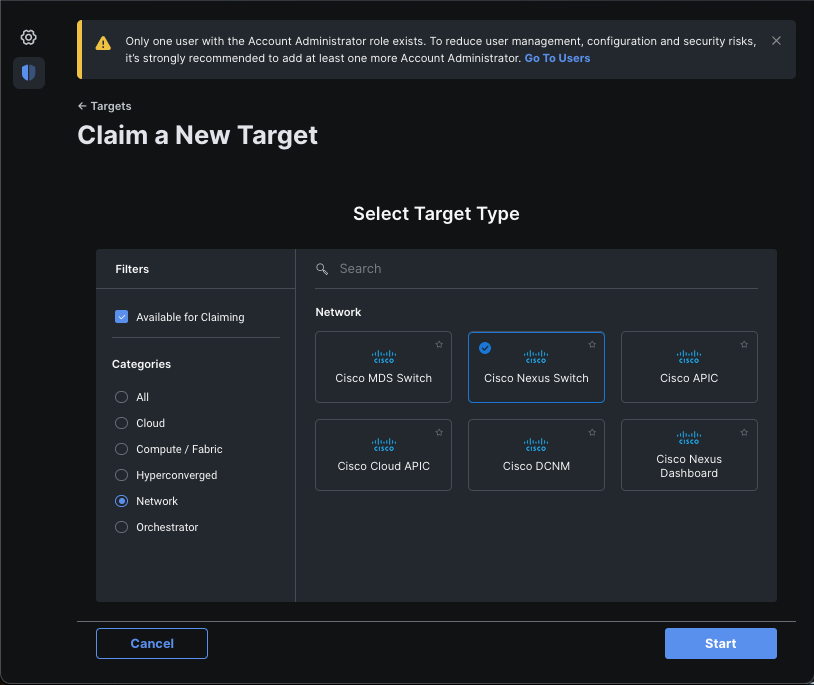
3. 定位至ADMIN > Targets > Claim a New Target。
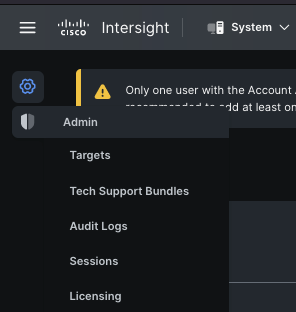
3.1.按一下宣告新目標,如圖所示。
4. 選擇可用於申請,並選擇要申請的目標型別(例如,網路)。按一下Start。
5. 輸入所需的詳細資訊,然後按一下索賠以完成索賠流程。

註:交換機上的安全令牌用作宣告代碼,交換機的序列號為裝置ID。

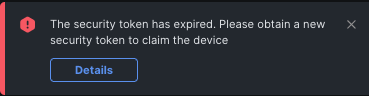
注意:安全令牌過期。您必須在之前完成宣告,否則系統會提示您重新產生宣告。
使用Ansight在intersight.com中宣告一對多獨立式Nexus裝置®
要聲稱是一對多Nexus裝置,可以運行Ansible手冊。
- 可以從https://github.com/datacenter/ansible-intersight-nxos克隆ansible資產和攻略。
- 在Ansible
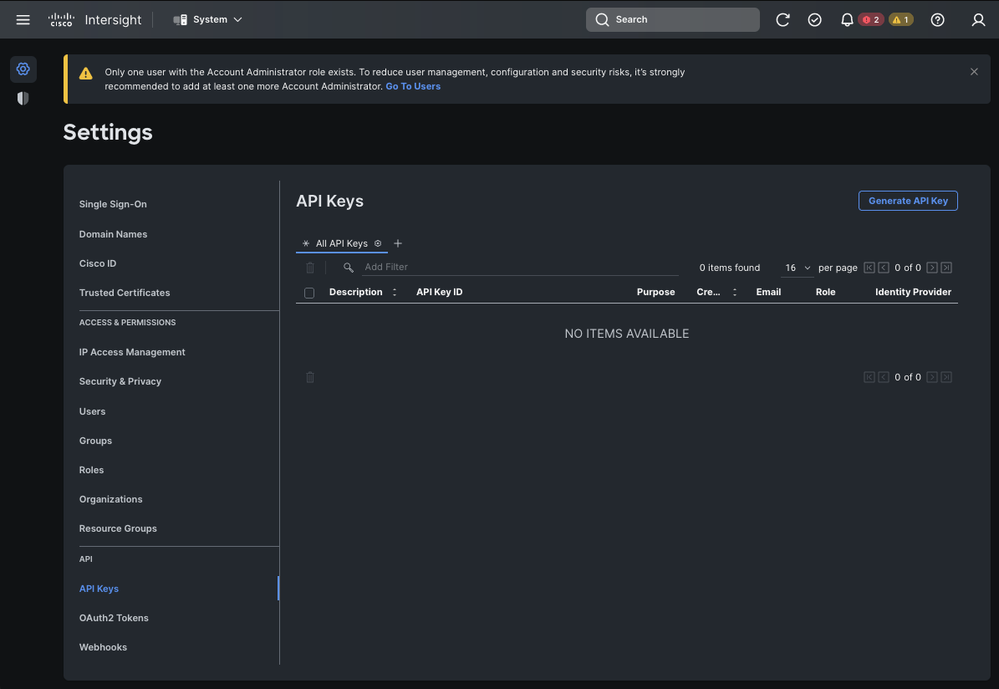
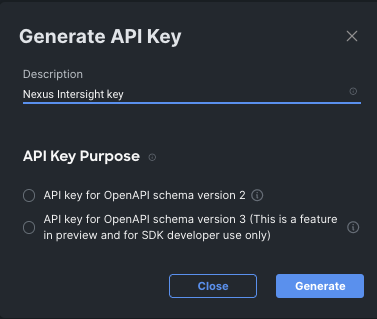
inventory.yaml中,ansible_connection型別設定為ansible.netcommon.network_cli,以便向Nexus交換機傳送命令。可以將其更改為ansible.netcommon.httpapi,以便透過NXAPI進行連線。 - 要連線到Intersight終結點,需要一個API金鑰,該金鑰可透過您的intersight.com帳戶生成。
配置Nexus NXAPI(僅在使用ansible.netcommon.httpapi時使用)

注意:如果配置了系統級代理(HTTP(S)_PROXY),並且Ansible不能使用代理來連線Nexus NXAPI終結點,則需要設定ansible_httpapi_use_proxy: False(預設為True)。
