Use Cisco aIOS WGB with EAP-TLS Authentication in a CUWN
Available Languages
Contents
Introduction
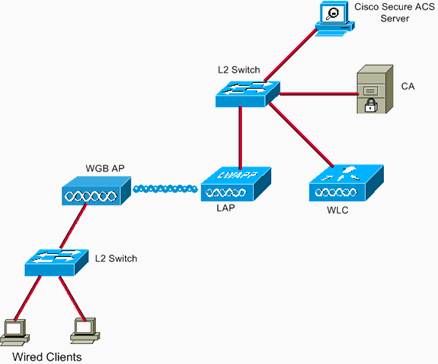
This example shows how to configure and use an autonomous IOS (aIOS) AP, running in Workgroup Bridge (WGB) mode, with EAP-TLS authentication, in a Cisco Unified Wireless Network (CUWN). In this example, a Microsoft Certification Authority (Windows 2003) issued the certificates of the WGB and through the copy-and-paste method, these certificates are manually entered on the WGB. ACS acts as the RADIUS server. WPA1/TKIP encryption with 802.1X key management is used.
Prerequisites
Requirements
Ensure that you meet these requirements before you attempt this configuration:
-
Knowledge of Cisco Autonomous solution and Cisco IOS-based Access Points.
-
Knowledge of Light Weight Access Point Protocol (LWAPP)
Components Used
The information in this document is based on these software and hardware versions:
-
WGB that runs Cisco IOS® Software Release 12.4(10b)JA2
It is important to use Cisco IOS Software Release 12.4(10b)JA2 or later for these reasons:
-
Cisco bug ID CSCsl85710 (registered customers only) —802.11a WGB cannot disable DFS channels or enable 'mobile station'
-
Cisco bug ID CSCsl85798 (registered customers only) —After DFS event, WGB does not rescan
-
Cisco bug ID CSCsm37686 (registered customers only) —WGB configured for TKIP-only cannot assoc to (WPA+TKIP)+(WPA2+AES)
-
Cisco bug ID CSCsk85945 (registered customers only) —WPA1 WGB can't associate to a WPA1+WPA2 WLAN
-
Cisco bug ID CSCsk52437 (registered customers only) —WGB retransmit fails when AP goes offchannel
-
Cisco bug ID CSCsb85791 (registered customers only) —1130 crashes just after installation of the new image
-
Cisco bug ID CSCsk63882 (registered customers only) —Bad Id error with traceback seen when 12.4-Based 802.11 AP comes up
-
Cisco bug ID CSCsl36227 (registered customers only) —Tracebacks on WGB: %SM-4-BADEVENT: Event 'eapResp' is invalid
-
Cisco bug ID CSCsl46209 (registered customers only) —WGB 1242 11g radio stuck in reset, stops transmitting
-
Cisco bug ID CSCsl58071 (registered customers only) —WGB intermittently takes a long time to reauthenticate in EAP-TLS
-
-
WLC that runs version 4.2.99.0
It is important to use 4.1.185.0 or later for this reason:
-
Cisco bug ID CSCsk41360 (registered customers only) —Controller continues processing EAPOL LOGOFF after receiving EAPOL
-
Note: You need to be a registered customer in order to view the details of the bug.
The ACS was running 4.1; the CA was running Microsoft Windows 2003 Advanced Server SP1. In all cases, when you browsed to the CA, the client browser was Internet Explorer with Active X enabled.
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Conventions
Refer to the Cisco Technical Tips Conventions for more information on document conventions.
Configuration Overview
-
Configure the Certificates of the WGB
-
Set the hostname, domain name and time as needed
-
Configure the trustpoint.
-
Install the CA certificate.
-
Generate the AP certificate request.
-
Send the AP certificate request to the CA.
-
Issue the certificate.
-
Install the AP certificate.
-
Configure
In this section, you are presented with the information to configure the features described in this document.
Note: Use the Command Lookup Tool (registered customers only) in order to obtain more information on the commands used in this section.
Bring up the Microsoft CA (If Necessary)
Complete these steps in order to open the Microsoft CA with the use of Windows 2003 Advanced Server:
-
First, have IIS installed. Choose Control Panel > Add/Remove Programs > Windows Components > Application Server.
-
Then, install the CA. Choose Control Panel > Add Remove Programs > Windows Components > Certificate Services.
-
Choose an Enterprise Root CA.
-
Give the CA a name, and make a note of it.
-
Install the Server Certificate in the ACS
Complete these steps in order to install the server certificate in the ACS.
-
From a browser that runs on the ACS server, browse to the CA: http://ip.of.CA.server/certsrv
-
Request a Certificate > Advanced Request > Create and Submit a request to this CA.
-
In the Name (CN) field, enter something. Make a note of it.
-
In the Type of Certificate Needed drop-down menu, choose Server Authentication Certificate.
-
Under key options, choose:
-
CSP — Microsoft Base Cryptographic Provider v1.0
-
Key size — 1024
-
Check Mark keys as exportable.
-
Check Store cert in the local computer cert store.
-
-
Leave everything else as default, and click Submit.
-
You should see a Certificate Pending status report that says Your certificate request has been received. If you have a problem, see MS KB 323172, or other things that can get in the way of Active X.
-
-
Now, on the CA, go into the CA admin utility and choose Start > Administrative Tools > Certification Authority.
-
On the left, expand the CA icon, and look under Pending Requests.
-
On the right, right-click the request from the ACS and choose All Tasks > Issue. The request should now appear under Issued Certificates.
-
-
Back on the ACS server, browse again to http://ip.of.CA.server/certsrv.
-
Click View the status of a pending certificate request.
-
Click Server Authentication Certificate.
-
Click Install this certificate.
-
Install the CA Certificate on the ACS
Complete these steps:
From a browser that runs on the ACS server, browse to the CA: http://ip.of.CA.server/certsrv
-
Click Download a CA certificate, certificate chain, or CRL.
-
Choose Encoding method: Base 64.
-
Choose Download CA certificate.
-
Open the .cer file, then click Install Certificate.
-
In the Certificate Import Wizard, click Next, then Place all certificates in the following store, then Browse.
-
Check the Show physical stores box.
-
Expand Trusted root certification authorities, choose Local Computer, and click Ok.
-
Click Next, FINISH, and OK for The import was successful box.
Setup the ACS to Use the Server Certificate
Complete these steps:
-
On the ACS server, choose System Configuration.
-
Choose ACS Certificate Setup.
-
Choose Install ACS certificate.
-
Choose Use certificate from storage.
-
Type in the CN name, the same name that was used in a previous step.
-
Click Submit.
-
In the ACS server, click System configuration.
-
Choose ACS Certificate Setup.
-
Choose Edit Certificate Trust List.
-
Check the box for the CA.
-
Click Submit.
Configure ACS to Let the WGB authenticate in EAP-TLS
Complete these steps in order to configure the ACS to let the WGB authenticate in ACS:
-
Add the WLC as a NAS (AAA client).
-
In the ACS GUI, click Network Configuration on the left.
-
Under AAA Clients, click Add Entry.
-
Enter a name under AAA Client Hostname.
-
Enter the management interface IP address of the WLC under AAA Client IP Address.
-
Enter the RADIUS key under Shared Secret and make a note of it.
-
In the Authenticate Using drop-down menu, choose RADIUS (Cisco Airespace).
-
Click Submit+Apply.
-
-
Enable EAP-TLS in ACS.
-
Choose System Configuration > Global Authentication Setup.
-
Under EAP-TLS, for example, the top-level EAP-TLS, after EAP-FAST, not the EAP-TLS under PEAP, check Allow EAP-TLS.
-
Check all three of the certificate verification options.
-
Choose Submit + Restart.
-
-
Add the WGB as an ACS.
-
In User Setup, enter the name of the WGB in the User panel, and click Add/Edit. This example uses "WGB".
-
Enter a hard-to-guess password. This is required, although not used in EAP-TLS.
-
Click Submit.
-
Configure the WLAN of the WLC to Authenticate to ACS
Complete these steps:
-
Browse to the GUI of the WLC.
-
Add the ACS to the RADIUS server list:
-
Choose Security > AAA > RADIUS > Authentication and click New.
-
Enter the ACS IP address in the Server IP Address panel.
-
Enter the RADIUS shared secret from the previous step.
-
Click Apply.
-
-
Add a WLAN for the EAP-TLS clients:
-
Under WLANs, click New.
-
Enter the SSID as the Profile Name and the WLAN SSID.
-
In the General tab, check the Enabled checkbox, and Broadcast SSID (as desired).
-
Under the Security tab:
-
Under the Layer 2 tab, choose WPA+WPA2 in the Layer 2 Security drop-down menu, check WPA Policy with TKIP encryption, uncheck WPA2 policy with AES encryption, and choose 802.1X for Auth Key Mgmt.
-
Under the AAA Servers, add the ACS, unless the ACS is the global default RADIUS server.
-
-
Click Apply.
-
Configure the Certificates of the WGB
Complete these steps:
Note: This method uses the copy-and-paste method. Refer to Configuring Certificates Using the crypto pki CLI in the Cisco 3200 Series Wireless MIC Software Configuration Guide for more information on how to use the TFTP and SCEP methods.
-
Set the hostname, domain name and time of the WGB as needed.
-
The hostname must match the username entered for it in ACS as in the previous step:
ap#configure terminal ap(config)#hostname WGB WGB(config)#
-
The time must be correct, for the certifications to work (clock set exec CLI, or configure an sntp server).
-
-
Configure the trustpoint for the CA:
WGB#config term WGB(config)#crypto pki trustpoint CUT-PASTE WGB(config)#enrollment terminal WGB(config)#subject-name CN=WGB
Note: subject-name CN=<ClientName> is required. Without it, the Microsoft CA fails to issue the cert, with the The request subject name is invalid or too long. 0x80094001 error message.
WGB(config)#revocation-check none
Note: The revocation-check none command is necessary to avoid the problem described in Cisco bug ID CSCsl07349 (registered customers only) . WGB disassociates/reassociates often and takes a long time to reconnect.
WGB(config)#rsakeypair manual-keys 1024
-
Install the CA cert on the WGB:
-
Get a copy of the CA cert:
-
Browse to the CA: http://ip.of.CA.server/certsrv
-
Click Download a CA certificate, certificate chain, or CRL.
-
Choose Encoding method: Base 64.
-
Click Download CA certificate.
-
Save the .cer file.
-
-
Install the CA cert:
WGB(config)#crypto pki authenticate CUT-PASTE Enter the base 64 encoded CA certificate. End with a blank line or the word "quit" on a line by itself
Now, paste in the text from the .cer file downloaded in the previous step.
-----BEGIN CERTIFICATE----- [ ... ] -----END CERTIFICATE----- quit Certificate has the following attributes: Fingerprint: 45EC6866 A66B4D8F 2E05960F BC5C1B76 % Do you accept this certificate? [yes/no]: yes Trustpoint CA certificate accepted. % Certificate successfully imported
-
-
Request and install the client certificate on the WGB:
-
Generate the certificate request on the WGB:
WGB(config)#crypto pki enroll CUT-PASTE % Start certificate enrollment .. % The subject name in the certificate will include: CN=WGB % Include the router serial number in the subject name? [yes/no]: no % Include an IP address in the subject name? [no]: no Display Certificate Request to terminal? [yes/no]: yes Certificate Request follows: MIIBjzCB+QIBADAvMQwwCgYDVQQDEwNXR0IxHzAdBgkqhkiG9w0BCQIWEFdHQi5j Y2lld2lmaS5jb20wgZ8wDQYJKoZIhvcNAQEBBQADgY0AMIGJAoGBAMuyZ0Y/xI3O 6Pwch3qA/JoBobYcvKHlc0B0qvqPgCmZgNb8nsFDV8ZFQKb3ySdIxlqOGtrn/Yoh 2LHzRKi+AWQHFGAB2vkFD0SJD8A6+YD/GqEdXGoo/e0eqJ7LgFq0wpUQoYlPxsPn QUcK9ZDwd8EZNYdxU/jBtLG9MLX4gta9AgMBAAGgITAfBgkqhkiG9w0BCQ4xEjAQ MA4GA1UdDwEB/wQEAwIFoDANBgkqhkiG9w0BAQQFAAOBgQAsCItCKRtu16JmG4rz cDROO1QdmNYDuwkswHRgSHDMjVvBmoqA2bKeNsTj+svuX5S/Q2cGbzC6OLN/ftQ7 fw+RcKKm8+SpaEnU3eYGs3HhY7W9L4MY4JkY8I89ah15/V82SoIAOfCJDy5BvBP6 hk7GAPbMYkW9wJaNruVEvkYoLQ== ---End - This line not part of the certificate request--- Redisplay enrollment request? [yes/no]: no WGB(config)#
-
Request the Client/User certificate to the CA with the output previously gathered. Use a PC with access to the CA and request the User certificate using this method:
-
Browse to the CA: http://ip.of.CA.server/certsrv
-
Choose the "Request a certificate" option.
