FlexVPN VRF感知遠端訪問配置示例
簡介
本檔案將提供在遠端存取情況下感知VPN路由和轉送(VRF)的FlexVPN的組態範例。此配置使用Cisco IOS®路由器作為具有遠端訪問AnyConnect客戶端的隧道聚合裝置。
必要條件
需求
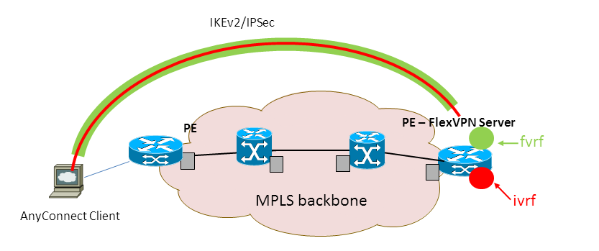
在此範例組態中,VPN連線會在多重協定標籤交換(MPLS)提供者邊緣(PE)裝置上終止,其中通道終端點位於MPLS VPN中(前端VRF [FVRF])。 加密流量解密後,明文流量將轉發到另一個MPLS VPN(內部VRF [IVRF])。
採用元件
本文中的資訊係根據以下軟體和硬體版本:
-
採用IOS-XE3.7.1(15.2(4)S1)作為FlexVPN伺服器的Cisco ASR 1000系列聚合服務路由器
-
Cisco AnyConnect安全行動化使用者端和Cisco AnyConnect VPN使用者端版本3.1
-
Microsoft網路策略伺服器(NPS)RADIUS伺服器
本文中的資訊是根據特定實驗室環境內的裝置所建立。文中使用到的所有裝置皆從已清除(預設)的組態來啟動。如果您的網路正在作用,請確保您已瞭解任何指令可能造成的影響。
慣例
設定
本節提供用於設定本文件中所述功能的資訊。
註:使用Command Lookup Tool(僅供已註冊客戶使用)可獲取本節中使用的命令的詳細資訊。
網路拓撲
本檔案會使用以下網路設定:
FlexVPN伺服器配置
以下是FlexVPN伺服器配置的示例:
hostname ASR1K ! aaa new-model ! ! aaa group server radius lab-AD server-private 172.18.124.30 key Cisco123 ! aaa authentication login default local aaa authentication login AC group lab-AD aaa authorization network AC local ! aaa session-id common ! ip vrf fvrf rd 2:2 route-target export 2:2 route-target import 2:2 ! ip vrf ivrf rd 1:1 route-target export 1:1 route-target import 1:1 ! ! crypto pki trustpoint AC enrollment mode ra enrollment url http://lab-ca:80/certsrv/mscep/mscep.dll fqdn asr1k.labdomain.cisco.com subject-name cn=asr1k.labdomain.cisco.com revocation-check crl rsakeypair AC ! ! crypto pki certificate chain AC certificate 433D7311000100000259 certificate ca 52DD978E9680C1A24812470E79B8FB02 ! ! crypto ikev2 authorization policy default pool flexvpn-pool def-domain cisco.com route set interface ! crypto ikev2 authorization policy AC pool AC dns 10.7.7.129 netmask 255.255.255.0 banner ^CCC Welcome ^C def-domain example.com ! crypto ikev2 proposal AC encryption aes-cbc-256 integrity sha1 group 5 ! crypto ikev2 policy AC match fvrf fvrf proposal AC ! ! crypto ikev2 profile AC match fvrf fvrf match identity remote key-id cisco.com identity local dn authentication remote eap query-identity authentication local rsa-sig pki trustpoint AC dpd 60 2 on-demand aaa authentication eap AC aaa authorization group eap list AC AC virtual-template 40 ! ! crypto ipsec transform-set AC esp-aes 256 esp-sha-hmac mode tunnel ! crypto ipsec profile AC set transform-set AC set ikev2-profile AC ! ! interface Loopback0 description BGP source interface ip address 10.5.5.5 255.255.255.255 ! interface Loopback99 description VPN termination point in the FVRF ip vrf forwarding fvrf ip address 7.7.7.7 255.255.255.255 ! interface Loopback100 description loopback interface in the IVRF ip vrf forwarding ivrf ip address 6.6.6.6 255.255.255.255 ! interface GigabitEthernet0/0/1 description MPLS IP interface facing the MPLS core ip address 20.11.11.2 255.255.255.0 negotiation auto mpls ip cdp enable ! ! ! interface Virtual-Template40 type tunnel no ip address tunnel mode ipsec ipv4 tunnel vrf fvrf tunnel protection ipsec profile AC ! router bgp 2 bgp log-neighbor-changes redistribute connected redistribute static neighbor 10.2.2.2 remote-as 2 neighbor 10.2.2.2 update-source Loopback0 ! address-family vpnv4 neighbor 10.2.2.2 activate neighbor 10.2.2.2 send-community extended exit-address-family ! address-family ipv4 vrf fvrf redistribute connected redistribute static exit-address-family ! address-family ipv4 vrf ivrf redistribute connected redistribute static exit-address-family ! ip local pool AC 192.168.1.100 192.168.1.150