# configure terminal
# cfeature nxapi
# nxapi port 80
# no nxapi https port 443
# end
# show nxapi
nxapi enabled
NXAPI timeout 10
NXAPI cmd timeout 300
HTTP Listen on port 80
HTTPS Listen on port 443
Certificate Information:
Issuer: issuer=C = US, ST = CA, L = San Jose, O = Cisco Systems Inc., OU = dcnxos, CN = nxos
Expires: Feb 10 22:30:38 2024 GMT
要獨立驗證到NXAPI終端的HTTP連線,可以嘗試傳送show clock。在下一個示例中,交換機使用基本身份驗證對客戶端進行身份驗證。也可以配置NXAPI伺服器,以便根據X.509使用者證書對客戶端進行身份驗證。

注意:基本身份驗證雜湊透過username:password的base64編碼獲得。在本示例中,admin:cisco!123 base64編碼為YWRtaW46Y2lzY28hMTIz。
curl -v --noproxy '*' \
--location 'http://10.1.1.3:80/ins' \
--header 'Content-Type: application/json' \
--header 'Authorization: Basic YWRtaW46Y2lzY28hMTIz' \
--data '{
"ins_api": {
"version": "1.0",
"type": "cli_show",
"chunk": "0",
"sid": "sid",
"input": "show clock",
"output_format": "json"
}
}'
捲曲回應:
* Trying 10.1.1.3...