-
Choose the "advanced certificate request" option.
-
Choose the "Submit a certificate request by using a base-64-encoded CMC or PKCS #10 files, or submit a renewal request by using a base-64-encoded PKCS #7 file" option.
-
Paste in the certificate request that IOS generated from the "crypto pki enroll" command previously used, and just submit the request.
-
Finally, just download the certificate as "Base 64 encoded".
Note: You need to make sure that the certificate was actually generated for the WGB, with the Subject having "WGB" (the username you provided to the WGB) as the CN.
-
-
Install the user certificate on the WGB:
WGB(config)#crypto pki import CUT-PASTE certificate Enter the base 64 encoded certificate. End with a blank line or the word "quit" on a line by itselfNow, paste in the text from the .cer file downloaded in the previous step.
-----BEGIN CERTIFICATE----- [ ... ] -----END CERTIFICATE----- % Router Certificate successfully imported
-
-
Verify the certifications from the WGB CLI:
WGB#show crypto pki certificates Certificate Status: Available Certificate Serial Number: 1379B07200000000000C Certificate Usage: General Purpose Issuer: cn=AARONLAB Subject: Name: WGB cn=WGB CRL Distribution Points: http://wcswin/CertEnroll/AARONLAB.crl Validity Date: start date: 11:33:09 MST Mar 3 2008 end date: 11:43:09 MST Mar 3 2009 Associated Trustpoints: COPY-PASTE CA Certificate Status: Available Certificate Serial Number: 612683248DBA539B44B039BD51CD1D48 Certificate Usage: Signature Issuer: cn=AARONLAB Subject: cn=AARONLAB CRL Distribution Points: http://wcswin/CertEnroll/AARONLAB.crl Validity Date: start date: 16:34:48 MST Feb 28 2008 end date: 16:41:25 MST Feb 28 2018 Associated Trustpoints: COPY-PASTE
Configure the WGB SSID, Supplicant and Radio as Needed
Complete these steps:
-
Configure the SSID. This should match the SSID configured on the WLC in this previous step:
dot11 ssid EAPTLS authentication network-eap eap_methods authentication key-management wpa version 1 dot1x credentials EAPTLS dot1x eap profile EAPTLS infrastructure-ssid
-
Configure the EAP-TLS supplicant. The username must match the CN on the trustpoint and the username entry in ACS.
eap profile EAPTLS method tls ! dot1x credentials EAPTLS username WGB pki-trustpoint CUT-PASTE
-
Configure the radio interface as needed. In this example, the 2.4 GHz radio (Dot11Radio0) is used.
interface Dot11Radio0 encryption mode ciphers aes-ccm tkip ssid EAPTLS ! packet retries 128 drop-packet station-role workgroup-bridge
Note: With packet retries 128 drop-packet, the WGB remains associated to its root AP as long as it can, so this is a suitable configuration for an immobile WGB. For a WGB that is physically roaming, these configurations can be used, in order of increasingly aggressive roaming:
packet retries 128
Note: or
packet retries 128 mobile station period 5 threshold 82 (tune the mobile station command as needed for a specialized application)
Configure Entries for a Passive Client (If Necessary)
If one or more "passive clients" are behind the WGB, for example, wired devices that have static IP addresses and that do not continuously transmit unsolicited IP data, then special steps need to be taken in order to ensure that the WGB and the CUWN can find those clients. In this example, the client has an IP address of 10.0.47.66 and a MAC address of 0040.96b4.7e8f.
Complete these steps in order to use this method:
-
Configure a static bridge entry on the WGB for the client:
B(config)#bridge 1 address 0040.96b4.7e8f forward fastethernet0
-
Configure a static MAC-to-IP address mapping on the WLC:
-
Configure the WLAN in order to enable MAC filtering, AAA override, and not to require DHCP:
(Cisco Controller) >show wlan summary !--- Make a note of the WLAN ID for the SSID used for EAP-TLS. (Cisco Controller) >config wlan disable 6 (Cisco Controller) >config wlan mac-filtering enable 6 (Cisco Controller) >config wlan aaa-override enable 6 (Cisco Controller) >config wlan dhcp_server 6 0.0.0.0 !--- Do not have DHCP required checked.
-
Add the MAC filter (MAC-to-IP mapping) for each client:
(Cisco Controller) >config macfilter add 0040.96b4.7e8f 6 management "client1" 10.0.47.66
-
Special Notes if 802.11a (5 GHz) is Used
Since 802.11a supports many more channels than 802.11b/g (2.4 GHz), it can take the WGB much longer to scan all available channels. Therefore, outages while you roam in 5 GHz, or after a connectivity problem to the root AP, can last for several seconds. Additionally, if you use DFS channels, channel scanning can take much longer, and brief outages after a DFS radar detection event can occur.
It is therefore recommended that if you use 802.11a, you should avoid the use of DFS channels, for example, in the FCC domain, and to use only the UNII-1 and UNII-3 bands. The Dot11Radio1 interface of the WGB should also be configured to scan only the channels in use in the coverage area. For example:
WGB(config-if)#mobile station scan 36 40 44 48 149 153 157
Configurations
Here is an example WGB configuration for an AP1242, that uses Cisco IOS Software Release 12.4(10b)JA2, EAP-TLS authentication with WPA1-TKIP, 2.4 GHz.
Note: Some lines of this configuration have been moved to the second line due to space constraints.
version 12.4 no service pad service timestamps debug datetime msec service timestamps log datetime msec no service password-encryption ! hostname WGB ! logging buffered 200000 debugging enable secret 5 $1$xPtX$hjxzdWVR9qa4ykoxLYba91 ! no aaa new-model clock timezone MST -7 ! ! ! dot11 ssid EAPTLS authentication network-eap eap_methods authentication key-management wpa version 1 dot1x credentials EAPTLS dot1x eap profile EAPTLS infrastructure-ssid ! power inline negotiation prestandard source eap profile EAPTLS method tls ! ! crypto pki trustpoint COPY-PASTE enrollment terminal subject-name CN=WGB revocation-check none rsakeypair manual-keys 1024 ! ! crypto pki certificate chain COPY-PASTE certificate 1379B07200000000000C [...] quit certificate ca 612683248DBA539B44B039BD51CD1D48 [...] quit dot1x credentials EAPTLS username WGB pki-trustpoint COPY-PASTE ! username Cisco password 0 Cisco ! bridge irb ! ! interface Dot11Radio0 no ip address no ip route-cache ! encryption mode ciphers tkip ! ssid EAPTLS ! packet retries 128 drop-packet station-role workgroup-bridge no dot11 qos mode bridge-group 1 bridge-group 1 spanning-disabled ! interface Dot11Radio1 no ip address no ip route-cache shutdown ! station-role root bridge-group 1 bridge-group 1 subscriber-loop-control bridge-group 1 block-unknown-source no bridge-group 1 source-learning no bridge-group 1 unicast-flooding bridge-group 1 spanning-disabled ! interface FastEthernet0 no ip address no ip route-cache duplex auto speed auto bridge-group 1 bridge-group 1 spanning-disabled ! interface BVI1 ip address dhcp client-id FastEthernet0 no ip route-cache ! ip http server no ip http secure-server ip http help-path bridge 1 route ip ! ! ! line con 0 line vty 0 4 login local ! sntp server 10.0.47.1 end |
Synchronize the Cisco IOS supplicant's clock and save its time to NVRAM (for systems with Cisco IOS Software Release 12.4(21a)JY)
A Cisco IOS device whose supplicant is configured to perform certificate-based authentication of its network connection, which device is hereafter referred to as the Supplicant, may be unable to connect to the network, unless these steps are taken.
In order to make sure that the Supplicant, after a reload but before it has connected to the network, knows approximately what time it is, so that it can validate the certificate of the server, you must configure the Supplicant to learn the time from an NTP server, and to write the time to its NVRAM. This is a requirement for any system that runs Cisco IOS Software Release 12.4(21a)JY.
Complete these steps:
-
Configure the Supplicant to synchronize its time to a known good NTP server, to which the Supplicant has network access, and to store its time into its NVRAM.
Example 1.1. (on a system with SNTP, and without a hardware calendar):
Supp(config)#sntp server 10.0.47.1 Supp(config)#clock save interval 8 Supp(config)#end Supp#write memory
Example 1.2. (on a system with NTP, and with a hardware calendar):
Supp(config)#ntp server 10.0.47.1 iburst Supp(config)#ntp update-calendar Supp(config)#end Supp#write memory
-
Make sure that the Supplicant has network connectivity to the NTP server and has synchronized its time.
Example 2.1:
Supp#show sntp SNTP server Stratum Version Last Receive 10.0.47.1 3 1 00:00:09 Synced
Example 2.2:
Supp#show ntp status Clock is synchronized, stratum 4, reference is 10.95.42.129 [ ... ]
-
Make sure that the correct time is saved to the hardware calendar of the Supplicant if it has one, or to NVRAM if it does not.
Example 3.1. On a system with no hardware calendar:
Reload the Supplicant in order to make sure that the time is saved to NVRAM. After it reloads, verify that the time is approximately correct, even when the NTP server is unavailable:
Supp#show clock detail *08:24:30.103 -0700 Thu Apr 15 2010 No time source
Example 3.2. On a system with hardware calendar:
Write the current, correct time to the hardware calendar:
Supp#clock update-calendar
Verify that the calendar is correct:
Supp#show calendar
Verify
Use this section to confirm that your configuration works properly.
The Output Interpreter Tool (registered customers only) (OIT) supports certain show commands. Use the OIT to view an analysis of show command output.
Verify the WGB connection.
On the WLC, the radio MAC address of the WGB should appear as an Associated client. For example:
(Cisco Controller) >show client summary
Number of Clients................................ 5
MAC Address AP Name Status WLAN/ Auth Protocol Port Wired
Guest-Lan
----------------- --------------- ---------- --------- ---- -------- ---- -----
00:00:39:dd:4d:24 AP0019.e802.3034 Associated 6 Yes N/A 4 No
00:0e:9b:cb:d3:9c AP0019.e802.3034 Associated 1 No 802.11b 4 No
00:16:6f:50:e1:25 AP0019.e802.3034 Probing N/A No 802.11b 4 No
00:19:56:b0:7e:b6 AP0019.e802.3034 Associated 6 Yes 802.11b 4 No
00:40:96:b4:7e:8f AP0019.e802.3034 Associated 6 Yes N/A 4 No
Use "show client detail <MAC>" to see more information on the WGB:
(Cisco Controller) >show client detail 00:19:56:b0:7e:b6
Client MAC Address............................... 00:19:56:b0:7e:b6
Client Username ................................. WGB
AP MAC Address................................... 00:19:a9:42:e4:10
Client State..................................... Associated
Workgroup Bridge................................. 2 client(s)
Wireless LAN Id.................................. 6
BSSID............................................ 00:19:a9:42:e4:15
Channel.......................................... 1
IP Address....................................... 10.0.47.23
On the WGB, you can use the show dot11 associations and show dot11 associations all-clients commands in order to see more detail about the association to the AP. Use the ping w.x.y.z command in order to ping the WGB's default gateway.