Radius使用者設定檔組態
用於RADIUS配置檔案的關鍵配置是兩個思科供應商特定屬性(VSA)屬性值(AV)對,它們將動態建立的虛擬訪問介面放在IVRF中,並在動態建立的虛擬訪問介面上啟用IP:
ip:interface-config=ip unnumbered loopback100 ip:interface-config=ip vrf forwarding ivrf
在Microsoft NPS中,配置位於網路策略設定中,如以下示例所示:
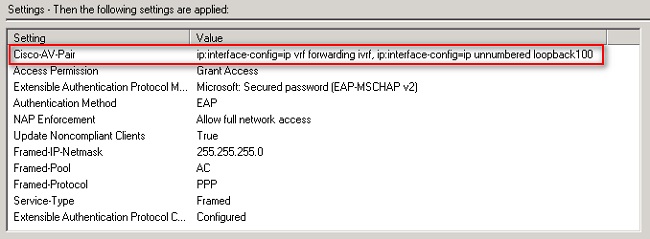
 注意:ip vrf forwarding命令必須位於ip unnumbered命令之前。如果虛擬訪問介面從虛擬模板克隆,然後應用ip vrf forwarding命令,則將從虛擬訪問介面刪除任何IP配置。雖然已建立通道,但點對點(P2P)介面的CEF鄰接關係並不完整。以下是show adjacency命令的示例,結果不完整:
注意:ip vrf forwarding命令必須位於ip unnumbered命令之前。如果虛擬訪問介面從虛擬模板克隆,然後應用ip vrf forwarding命令,則將從虛擬訪問介面刪除任何IP配置。雖然已建立通道,但點對點(P2P)介面的CEF鄰接關係並不完整。以下是show adjacency命令的示例,結果不完整:
ASR1k#show adjacency virtual-access 1 Protocol Interface Address IP Virtual-Access1 point2point(6) (incomplete)
如果CEF鄰接關係不完整,則會丟棄所有出站VPN流量。
驗證
使用本節內容,確認您的組態是否正常運作。驗證派生的虛擬接入介面,然後驗證IVRF和FVRF設定。
派生虛擬訪問介面
確認已正確從虛擬模板介面克隆建立的虛擬訪問介面,並已應用從RADIUS伺服器下載的所有每使用者屬性:
ASR1K#sh derived-config interface virtual-access 1 Building configuration...Derived configuration : 250 bytes ! interface Virtual-Access1 ip vrf forwarding ivrf ip unnumbered Loopback100 tunnel source 7.7.7.7 tunnel mode ipsec ipv4 tunnel destination 8.8.8.10 tunnel vrf fvrf tunnel protection ipsec profile AC no tunnel protection ipsec initiate end
加密作業階段
使用這些控制平面輸出驗證IVRF和FVRF設定。
以下是show crypto session detail指令輸出的範例:
ASR1K#show crypto session detail
Crypto session current status
Code: C - IKE Configuration mode, D - Dead Peer Detection
K - Keepalives, N - NAT-traversal, T - cTCP encapsulation
X - IKE Extended Authentication, F - IKE Fragmentation
Interface: Virtual-Access1
Uptime: 00:23:19
Session status: UP-ACTIVE
Peer: 8.8.8.10 port 57966 fvrf: fvrf ivrf: ivrf
Phase1_id: cisco.com
Desc: (none)
IKEv2 SA: local 7.7.7.7/4500 remote 8.8.8.10/57966 Active
Capabilities:(none) connid:1 lifetime:23:36:41
IPSEC FLOW: permit ip 0.0.0.0/0.0.0.0 host 192.168.1.103
Active SAs: 2, origin: crypto map
Inbound: #pkts dec'ed 95 drop 0 life (KB/Sec) 4607990/2200
Outbound: #pkts enc'ed 44 drop 0 life (KB/Sec) 4607997/2200
以下是show crypto IKEv2 session detail命令的輸出示例:
ASR1K#show crypto ikev2 sess detail
IPv4 Crypto IKEv2 Session
Session-id:4, Status:UP-ACTIVE, IKE count:1, CHILD count:1
Tunnel-id Local Remote fvrf/ivrf Status
1 7.7.7.7/4500 8.8.8.10/57966 fvrf/ivrf READY
Encr: AES-CBC, keysize: 256, Hash: SHA96, DH Grp:5, Auth sign: RSA, Auth verify: EAP
Life/Active Time: 86400/1298 sec
CE id: 1004, Session-id: 4
Status Description: Negotiation done
Local spi: EE87373C2C2643CA Remote spi: F80C8A4CB4143091
Local id: cn=asr1k.labdomain.cisco.com,hostname=asr1k.labdomain.cisco.com
Remote id: cisco.com
Remote EAP id: user1
Local req msg id: 1 Remote req msg id: 43
Local next msg id: 1 Remote next msg id: 43
Local req queued: 1 Remote req queued: 43
Local window: 5 Remote window: 1
DPD configured for 60 seconds, retry 2
NAT-T is detected outside
Cisco Trust Security SGT is disabled
Assigned host addr: 192.168.1.103
Initiator of SA : No
Child sa: local selector 0.0.0.0/0 - 255.255.255.255/65535
remote selector 192.168.1.103/0 - 192.168.1.103/65535
ESP spi in/out: 0x88F2A69E/0x19FD0823
AH spi in/out: 0x0/0x0
CPI in/out: 0x0/0x0
Encr: AES-CBC, keysize: 256, esp_hmac: SHA96
ah_hmac: None, comp: IPCOMP_NONE, mode tunnel
IPv6 Crypto IKEv2 Session
ASR1K#
疑難排解
目前尚無適用於此組態的具體疑難排解資訊。
相關資訊
修訂記錄
| 修訂 | 發佈日期 | 意見 |
|---|---|---|
1.0 |
27-Mar-2013 |
初始版本 |
 意見
意見