* TCP_NODELAY set
* Connected to 10.1.1.3 (10.1.1.3) port 80 (#0)
> POST /ins HTTP/1.1
> Host: 10.1.1.3
> User-Agent: curl/7.61.1
> Accept: */*
> Content-Type: application/json
> Authorization: Basic YWRtaW56Y2lzY28hBNIz
> Content-Length: 297
>
* upload completely sent off: 297 out of 297 bytes
< HTTP/1.1 200 OK
< Server: nginx/1.19.6
< Date: Fri, 09 Feb 2024 23:17:10 GMT
< Content-Type: text/json; charset=UTF-8
< Transfer-Encoding: chunked
< Connection: keep-alive
< Set-Cookie: nxapi_auth=dzqnf:xRYwR0l1Tra64VfOMVuD4oI4=; Secure; HttpOnly;
< anticsrf: /i3vzCvxhOr4w2IrKP+umbDnzHQ=
< Strict-Transport-Security: max-age=31536000; includeSubDomains
< X-Frame-Options: SAMEORIGIN
< X-Content-Type-Options: nosniff
< Content-Security-Policy: block-all-mixed-content; base-uri 'self'; default-src 'self'; script-src 'self' 'nonce-zHx12KP1tervan1s6lrFQz7N6PF0rh'; style-src 'self' 'nonce-zHx12KP1tervan1s6lrFQz7N6P40rh'; img-src 'self'; connect-src 'self'; font-src 'self'; object-src 'self'; media-src 'self'; form-action 'self'; frame-ancestors 'self';
<
{
"ins_api": {
"type": "cli_show",
"version": "1.0",
"sid": "eoc",
"outputs": {
"output": {
"input": "show clock",
"msg": "Success",
"code": "200",
"body": {
"simple_time": "23:17:10.814 UTC Fri Feb 09 2024\n",
"time_source": "NTP"
}
}
}
}
* Connection #0 to host 10.1.1.3 left intact
}%
產生Intersight API金鑰
有關如何從Intersight System > Settings > API keys > Generate API Key獲取API金鑰,請參閱README.md部分。
範例:Ansible inventory.yaml

注意:在下一個示例中,對ansible進行了配置,以便使用ansible_httpapi_use_proxy: False忽略作業系統代理設定。如果您需要Ansible伺服器使用代理才能連線到交換器,可以移除該組態或將其設定為True (預設值)。

注意:API金鑰ID是一個字串。API私鑰包含指向包含私鑰的檔案的完整路徑。對於生產環境,建議使用Ansible保管庫。
---
all:
hosts:
switch1:
ansible_host: "10.1.1.3"
intersight_src: "mgmt0"
intersight_vrf: "management"
vars:
ansible_user: "admin"
ansible_password: "cisco!123"
ansible_connection: ansible.netcommon.network_cli
ansible_network_os: cisco.nxos.nxos
ansible_httpapi_use_proxy: False
remote_tmp: "/bootflash"
proxy_env:
- no_proxy: "10.1.1.3/24"
intersight_proxy_host: 'proxy.cisco.com'
intersight_proxy_port: '80'
api_key_id: "5fcb99d97564612d33fdfcal/5fcb99d97564612d33fdf1b2/65c6c09d756461330198ce7e"
api_private_key: "/home/admin/ansible-intersight-nxos/my_intersight_private_key.txt"
...
範例:執行playbook.yaml
有關使用Ansible對獨立Nexus裝置進行程式設計的詳細資訊,請參閱適用於當前版本的Cisco Nexus 9000系列NX-OS可程式設計性指南使用Cisco NX-OS的Applications/Using Ansible部分。
❯ ansible-playbook -i inventory.yaml playbook.yaml
PLAY [all] *********************************************************************************************************************************************************
TASK [Enable feature intersight] ***********************************************************************************************************************************
[WARNING]: To ensure idempotency and correct diff the input configuration lines should be similar to how they appear if present in the running configuration on
device
changed: [switch1]
TASK [Configure proxy] *********************************************************************************************************************************************
ok: [switch1]
TASK [Unconfigure proxy] *******************************************************************************************************************************************
skipping: [switch1]
TASK [Configure src interface] *************************************************************************************************************************************
ok: [switch1]
TASK [Unconfigure src interface] ***********************************************************************************************************************************
skipping: [switch1]
TASK [Configure src vrf] *******************************************************************************************************************************************
ok: [switch1]
TASK [Unconfigure src vrf] *****************************************************************************************************************************************
skipping: [switch1]
TASK [Await connection to Intersight] ******************************************************************************************************************************
FAILED - RETRYING: [switch1]: Await connection to Intersight (10 retries left).