Verify the WGB's client connectivity.
On the WGB, you can use the show bridge 1 fastethernet0 command in order to see addresses learned through the FastEthernet0 interface:
WGB.Cisco.COM#show bridge 1 fastethernet0
Total of 300 station blocks, 292 free
Codes: P - permanent, S - self
Bridge Group 1:
Address Action Interface Age RX count TX count
0000.39dd.4d24 forward FastEthernet0 1 328 71
0040.96b4.7e8f forward FastEthernet0 P 0 352
On the WLC, the WGB's wired clients will show up as associated clients with
protocol "N/A":
(Cisco Controller) >show client summary
Number of Clients................................ 5
MAC Address AP Name Status WLAN/ Auth Protocol Port Wired
Guest-Lan
----------------- --------------- ---------- --------- ---- -------- ---- -----
00:00:39:dd:4d:24 AP0019.e802.3034 Associated Yes N/A 4 No
00:0e:9b:cb:d3:9c AP0019.e802.3034 Associated 1 No 802.11b 4 No
00:16:6f:50:e1:25 AP0019.e802.3034 Probing N/A No 802.11b 4 No
00:19:56:b0:7e:b6 AP0019.e802.3034 Associated 6 Yes 802.11b 4 No
00:40:96:b4:7e:8f AP0019.e802.3034 Associated 6 Yes N/A 4 No
(Cisco Controller) >show client detail 00:00:39:dd:4d:24
Client MAC Address.............................. 00:00:39:dd:4d:24
Client Username ................................ N/A
AP MAC Address.................................. 00:19:a9:42:e4:10
Client State.................................... Associated
Workgroup Bridge Client......................... WGB: 00:19:56:b0:7e:b6
Wireless LAN Id................................. 6
BSSID........................................... 00:19:a9:42:e4:15
Channel......................................... 1
Troubleshoot
This section provides information you can use to troubleshoot your configuration.
Troubleshooting Commands
The Output Interpreter Tool (registered customers only) (OIT) supports certain show commands. Use the OIT to view an analysis of show command output.
Note: Refer to Important Information on Debug Commands before you use debug commands.
Debugging Examples
WGB-side example
On the WGB, this example assumes 2.4 GHz; if you use 5 GHz, specify Dot11Radio1 instead of Dot11Radio0.
WGB#no debug dot11 dot11radio0 print printf !--- This runs the radio debugs through !--- the standard Cisco IOS logger. WGB#debug dot11 dot11radio0 trace print mgmt uplink !--- radio driver debugs: 802.11 management frames !--- and uplink events WGB#debug dot11 supp-sm-dot1x !--- interface to the 802.1X supplicant
Here is an example of a normal association given in the previous configuration:
| WGB-side Example |
|---|
Mar 4 23:22:39.427: 108DD0BF-0 Uplink: Enabling active scan
Mar 4 23:22:39.427: 108DD0D0-0 Uplink: Not busy, scan all channels
Mar 4 23:22:39.427: 108DD0DE-0 Uplink: Scanning
Mar 4 23:22:39.430: 108DDF83-0 Uplink: Rcvd response from 0019.a942.e415
channel 1 3237
!--- WGB scans the 2.4 GHz channels, !--- found an AP on channel 1.
Mar 4 23:22:39.470: 108E7B31-0 Uplink: dot11_uplink_scan_done: ssnie_accept
returns 0x0 key_mgmt 0x50F201 encrypt_type 0x20
Mar 4 23:22:39.470: 108E7B67-0 Uplink: ssid EAPTLS auth leap
Mar 4 23:22:39.471: 108E7B77-0 Uplink: try 0019.a942.e415, enc 20 key 1,
priv 1, eap 11
Mar 4 23:22:39.471: 108E7B93-0 Uplink: Authenticating
Mar 4 23:22:39.479: 108E9C71 t 1 0 - B000 13A 42E415 B07EB6 42E415 D9E0
auth l 6
algorithm 128
sequence 1
status 0
Mar 4 23:22:39.480: 108EA160 r 1 73/ 26- B000 13A B07EB6 42E415 42E415 5E70
auth l 37
algorithm 128
sequence 2
status 0
221 - 0 40 96 C 1 A 22 79 95 1A 7C 18 1 0 0 CA 4 0 0 0 0 74 52 EA
31 F4 9E 89 5A
!--- WGB completes 802.11 authentication.
Mar 4 23:22:39.480: 108EA1EB-0 Uplink: Associating
Mar 4 23:22:39.481: 108EA951 t 1 0 - 0000 13A 42E415 B07EB6 42E415 D9F0
assreq l 119
cap 431 infra privacy shorthdr
listen interval 200
ssid EAPTLS
rates 82 84 8B C 12 96 18 24
extrates 30 48 60 6C
aironet WGB.Cisco.COM load 0 clients 0 hops 0 device 7C-2700
refresh 15 CW 0-0 flags 0 distance 0
ccxver 5
221 - 0 40 96 14 0
IP 10.0.47.23 1
wpa1 mcst tkip ucst tkip keymgmt wpa cap 2800
221 - 0 40 96 6 2
Mar 4 23:22:39.484: 108EB2C6 r 1 80/77 19- 1000 13A B07EB6 42E415 42E415
5E80 assrsp l 101
cap 31 infra privacy shorthdr
status 0
aid C003
rates 82 4 B 16
aironet AP0019.e802.303 load 0 clients 0 hops 0 device 8F-2700
refresh 15 CW 31-1023 flags 40 distance 0
IP 10.0.47.6 0
ccxver 5
221 - 0 40 96 14 0
221 - 0 40 96 C 1 A 22 7E 95 1A 7C 18 1 0 0 CB 4 0 0 0 0 FB 4C F3 7D D
29 71 E2
!--- WGB completes 802.11 association.
Mar 4 23:22:39.486: Uplink address set to 0019.a942.e415
Mar 4 23:22:39.486: Initialising common IOS structures for dot1x
Mar 4 23:22:39.486: Done.
Mar 4 23:22:39.486: DOT1X_SHIM: Start supplicant on Dot11Radio0
(credentials EAPTLS)
Mar 4 23:22:39.486: DOT1X_SHIM: Starting dot1x_mgr_auth (auth type 128)
Mar 4 23:22:39.486: DOT1X_SHIM: Initialising WPA [or WPA-PSK or CCKM]
key management module
!--- Starting the EAP-TLS supplicant
Mar 4 23:22:39.488: DOT1X_SHIM: Dot1x pkt sent (uplink)
with dest 0019.a942.e415
Mar 4 23:22:39.489: DOT1X_SHIM: No AAA client found for 0019.a942.e415
(on Dot11Radio0)
Mar 4 23:22:39.489: DOT1X_SHIM: Dot1x pkt sent (uplink)
with dest 0019.a942.e415
Mar 4 23:22:39.490: DOT1X_SHIM: No AAA client found for 0019.a942.e415
(on Dot11Radio0)
!--- The "No AAA client found" message appears !--- to be a bogon and can be ignored.
Mar 4 23:22:39.491: DOT1X_SHIM: Dot1x pkt sent (uplink)
with dest 0019.a942.e415
Mar 4 23:22:39.491: 108EB9B4-0 Uplink: EAP authenticating
Mar 4 23:22:39.491: 108EBD22 r 11 73/ 4 - 0802 13A B07EB6 42E415 42E415
5E90 l64
0100 0034 0101 0034 0100 6E65 7477 6F72 6B69 643D 4541 5054 4C53 2C6E
6173 6964 3D74 7563 736F 6E2D 776C 6332 3030 362C 706F 7274 6964 3D34 0000
Mar 4 23:22:39.492: 108EC770 t 11 0 - 0801 13A 42E415 B07EB6 42E415
DA00 l68
EAPOL2 EAPOL start
Mar 4 23:22:39.492: 108ECA4D r 11 74/ 18- 0802 13A B07EB6 42E415 42E415
5EA0 l64
0100 0034 0102 0034 0100 6E65 7477 6F72 6B69 643D 4541 5054 4C53 2C6E
6173 6964 3D74 7563 736F 6E2D 776C 6332 3030 362C 706F 7274 6964 3D34 0000
Mar 4 23:22:39.492: 108ECDE2 t 11 0 - 0801 13A 42E415 B07EB6 42E415
DA10 l68
EAPOL2 EAP id 1 resp ident "WGB"
Mar 4 23:22:39.493: 108ED000 t 11 0 - 0801 13A 42E415 B07EB6 42E415
DA20 l68
EAPOL2 EAP id 2 resp ident "WGB"
Mar 4 23:22:39.524: 108F50C4 r 11 74/ 18- 080A 13A B07EB6 42E415 42E415
5EC0 l31
0100 0013 01AF 0013 1101 0008 E23F 829E AE45 57EB 5747 4200 0000 0000
0000 00
!--- The WGB sends an EAPOL START, !--- the WLC authenticator sends an EAP ID Request, !--- and the WGB responds with an EAP ID response.
Mar 4 23:22:39.525: DOT1X_SHIM: No AAA client found for 0019.a942.e415
(on Dot11Radio0)
Mar 4 23:22:39.525: DOT1X_SHIM: Dot1x pkt sent (uplink)
with dest 0019.a942.e415
Mar 4 23:22:39.526: 108F57D0 t 11 0 - 0801 13A 42E415 B07EB6 42E415
DA30 l68
EAPOL2 EAP id 175 resp nak 0D
Mar 4 23:22:39.547: 108FA89C r 11 86/77 19- 080A 13A B07EB6 42E415 42E415
5ED0 l18
0100 0006 01B0 0006 0D20 0000 0000 0000 0000
Mar 4 23:22:39.547: DOT1X_SHIM: No AAA client found for 0019.a942.e415
(on Dot11Radio0)
Mar 4 23:22:39.561: DOT1X_SHIM: Dot1x pkt sent (uplink)
with dest 0019.a942.e415
Mar 4 23:22:39.561: 108FE059 t 11 0 - 0801 13A 42E415 B07EB6 42E415
DA40 l86
EAPOL2 EAP id 176 resp tls 8000 0000 3216 0301 002D 0100 0029 0301 47CD
D9BF CE1B 71B1 A815 CB99 8C80 8876 39F2 57A3 0F02 F382 147E 9D0C 657E 3AA7
Mar 4 23:22:39.572: DOT1X_SHIM: No AAA client found for 0019.a942.e415
(on Dot11Radio0)
Mar 4 23:22:39.573: DOT1X_SHIM: Dot1x pkt sent (uplink)
with dest 0019.a942.e415
Mar 4 23:22:39.573: 10900868 r 11 86/77 20- 0802 13A B07EB6 42E415 42E415
5EF0 l1024
0100 03F4 01B1 03F4 0DC0 0000 079D 1603 0100 4A02 0000 4603 0147 CDD9
B413 0683 9734 4D26 136F EC8F ECD3 5D3B 77C7 4D20 7DA1 9B17 D7D3 E4A6 1720
Mar 4 23:22:39.574: 109012E6 t 11 1 - 0809 13A 42E415 B07EB6 42E415
DA50 l68
EAPOL2 EAP id 177 resp tls 00
Mar 4 23:22:39.582: DOT1X_SHIM: No AAA client found for 0019.a942.e415
(on Dot11Radio0)
Mar 4 23:22:39.734: DOT1X_SHIM: Dot1x pkt sent (uplink)
with dest 0019.a942.e415
Mar 4 23:22:39.735: 1090317E r 11 /78 19- 0802 13A B07EB6 42E415 42E415
5F00 l965
0100 03B9 01B2 03B9 0D00 C687 1DB6 065B 2467 2609 EE5F 9C64 F3A9 C199
493E 2B79 F157 1765 6C2F C409 4D54 7DA4 6791 4859 ECAA 685B 0F66 C5E9 22A6
Mar 4 23:22:39.736: 10928A31 t 11 0 - 0801 13A 42E415 B07EB6 42E415
DA60 l1239
EAPOL2 EAP id 178 resp tls 8000 0004 B316 0301 036D 0B00 0369 0003 6600
0363 3082 035F 3082 0247 A003 0201 0202 0A13 79B0 7200 0000 0000 0C30 0D06
Mar 4 23:22:39.755: 1092D464 r 11 /78 18- 0802 13A B07EB6 42E415
42E415 5F40 l65
0100 0035 01B3 0035 0D80 0000 002B 1403 0100 0101 1603 0100 20B8 EBFA
2DDB 2E1A BF84 37A8 892C 84C5 50B2 B1A5 6F3E B2B5 981A 2899 1DE2 B470 6800
Mar 4 23:22:39.755: DOT1X_SHIM: No AAA client found for 0019.a942.e415
(on Dot11Radio0)
Mar 4 23:22:39.760: DOT1X_SHIM: Dot1x pkt sent (uplink)
with dest 0019.a942.e415
Mar 4 23:22:39.760: 1092E92C t 11 0 - 0801 13A 42E415 B07EB6 42E415
DA70 l68
EAPOL2 EAP id 179 resp tls 00
Mar 4 23:22:39.770: 10930F50 r 11 75/80 19- 0802 13A B07EB6 42E415 42E415
5F60 l16
0100 0004 03B3 0004 0000 0000 0000 0000
Mar 4 23:22:39.770: DOT1X_SHIM: No AAA client found for 0019.a942.e415
(on Dot11Radio0)
Mar 4 23:22:39.774: DOT1X_SHIM: Received Dot1x success - Authenticated
with EAP-TLS
!--- EAP-TLS authentication is successful, !--- now come the keys.
