보안 방화벽에서 동적 라우팅 프로토콜로 DVTI 구성
편견 없는 언어
본 제품에 대한 문서 세트는 편견 없는 언어를 사용하기 위해 노력합니다. 본 설명서 세트의 목적상, 편견 없는 언어는 나이, 장애, 성별, 인종 정체성, 민족 정체성, 성적 지향성, 사회 경제적 지위 및 교차성에 기초한 차별을 의미하지 않는 언어로 정의됩니다. 제품 소프트웨어의 사용자 인터페이스에서 하드코딩된 언어, RFP 설명서에 기초한 언어 또는 참조된 서드파티 제품에서 사용하는 언어로 인해 설명서에 예외가 있을 수 있습니다. 시스코에서 어떤 방식으로 포용적인 언어를 사용하고 있는지 자세히 알아보세요.
이 번역에 관하여
Cisco는 전 세계 사용자에게 다양한 언어로 지원 콘텐츠를 제공하기 위해 기계 번역 기술과 수작업 번역을 병행하여 이 문서를 번역했습니다. 아무리 품질이 높은 기계 번역이라도 전문 번역가의 번역 결과물만큼 정확하지는 않습니다. Cisco Systems, Inc.는 이 같은 번역에 대해 어떠한 책임도 지지 않으며 항상 원본 영문 문서(링크 제공됨)를 참조할 것을 권장합니다.
소개
이 문서에서는 Secure Firewall 9.20에서 DVTI(Dynamic Virtual Tunnel Interface)를 구성하는 방법에 대해 설명합니다.
사전 요구 사항
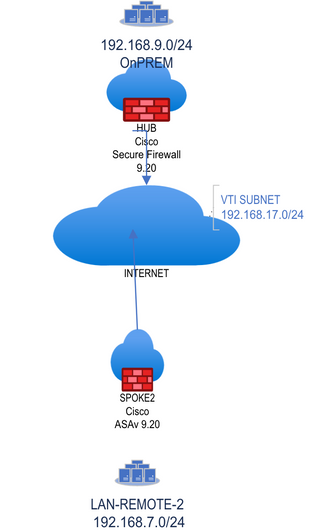
- 기본 라우팅 컨피그레이션과 IKEV2 지원을 갖춘 ASA 9.20 이상의 Cisco Secure Firewall 1대를 보유하고, 루프백 인터페이스가 하나인 허브로 작동하여 192.168.9.0/24의 온프레미스 로컬 네트워크를 시뮬레이션합니다.
- 기본 라우팅 컨피그레이션과 IKEv2 지원을 갖춘 ASA 9.20 이상의 Cisco Secure Firewall 1개를 192.168.7.0/24의 원격 네트워크를 시뮬레이션하도록 사전 구성된 루프백 인터페이스 1개로 스포크-1로 작동하도록 준비하십시오.
요구 사항
- 이 문서에 설명된 모든 동적 라우팅 프로토콜에 대한 일반적인 지식(OSPF, EIGRP 및 BGP).
- Cisco Secure Firewall 디바이스의 CLI 컨피그레이션에 대해 숙지하십시오.
사용되는 구성 요소
이 문서의 정보는 다음 소프트웨어 버전을 기반으로 합니다.
- Cisco Secure Firewall with ASA 9.20 이상

참고: 이 문서의 정보는 특정 랩 환경의 디바이스에서 작성되었습니다. 이 문서에 사용된 모든 디바이스는 초기화된(기본) 컨피그레이션으로 시작되었습니다. 현재 네트워크가 작동 중인 경우 모든 명령의 잠재적인 영향을 미리 숙지하시기 바랍니다.
배경 정보
동적 가상 터널 인터페이스
DVTI(Dynamic Virtual Tunnel Interface)는 원격 액세스 VPN(Virtual Private Network)을 위해 매우 안전하고 확장 가능한 연결을 제공할 수 있습니다.
DVTI는 허브 및 스포크 구성에 모두 사용할 수 있습니다. 터널은 각 VPN 세션에 대해 별도의 온디맨드 가상 액세스 인터페이스를 제공합니다.
1. 스포크가 VPN 연결을 위해 허브와 IKE 교환 요청을 시작합니다.