FAILED - RETRYING: [switch1]: Await connection to Intersight (9 retries left).
FAILED - RETRYING: [switch1]: Await connection to Intersight (8 retries left).
FAILED - RETRYING: [switch1]: Await connection to Intersight (7 retries left).
FAILED - RETRYING: [switch1]: Await connection to Intersight (6 retries left).
FAILED - RETRYING: [switch1]: Await connection to Intersight (5 retries left).
FAILED - RETRYING: [switch1]: Await connection to Intersight (4 retries left).
ok: [switch1]
TASK [Get show system device-connector claim-info] *****************************************************************************************************************
ok: [switch1]
TASK [Set claiminfoDict] *******************************************************************************************************************************************
ok: [switch1] => (item=SerialNumber: FDO21112E2L)
ok: [switch1] => (item= SecurityToken: 0A70886FE1B8)
ok: [switch1] => (item= Duration: 599)
ok: [switch1] => (item= Message: )
ok: [switch1] => (item= Claim state: Not Claimed)
TASK [claim device - PROXY] ****************************************************************************************************************************************
skipping: [switch1]
TASK [claim device - NO PROXY] *************************************************************************************************************************************
changed: [switch1]
PLAY RECAP *********************************************************************************************************************************************************
switch1 : ok=8 changed=2 unreachable=0 failed=0 skipped=4 rescued=0 ignored=0
驗證
若要驗證新目標的宣告,請完成以下步驟:
在Nexus交換機上
10.3(4a)M之前的版本
#運行bash sudo cat /mnt/pss/connector.db
Nexus# run bash sudo cat /mnt/pss/connector.db
{
"AccountOwnershipState": "Claimed",
"AccountOwnershipUser": "bpaez@cisco.com",
"AccountOwnershipTime": "2024-04-25T22:37:25.173Z",
"AccountOwnershipId": "TAC-DCRS",
"DomainGroupMoid": "6620503275646133014ec978",
"AccountMoid": "6620503275646133014ec977",
"CloudDns": "svc.ucs-connect.com",
"CloudDnsList": [
"svc.intersight.com",
"svc-static1.intersight.com",
"svc.ucs-connect.com",
"svc-static1.ucs-connect.com"
],
"CloudCert": "",
"UserCloudCerts": {},
"Identity": "662adb256f72613901e8bc19",
"AccessKeyId": "98facfdbf3855bcfd340f2bbb0c388f8",
"AccessKey": "",
"PrivateAccessKey": "-----BEGIN RSA PRIVATE KEY-----
-CUT-
5Do\nD18Ta5YvuIYFLZrYlHLyCDOhS5035AUEGNtEceiPhQjOCvRumyJD\n-----END RSA PRIVATE KEY-----\n",
"CloudEnabled": true,
"ReadOnlyMode": false,
"LocalConfigLockout": false,
"TunneledKVM": false,
"HttpProxy": {
"ProxyHost": "proxy.cisco.com",
"ProxyPort": 8080,
"Preference": 0,
"ProxyType": "Manual",
"Targets": [
{
"ProxyHost": "proxy.cisco.com",
"ProxyPort": 8080,
"Preference": 0
}
]
},
"LogLevel": "info",
"DbVersion": 1,
"AutoUpgradeAdminState": "Automatic"以10.3(4a)M開頭的版本
# show system device-connector claim-info
N9k-Leaf-2# show system device-connector claim-info
SerialNumber: FDO23021ZUJ
SecurityToken:
Duration: 0
Message: Cannot fetch claim code for already claimed device