Mar 4 23:22:39.774: DOT1X_SHIM: treat key material as wpa-v1 v2 pmk
Mar 4 23:22:39.774: DOT1X_SHIM: WPA PMK key size truncated from 64 to 32
Mar 4 23:22:39.777: DOT1X_SHIM: Got Eapol key packet from dot1x manager
Mar 4 23:22:39.777: DOT1X_SHIM: Passing key packet to KM module
Mar 4 23:22:39.777: supp_km_processKey: descriptor type = 254
Mar 4 23:22:39.777: supp_km_processKey: key length = 137
Mar 4 23:22:39.778: 109319B7 r 11 /77 16- 080A 13A B07EB6 42E415 42E415
5F70 l107
0103 005F FE00 8900 2000 0000 0000 0000 006E 64D0 C659 1C91 11D2 6040
C251 0592 E6B6 3799 0EDE B1BD B3A6 87B7 8C9B 0D5E DF00 0000 0000 0000 0000
Mar 4 23:22:39.779: 109332C2 t 11 1 - 0809 13A 42E415 B07EB6 42E415
DA80 l133
EAPOL key desc FE info 109 len 20 replay 0000000000000000
nonce 11AADA303F5F9B2357A932B3093483905E69F8408D019FB2EF56F7AD706F0759
iv 00000000000000000000000000000000 rsc 0000000000000000
id 0000000000000000 mic DBD06C383B83E3478F802844095E9444
datalen 1A key DD18 0050 F201 0100 0050 F202 0100 0050 F202 0100
0050 F201
2800
Mar 4 23:22:39.780: 109336C1 r 11 83/78 18- 0802 13A B07EB6 42E415 42E415
5F80 l133
0103 0079 FE01 C900 2000 0000 0000 0000 016E 64D0 C659 1C91 11D2 6040
C251 0592 E6B6 3799 0EDE B1BD B3A6 87B7 8C9B 0D5E DF6E 64D0 C659 1C91 11D2
Mar 4 23:22:39.781: DOT1X_SHIM: Got Eapol key packet from dot1x manager
Mar 4 23:22:39.781: DOT1X_SHIM: Passing key packet to KM module
Mar 4 23:22:39.781: supp_km_processKey: descriptor type = 254
Mar 4 23:22:39.781: supp_km_processKey: key length = 457
Mar 4 23:22:39.781: dot1x_pakio_plumb_keys: trying to plumb PTK key
Mar 4 23:22:39.782: 10933E11 t 11 0 - 0801 13A 42E415 B07EB6 42E415
DA90 l107
EAPOL key desc FE info 109 len 20 replay 0000000000000001
nonce 0000000000000000000000000000000000000000000000000000000000000000
iv 00000000000000000000000000000000 rsc 0000000000000000
id 0000000000000000 mic 3A59680D1130EC24B00F7246F9D0738F
datalen 0 key
Mar 4 23:22:39.785: 10934749 r 11 88/77 17- 0842 13A B07EB6 42E415 42E415
5F90 l155
IV 0103007F-FE039100 2000 0000 0000 0000 026E 64D0 C659 1C91 11D2 6040
C251 0592 E6B6 3799 0EDE B1BD B3A6 87B7 8C9B 0D5E D76E 64D0 C659 1C91 11D2
Mar 4 23:22:39.785: DOT1X_SHIM: Got Eapol key packet from dot1x manager
Mar 4 23:22:39.785: DOT1X_SHIM: Passing key packet to KM module
Mar 4 23:22:39.785: supp_km_processKey: descriptor type = 254
Mar 4 23:22:39.785: supp_km_processKey: key length = 913
Mar 4 23:22:39.786: dot1x_pakio_plumb_keys: trying to plumb vlan
key - length: 32
Mar 4 23:22:39.787: %DOT11-4-UPLINK_ESTABLISHED: Interface Dot11Radio0,
Associated To AP AP0019.e802.303 0019.a942.e415 [EAP-TLS WPA]
Mar 4 23:22:39.787: %LINK-3-UPDOWN: Interface Dot11Radio0, changed state to up
Mar 4 23:22:39.789: 10934D63-0 Uplink: Done
Mar 4 23:22:39.789: 10934D94-0 Interface up
Mar 4 23:22:39.790: 10934ED7 t 11 0 - 0841 13A 42E415 B07EB6 42E415
DAA0 l115
EAPOL key desc FE info 311 len 0 replay 0000000000000002
nonce 0000000000000000000000000000000000000000000000000000000000000000
iv 00000000000000000000000000000000 rsc 0000000000000000
id 0000000000000000 mic DA60CCDAE27E7362B9B720B52715E081
datalen 0 key
!--- The keys are all distributed, !--- and the Dot11Radio0 interface is fully up.
|
WLC-side Debugs
| WLC-side Example |
|---|
(Cisco Controller) >debug mac addr
00:19:56:b0:7e:b6
!--- Filter debugs on the radio !--- MAC address of the WGB.
(Cisco Controller) >debug dot11 state enable
(Cisco Controller) >debug dot1x events enable
(Cisco Controller) >debug dot1x states enable
(Cisco Controller) >debug pem events enable
(Cisco Controller) >debug pem state enable
(Cisco Controller) >debug aaa packet enable
(Cisco Controller) >debuug aaa events enable
(Cisco Controller) >debug aaa events enable
Tue Mar 4 16:45:56 2008: 00:19:56:b0:7e:b6 Processing WPA IE type 221,
length 24 for mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:56 2008: 00:19:56:b0:7e:b6 10.0.47.23 RUN (20)
Change state to START (0) last state RUN (20)
Tue Mar 4 16:45:56 2008: 00:19:56:b0:7e:b6 10.0.47.23 START (0)
Initializing policy
Tue Mar 4 16:45:56 2008: 00:19:56:b0:7e:b6 10.0.47.23 START (0)
Change state to AUTHCHECK (2) last state RUN (20)
Tue Mar 4 16:45:56 2008: 00:19:56:b0:7e:b6 10.0.47.23 AUTHCHECK (2)
Change state to 8021X_REQD (3) last state RUN (20)
Tue Mar 4 16:45:56 2008: 00:19:56:b0:7e:b6 10.0.47.23 8021X_REQD (3)
Plumbed mobile LWAPP rule on AP 00:19:a9:42:e4:10
Tue Mar 4 16:45:56 2008: 00:19:56:b0:7e:b6 apfPemAddUser2 (apf_policy.c:209)
Changing state for mobile 00:19:56:b0:7e:b6 on
AP 00:19:a9:42:e4:10 from Associated to Associated
Tue Mar 4 16:45:56 2008: 00:19:56:b0:7e:b6 apfProcessAssocReq (apf_80211.c:4149)
Changing state for mobile 00:19:56:b0:7e:b6 on
AP 00:19:a9:42:e4:10 from Associated to Associated
!--- WGB is associated in 802.11. !--- Note in this case that the WGB associated !--- when it was already associated.
Tue Mar 4 16:45:56 2008: 00:19:56:b0:7e:b6 dot1x - moving
mobile 00:19:56:b0:7e:b6 into Connecting state
Tue Mar 4 16:45:56 2008: 00:19:56:b0:7e:b6 Sending EAP-Request/Identity to
mobile 00:19:56:b0:7e:b6 (EAP Id 1)
Tue Mar 4 16:45:56 2008: 00:19:56:b0:7e:b6 10.0.47.23 Removed NPU entry.
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Received EAPOL START from
mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 dot1x - moving
mobile 00:19:56:b0:7e:b6 into Connecting state
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Sending EAP-Request/Identity to
mobile 00:19:56:b0:7e:b6 (EAP Id 2)
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Received EAPOL EAPPKT from
mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Received EAP Response packet with
mismatching id (currentid=2, eapid=1) from mobile
00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Received EAPOL EAPPKT from
mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Received Identity Response (count=2) from
mobile 00:19:56:b0:7e:b6
!--- WGB sends EAPOL START while !--- WLC sends its EAP ID-request, !--- which confuses the state machines for a moment, !--- but eventually we get on track, and the WLC !--- gets its ID-response from the WGB supplicant.
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 EAP State update from Connecting to
Authenticating for mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 dot1x - moving mobile
00:19:56:b0:7e:b6 into Authenticating state
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Entering Backend Auth Response
state for mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Successful transmission of
Authentication Packet (id 17) to 10.0.47.42:1812,
proxy state 00:19:56:b0:7e:b6-00:00
Tue Mar 4 16:45:59 2008: 00000000: 01 11 00 9c 85 82 35 15
62 0f 50 bd 32 60 0c e6 ......5.b.P.2`..
Tue Mar 4 16:45:59 2008: 00000010: de 94 b2 40 01 05 57 47
42 1f 13 30 30 2d 31 39 ...@..WGB..00-19
Tue Mar 4 16:45:59 2008: 00000020: 2d 35 36 2d 42 30 2d 37
45 2d 42 36 1e 1a 30 30 -56-B0-7E-B6..00
Tue Mar 4 16:45:59 2008: 00000030: 2d 31 39 2d 41 39 2d 34
32 2d 45 34 2d 31 30 3a -19-A9-42-E4-10:
Tue Mar 4 16:45:59 2008: 00000040: 45 41 50 54 4c 53 05 06
00 00 00 04 04 06 0a 00 EAPTLS..........
Tue Mar 4 16:45:59 2008: 00000050: 2f 06 20 10 74 75 63 73
6f 6e 2d 77 6c 63 32 30 /...tucson-wlc20
Tue Mar 4 16:45:59 2008: 00000060: 30 36 1a 0c 00 00 37 63
01 06 00 00 00 06 06 06 06....7c........
Tue Mar 4 16:45:59 2008: 00000070: 00 00 00 02 0c 06 00 00
05 14 3d 06 00 00 00 13 ..........=.....
Tue Mar 4 16:45:59 2008: 00000080: 4f 0a 02 02 00 08 01 57
47 42 50 12 c5 f3 f5 9c O......WGBP.....
