Introduction
This document describes a configuration example for Firepower Device Manager (FDM) with Active Authentication (Captive-Portal) integration. This configuration uses Active Directory (AD) as the source and self-signed certificates.
Prerequisites
Requirements
Cisco recommends that you have knowledge of these topics:
- Cisco Firepower Threat Defense (FTD)
- Active Directory (AD)
- Self-signed Certificates.
- Secure Socket Layer (SSL)
Components Used
The information in this document is based on the following software version:
- Firepower Threat Defense 6.6.4
- Active Directory
- PC test
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command.
Background Information
Establish User Identity through Active Authentication
Authentication is the act of confirms the identity of a user. With active authentication, when an HTTP traffic flow comes from an IP address for which the system has no user-identity mapping, you can decide whether to authenticate the user who initiated the traffic flow against the directory configured for the system. If the user successfully authenticates, the IP address is considered to have the identity of the authenticated user.
Failure to authenticate does not prevent network access for the user. Your access rules ultimately decide what access to provide these users.
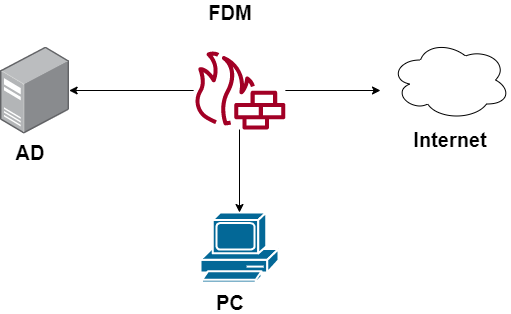
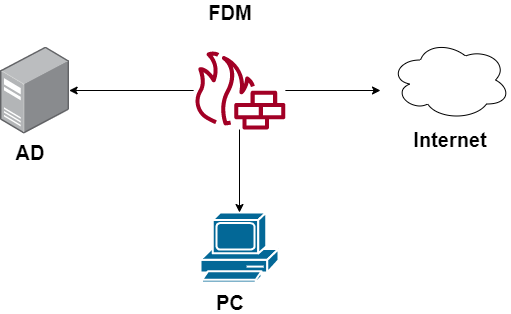
Network Diagram
Configure
Implement the Identity Policy
To enable user identity acquisition, so that the user associated with an IP address is known, you need to configure several items
Step 1. Configure the AD identity realm
Whether you collect user identity actively (by prompt for user authentication) or passively, you need to configure the Active Directory (AD) server that has the user identity information.
Navigate to Objects > Identity Services and select the option AD to add the Active Directory.

Add the Active Directory configuration:

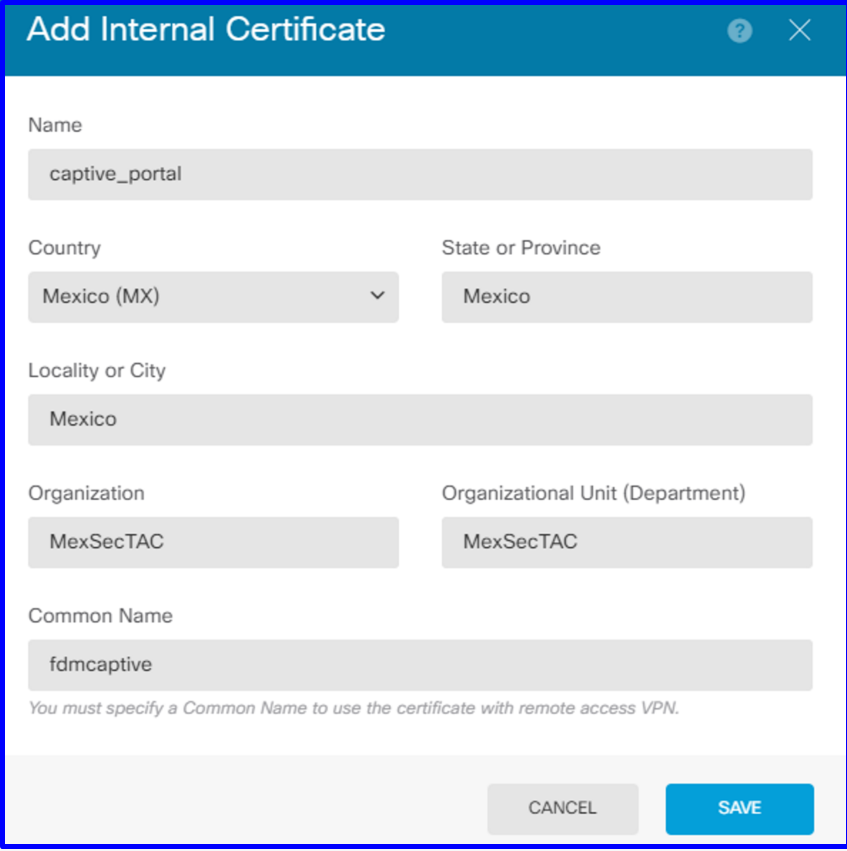
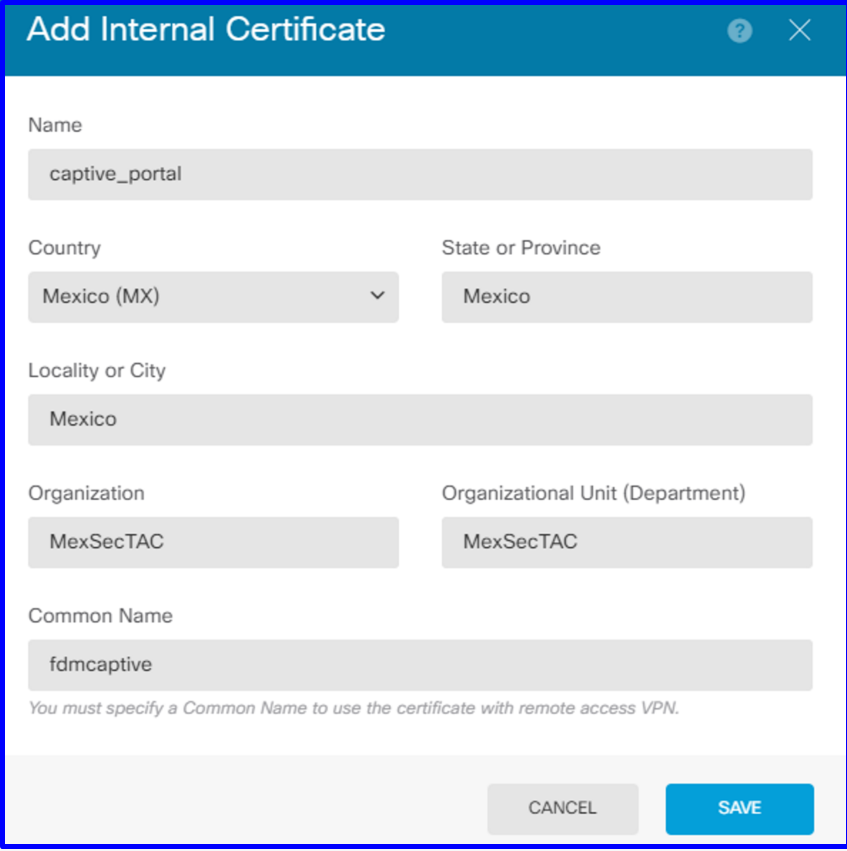
Step 2. Create Self-signed certificates
In order to create a Captive Portal configuration, you need two certificates one for the captive portal and one for SSL decryption.
You can create a self-signed certificate like in this example.
Navigate to Objects > Certificates

Captive portal Self Signed Certificate:
SSL Self Signed certificate:

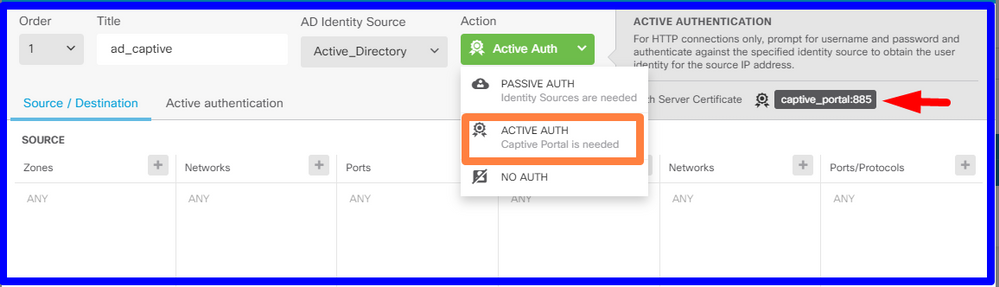
Step 3. Create Identity rule
Navigate to Policies > Identity > select [+] button to add a new Identity rule.
You need to create the Identity policy in order to configure active authentication, the policy must have the below elements:
- AD Identity Source: The same you add in the step number 1
- Action: ACTIVE AUTH
- Server Certificate: The same Self-signed Certificate you created Before [In this scenario captive_portal]
- Type: HTTP Basic (in this example scenario)
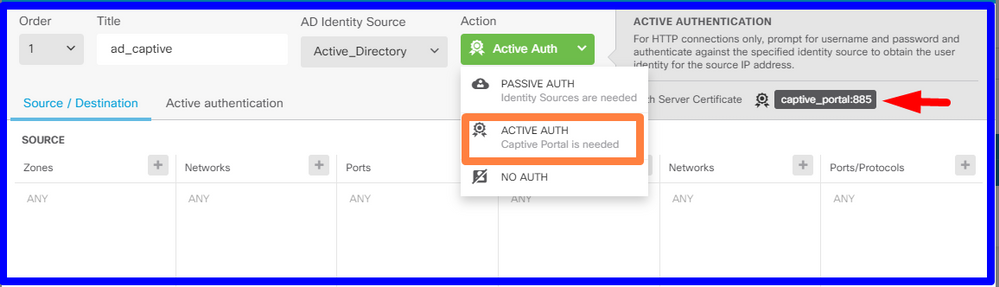
Once the Identity policy is created as active authentication, automatically creates an SSL rule, by default this rule is set up as any any with Decrypt-Resign, which means that there are no SSL modifications into this rule.