2. 허브가 스포크를 인증합니다.
3. Cisco Secure Firewall Management Center는 허브에 동적 가상 템플릿을 할당합니다.
4. 가상 템플릿은 허브에 가상 액세스 인터페이스를 동적으로 생성합니다. 이 인터페이스는 스포크당 VPN 세션에 대해 고유합니다.
5. 허브는 가상 액세스 인터페이스를 사용하는 스포크와 동적 VTI 터널을 설정합니다.
6. 동적 라우팅 프로토콜(BGP/OSPF/EIGRP)을 사용하거나 보호된 네트워크 기능(Multiple-Security Association VTI)을 사용하는 터널을 통해 허브 및 스포크가 트래픽을 교환합니다.
7. 동적 VTI는 다른 인터페이스와 마찬가지로 작동하므로 터널이 활성화되는 즉시 QoS, 방화벽 규칙, 라우팅 프로토콜 및 기타 기능을 적용할 수 있습니다.
8. 단일 DVTI가 여러 원격/스포크 사이트에 대해 HUB 디바이스 및 여러 고정 터널 인터페이스에 생성됩니다.
이 문서에서는 BGP에서 OSPF 및 EIGRP를 DVTI를 통해 테스트할 수 있습니다.

참고: Cisco Secure Firewall은 버전 7.3에 DVTI 지원을 추가했으며 현재 Cisco 버그 ID CSCwe13781에 따라 단일 DVTI만 지원합니다.
구성
네트워크 다이어그램
설정
Cisco Secure Firewall Hub 컨피그레이션
물리적 터널 소스 인터페이스를 구성합니다.
interface GigabitEthernet0/0
nameif vlan2820
security-level 100
ip address 10.28.20.98 255.255.255.0 IkEv2 정책을 구성합니다.
crypto ikev2 policy 1
encryption aes-256 aes-192 aes
integrity sha512 sha384 sha256 sha
group 21 20 14
prf sha256
lifetime seconds 86400IPSEC 정책을 구성하고 새 IPSEC 프로필에 연결합니다.
crypto ipsec ikev2 ipsec-proposal VPN-LAB
protocol esp encryption aes-256 aes-192 aes
protocol esp integrity sha-512 sha-256 sha-1
crypto ipsec profile VPN-LAB-PROFILE
set ikev2 ipsec-proposal VPN-LAB
set security-association lifetime seconds 1000
이전에 생성한 IPSEC 프로필로 Virtual-template을 구성하고 이를 DVTI의 IP 주소를 제공하는 루프백 인터페이스에 할당합니다.

참고: Virtual-template은 온디맨드 터널용 DVTI를 구성하는 데 사용됩니다.
interface Loopback200
nameif DVTI-LOOPBACK
ip address 172.16.17.1 255.255.255.255
interface Virtual-Template1 type tunnel
nameif DVTI-HUB
ip unnumbered DVTI-LOOPBACK
tunnel source interface vlan2820
tunnel mode ipsec ipv4
tunnel protection ipsec profile FMC_IPSEC_PROFILE_2
허브 뒤에 있는 OnPREM 네트워크에서 트래픽을 시뮬레이션하는 보조 루프백 인터페이스를 생성합니다.

참고: 허브 뒤에 로컬 트래픽이 있는 경우 이 단계를 건너뜁니다.
interface Loopback100
nameif ON-PREM
ip address 192.168.9.1 255.255.255.255터널 그룹을 구성합니다.

참고: 명령 경로 집합 인터페이스는 DVTI IP 주소를 고정 IP 주소로 피어에 전송합니다.
tunnel-group 10.28.20.100 type ipsec-l2l
tunnel-group 10.28.20.100 ipsec-attributes
virtual-template 1
ikev2 remote-authentication pre-shared-key *****
ikev2 local-authentication pre-shared-key *****
ikev2 route set interface터널을 작성하는 인터페이스에서 IKEv2를 활성화합니다.
crypto ikev2 enable vlan2820Cisco Secure Firewall 스포크 컨피그레이션
물리적 터널 소스 인터페이스를 구성합니다.
interface GigabitEthernet0/0
nameif vlan2820
security-level 100
ip address 10.28.20.100 255.255.255.0 IKEv2 정책을 구성합니다.