Tue Mar 4 16:45:59 2008: 00000090: c0 81 0e 3e 23 c0 a7 1b
03 f7 af 5b ...>#......[
Tue Mar 4 16:45:59 2008: 00000000: 0b 11 00 47 54 d3 b6 45
75 eb 83 b7 97 7c 80 1b ...GT..Eu....|..
Tue Mar 4 16:45:59 2008: 00000010: 13 03 71 1d 4f 15 01 b0
00 13 11 01 00 08 3d 17 ..q.O.........=.
Tue Mar 4 16:45:59 2008: 00000020: 4a 94 eb c7 3b 3e 57 47
42 18 0c 53 56 43 3d 30 J...;>WGB..SVC=0
Tue Mar 4 16:45:59 2008: 00000030: 2e 36 34 37 3b 50 12 67
50 d3 ad 88 7d 16 8b 5b .647;P.gP...}..[
Tue Mar 4 16:45:59 2008: 00000040: d1 25 57 56 b2 ec 76.%WV..v
Tue Mar 4 16:45:59 2008: ****Enter processIncomingMessages: response code=11
Tue Mar 4 16:45:59 2008: ****Enter processRadiusResponse: response code=11
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Access-Challenge received from
RADIUS server 10.0.47.42 for mobile 00:19:56:b0:7e:b6
receiveId = 7
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Processing Access-Challenge for
mobile 00:19:56:b0:7e:b6
!--- The WLC forwards the ID-request info, !--- that it had received !--- in 802.1X from the WGB supplicant, to the RADIUS server, !--- in a RADIUS Access-Request packet. !--- The RADIUS server responds with an Access-Challenge. !--- If there is a configuration problem with RADIUS, then either !--- the RADIUS server does not respond, or it responds !--- with a RADIUS Access-Reject. !--- If EAP-TLS goes well, there is much back and forth !--- between the EAP exchange on the wireless !--- link, and the RADIUS exchange between the WLC and ACS.
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Entering Backend Auth Req state
(id=176) for mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 WARNING: updated
EAP-Identifer 2 ===> 176 for STA 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Sending EAP Request from AAA to
mobile 00:19:56:b0:7e:b6 (EAP Id 176)
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Received EAPOL EAPPKT from
mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Received EAP Response from
mobile 00:19:56:b0:7e:b6 (EAP Id 176, EAP Type 3)
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Entering Backend Auth Response
state for mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Successful transmission of
Authentication Packet (id 18) to 10.0.47.42:1812,
proxy state 00:19:56:b0:7e:b6-00:00
Tue Mar 4 16:45:59 2008: 00000000: 01 12 00 a6 d5 64 56 8a
e8 27 fa de ca 69 c4 2a .....dV..'...i.*
Tue Mar 4 16:45:59 2008: 00000010: cd 06 26 0c 01 05 57 47
42 1f 13 30 30 2d 31 39 ..&...WGB..00-19
Tue Mar 4 16:45:59 2008: 00000020: 2d 35 36 2d 42 30 2d 37
45 2d 42 36 1e 1a 30 30 -56-B0-7E-B6..00
Tue Mar 4 16:45:59 2008: 00000030: 2d 31 39 2d 41 39 2d 34
32 2d 45 34 2d 31 30 3a -19-A9-42-E4-10:
Tue Mar 4 16:45:59 2008: 00000040: 45 41 50 54 4c 53 05 06
00 00 00 04 04 06 0a 00 EAPTLS..........
Tue Mar 4 16:45:59 2008: 00000050: 2f 06 20 10 74 75 63 73
6f 6e 2d 77 6c 63 32 30 /...tucson-wlc20
Tue Mar 4 16:45:59 2008: 00000060: 30 36 1a 0c 00 00 37 63
01 06 00 00 00 06 06 06 06....7c........
Tue Mar 4 16:45:59 2008: 00000070: 00 00 00 02 0c 06 00 00
05 14 3d 06 00 00 00 13 ..........=.....
Tue Mar 4 16:45:59 2008: 00000080: 4f 08 02 b0 00 06 03 0d
18 0c 53 56 43 3d 30 2e O.........SVC=0.
Tue Mar 4 16:45:59 2008: 00000090: 36 34 37 3b 50 12 43 6e
32 b6 e9 11 a3 47 8e 96 647;P.Cn2....G..
Tue Mar 4 16:45:59 2008: 000000a0: dc f0 37 a8 37 9e..7.7.
Tue Mar 4 16:45:59 2008: 00000000: 0b 12 00 4b 71 7a 36 1d
d9 24 16 8d c0 2f 45 52 ...Kqz6..$.../ER
Tue Mar 4 16:45:59 2008: 00000010: 82 3d 58 cf 4f 08 01 b1
00 06 0d 20 18 1d 45 41 .=X.O.........EA
Tue Mar 4 16:45:59 2008: 00000020: 50 3d 30 2e 32 30 32 2e
32 37 65 61 2e 31 3b 53 P=0.202.27ea.1;S
Tue Mar 4 16:45:59 2008: 00000030: 56 43 3d 30 2e 36 34 37
3b 50 12 71 bf 1f 5c c7 VC=0.647;P.q..\.
Tue Mar 4 16:45:59 2008: 00000040: 69 7e e8 cc 9d 71 18 de
b7 e5 b7 i~...q.....
Tue Mar 4 16:45:59 2008: ****Enter processIncomingMessages: response code=11
Tue Mar 4 16:45:59 2008: ****Enter processRadiusResponse: response code=11
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Access-Challenge received from
RADIUS server 10.0.47.42 for mobile 00:19:56:b0:7e
:b6 receiveId = 7
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Processing Access-Challenge for
mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Entering Backend Auth Req state
(id=177) for mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Sending EAP Request from AAA to
mobile 00:19:56:b0:7e:b6 (EAP Id 177)
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Received EAPOL EAPPKT from
mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Received EAP Response from
mobile 00:19:56:b0:7e:b6 (EAP Id 177, EAP Type 13)
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Entering Backend Auth Response
state for mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:45:59 2008: 00:19:56:b0:7e:b6 Successful transmission of
Authentication Packet (id 19) to 10.0.47.42:1812,
proxy state 00:19:56:b0:7e:b6-00:00
Tue Mar 4 16:45:59 2008: 00000000: 01 13 00 ed 30 a2 b8 d3
6c 6a e9 08 04 f9 b9 32 ....0...lj.....2
Tue Mar 4 16:45:59 2008: 00000010: 98 fe 36 62 01 05 57 47
42 1f 13 30 30 2d 31 39 ..6b..WGB..00-19
Tue Mar 4 16:45:59 2008: 00000020: 2d 35 36 2d 42 30 2d 37
45 2d 42 36 1e 1a 30 30 -56-B0-7E-B6..00
Tue Mar 4 16:45:59 2008: 00000030: 2d 31 39 2d 41 39 2d 34
32 2d 45 34 2d 31 30 3a -19-A9-42-E4-10:
Tue Mar 4 16:45:59 2008: 00000040: 45 41 50 54 4c 53 05 06
00 00 00 04 04 06 0a 00 EAPTLS..........
Tue Mar 4 16:45:59 2008: 00000050: 2f 06 20 10 74 75 63 73
6f 6e 2d 77 6c 63 32 30 /...tucson-wlc20
Tue Mar 4 16:45:59 2008: 00000060: 30 36 1a 0c 00 00 37 63
01 06 00 00 00 06 06 06 06....7c........
Tue Mar 4 16:45:59 2008: 00000070: 00 00 00 02 0c 06 00 00
05 14 3d 06 00 00 00 13 ..........=.....
Tue Mar 4 16:45:59 2008: 00000080: 4f 3e 02 b1 00 3c 0d 80
00 00 00 32 16 03 01 00 O>...<.....2....
Tue Mar 4 16:45:59 2008: 00000090: 2d 01 00 00 29 03 01 47
cd df 36 c4 bc 40 48 75 -...)..G..6..@Hu
Tue Mar 4 16:45:59 2008: 000000a0: f4 09 ea 60 0c 40 fc 99
a0 e7 11 15 00 7e ca 90 ...`.@.......~..
Tue Mar 4 16:45:59 2008: 000000b0: da 5a d3 39 45 be ca 00
00 02 00 04 01 00 18 1d .Z.9E...........
Tue Mar 4 16:45:59 2008: 000000c0: 45 41 50 3d 30 2e 32 30
32 2e 32 37 65 61 2e 31 EAP=0.202.27ea.1
Tue Mar 4 16:45:59 2008: 000000d0: 3b 53 56 43 3d 30 2e 36
34 37 3b 50 12 c0 6b 4c ;SVC=0.647;P..kL
Tue Mar 4 16:45:59 2008: 000000e0: 37 6c 1a 4f 58 89 18 2b
c4 0e 99 cd 0f 7l.OX..+.....
Tue Mar 4 16:45:59 2008: 00000000: 0b 13 04 3f 5d 80 89 e2
e7 3f b0 c4 4c 99 d2 bd ...?]....?..L...
Tue Mar 4 16:45:59 2008: 00000010: e5 e3 6e af 4f ff 01 b2
03 f4 0d c0 00 00 07 9d ..n.O...........
Tue Mar 4 16:45:59 2008: 00000020: 16 03 01 00 4a 02 00 00
46 03 01 47 cd df 2a f3 ....J...F..G..*.
Tue Mar 4 16:45:59 2008: 00000030: 19 0f 6f 52 2f a7 c3 00
d4 c8 f0 50 1c 8f 47 f4 ..oR/......P..G.
Tue Mar 4 16:45:59 2008: 00000040: 97 1b f2 a0 ca a9 f4 27
0c 34 32 20 d9 33 c4 27 .......'.42..3.'
Tue Mar 4 16:45:59 2008: 00000050: 81 91 e4 97 d7 a6 6b 03
58 1a 4a c8 6d 4a e7 ef ......k.X.J.mJ..
Tue Mar 4 16:45:59 2008: 00000060: 9d f8 fd ad c9 95 aa b5
3e f5 1b dc 00 04 00 16 ........>.......
Tue Mar 4 16:45:59 2008: 00000070: 03 01 07 37 0b 00 07 33
00 07 30 00 03 c2 30 82 ...7...3..0...0.
Tue Mar 4 16:45:59 2008: 00000080: 03 be 30 82 02 a6 a0 03
02 01 02 02 0a 61 0f c8 ..0..........a..
Tue Mar 4 16:45:59 2008: 00000090: d9 00 00 00 00 00 02 30
0d 06 09 2a 86 48 86 f7 .......0...*.H..
Tue Mar 4 16:45:59 2008: 000000a0: 0d 01 01 05 05 00 30 13
31 11 30 0f 06 03 55 04 ......0.1.0...U.
Tue Mar 4 16:45:59 2008: 000000b0: 03 13 08 41 41 52 4f 4e
4c 41 42 30 1e 17 0d 30 ...AARONLAB0...0
Tue Mar 4 16:45:59 2008: 000000c0: 38 30 32 32 39 30 30 30
32 35 30 5a 17 0d 30 39 80229000250Z..09
Tue Mar 4 16:45:59 2008: 000000d0: 30 32 32 38 30 30 31 32
35 30 5a 30 12 31 10 30 0228001250Z0.1.0
Tue Mar 4 16:45:59 2008: 000000e0: 0e 06 03 55 04 03 13 07
41 43 53 63 65 72 74 30 ...U....ACScert0
Tue Mar 4 16:45:59 2008: 000000f0: 81 9f 30 0d 06 09 2a 86
48 86 f7 0d 01 01 01 05 ..0...*.H.......
Tue Mar 4 16:45:59 2008: 00000100: 00 03 81 8d 00 30 81 89
02 81 81 00 e4 cb 25 a1 .....0........%.