Claim state: Claimed
Claim time: 2024-02-09T15:38:57.561Z
Claimed by: brvarney@cisco.com
Account: ACI-DCRS-TAC
Site name:
Site ID:# show system internal intersight info
# show system internal intersight info
Intersight connector.db Info:
ConnectionState :Connected
ConnectionStateQual :
AccountOwnershipState :Claimed
AccountOwnershipUser :brvarney@cisco.com
AccountOwnershipTime :2024-02-09T15:38:57.561Z
AccountOwnershipId :ACI-DCRS-TAC
DomainGroupMoid :5eb2e1e47565612d3079fe9a
AccountMoid :5eb2e1e47565612d3079fe92
CloudDns :svc.ucs-connect.com
CloudDnsList:
1. :svc.ucs-connect.com
2. :svc.intersight.com
3. :svc-static1.intersight.com
4. :svc-static1.ucs-connect.com
Identity :65c647116f72513501e75530
CloudEnabled :true
ReadOnlyMode :false
LocalConfigLockout :false
TunneledKVM :false
HttpProxy:
ProxyHost :proxy.cisco.com
ProxyPort :8080
Preferenc :0
ProxyType :Manual
Target[1]:
ProxyHost :proxy.cisco.com
ProxyPort :8080
Preference :0
LogLevel :info
DbVersion :1
AutoUpgradeAdminState :Automatic
阿尼塞
可以在playbook.yaml末尾增加一個任務,以便獲取交換機插入資訊。
- name: Get intersight info
nxos_command:
commands:
- show system internal intersight info
register: intersightInfo_claimed
retries: 10
delay: 10
until: intersightInfo.stdout is search("Connecte")
- name: Display intersight info
vars:
msg: |-
output from {{ inventory_hostname }}:
{{ intersightInfo_claimed.stdout | join("") }}
debug:
msg: "{{ msg.split('\n') }}"
以下是相應的輸出:
TASK [Get intersight info] ***************************************************************************************************
ok: [switch1]
TASK [Display intersight info] ***********************************************************************************************
ok: [switch1] => {
"msg": [
"output from switch1:",
"Intersight connector.db Info:",
"ConnectionState :Connected",
"ConnectionStateQual :",
"AccountOwnershipState :Claimed",
"AccountOwnershipUser :vricci@cisco.com",
"AccountOwnershipTime :2024-02-10T01:00:28.516Z",
"AccountOwnershipId :vricci",
"DomainGroupMoid :5fcb98d97565612d33fdf1ae",
"AccountMoid :5fcb98d97565612d33fdf1ac",
"CloudDns :svc.intersight.com",
"CloudDnsList: ",
" 1. :svc.intersight.com",
" 2. :svc-static1.intersight.com",
" 3. :svc.ucs-connect.com",
" 4. :svc-static1.ucs-connect.com",
"Identity :65c6caac6f72613901f841c1",
"CloudEnabled :true",
"ReadOnlyMode :false",
"LocalConfigLockout :false",
"TunneledKVM :false",
"HttpProxy: ",
" ProxyHost :proxy.cisco.com",
" ProxyPort :80",
" Preferenc :0",
" ProxyType :Manual",
" Target[1]: ",
" ProxyHost :proxy.cisco.com",
" ProxyPort :80",
" Preference :0",
"LogLevel :info",
"DbVersion :1",
"AutoUpgradeAdminState :Automatic"
]
}
停用裝置聯結器
| 命令或操作 | 目的 | |
|---|---|---|
| 步驟 1 |
無功能intersight 範例: switch(config)# no feature intersight |
停用intersight進程並刪除所有NXDC配置和日誌儲存。 |
修訂記錄
| 修訂 | 發佈日期 | 意見 |
|---|---|---|
4.0 |
30-Sep-2024 |
已將EMEA地區通知增加到「Intersight門戶上的配置」部分 |
3.0 |
15-May-2024 |
增加了用於手動申請NXOS裝置的快速入門影片 |
2.0 |
02-Apr-2024 |
增加了「停用裝置聯結器」部分 |
1.0 |
22-Feb-2024 |
初始版本 |
由思科工程師貢獻
- Branden VarneyTechnical Leader
- Vincent RicciTechnical Leader
- Yogesh RamdossPrincipal Engineer
 意見
意見