crypto ikev2 policy 1
encryption aes-256 aes-192 aes
integrity sha512 sha384 sha256 sha
group 21 20 14
prf sha256
lifetime seconds 86400IPSEC 정책을 구성하고 새 IPSEC 프로필에 연결합니다.
crypto ipsec ikev2 ipsec-proposal VPN-LAB
protocol esp encryption aes-256 aes-192 aes
protocol esp integrity sha-512 sha-256 sha-1
crypto ipsec profile VPN-LAB-PROFILE
set ikev2 ipsec-proposal VPN-LAB
set security-association lifetime seconds 1000
이전에 생성한 IPSEC 프로파일을 사용하여 고정 가상 터널 인터페이스를 구성하고, 이를 번호가 지정되지 않은 IP 주소를 제공하는 루프백 인터페이스에 할당합니다.
interface Loopback200
nameif VTI-LOOPBACK
ip address 172.16.17.2 255.255.255.255
interface Tunnel2
nameif SVTI-SPOKE-3
ip unnumbered VTI-LOOPBACK
tunnel source interface vlan2820
tunnel destination 10.28.20.98
tunnel mode ipsec ipv4
tunnel protection ipsec profile VPN-LAB-PROFILE스포크 뒤에 있는 LAN-REMOTE-1 네트워크의 트래픽을 시뮬레이션하는 보조 루프백 인터페이스를 생성합니다.
interface Loopback100
nameif LAN-REMOTE-1
ip address 192.168.7.1 255.255.255.255터널 그룹을 구성합니다.

참고: 명령 경로 집합 인터페이스는 SVTI IP 주소를 고정 IP 주소로 피어에 전송합니다.
tunnel-group 10.28.20.98 type ipsec-l2l
tunnel-group 10.28.20.98 ipsec-attributes
ikev2 remote-authentication pre-shared-key *****
ikev2 local-authentication pre-shared-key *****
ikev2 route set interface터널을 구축할 수 있는 인터페이스에서 IKEv2를 활성화합니다.
crypto ikev2 enable vlan2820OSPF 구성
허브 컨피그레이션

참고: Redistribute connected subnets 명령은 OSPF를 통해 스포크에 OnPREM 네트워크를 광고하는 데 사용됩니다. 재배포는 설계에 따라 다를 수 있습니다.
router ospf 1
router-id 172.16.17.1
network 172.16.17.0 255.255.255.0 area 0
log-adj-changes
redistribute connected subnets스포크 컨피그레이션
router ospf 1
router-id 172.16.17.2
network 172.16.17.0 255.255.255.0 area 0
log-adj-changes
redistribute connected subnetsOSPF 확인
허브 확인
ASAV2-hub# show ospf
Routing Process "ospf 1" with ID 172.16.17.1
Start time: 4d23h, Time elapsed: 3d04h
Supports only single TOS(TOS0) routes
Supports opaque LSA
Supports Link-local Signaling (LLS)
Supports area transit capability
Event-log enabled, Maximum number of events: 1000, Mode: cyclic
It is an autonomous system boundary router
Redistributing External Routes from,
connected, includes subnets in redistribution
Router is not originating router-LSAs with maximum metric
Initial SPF schedule delay 5000 msecs
Minimum hold time between two consecutive SPFs 10000 msecs
Maximum wait time between two consecutive SPFs 10000 msecs
Incremental-SPF disabled
Minimum LSA interval 5 secs
Minimum LSA arrival 1000 msecs
LSA group pacing timer 240 secs
Interface flood pacing timer 33 msecs
Retransmission pacing timer 66 msecs
Number of external LSA 5. Checksum Sum 0x39716
Number of opaque AS LSA 0. Checksum Sum 0x0
Number of DCbitless external and opaque AS LSA 0
Number of DoNotAge external and opaque AS LSA 0
Number of areas in this router is 1. 1 normal 0 stub 0 nssa
Number of areas transit capable is 0
External flood list length 0
IETF NSF helper support enabled
Cisco NSF helper support enabled
Reference bandwidth unit is 100 mbps
Area BACKBONE(0)
Number of interfaces in this area is 3 (1 loopback)
Area has no authentication
SPF algorithm last executed 2d04h ago
SPF algorithm executed 10 times
Area ranges are
Number of LSA 2. Checksum Sum 0x1c99f
Number of opaque link LSA 0. Checksum Sum 0x0
Number of DCbitless LSA 0
Number of indication LSA 0
Number of DoNotAge LSA 0
Flood list length 0
ASAV2-hub# show ospf neighbor
Neighbor ID Pri State Dead Time Address Interface
172.16.17.2 0 FULL/ - 0:00:39 172.16.17.2 DVTI-HUB_va11이제 허브의 라우팅 테이블에 OSPF를 통한 LAN-REMOTE-1 네트워크가 표시됩니다.