Step 4. Create Access rule into Access Control Policy
You need to allow pot 885/tcp which redirects the traffic to the captive portal authentication. Navigate to Policies > Access Control and add the access rule.

If you need to check if the users were downloaded from AD, you can edit the access rule and navigate to the Users section, then on AVAILABLE USERS, you can verify how many users does the FDM already has.

Remember to deploy the configuration changes.
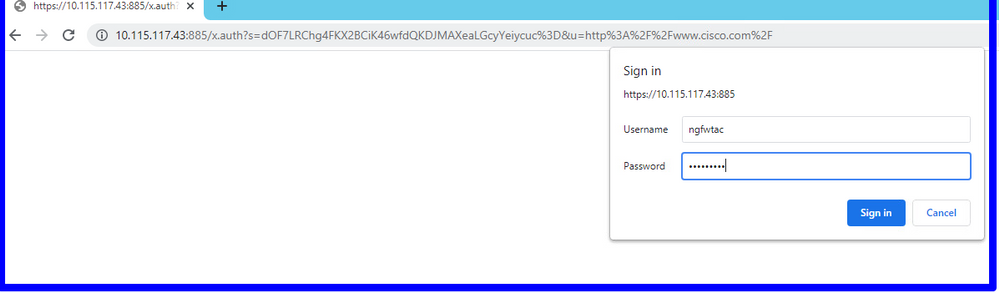
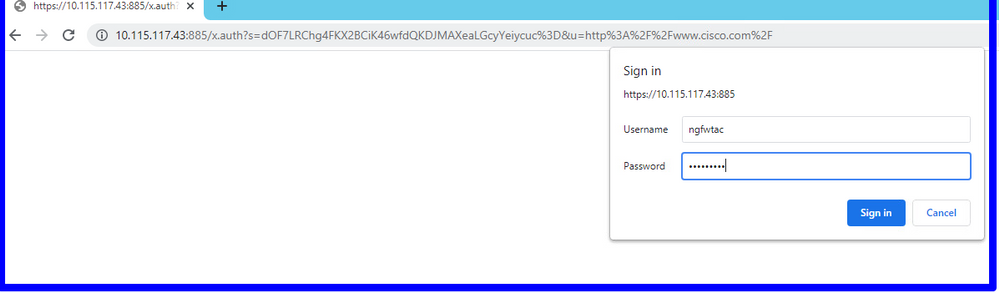
Verify
Verify that the user's device receives the check box when navigates to a HTTPS site.

Enter the user AD credentials.

Troubleshoot
You can use the user_map_query.pl script to validate FDM has the user ip mapping
user_map_query.pl -u username ---> for users
user_map_query.pl -i x.x.x.x ---> for ip addresses
root@firepower:~# user_map_query.pl -u ngfwtac
WARNING: This script was not tested on this major version (6.6.0)! The results may be unexpected.
Current Time: 06/24/2021 20:45:54 UTC
Getting information on username(s)...
---
User #1: ngfwtac
---
ID: 8
Last Seen: 06/24/2021 20:44:03 UTC
for_policy: 1
Realm ID: 4
==============================
| Database |
==============================
##) IP Address [Realm ID]
1) ::ffff:10.115.117.46 [4]
##) Group Name (ID) [realm: Realm Name (ID)]
1) Domain Users (12) [realm: Active_Directory (4)]
On clish mode you can configure:
system support identity-debug to verify if redirection is successful.
> system support identity-debug
Enable firewall-engine-debug too? [n]: y
Please specify an IP protocol:
Please specify a client IP address: 10.115.117.46
Please specify a client port:
Please specify a server IP address:
Please specify a server port:
Monitoring identity and firewall debug messages
10.115.117.46-55809 > 72.163.47.11-53 17 AS 1-1 I 1 deleting firewall session flags = 0x10001, fwFlags = 0x100
10.115.117.46-55809 > 72.163.47.11-53 17 AS 1-1 I 1 Logging EOF as part of session delete with rule_id = 1 ruleAction = 2 ruleReason = 0
10.115.117.46-50611 > 142.250.138.94-443 6 AS 1-1 I 0 Got end of flow event from hardware with flags 00010001. Rule Match Data: rule_id 0, rule_action 0 rev_id 0, rule_flags 2
10.115.117.46-50611 > 142.250.138.94-443 6 AS 1-1 I 0 Logging EOF for event from hardware with rule_id = 1 ruleAction = 2 ruleReason = 0
10.115.117.46-50611 > 142.250.138.94-443 6 AS 1-1 I 0 : Received EOF, deleting the snort session.
10.115.117.46-50611 > 142.250.138.94-443 6 AS 1-1 I 0 deleting firewall session flags = 0x10003, fwFlags = 0x114
10.115.117.46-65489 > 72.163.47.11-53 17 AS 1-1 I 1 deleting firewall session flags = 0x10001, fwFlags = 0x100
10.115.117.46-65489 > 72.163.47.11-53 17 AS 1-1 I 1 Logging EOF as part of session delete with rule_id = 1 ruleAction = 2 ruleReason = 0
10.115.117.46-65489 > 173.36.131.10-53 17 AS 1-1 I 1 deleting firewall session flags = 0x10001, fwFlags = 0x100
10.115.117.46-65489 > 173.36.131.10-53 17 AS 1-1 I 1 Logging EOF as part of session delete with rule_id = 1 ruleAction = 2 ruleReason = 0
10.115.117.46-53417 > 72.163.47.11-53 17 AS 1-1 I 0 deleting firewall session flags = 0x10001, fwFlags = 0x100
10.115.117.46-53417 > 72.163.47.11-53 17 AS 1-1 I 0 Logging EOF as part of session delete with rule_id = 1 ruleAction = 2 ruleReason = 0
10.115.117.46-63784 > 72.163.47.11-53 17 AS 1-1 I 1 Starting authentication (sfAuthCheckRules params) with zones 2 -> 3, port 63784 -> 53, geo 16671760 -> 16671778
10.115.117.46-63784 > 72.163.47.11-53 17 AS 1-1 I 1 looked for user_id with realm_id 4 auth_type 2, returning realm_id 4 auth_type 2 user_id 8
10.115.117.46-63784 > 72.163.47.11-53 17 AS 1-1 I 1 found active binding for user_id 8 in realm 4
10.115.117.46-63784 > 72.163.47.11-53 17 AS 1-1 I 1 matched auth rule id = 2023803385 user_id = 8 realm_id = 4
10.115.117.46-63784 > 72.163.47.11-53 17 AS 1-1 I 1 new firewall session
10.115.117.46-63784 > 72.163.47.11-53 17 AS 1-1 I 1 using HW or preset rule order 4, 'Default Action', action Allow and prefilter rule 0
10.115.117.46-63784 > 72.163.47.11-53 17 AS 1-1 I 1 HitCount data sent for rule id: 1,
10.115.117.46-63784 > 72.163.47.11-53 17 AS 1-1 I 1 allow action
10.115.117.46-50619 > 142.250.138.94-443 6 AS 1-1 I 0 Starting authentication (sfAuthCheckRules params) with zones 2 -> 3, port 50619 -> 443, geo 16671760 -> 16671778
10.115.117.46-50619 > 142.250.138.94-443 6 AS 1-1 I 0 looked for user_id with realm_id 4 auth_type 2, returning realm_id 4 auth_type 2 user_id 8
10.115.117.46-50619 > 142.250.138.94-443 6 AS 1-1 I 0 found active binding for user_id 8 in realm 4
10.115.117.46-50619 > 142.250.138.94-443 6 AS 1-1 I 0 matched auth rule id = 2023803385 user_id = 8 realm_id = 4
10.115.117.46-50619 > 142.250.138.94-443 6 AS 1-1 I 0 new firewall session
10.115.117.46-50619 > 142.250.138.94-443 6 AS 1-1 I 0 using HW or preset rule order 4, 'Default Action', action Allow and prefilter rule 0
10.115.117.46-50619 > 142.250.138.94-443 6 AS 1-1 I 0 HitCount data sent for rule id: 1,
10.115.117.46-50619 > 142.250.138.94-443 6 AS 1-1 I 0 allow action
Reference:
https://www.cisco.com/c/en/us/td/docs/security/firepower/660/fdm/fptd-fdm-config-guide-660/fptd-fdm-identity.html#id_71535
https://www.cisco.com/c/en/us/td/docs/security/firepower/660/fdm/fptd-fdm-config-guide-660/fptd-fdm-identity-sources.html#task_83008ECD0DBF4E388B28B6247CB2E64B











 Feedback
Feedback