Tue Mar 4 16:45:59 2008: 00000110: 96 3f df 4f ff 0d de 8a
89 6f 33 b1 b3 b9 fe 6e .?.O.....o3....n
Tue Mar 4 16:45:59 2008: 00000120: df 6a 01 cf 7f b4 44 5b
6b 4e 91 17 9c 88 d3 6c .j....D[kN.....l
Tue Mar 4 16:45:59 2008: 00000130: 1a 44 5e 1e e7 c1 c5 ae
c2 6f e7 ca 63 31 5f 3a .D^......o..c1_:
Tue Mar 4 16:45:59 2008: 00000140: cf a9 da 83 0e c8 94 93
35 2e c8 f1 21 b0 78 1c ........5...!.x.
Tue Mar 4 16:45:59 2008: 00000150: a1 ca f7 e9 40 a7 d1 7a
f1 85 d6 e9 36 46 51 a7 ....@..z....6FQ.
Tue Mar 4 16:45:59 2008: 00000160: a7 bf 70 db a7 47 da db
59 69 17 db 06 a3 7e b1 ..p..G..Yi....~.
Tue Mar 4 16:45:59 2008: 00000170: 3c e5 ad 39 7f ee 61 cd
ab 3e 0e 8a d5 c1 47 d4 <..9..a..>....G.
Tue Mar 4 16:45:59 2008: 00000180: 65 62 09 22 f4 75 c5 5b
b1 42 94 14 9f c7 02 03 eb.".u.[.B......
Tue Mar 4 16:45:59 2008: 00000190: 01 00 01 a3 82 01 97 30
82 01 93 30 0e 06 03 55 .......0...0...U
Tue Mar 4 16:45:59 2008: 000001a0: 1d 0f 01 01 ff 04 04 03
02 04 f0 30 44 06 09 2a ...........0D..*
Tue Mar 4 16:45:59 2008: 000001b0: 86 48 86 f7 0d 01 09 0f
04 37 30 35 30 0e 06 08 .H.......7050...
Tue Mar 4 16:45:59 2008: 000001c0: 2a 86 48 86 f7 0d 03 02
02 02 00 80 30 0e 06 08 *.H.........0...
Tue Mar 4 16:45:59 2008: 000001d0: 2a 86 48 86 f7 0d 03 04
02 02 00 80 30 07 06 05 *.H.........0...
Tue Mar 4 16:45:59 2008: 000001e0: 2b 0e 03 02 07 30 0a 06
08 2a 86 48 86 f7 0d 03 +....0...*.H....
Tue Mar 4 16:45:59 2008: 000001f0: 07 30 1d 06 03 55 1d 0e
04 16 04 14 b3 fe c9 de .0...U..........
Tue Mar 4 16:45:59 2008: 00000200: 52 60 44 c8 9a c2 4a c2
b4 fd 98 2c 8b 39 5a a6 R`D...J....,.9Z.
Tue Mar 4 16:45:59 2008: 00000210: 30 13 4f ff 06 03 55 1d
25 04 0c 30 0a 06 08 2b 0.O...U.%..0...+
Tue Mar 4 16:45:59 2008: 00000220: 06 01 05 05 07 03 01 30
1f 06 03 55 1d 23 04 18 .......0...U.#..
Tue Mar 4 16:45:59 2008: 00000230: 30 16 80 14 f0 a4 3a c2
cd f5 d4 c8 b4 5e ee 03 0.....:......^..
Tue Mar 4 16:45:59 2008: 00000240: 4f 83 79 b1 f2 d4 e0 19
30 5f 06 03 55 1d 1f 04 O.y.....0_..U...
Tue Mar 4 16:45:59 2008: 00000250: 58 30 56 30 54 a0 52 a0
50 86 25 68 74 74 70 3a X0V0T.R.P.%http:
Tue Mar 4 16:45:59 2008: 00000260: 2f 2f 77 63 73 77 69 6e
2f 43 65 72 74 45 6e 72 //wcswin/CertEnr
Tue Mar 4 16:46:00 2008: 00000270: 6f 6c 6c 2f 41 41 52 4f
4e 4c 41 42 2e 63 72 6c oll/AARONLAB.crl
Tue Mar 4 16:46:00 2008: 00000280: 86 27 66 69 6c 65 3a 2f
2f 5c 5c 77 63 73 77 69 .'file://\\wcswi
Tue Mar 4 16:46:00 2008: 00000290: 6e 5c 43 65 72 74 45 6e
72 6f 6c 6c 5c 41 41 52 n\CertEnroll\AAR
Tue Mar 4 16:46:00 2008: 000002a0: 4f 4e 4c 41 42 2e 63 72
6c 30 81 84 06 08 2b 06 ONLAB.crl0....+.
Tue Mar 4 16:46:00 2008: 000002b0: 01 05 05 07 01 01 04 78
30 76 30 38 06 08 2b 06 .......x0v08..+.
Tue Mar 4 16:46:00 2008: 000002c0: 01 05 05 07 30 02 86 2c
68 74 74 70 3a 2f 2f 77 ....0..,http://w
Tue Mar 4 16:46:00 2008: 000002d0: 63 73 77 69 6e 2f 43 65
72 74 45 6e 72 6f 6c 6c cswin/CertEnroll
Tue Mar 4 16:46:00 2008: 000002e0: 2f 77 63 73 77 69 6e 5f
41 41 52 4f 4e 4c 41 42 /wcswin_AARONLAB
Tue Mar 4 16:46:00 2008: 000002f0: 2e 63 72 74 30 3a 06 08
2b 06 01 05 05 07 30 02 .crt0:..+.....0.
Tue Mar 4 16:46:00 2008: 00000300: 86 2e 66 69 6c 65 3a 2f
2f 5c 5c 77 63 73 77 69 ..file://\\wcswi
Tue Mar 4 16:46:00 2008: 00000310: 6e 4f ff 5c 43 65 72 74
45 6e 72 6f 6c 6c 5c 77 nO.\CertEnroll\w
Tue Mar 4 16:46:00 2008: 00000320: 63 73 77 69 6e 5f 41 41
52 4f 4e 4c 41 42 2e 63 cswin_AARONLAB.c
Tue Mar 4 16:46:00 2008: 00000330: 72 74 30 0d 06 09 2a 86
48 86 f7 0d 01 01 05 05 rt0...*.H.......
Tue Mar 4 16:46:00 2008: 00000340: 00 03 82 01 01 00 67 35
f2 80 42 b5 a8 be f7 c4 ......g5..B.....
Tue Mar 4 16:46:00 2008: 00000350: 9b ea 19 10 67 39 78 cb
38 fb 36 15 69 2a f0 80 ....g9x.8.6.i*..
Tue Mar 4 16:46:00 2008: 00000360: 1e a1 7d 63 72 6a e0 7e
d4 51 7a 1d 64 ec ee b5 ..}crj.~.Qz.d...
Tue Mar 4 16:46:00 2008: 00000370: 2a 73 dc b0 d1 eb 0f 28
1d 66 7a bc 12 ef d8 61 *s.....(.fz....a
Tue Mar 4 16:46:00 2008: 00000380: 5d 05 7b 81 0f 57 20 4d
49 37 4d ba 0b 5a 96 65 ].{..W.MI7M..Z.e
Tue Mar 4 16:46:00 2008: 00000390: d6 a8 e1 bb 1f c6 0e 27
4c 4b d6 3a 00 c7 8d 83 .......'LK.:....
Tue Mar 4 16:46:00 2008: 000003a0: 22 a5 29 61 36 19 19 33
f2 41 18 f7 c6 42 23 36 ".)a6..3.A...B#6
Tue Mar 4 16:46:00 2008: 000003b0: 92 66 4a d9 ef fa 32 d7
a5 0a df 47 50 3c 72 23 .fJ...2....GP<r#
Tue Mar 4 16:46:00 2008: 000003c0: f0 0a d5 59 eb a8 79 f2
e0 56 a0 97 91 48 60 31 ...Y..y..V...H`1
Tue Mar 4 16:46:00 2008: 000003d0: 56 8d 2f b2 69 45 e5 44
3a 59 13 dd 66 eb c7 58 V./.iE.D:Y..f..X
Tue Mar 4 16:46:00 2008: 000003e0: 35 90 7c 79 69 ee dc 6e
19 68 b3 c3 4c ba 7d b3 5.|yi..n.h..L.}.
Tue Mar 4 16:46:00 2008: 000003f0: 8f a0 b9 e0 cf df 67 93
6f 01 d4 34 33 86 b6 95 ......g.o..43...
Tue Mar 4 16:46:00 2008: 00000400: 77 1b 19 61 34 46 82 4c
8e 6b b4 6b e2 4a c1 20 w..a4F.L.k.k.J..
Tue Mar 4 16:46:00 2008: 00000410: 18 1d 45 41 50 3d 30 2e
32 30 32 2e 32 37 65 61 ..EAP=0.202.27ea
Tue Mar 4 16:46:00 2008: 00000420: 2e 32 3b 53 56 43 3d 30
2e 36 34 37 3b 50 12 3a .2;SVC=0.647;P.:
Tue Mar 4 16:46:00 2008: 00000430: f3 3b 7f 99 45 f4 e6 a6
29 c4 17 51 ce 97 df .;..E...)..Q...
Tue Mar 4 16:46:00 2008: ****Enter processIncomingMessages: response code=11
Tue Mar 4 16:46:00 2008: ****Enter processRadiusResponse: response code=11
Tue Mar 4 16:46:00 2008: 00:19:56:b0:7e:b6 Access-Challenge received from
RADIUS server 10.0.47.42 for mobile 00:19:56:b0:
7e:b6 receiveId = 7
Tue Mar 4 16:46:00 2008: 00:19:56:b0:7e:b6 Processing Access-Challenge for
mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:46:00 2008: 00:19:56:b0:7e:b6 Entering Backend Auth Req state
(id=178) for mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:46:00 2008: 00:19:56:b0:7e:b6 Sending EAP Request from AAA to
mobile 00:19:56:b0:7e:b6 (EAP Id 178)
Tue Mar 4 16:46:00 2008: 00:19:56:b0:7e:b6 Received EAPOL EAPPKT from
mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:46:00 2008: 00:19:56:b0:7e:b6 Received EAP Response from
mobile 00:19:56:b0:7e:b6 (EAP Id 178, EAP Type 13)
Tue Mar 4 16:46:00 2008: 00:19:56:b0:7e:b6 Entering Backend Auth Response
state for mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:46:00 2008: 00:19:56:b0:7e:b6 Successful transmission of
Authentication Packet (id 20) to 10.0.47.42:1812,
proxy state 00:19:56:b0:7e:b6-00:00
Tue Mar 4 16:46:00 2008: 00000000: 01 14 00 b7 e8 b0 94 59
96 a1 7f e5 af 22 0f 6c .......Y.....".l
Tue Mar 4 16:46:00 2008: 00000010: 1e 33 6e ee 01 05 57 47
42 1f 13 30 30 2d 31 39 .3n...WGB..00-19
Tue Mar 4 16:46:00 2008: 00000020: 2d 35 36 2d 42 30 2d 37
45 2d 42 36 1e 1a 30 30 -56-B0-7E-B6..00
Tue Mar 4 16:46:00 2008: 00000030: 2d 31 39 2d 41 39 2d 34
32 2d 45 34 2d 31 30 3a -19-A9-42-E4-10:
Tue Mar 4 16:46:00 2008: 00000040: 45 41 50 54 4c 53 05 06
00 00 00 04 04 06 0a 00 EAPTLS..........
Tue Mar 4 16:46:00 2008: 00000050: 2f 06 20 10 74 75 63 73
6f 6e 2d 77 6c 63 32 30 /...tucson-wlc20
Tue Mar 4 16:46:00 2008: 00000060: 30 36 1a 0c 00 00 37 63
01 06 00 00 00 06 06 06 06....7c........
Tue Mar 4 16:46:00 2008: 00000070: 00 00 00 02 0c 06 00 00
05 14 3d 06 00 00 00 13 ..........=.....
Tue Mar 4 16:46:00 2008: 00000080: 4f 08 02 b2 00 06 0d 00
18 1d 45 41 50 3d 30 2e O.........EAP=0.