ASAV2-hub# show route ospf
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
SI - Static InterVRF, BI - BGP InterVRF
Gateway of last resort is 10.28.20.101 to network 0.0.0.0
O E2 192.168.7.0 255.255.255.255
[110/20] via 172.16.17.2, 2d04h, DVTI-HUB_va11스포크 확인
ASAv-spoke-2# show ospf
Routing Process "ospf 1" with ID 172.16.17.2
Start time: 3w3d, Time elapsed: 3d04h
Supports only single TOS(TOS0) routes
Supports opaque LSA
Supports Link-local Signaling (LLS)
Supports area transit capability
Event-log enabled, Maximum number of events: 1000, Mode: cyclic
It is an autonomous system boundary router
Redistributing External Routes from,
connected, includes subnets in redistribution
Router is not originating router-LSAs with maximum metric
Initial SPF schedule delay 5000 msecs
Minimum hold time between two consecutive SPFs 10000 msecs
Maximum wait time between two consecutive SPFs 10000 msecs
Incremental-SPF disabled
Minimum LSA interval 5 secs
Minimum LSA arrival 1000 msecs
LSA group pacing timer 240 secs
Interface flood pacing timer 33 msecs
Retransmission pacing timer 66 msecs
Number of external LSA 4. Checksum Sum 0x37bc8
Number of opaque AS LSA 0. Checksum Sum 0x0
Number of DCbitless external and opaque AS LSA 0
Number of DoNotAge external and opaque AS LSA 0
Number of areas in this router is 1. 1 normal 0 stub 0 nssa
Number of areas transit capable is 0
External flood list length 0
IETF NSF helper support enabled
Cisco NSF helper support enabled
Reference bandwidth unit is 100 mbps
Area BACKBONE(0)
Number of interfaces in this area is 2 (1 loopback)
Area has no authentication
SPF algorithm last executed 2d04h ago
SPF algorithm executed 1 times
Area ranges are
Number of LSA 2. Checksum Sum 0x1fe9a
Number of opaque link LSA 0. Checksum Sum 0x0
Number of DCbitless LSA 0
Number of indication LSA 0
Number of DoNotAge LSA 0
Flood list length 0
ASAv-spoke-2# show ospf neighbor
Neighbor ID Pri State Dead Time Address Interface
172.16.17.1 0 FULL/ - 0:00:34 172.16.17.1 SVTI-SPOKE-3이제 스포크의 라우팅 테이블에 OSPF를 통한 OnPREM 네트워크가 표시됩니다.
ASAv-spoke-2# show route ospf
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
SI - Static InterVRF, BI - BGP InterVRF
Gateway of last resort is 10.28.20.101 to network 0.0.0.0
O E2 192.168.9.1 255.255.255.255
[110/20] via 172.16.17.1, 2d04h, SVTI-SPOKE-3이제 스포크 LAN-REMOTE-1에서 OnPREM에 연결할 수 있습니다.
ASAv-spoke-2# ping LAN-REMOTE-1 192.168.9.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.9.1, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 1/2/10 ms
ASAv-spoke-2# show crypto ipsec sa peer 10.28.20.98 | i cap|iden|spi
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
#pkts encaps: 9, #pkts encrypt: 9, #pkts digest: 9
#pkts decaps: 9, #pkts decrypt: 9, #pkts verify: 9
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
current outbound spi: 4BC1FF2C
current inbound spi : FB455CB8
spi: 0xFB455CB8 (4215626936)
spi: 0x4BC1FF2C (1271004972)이제 허브 OnPREM에서 LAN-REMOTE-1에 연결할 수 있습니다.
ASAV2-hub# ping ON-PREM 192.168.7.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.7.1, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 1/2/10 ms
ASAV2-hub# show crypto ipsec sa peer 10.28.20.100
peer address: 10.28.20.100
interface: DVTI-HUB_va12
Crypto map tag: DVTI-HUB_vtemplate_dyn_map, seq num: 1, local addr: 10.28.20.98
Protected vrf (ivrf): Global
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
current_peer: 10.28.20.100
#pkts encaps: 15, #pkts encrypt: 15, #pkts digest: 15
#pkts decaps: 15, #pkts decrypt: 15, #pkts verify: 15
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 15, #pkts comp failed: 0, #pkts decomp failed: 0
#pre-frag successes: 0, #pre-frag failures: 0, #fragments created: 0
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
#TFC rcvd: 0, #TFC sent: 0
#Valid ICMP Errors rcvd: 0, #Invalid ICMP Errors rcvd: 0
#send errors: 0, #recv errors: 0
local crypto endpt.: 10.28.20.98/500, remote crypto endpt.: 10.28.20.100/500
path mtu 1500, ipsec overhead 94(44), media mtu 1500
PMTU time remaining (sec): 0, DF policy: copy-df
ICMP error validation: disabled, TFC packets: disabledEIGRP 구성
허브 구성:
ASAV2-hub# sh run router
router eigrp 10
network 172.16.17.0 255.255.255.0
redistribute connected스포크 구성:
ASAv-spoke-2# sh run router
router eigrp 10
network 172.16.17.0 255.255.255.0
redistribute connected
이제 스포크 LAN-REMOTE-1에서 OnPREM에 연결할 수 있습니다.
ASAv-spoke-2# ping LAN-REMOTE-1 192.168.9.1 rep 100
Type escape sequence to abort.
Sending 100, 100-byte ICMP Echos to 192.168.9.1, timeout is 2 seconds:
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Success rate is 100 percent (100/100), round-trip min/avg/max = 1/2/10 ms
ASAv-spoke-2# show crypto ipsec sa peer 10.28.20.98 | i cap|iden|spi
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
#pkts encaps: 102, #pkts encrypt: 102, #pkts digest: 102
#pkts decaps: 102, #pkts decrypt: 102, #pkts verify: 102
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
current outbound spi: 3EED404C
current inbound spi : 646D2C0C
spi: 0x646D2C0C (1684876300)
spi: 0x3EED404C (1055735884)이제 허브 OnPREM에서 LAN-REMOTE-1에 연결할 수 있습니다.
ASAV2-hub# ping ON-PREM 192.168.7.1 rep 100
Type escape sequence to abort.
Sending 100, 100-byte ICMP Echos to 192.168.7.1, timeout is 2 seconds:
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Success rate is 100 percent (100/100), round-trip min/avg/max = 1/1/10 ms
ASAV2-hub# show crypto ipsec sa peer 10.28.20.100 | i cap|iden|spi
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
#pkts encaps: 208, #pkts encrypt: 208, #pkts digest: 208
#pkts decaps: 208, #pkts decrypt: 208, #pkts verify: 208
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
current outbound spi: 646D2C0C
current inbound spi : 3EED404C
spi: 0x3EED404C (1055735884)
spi: 0x646D2C0C (1684876300)EIGRP 확인
허브 확인:
ASAV2-hub# show eigrp neighbors
EIGRP-IPv4 Neighbors for AS(10)
H Address Interface Hold Uptime SRTT RTO Q Seq
(sec) (ms) Cnt Num
0 172.16.17.2 DVTI-HUB_va12 12 00:02:01 8 200 0 4이제 허브의 라우팅 테이블에 EIGRP를 통한 LAN-REMOTE-1 네트워크가 표시됩니다.
ASAV2-hub# show route eigrp
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
SI - Static InterVRF, BI - BGP InterVRF
Gateway of last resort is 10.28.20.101 to network 0.0.0.0
D EX 192.168.7.1 255.255.255.255
[170/53760] via 172.16.17.2, 00:05:28, DVTI-HUB_va12스포크 확인:
ASAv-spoke-2# show eigrp neighbors
EIGRP-IPv4 Neighbors for AS(10)
H Address Interface Hold Uptime SRTT RTO Q Seq
(sec) (ms) Cnt Num
0 172.16.17.1 SVTI-SPOKE-3 12 00:07:05 34 204 0 3이제 스포크의 라우팅 테이블에 EIGRP를 통한 OnPREM 네트워크가 표시됩니다.