Tue Mar 4 16:46:00 2008: 00000090: 32 30 32 2e 32 37 65 61
2e 32 3b 53 56 43 3d 30 202.27ea.2;SVC=0
Tue Mar 4 16:46:00 2008: 000000a0: 2e 36 34 37 3b 50 12 a2
aa c7 ed 12 84 25 db 4b .647;P.......%.K
Tue Mar 4 16:46:00 2008: 000000b0: 4c dc 45 09 06 44 c6 L.E..D.
Tue Mar 4 16:46:00 2008: 00000000: 0b 14 04 04 6b 98 3a 74
12 1f 77 54 77 d8 a8 77 ....k.:t..wTw..w
Tue Mar 4 16:46:00 2008: 00000010: 4e a8 a7 6b 4f ff 01 b3
03 b9 0d 00 c6 87 1d b6 N..kO...........
Tue Mar 4 16:46:00 2008: 00000020: 06 5b 24 67 26 09 ee 5f
9c 64 f3 a9 c1 99 49 3e .[$g&.._.d....I>
Tue Mar 4 16:46:00 2008: 00000030: 2b 79 f1 57 17 65 6c 2f
c4 09 4d 54 7d a4 67 91 +y.W.el/..MT}.g.
Tue Mar 4 16:46:00 2008: 00000040: 48 59 ec aa 68 5b 0f 66
c5 e9 22 a6 09 8d 36 cf HY..h[.f.."...6.
Tue Mar 4 16:46:00 2008: 00000050: e3 d9 00 03 68 30 82 03
64 30 82 02 4c a0 03 02 ....h0..d0..L...
Tue Mar 4 16:46:00 2008: 00000060: 01 02 02 10 61 26 83 24
8d ba 53 9b 44 b0 39 bd ....a&.$..S.D.9.
Tue Mar 4 16:46:00 2008: 00000070: 51 cd 1d 48 30 0d 06 09
2a 86 48 86 f7 0d 01 01 Q..H0...*.H.....
Tue Mar 4 16:46:00 2008: 00000080: 05 05 00 30 13 31 11 30
0f 06 03 55 04 03 13 08 ...0.1.0...U....
Tue Mar 4 16:46:00 2008: 00000090: 41 41 52 4f 4e 4c 41 42
30 1e 17 0d 30 38 30 32 AARONLAB0...0802
Tue Mar 4 16:46:00 2008: 000000a0: 32 38 32 33 33 34 34 38
5a 17 0d 31 38 30 32 32 28233448Z..18022
Tue Mar 4 16:46:00 2008: 000000b0: 38 32 33 34 31 32 35 5a
30 13 31 11 30 0f 06 03 8234125Z0.1.0...
Tue Mar 4 16:46:00 2008: 000000c0: 55 04 03 13 08 41 41 52
4f 4e 4c 41 42 30 82 01 U....AARONLAB0..
Tue Mar 4 16:46:00 2008: 000000d0: 22 30 0d 06 09 2a 86 48
86 f7 0d 01 01 01 05 00 "0...*.H........
Tue Mar 4 16:46:00 2008: 000000e0: 03 82 01 0f 00 30 82 01
0a 02 82 01 01 00 c8 5a .....0.........Z
Tue Mar 4 16:46:00 2008: 000000f0: 57 75 45 19 4a 8b 99 da
35 6c cb e0 b6 a0 ff 66 WuE.J...5l.....f
Tue Mar 4 16:46:00 2008: 00000100: e2 8f c1 44 89 09 32 13
c7 d8 70 6c 6d 74 2d e5 ...D..2...plmt-.
Tue Mar 4 16:46:00 2008: 00000110: 89 b8 23 4f ff ea 0a 0e
2d 57 1b 62 36 05 90 92 ..#O....-W.b6...
Tue Mar 4 16:46:00 2008: 00000120: e0 ea f9 a3 e2 fb 54 87
f4 cf 69 52 86 be 0b ca ......T...iR....
Tue Mar 4 16:46:00 2008: 00000130: 14 d1 88 9d 82 01 9a f7
08 da ba cc c9 29 37 94 .............)7.
Tue Mar 4 16:46:00 2008: 00000140: 27 75 d4 6e ae 9e 60 06
84 94 9b 42 f6 c7 5e e0 'u.n..`....B..^.
Tue Mar 4 16:46:00 2008: 00000150: 29 34 b3 06 cb 24 b1 39
73 84 ba be ba d8 6f bb )4...$.9s.....o.
Tue Mar 4 16:46:00 2008: 00000160: 94 f9 32 36 d6 68 68 f2
b2 43 e6 0e a9 b6 4b 62 ..26.hh..C....Kb
Tue Mar 4 16:46:00 2008: 00000170: b8 f9 6e 47 dc 0e c5 5b
16 a3 94 e9 96 08 e5 18 ..nG...[........
Tue Mar 4 16:46:00 2008: 00000180: f0 38 ad a2 98 d3 7c 73
39 80 4a ae 14 e3 f8 f7 .8....|s9.J.....
Tue Mar 4 16:46:00 2008: 00000190: 1e 14 27 bb 6a ce a1 2a
dc 18 66 59 ea b4 d9 b1 ..'.j..*..fY....
Tue Mar 4 16:46:00 2008: 000001a0: a7 50 e9 ff 56 09 ea 93
df 31 08 09 17 ab e5 e9 .P..V....1......
Tue Mar 4 16:46:00 2008: 000001b0: 80 90 30 95 e4 54 90 75
bc f0 7f 13 b1 e7 cd 0b ..0..T.u........
Tue Mar 4 16:46:00 2008: 000001c0: 88 33 81 e7 74 d2 81 d9
97 ab b2 57 f4 5f f6 8b .3..t......W._..
Tue Mar 4 16:46:00 2008: 000001d0: 1e c2 62 d4 de 94 74 7f
8a 28 3b 64 73 88 86 28 ..b...t..(;ds..(
Tue Mar 4 16:46:00 2008: 000001e0: 92 74 b0 92 94 7e ce e1
74 23 f2 64 da 9a 88 47 .t...~..t#.d...G
Tue Mar 4 16:46:00 2008: 000001f0: 02 03 01 00 01 a3 81 b3
30 81 b0 30 0b 06 03 55 ........0..0...U
Tue Mar 4 16:46:00 2008: 00000200: 1d 0f 04 04 03 02 01 86
30 0f 06 03 55 1d 13 01 ........0...U...
Tue Mar 4 16:46:00 2008: 00000210: 01 ff 4f ff 04 05 30 03
01 01 ff 30 1d 06 03 55 ..O...0....0...U
Tue Mar 4 16:46:00 2008: 00000220: 1d 0e 04 16 04 14 f0 a4
3a c2 cd f5 d4 c8 b4 5e ........:......^
Tue Mar 4 16:46:00 2008: 00000230: ee 03 4f 83 79 b1 f2 d4
e0 19 30 5f 06 03 55 1d ..O.y.....0_..U.
Tue Mar 4 16:46:00 2008: 00000240: 1f 04 58 30 56 30 54 a0
52 a0 50 86 25 68 74 74 ..X0V0T.R.P.%htt
Tue Mar 4 16:46:00 2008: 00000250: 70 3a 2f 2f 77 63 73 77
69 6e 2f 43 65 72 74 45 p://wcswin/CertE
Tue Mar 4 16:46:00 2008: 00000260: 6e 72 6f 6c 6c 2f 41 41
52 4f 4e 4c 41 42 2e 63 nroll/AARONLAB.c
Tue Mar 4 16:46:00 2008: 00000270: 72 6c 86 27 66 69 6c 65
3a 2f 2f 5c 5c 77 63 73 rl.'file://\\wcs
Tue Mar 4 16:46:00 2008: 00000280: 77 69 6e 5c 43 65 72 74
45 6e 72 6f 6c 6c 5c 41 win\CertEnroll\A
Tue Mar 4 16:46:00 2008: 00000290: 41 52 4f 4e 4c 41 42 2e
63 72 6c 30 10 06 09 2b ARONLAB.crl0...+
Tue Mar 4 16:46:00 2008: 000002a0: 06 01 04 01 82 37 15 01
04 03 02 01 00 30 0d 06 .....7.......0..
Tue Mar 4 16:46:00 2008: 000002b0: 09 2a 86 48 86 f7 0d 01
01 05 05 00 03 82 01 01 .*.H............
Tue Mar 4 16:46:00 2008: 000002c0: 00 17 eb b2 43 da 02 66
05 cd 76 c0 7b 2a 16 83 ....C..f..v.{*..
Tue Mar 4 16:46:00 2008: 000002d0: 95 bb 5e bf d3 db fc 23
7e 14 6e 52 f8 37 01 7c ..^....#~.nR.7.|
Tue Mar 4 16:46:00 2008: 000002e0: dd e9 bf 34 60 49 f1 68
7e da 53 07 f6 b2 66 6d ...4`I.h~.S...fm
Tue Mar 4 16:46:00 2008: 000002f0: 8c bd ca 26 f4 fa 3d 03
4f db be 92 33 7e 50 06 ...&..=.O...3~P.
Tue Mar 4 16:46:00 2008: 00000300: 5e b3 b9 35 c6 83 3c 90
1e 42 54 3e 63 17 9a 8a ^..5..<..BT>c...
Tue Mar 4 16:46:00 2008: 00000310: d0 4f c4 68 24 97 90 a1
77 c9 c8 93 1f 58 ab ca .O.h$...w....X..
Tue Mar 4 16:46:00 2008: 00000320: f7 18 e6 8c 36 12 44 9d
a6 ca 43 5f 03 07 16 99 ....6.D...C_....
Tue Mar 4 16:46:00 2008: 00000330: 1d a4 48 7d a4 e5 12 7c
d0 81 e7 35 9e ad 69 5e ..H}...|...5..i^
Tue Mar 4 16:46:00 2008: 00000340: 15 d7 2a 7f 51 4e 8c 59
69 9f d1 41 9b 2e e1 05 ..*.QN.Yi..A....
Tue Mar 4 16:46:00 2008: 00000350: 95 15 bd b1 1a 97 a6 69
d3 9c 0b 93 00 16 e1 49 .......i.......I
Tue Mar 4 16:46:00 2008: 00000360: 66 e3 98 29 79 ba 14 69
cf 76 27 69 7d 43 d0 f4 f..)y..i.v'i}C..
Tue Mar 4 16:46:00 2008: 00000370: 86 3c 6b 58 55 d4 85 be
c5 da 71 e4 43 76 3d 0a .<kXU.....q.Cv=.
Tue Mar 4 16:46:00 2008: 00000380: d3 4f 49 97 12 75 e3 7d
88 92 99 5d fc 7a 69 28 .OI..u.}...].zi(
Tue Mar 4 16:46:00 2008: 00000390: f6 f0 20 70 33 b7 22 5a
bf c5 e5 28 43 35 00 2f ...p3."Z...(C5./
Tue Mar 4 16:46:00 2008: 000003a0: 47 46 9a 5a 45 5c 56 d5
24 3d 44 bf e9 63 f2 05 GF.ZE\V.$=D..c..
Tue Mar 4 16:46:01 2008: 000003b0: 84 da 94 17 b7 ef c3 31
7d 04 30 87 e1 c3 31 8a .......1}.0...1.
Tue Mar 4 16:46:01 2008: 000003c0: 2a e1 52 16 03 01 00 0d
0d 00 00 05 02 01 02 00 *.R.............
Tue Mar 4 16:46:01 2008: 000003d0: 00 0e 00 00 00 18 1d 45
41 50 3d 30 2e 32 30 32 .......EAP=0.202
Tue Mar 4 16:46:01 2008: 000003e0: 2e 32 37 65 61 2e 33 3b
53 56 43 3d 30 2e 36 34 .27ea.3;SVC=0.64
Tue Mar 4 16:46:01 2008: 000003f0: 37 3b 50 12 05 0e 3c e0
e4 5f 38 21 96 26 8e 39 7;P...<.._8!.&.9
Tue Mar 4 16:46:01 2008: 00000400: 96 a9 09 5d...]