ASAv-spoke-2# show route eigrp
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
SI - Static InterVRF, BI - BGP InterVRF
Gateway of last resort is 10.28.20.101 to network 0.0.0.0
D EX 192.168.9.1 255.255.255.255
[170/53760] via 172.16.17.1, 00:07:43, SVTI-SPOKE-3BGP 구성

참고: 고정 또는 동적 VTI 인터페이스가 eBGP와 결합되는 경우 BGP를 사용하는 경우 TTL 홉의 값이 둘 이상인지 확인합니다.
허브 구성:
router bgp 100
bgp log-neighbor-changes
bgp bestpath compare-routerid
address-family ipv4 unicast
neighbor 172.16.17.2 remote-as 200
neighbor 172.16.17.2 ebgp-multihop 10
neighbor 172.16.17.2 activate
redistribute connected
no auto-summary
no synchronization
exit-address-family스포크 컨피그레이션
router bgp 200
bgp log-neighbor-changes
bgp bestpath compare-routerid
address-family ipv4 unicast
neighbor 172.16.17.1 remote-as 100
neighbor 172.16.17.1 ebgp-multihop 10
neighbor 172.16.17.1 activate
redistribute connected
no auto-summary
no synchronization
exit-address-familyBGP 확인
허브 확인:
ASAV2-hub# show bgp neighbors
BGP neighbor is 172.16.17.2, context single_vf, remote AS 200, external link
BGP version 4, remote router ID 192.168.7.1
BGP state = Established, up for 00:05:28
Last read 00:00:01, last write 00:01:00, hold time is 180, keepalive interval is 60 seconds
Neighbor sessions:
1 active, is not multisession capable (disabled)
Neighbor capabilities:
Route refresh: advertised and received(new)
Four-octets ASN Capability: advertised and received
Address family IPv4 Unicast: advertised and received
Multisession Capability:
Message statistics:
InQ depth is 0
OutQ depth is 0
Sent Rcvd
Opens: 1 1
Notifications: 0 0
Updates: 2 2
Keepalives: 6 6
Route Refresh: 0 0
Total: 9 9
Default minimum time between advertisement runs is 30 seconds
For address family: IPv4 Unicast
Session: 172.16.17.2
BGP table version 7, neighbor version 7/0
Output queue size : 0
Index 1
1 update-group member
Sent Rcvd
Prefix activity: ---- ----
Prefixes Current: 3 3 (Consumes 240 bytes)
Prefixes Total: 3 3
Implicit Withdraw: 0 0
Explicit Withdraw: 0 0
Used as bestpath: n/a 2
Used as multipath: n/a 0
Outbound Inbound
Local Policy Denied Prefixes: -------- -------
Bestpath from this peer: 2 n/a
Total: 2 0
Number of NLRIs in the update sent: max 3, min 0
Address tracking is enabled, the RIB does have a route to 172.16.17.2
Connections established 1; dropped 0
Last reset never
External BGP neighbor may be up to 10 hops away.
Transport(tcp) path-mtu-discovery is enabled
Graceful-Restart is disabled
ASAV2-hub#
ASAV2-hub# sh run router
router bgp 100
bgp log-neighbor-changes
bgp bestpath compare-routerid
address-family ipv4 unicast
neighbor 172.16.17.2 remote-as 200
neighbor 172.16.17.2 ebgp-multihop 10
neighbor 172.16.17.2 activate
redistribute connected
no auto-summary
no synchronization
exit-address-family
!
ASAV2-hub# sh run all router
router bgp 100
bgp log-neighbor-changes
no bgp always-compare-med
no bgp asnotation dot
no bgp bestpath med
bgp bestpath compare-routerid
bgp default local-preference 100
no bgp deterministic-med
bgp enforce-first-as
bgp maxas-limit 0
bgp transport path-mtu-discovery
timers bgp 60 180 0
address-family ipv4 unicast
bgp scan-time 60
bgp nexthop trigger enable
bgp nexthop trigger delay 5
bgp aggregate-timer 30
neighbor 172.16.17.2 remote-as 200
neighbor 172.16.17.2 ebgp-multihop 10
neighbor 172.16.17.2 activate
no bgp redistribute-internal
no bgp soft-reconfig-backup
no bgp suppress-inactive
redistribute connected
distance bgp 20 200 200
no auto-summary
no synchronization
exit-address-family
! 이제 허브의 라우팅 테이블에 BGP를 통한 LAN-REMOTE-1 네트워크가 표시됩니다.
ASAV2-hub# show route bgp
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
SI - Static InterVRF, BI - BGP InterVRF
Gateway of last resort is 10.28.20.101 to network 0.0.0.0
B 192.168.7.1 255.255.255.255 [20/0] via 172.16.17.2, 00:06:16
스포크 확인:
ASAv-spoke-2# show bgp neighbors
BGP neighbor is 172.16.17.1, context single_vf, remote AS 100, external link
BGP version 4, remote router ID 192.168.9.1
BGP state = Established, up for 00:06:59
Last read 00:00:27, last write 00:00:20, hold time is 180, keepalive interval is 60 seconds
Neighbor sessions:
1 active, is not multisession capable (disabled)
Neighbor capabilities:
Route refresh: advertised and received(new)
Four-octets ASN Capability: advertised and received
Address family IPv4 Unicast: advertised and received
Multisession Capability:
Message statistics:
InQ depth is 0
OutQ depth is 0
Sent Rcvd
Opens: 1 1
Notifications: 0 0
Updates: 2 2
Keepalives: 7 8
Route Refresh: 0 0
Total: 10 11
Default minimum time between advertisement runs is 30 seconds
For address family: IPv4 Unicast
Session: 172.16.17.1
BGP table version 9, neighbor version 9/0
Output queue size : 0
Index 1
1 update-group member
Sent Rcvd
Prefix activity: ---- ----
Prefixes Current: 3 3 (Consumes 240 bytes)
Prefixes Total: 3 3
Implicit Withdraw: 0 0
Explicit Withdraw: 0 0
Used as bestpath: n/a 2
Used as multipath: n/a 0
Outbound Inbound
Local Policy Denied Prefixes: -------- -------
Bestpath from this peer: 3 n/a
Total: 3 0
Number of NLRIs in the update sent: max 3, min 0
Address tracking is enabled, the RIB does have a route to 172.16.17.1
Connections established 1; dropped 0
Last reset never
External BGP neighbor may be up to 10 hops away.
Transport(tcp) path-mtu-discovery is enabled
Graceful-Restart is disabled이제 스포크의 라우팅 테이블에 BGP를 통한 OnPREM 네트워크가 표시됩니다.
ASAv-spoke-2# show route bgp
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
SI - Static InterVRF, BI - BGP InterVRF
Gateway of last resort is 10.28.20.101 to network 0.0.0.0
B 192.168.9.1 255.255.255.255 [20/0] via 172.16.17.1, 00:09:22문제 해결
OSPF의 문제를 해결하려면 다음 debugs 및 show 명령을 사용합니다.
debug ip ospf
debug ip ospf packet
debug ip ospf events
debug ip ospf hello
debug ip ospf adj
show ospf
show ospf neighbor
show ospf interface EIGRP의 문제를 해결하려면 다음 debugs 및 show 명령을 사용합니다.
debug ip eigrp
debug ip eigrp neighbor
debug ip eigrp notifications
show eigrp
show eigrp
show eigrp interfaces show eigrp neighbors show eigrp topology
BGP의 문제를 해결하려면 다음 debugs 및 show 명령을 사용합니다.
debug ip bgp all
debug ip bgp updates
debug ip bgp events
show bgp
show bgp summary
show bgp neighbors IKEv2 문제를 해결하려면 다음 debugs 및 show 명령을 사용합니다.
debug crypto ikev2 protocol 255
debug crypto ikev2 platform 255
debug crypto ipsec 255관련 정보
개정 이력
| 개정 | 게시 날짜 | 의견 |
|---|---|---|
1.0 |
31-Mar-2023 |
최초 릴리스 |
 피드백
피드백