Tue Mar 4 16:46:01 2008: ****Enter processIncomingMessages: response code=11
Tue Mar 4 16:46:01 2008: ****Enter processRadiusResponse: response code=11
Tue Mar 4 16:46:01 2008: 00:19:56:b0:7e:b6 Access-Challenge received from
RADIUS server 10.0.47.42 for mobile 00:19:56:b0:
7e:b6 receiveId = 7
Tue Mar 4 16:46:01 2008: 00:19:56:b0:7e:b6 Processing Access-Challenge for
mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:46:01 2008: 00:19:56:b0:7e:b6 Entering Backend Auth Req state
(id=179) for mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:46:01 2008: 00:19:56:b0:7e:b6 Sending EAP Request from AAA to
mobile 00:19:56:b0:7e:b6 (EAP Id 179)
Tue Mar 4 16:46:01 2008: 00:19:56:b0:7e:b6 Received EAPOL EAPPKT from
mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:46:01 2008: 00:19:56:b0:7e:b6 Received EAP Response from
mobile 00:19:56:b0:7e:b6 (EAP Id 179, EAP Type 13)
Tue Mar 4 16:46:01 2008: 00:19:56:b0:7e:b6 Entering Backend Auth Response
state for mobile 00:19:56:b0:7e:b6
Tue Mar 4 16:46:01 2008: 00:19:56:b0:7e:b6 Successful transmission of
Authentication Packet (id 21) to 10.0.47.42:1812,
proxy state
00:19:56:b0:7e:b6-00:00
Tue Mar 4 16:46:01 2008: 00000000: 01 15 05 76 81 b7 fa 95
63 1f 50 6f 98 4d a3 6b ...v....c.Po.M.k
Tue Mar 4 16:46:01 2008: 00000010: db 3c bc 1d 01 05 57 47
42 1f 13 30 30 2d 31 39 .<....WGB..00-19
Tue Mar 4 16:46:01 2008: 00000020: 2d 35 36 2d 42 30 2d 37
45 2d 42 36 1e 1a 30 30 -56-B0-7E-B6..00
Tue Mar 4 16:46:01 2008: 00000030: 2d 31 39 2d 41 39 2d 34
32 2d 45 34 2d 31 30 3a -19-A9-42-E4-10:
Tue Mar 4 16:46:01 2008: 00000040: 45 41 50 54 4c 53 05 06
00 00 00 04 04 06 0a 00 EAPTLS..........
Tue Mar 4 16:46:01 2008: 00000050: 2f 06 20 10 74 75 63 73
6f 6e 2d 77 6c 63 32 30 /...tucson-wlc20
Tue Mar 4 16:46:01 2008: 00000060: 30 36 1a 0c 00 00 37 63
01 06 00 00 00 06 06 06 06....7c........
Tue Mar 4 16:46:01 2008: 00000070: 00 00 00 02 0c 06 00 00
05 14 3d 06 00 00 00 13 ..........=.....
Tue Mar 4 16:46:01 2008: 00000080: 4f ff 02 b3 04 bd 0d 80
00 00 04 b3 16 03 01 03 O...............
Tue Mar 4 16:46:01 2008: 00000090: 6d 0b 00 03 69 00 03 66
00 03 63 30 82 03 5f 30 m...i..f..c0.._0
Tue Mar 4 16:46:01 2008: 000000a0: 82 02 47 a0 03 02 01 02
02 0a 13 79 b0 72 00 00 ..G........y.r..
Tue Mar 4 16:46:01 2008: 000000b0: 00 00 00 0c 30 0d 06 09
2a 86 48 86 f7 0d 01 01 ....0...*.H.....
Tue Mar 4 16:46:01 2008: 000000c0: 05 05 00 30 13 31 11 30
0f 06 03 55 04 03 13 08 ...0.1.0...U....
Tue Mar 4 16:46:01 2008: 000000d0: 41 41 52 4f 4e 4c 41 42
30 1e 17 0d 30 38 30 33 AARONLAB0...0803
Tue Mar 4 16:46:01 2008: 000000e0: 30 33 31 38 33 33 30 39
5a 17 0d 30 39 30 33 30 03183309Z..09030
Tue Mar 4 16:46:01 2008: 000000f0: 33 31 38 34 33 30 39 5a
30 0e 31 0c 30 0a 06 03 3184309Z0.1.0...
Tue Mar 4 16:46:01 2008: 00000100: 55 04 03 13 03 57 47 42
30 81 9f 30 0d 06 09 2a U....WGB0..0...*
Tue Mar 4 16:46:01 2008: 00000110: 86 48 86 f7 0d 01 01 01
05 00 03 81 8d 00 30 81 .H............0.
Tue Mar 4 16:46:01 2008: 00000120: 89 02 81 81 00 a6 34 91
20 dd 58 df b2 60 c0 6c ......4...X..`.l
Tue Mar 4 16:46:01 2008: 00000130: d0 9d 10 86 01 a9 61 9f
cb 2b 01 22 49 d7 38 ee ......a..+."I.8.
Tue Mar 4 16:46:01 2008: 00000140: 00 fe be c9 cd 48 4b 73
a0 75 6d bb d0 c9 20 24 .....HKs.um....$
Tue Mar 4 16:46:01 2008: 00000150: 0f cc f0 76 2f ad ef 43
53 8f b7 ec c7 50 04 02 ...v/..CS....P..
Tue Mar 4 16:46:01 2008: 00000160: d8 03 4a 7d 08 9e b4 f2
78 ab 36 06 ba f7 02 ab ..J}....x.6.....
Tue Mar 4 16:46:01 2008: 00000170: a1 6e 26 6c 2d d4 10 08
0d 25 82 1a d2 fc 14 4f .n&l-....%.....O
Tue Mar 4 16:46:01 2008: 00000180: ff 86 fa fd 84 ec de be
3c 3e f8 be d6 b6 7b 81 ........<>....{.
Tue Mar 4 16:46:01 2008: 00000190: 89 9a da a6 96 fd 7f e7
dd bf 7f 26 6e 20 03 63 ...........&n..c
Tue Mar 4 16:46:01 2008: 000001a0: c4 a2 56 4c 8e 75 99 02
03 01 00 01 a3 82 01 3c ..VL.u.........<
Tue Mar 4 16:46:01 2008: 000001b0: 30 82 01 38 30 0e 06 03
55 1d 0f 01 01 ff 04 04 0..80...U.......
Tue Mar 4 16:46:01 2008: 000001c0: 03 02 05 a0 30 1d 06 03
55 1d 0e 04 16 04 14 41 ....0...U......A
Tue Mar 4 16:46:01 2008: 000001d0: 97 b6 32 83 7f c0 88 11
4d 59 d5 44 70 e9 0f c6 ..2.....MY.Dp...
Tue Mar 4 16:46:01 2008: 000001e0: 3b a2 85 30 1f 06 03 55
1d 23 04 18 30 16 80 14 ;..0...U.#..0...
Tue Mar 4 16:46:01 2008: 000001f0: f0 a4 3a c2 cd f5 d4 c8
b4 5e ee 03 4f 83 79 b1 ..:......^..O.y.
Tue Mar 4 16:46:01 2008: 00000200: f2 d4 e0 19 30 5f 06 03
55 1d 1f 04 58 30 56 30 ....0_..U...X0V0
Tue Mar 4 16:46:01 2008: 00000210: 54 a0 52 a0 50 86 25 68
74 74 70 3a 2f 2f 77 63 T.R.P.%http://wc
Tue Mar 4 16:46:01 2008: 00000220: 73 77 69 6e 2f 43 65 72
74 45 6e 72 6f 6c 6c 2f swin/CertEnroll/
Tue Mar 4 16:46:01 2008: 00000230: 41 41 52 4f 4e 4c 41 42
2e 63 72 6c 86 27 66 69 AARONLAB.crl.'fi
Tue Mar 4 16:46:01 2008: 00000240: 6c 65 3a 2f 2f 5c 5c 77
63 73 77 69 6e 5c 43 65 le://\\wcswin\Ce
Tue Mar 4 16:46:01 2008: 00000250: 72 74 45 6e 72 6f 6c 6c
5c 41 41 52 4f 4e 4c 41 rtEnroll\AARONLA
Tue Mar 4 16:46:01 2008: 00000260: 42 2e 63 72 6c 30 81 84
06 08 2b 06 01 05 05 07 B.crl0....+.....
Tue Mar 4 16:46:01 2008: 00000270: 01 01 04 78 30 76 30 38
06 08 2b 06 01 05 4f ff ...x0v08..+...O.
Tue Mar 4 16:46:01 2008: 00000280: 05 07 30 02 86 2c 68 74
74 70 3a 2f 2f 77 63 73 ..0..,http://wcs
Tue Mar 4 16:46:01 2008: 00000290: 77 69 6e 2f 43 65 72 74
45 6e 72 6f 6c 6c 2f 77 win/CertEnroll/w
Tue Mar 4 16:46:01 2008: 000002a0: 63 73 77 69 6e 5f 41 41
52 4f 4e 4c 41 42 2e 63 cswin_AARONLAB.c
Tue Mar 4 16:46:01 2008: 000002b0: 72 74 30 3a 06 08 2b 06
01 05 05 07 30 02 86 2e rt0:..+.....0...
Tue Mar 4 16:46:01 2008: 000002c0: 66 69 6c 65 3a 2f 2f 5c
5c 77 63 73 77 69 6e 5c file://\\wcswin\
Tue Mar 4 16:46:01 2008: 000002d0: 43 65 72 74 45 6e 72 6f
6c 6c 5c 77 63 73 77 69 CertEnroll\wcswi
Tue Mar 4 16:46:01 2008: 000002e0: 6e 5f 41 41 52 4f 4e 4c
41 42 2e 63 72 74 30 0d n_AARONLAB.crt0.
Tue Mar 4 16:46:01 2008: 000002f0: 06 09 2a 86 48 86 f7 0d
01 01 05 05 00 03 82 01 ..*.H...........
Tue Mar 4 16:46:01 2008: 00000300: 01 00 2e a1 3f f3 52 52
97 b5 83 43 0f 61 20 64 ....?.RR...C.a.d
Tue Mar 4 16:46:01 2008: 00000310: 40 fd d3 16 38 4f d9 5f
64 94 a7 c2 59 53 53 52 @...8O._d...YSSR
Tue Mar 4 16:46:01 2008: 00000320: 90 5d ee 1c e0 2a 90 af
f4 e8 51 3e 87 38 9a ce .]...*....Q>.8..
Tue Mar 4 16:46:01 2008: 00000330: 88 0c 4f 1f ad f1 ef dd
96 44 6b 51 4e 9f 2c a1 ..O......DkQN.,.
Tue Mar 4 16:46:01 2008: 00000340: 8a c5 0e bd d0 f9 7e 34
fa 22 67 26 e1 26 e6 3e ......~4."g&.&.>
Tue Mar 4 16:46:01 2008: 00000350: bd b8 9f 64 f0 65 6f 23
f0 67 40 60 0f 4b f1 ff ...d.eo#.g@`.K..
Tue Mar 4 16:46:01 2008: 00000360: c1 9c 3c 11 81 be b2 7a
45 b6 bd f2 26 76 2a 3a ..<....zE...&v*:
Tue Mar 4 16:46:01 2008: 00000370: 52 32 65 cf 62 0b 47 65
b4 b5 fa db b4 4f ff 07 R2e.b.Ge.....O..
Tue Mar 4 16:46:01 2008: 00000380: ae 54 58 11 d8 52 8f f8
e3 e5 00 f1 c4 1d 2a a4 .TX..R........*. |
Related Information
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
21-Jun-2010 |
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback