Configure AnyConnect VPN on FTD using Cisco ISE as a RADIUS Server with Windows Server 2012 Root CA
Available Languages
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
Contents
Contents
Introduction
This document describes how to configure AnyConnect VPN (Virtual Private Network) on an FTD (Firepower Threat Defense) firewall using Cisco ISE (Identity Services Engine) as a RADIUS server. We use a Windows Server 2012 as our Root CA (Certificate Authority) so that the communication over VPN is secured by certificates i.e. the employee PC will trust the certificate of the FTD because the FTD VPN certificate has been signed by our Windows Server 2012 Root CA
Prerequisites
Requirements
You must have the following deployed and running in your network:
- Firepower Management Center and Firepower Threat Defense firewall deployed with basic connectivity
- Cisco ISE deployed and running in your network
- Windows Server (with Active Directory) deployed and employees' Windows/Mac PC's joined to the AD (Active Directory) domain
In our example below, employees will open the AnyConnect Client on their Windows/Mac PC, and they will securely connect to the outside interface of the FTD via VPN using their credentials. The FTD will check their username and password against Cisco ISE (which will check with Windows Server Active Directory to verify their username, password, and group i.e. only users in the AD Group 'Employees' will be able to VPN into the company network.
Components Used
The information in this document is based on these software versions:
- Firepower Management Center and Firepower Threat Defense running 6.2.3
- Cisco Identity Services Engine running 2.4
- Cisco AnyConnect Secure Mobility Client running 4.6.03049
- Windows Server 2012 R2 running Active Directory and Certificate Services (this is our Root CA for all certificates)
- Windows 7, Windows 10, Mac PCs
Configure
Network Diagram
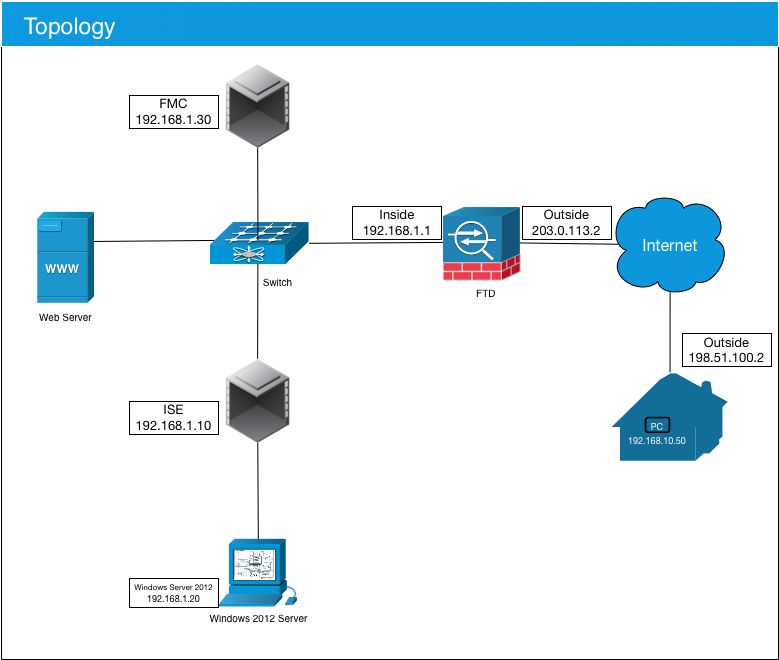
In this use case, the employee's Windows/Mac PC running the Anyconnect VPN Client will connect to the outside public IP address of the FTD firewall, and Cisco ISE will dynamically grant them limited or full access to certain internal or internet resources (configurable) once they are connected via VPN depending on what AD Group they are a member of in Active Directory
| Device | Hostname/FQDN | Public IP Address | Private IP Address | AnyConnect IP Address | |
| Windows PC | - | 198.51.100.2 | 10.0.0.1 | 192.168.10.50 | |
| FTD | ciscofp3.cisco.com | 203.0.113.2 | 192.168.1.1 | - | |
| FMC | - | - | 192.168.1.30 | - | |
| Cisco ISE | ciscoise.cisco.com | - | 192.168.1.10 | - | |
| Windows Server 2012 | ciscodc.cisco.com | - | 192.168.1.20 | - | |
| Internal Servers | - | - | 192.168.1.x | - |
Configuration
Export the Root CA certificate from Windows Server
In this document, we will use Microsoft Windows Server 2012 as our Root CA for certificates. The Client PC's will trust this Root CA to connect securely to the FTD via VPN (see steps below). This will make sure they can connect securely to the FTD over the internet and access internal resources from home. Their PC will trust the connection in their browser and AnyConnect Client.
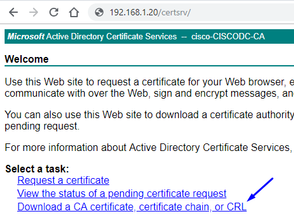
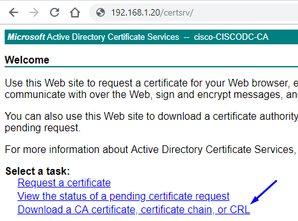
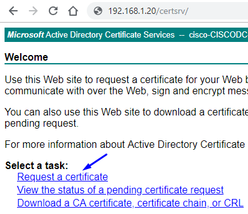
Go to http://192.168.1.20/certsrv and follow the below steps to download your Windows Server Root CA Certificate:
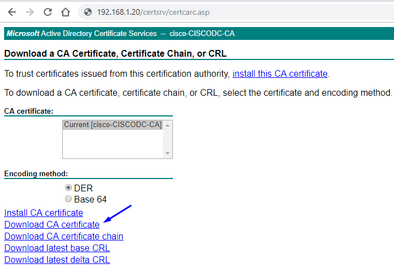
Click Download a CA certificate, certificate chain, or CRL
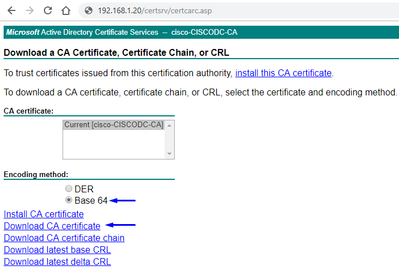
Click Download Certificate and rename it to 'RootCAcert3.cer'

Install the Root CA Certificate on employee Windows/Mac PCs
Method 1: Install the certificate on all employee PC's by pushing it via Windows Server Group Policy (ideal for anything over 10 VPN users):
How to use Windows Server to Distribute Certificates to Client Computers by Using Group Policy
Method 2: Install the certificate on all employee PC's by installing it individually on each PC (ideal to test one VPN user):
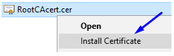
Right-click the certificate on your employees' Windows/Mac PC and click Install Certificate
Select 'Current User'
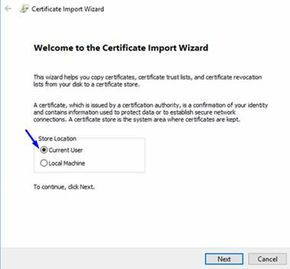
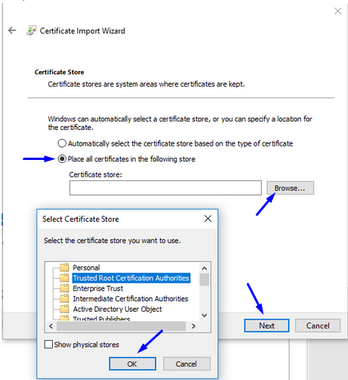
Select Place all certificates in the following store and select Trusted Root Certification Authorities, click Ok, click Next, and click Finish
Generate a CSR on FTD, get CSR signed by the Windows Server Root CA, and install that signed certificate on FTD
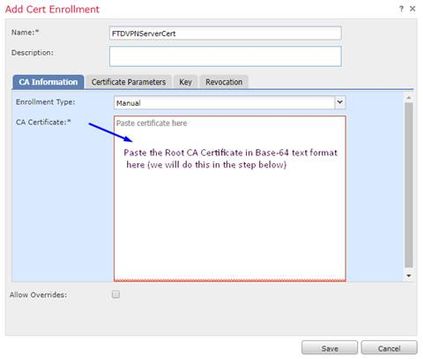
Go to Objects > Object Management > PKI > Cert Enrollment, click on Add Cert Enrollment
Click Add Cert Enrollment button
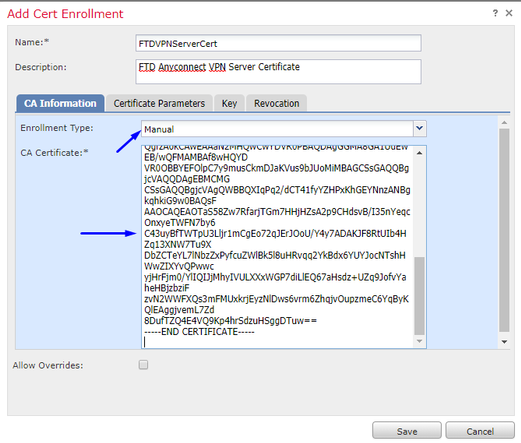
Select Enrollment Type > Manual
As seen in image below, we need to paste our Root CA certificate here:
Here is how to download your Root CA certificate, view it in text format, and paste it in the box above:
Go to http://192.168.1.20/certsrv
Click Download a CA certificate, certificate chain, or CRL
Click Base 64 button > click Download CA Certificate

Open the RootCAcertBase64.cer file in Notepad
Copy and paste the .cer contents (Root CA certificate) from Windows AD Server here:
Click Certificate Parameters tab >> type your certificate information
Note:
Custom FQDN field must be the FQDN of your FTD
Common Name field must be the FQDN of your FTD
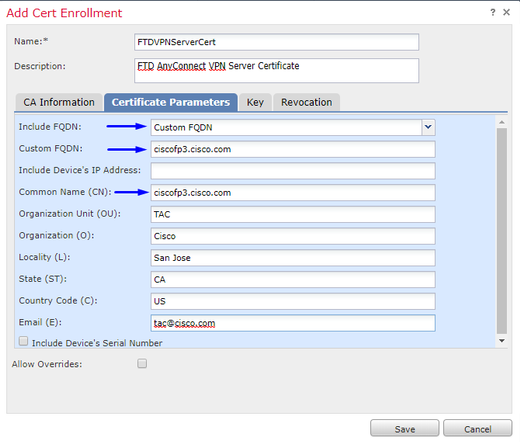
Tip: you can get the FQDN of your FTD by typing the following command from the FTD CLI:
> show network ===============[ System Information ]=============== Hostname : ciscofp3.cisco.com Domains : cisco DNS Servers : 192.168.1.20 Management port : 8305 IPv4 Default route Gateway : 192.168.1.1 ======================[ br1 ]======================= State : Enabled Channels : Management & Events Mode : Non-Autonegotiation MDI/MDIX : Auto/MDIX MTU : 1500 MAC Address : 00:0C:29:4F:AC:71 ----------------------[ IPv4 ]---------------------- Configuration : Manual Address : 192.168.1.2 Netmask : 255.255.255.0
Click Key tab and type any Key Name
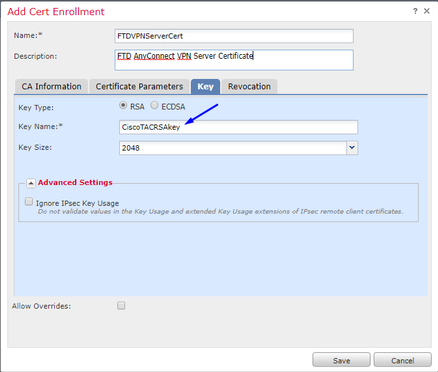
Click Save
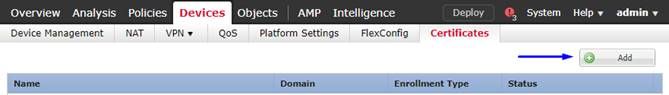
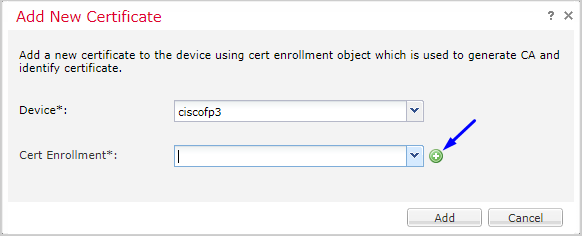
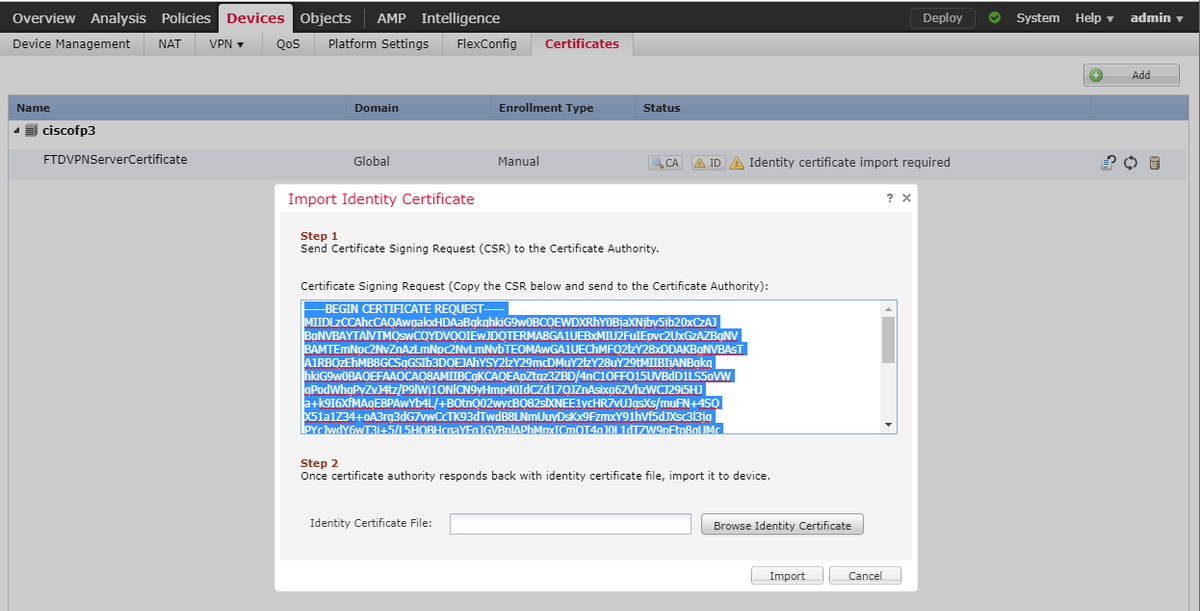
Select your FTDVPNServerCert we just created above and click Add
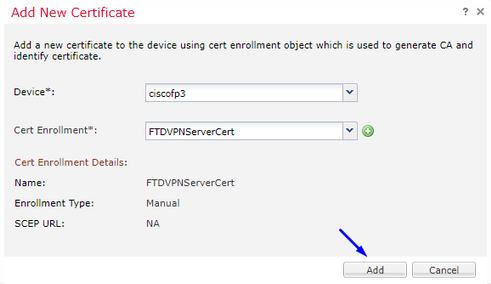
Tip: Wait about 10-30 seconds for the FMC + FTD to verify and install the Root CA certificate (click Refresh icon if it doesn't show)
Click the ID button:
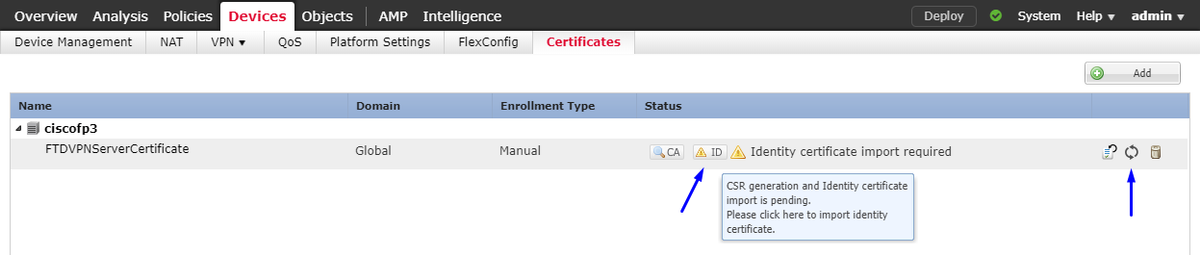
Copy and paste this CSR, and take it to your Windows Server Root CA:
Go to http://192.168.1.20/certsrv
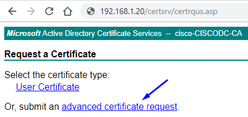
Click advanced certificate request
Paste your Certificate Signing Request (CSR) into the field below and select Web Server as the Certificate Template
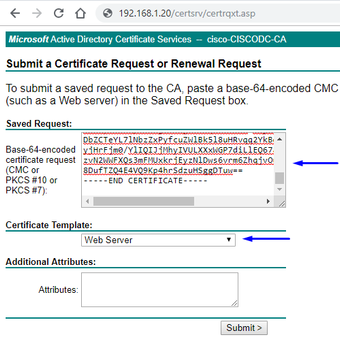
Click Submit
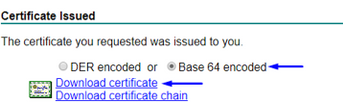
Click Base 64 encoded button and click Download certificate

Click Browse Identity Certificate and select the certificate we just downloaded
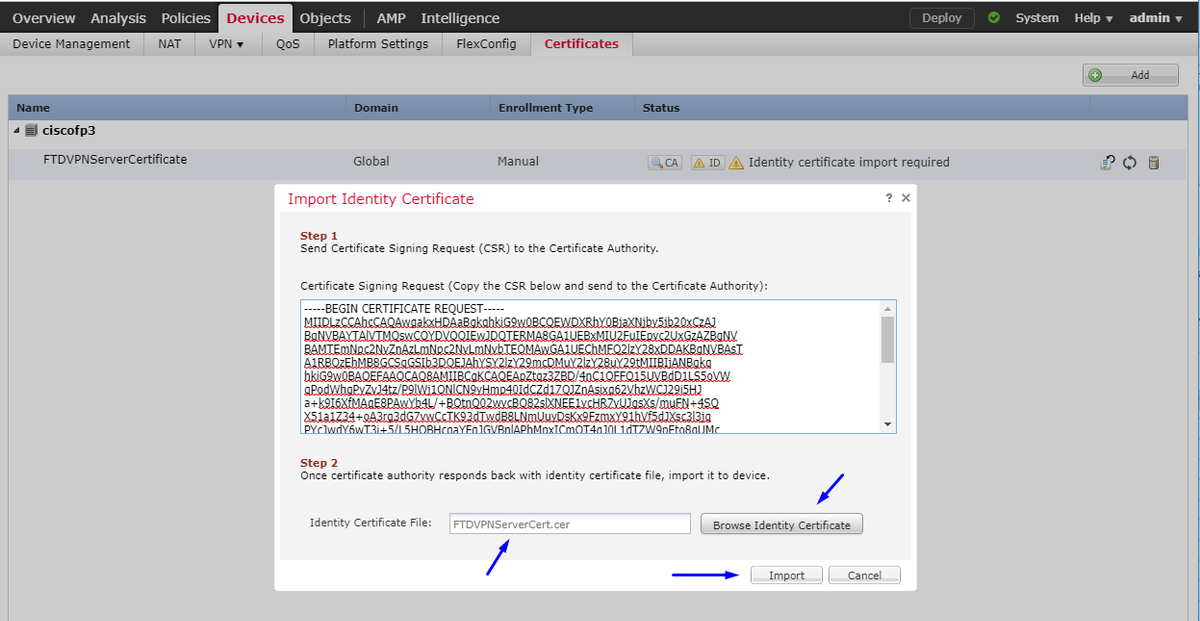
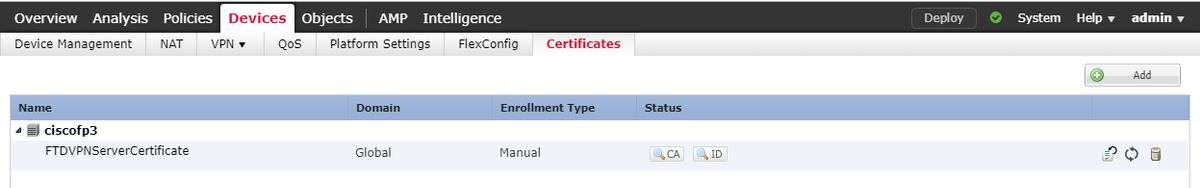
FTD VPN Server Certificate (signed by Windows Server Root CA) was installed successfully
Download AnyConnect image + AnyConnect Profile Editor and create a .xml profile
Download and install Cisco AnyConnect Profile Editor

Open AnyConnect Profile Editor
Click Server List > click Add...
Type a Display Name and the FQDN of your FTD's outside interface IP address. You should see entries in Server List
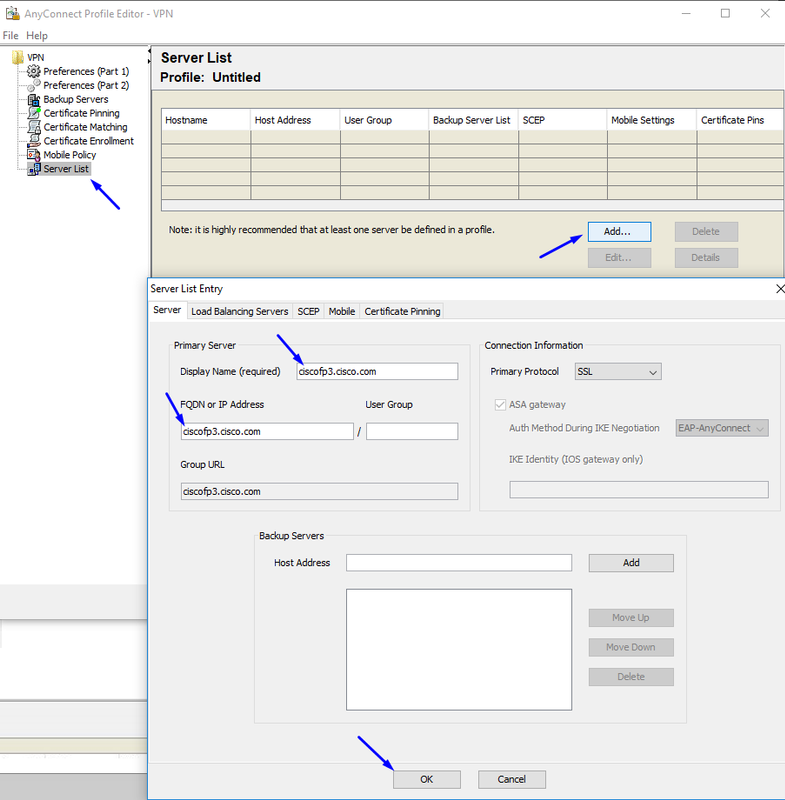
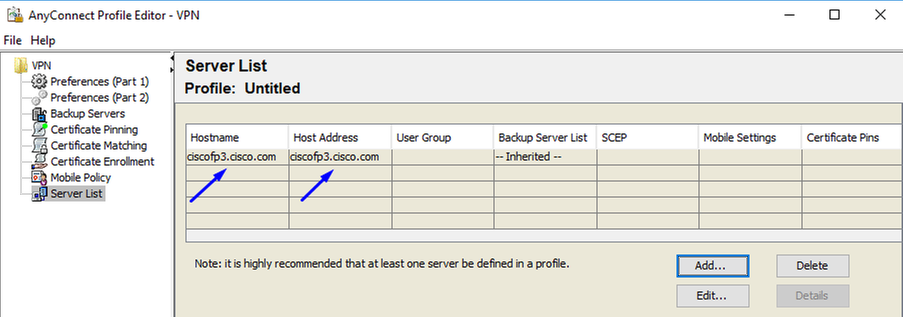
Click OK and File > Save as...
Download Windows and Mac .pkg images from here

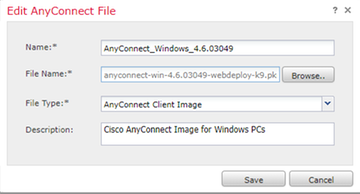
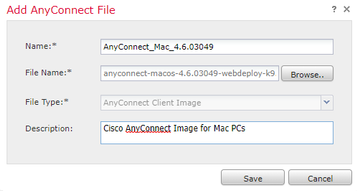
Go to Objects > Object Management > VPN > AnyConnect File > click Add AnyConnect File
Configure Anyconnect VPN on FTD (use the Root CA Certificate)
Login to the FirePOWER Management Center
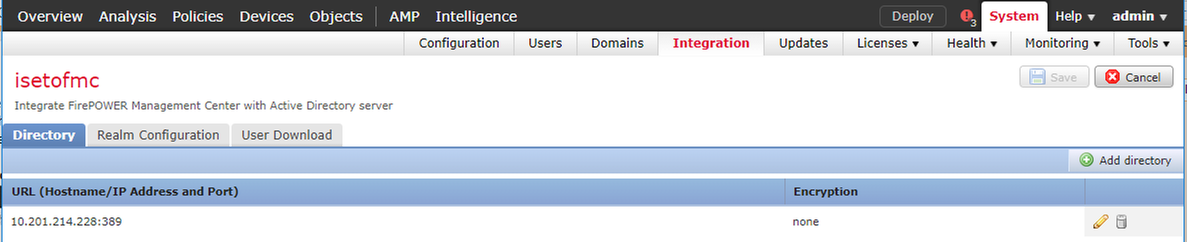
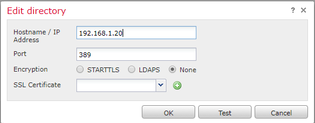
Click System > Integration > Realms > click New Realm >> click Directory tab > click Add directory
Click Realm Configuration tab - configure your domain controller's info here
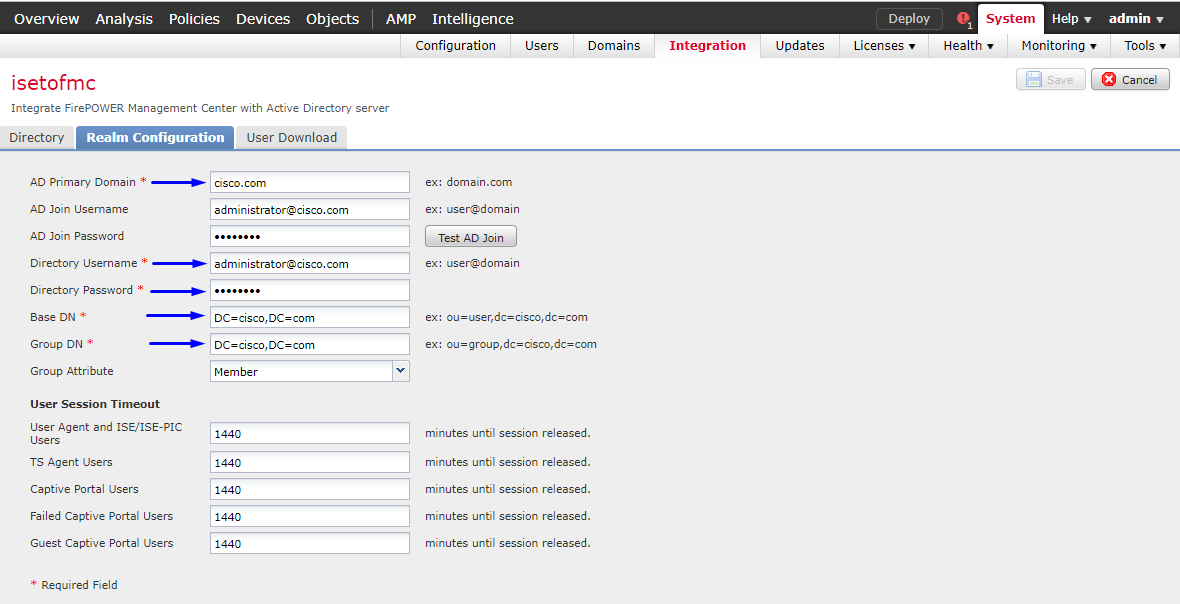
Note: In the above example, an AD username with 'Domain Admin' privileges in the Windows AD Server is used. If you want to configure a user with more specific, minimum permissions for the FMC to join your Active Directory Domain for your Realm configuration, you can see the steps here
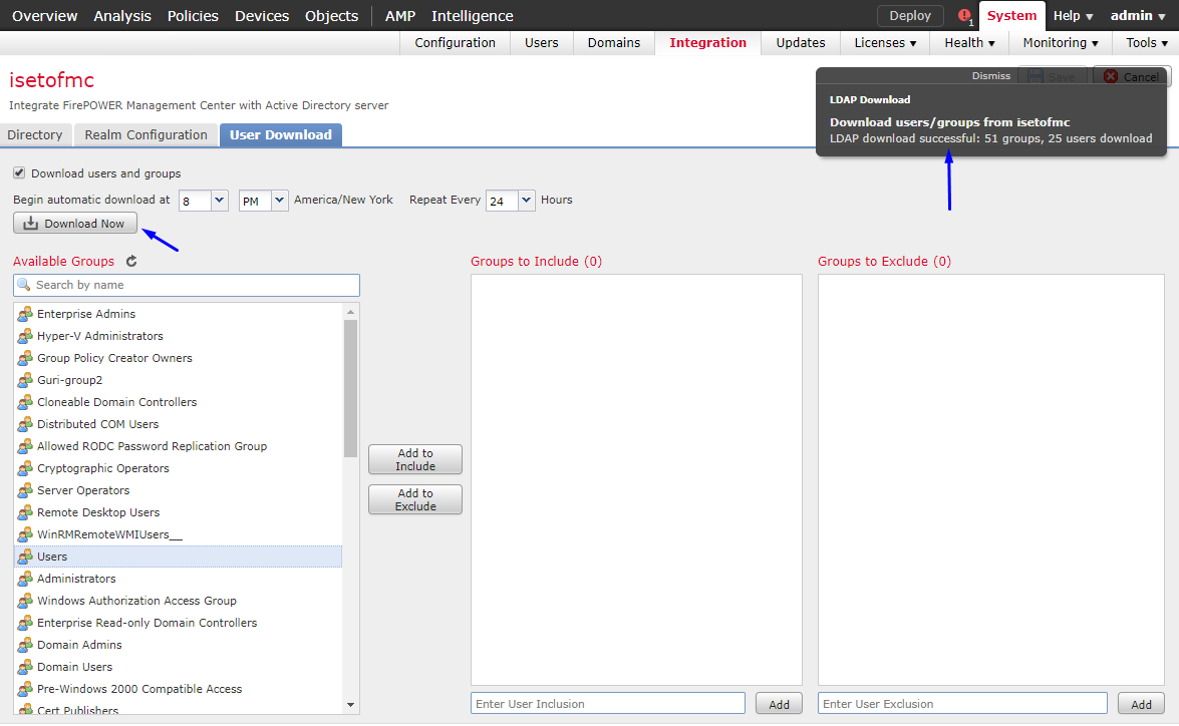
Click User Download tab - make sure User Download succeeds
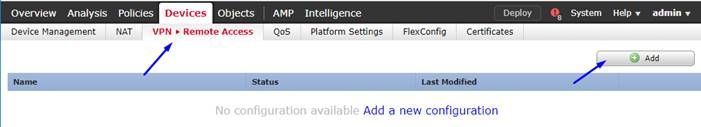
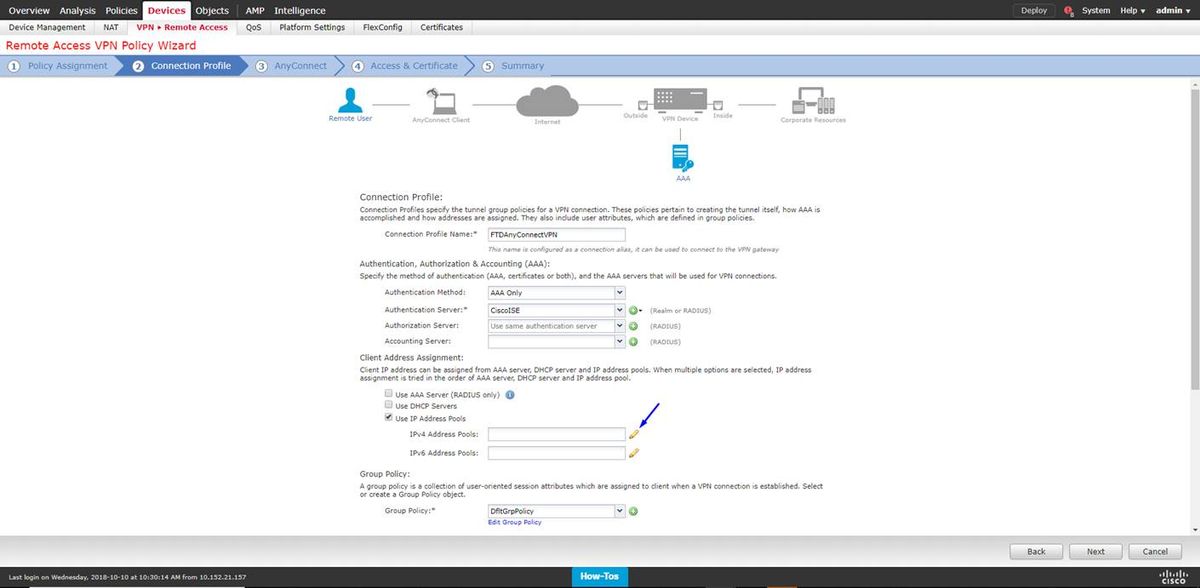
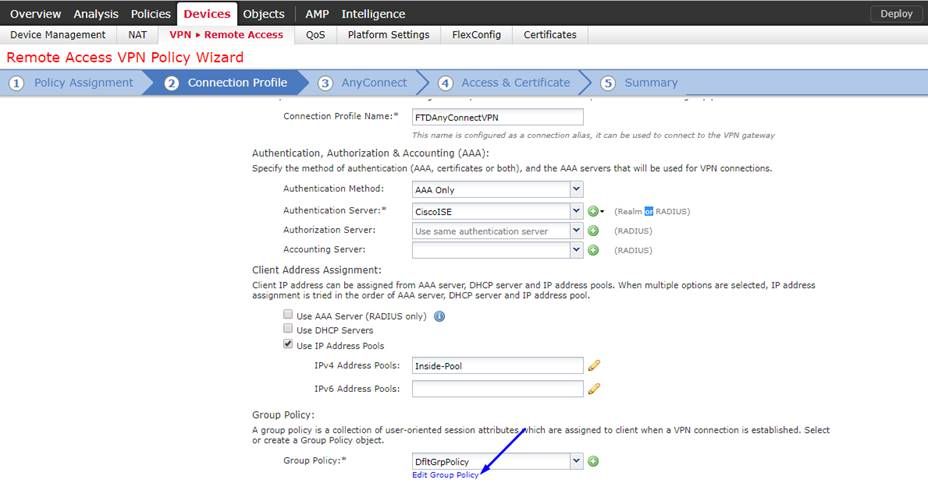
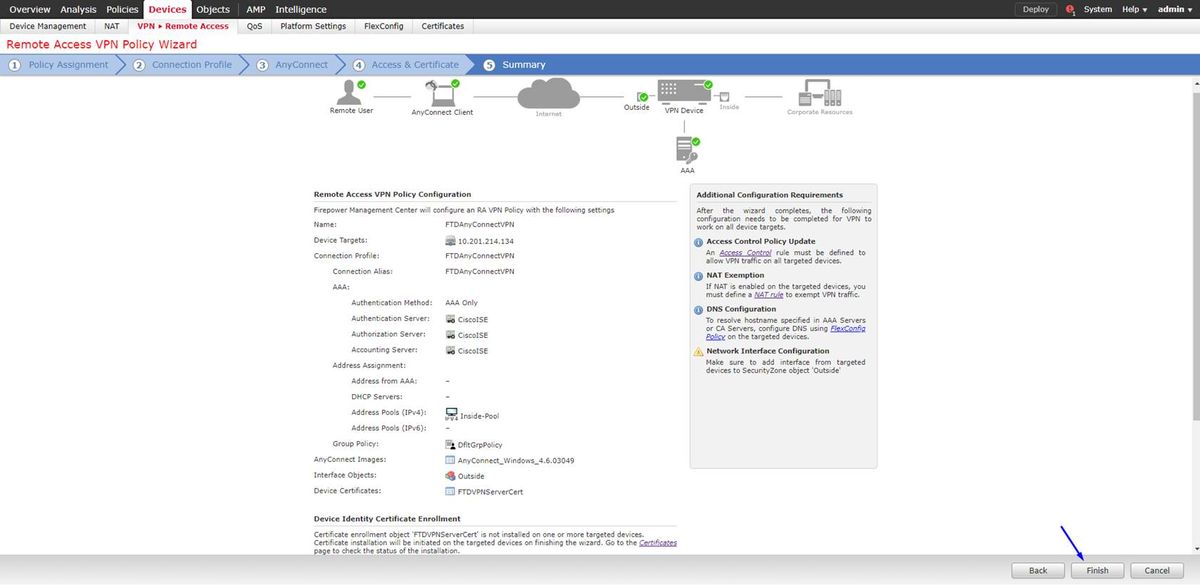
Click Devices > VPN > Remote Access > click Add
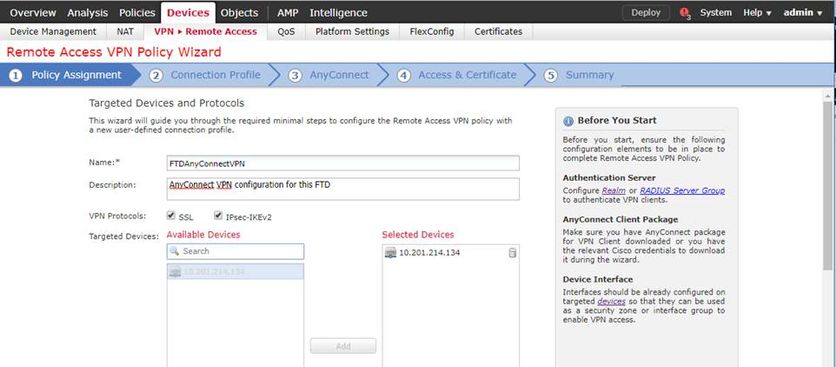
Type a Name, Description, and click Add to select the FTD device which you want to configure Anyconnect VPN on
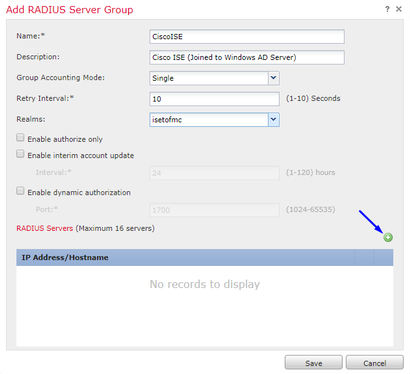
Click Add for the Authentication Server and choose RADIUS Server Group - this will be your Cisco Identity Services Engine PSN (Policy Services Node)
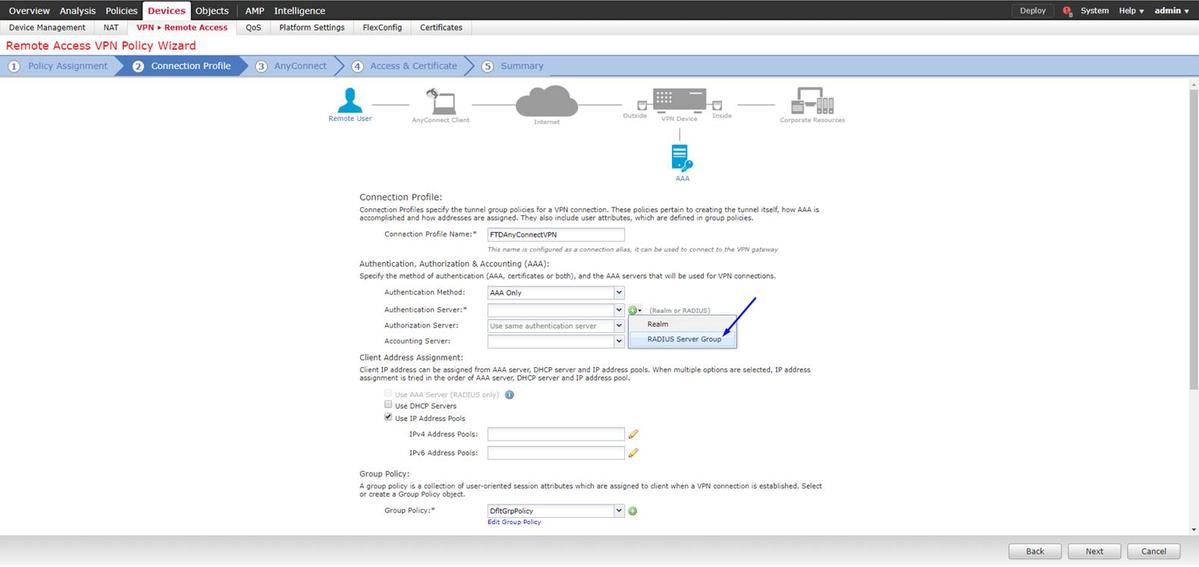
Type a Name for the RADIUS server
Select your Realm configured above
Click Add
Type the following info for your Cisco ISE node:
IP Address/Hostname: IP Address of Cisco ISE PSN (Policy Service Node) - this is where authentication requests will go
Key: cisco123
Confirm Key: cisco123
Caution: the above is your RADIUS Shared Secret key - we will use this key in a later step
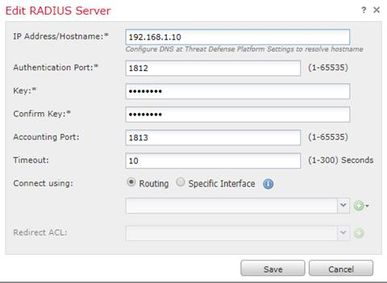
Note: When the end user attempts to connect to the FTD via AnyConnect VPN, the username + password they type will be sent as an authentication request to this FTD. The FTD will forward that request to the Cisco ISE PSN node for authentication (Cisco ISE will then check Windows Active Directory for that username and password, and enforce access control/network access depending on the condition we have currently configured in Cisco ISE)
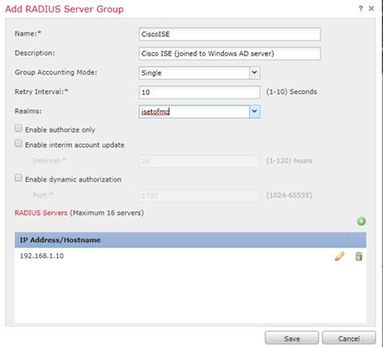
Click Save
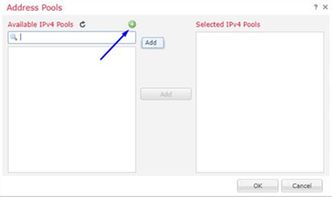
Click Edit for IPv4 Address Pool
Click Add
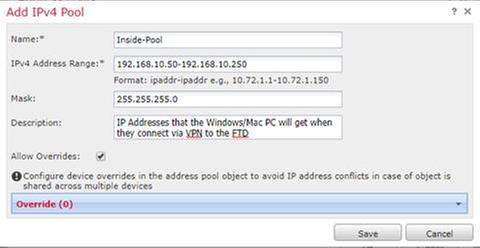
Type a Name, IPv4 Address Range, and Subnet Mask
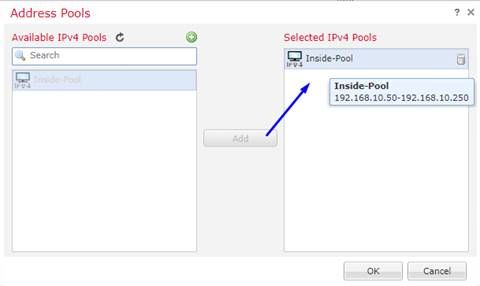
Select your IP address pool and click Okay
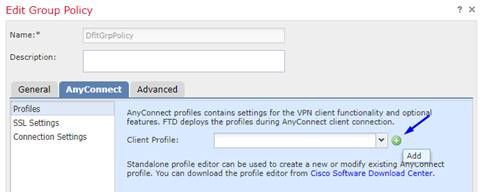
Click Edit Group Policy
Click Anyconnect tab > Profiles > click Add
Type a Name and click Browse… and select your VPNprofile.xml file from step 4 above
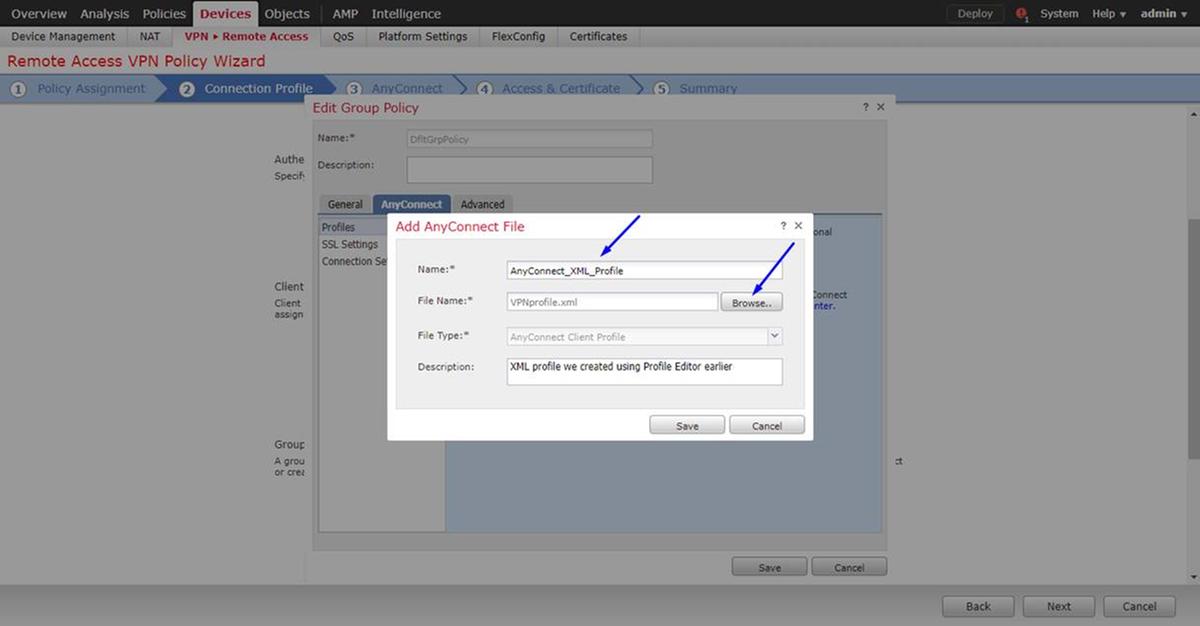
Click Save and click Next
Select the checkboxes for your AnyConnect Windows/Mac file from step 4 above
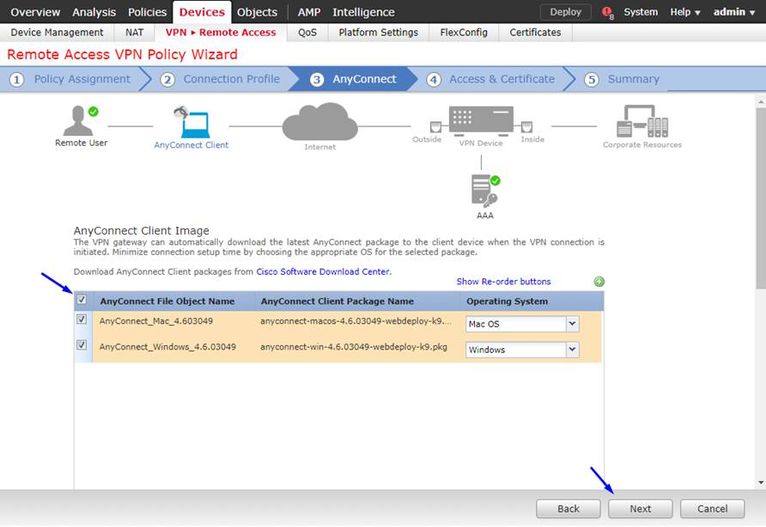
Click Next
Select Interface Group/Security Zone as Outside
Select Certificate Enrollment as your certificate we made in step 3 above
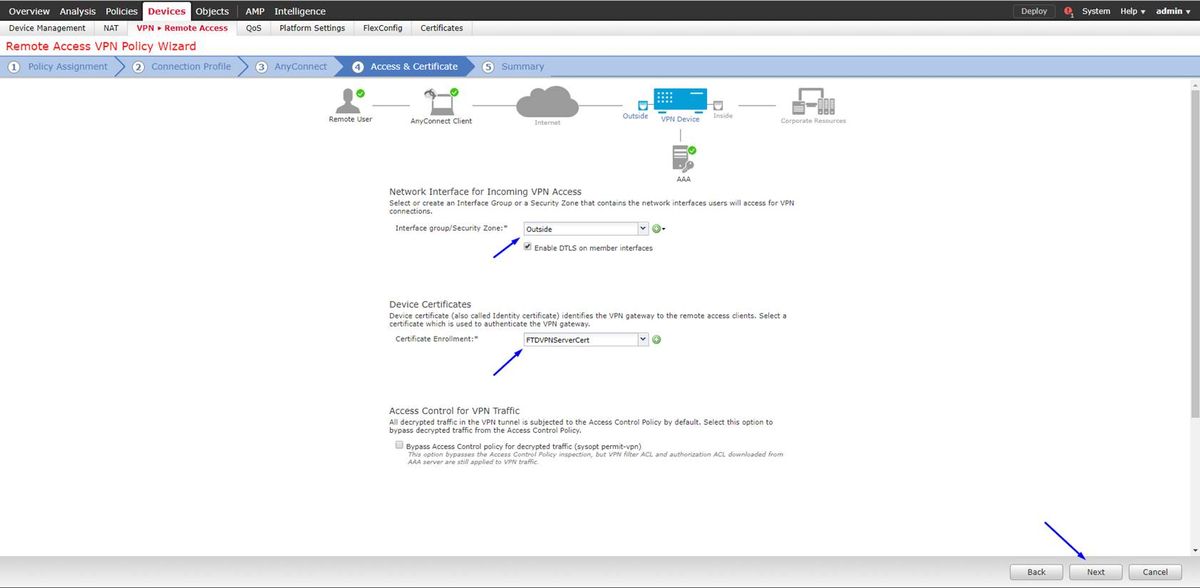
Review your configuration and click Next
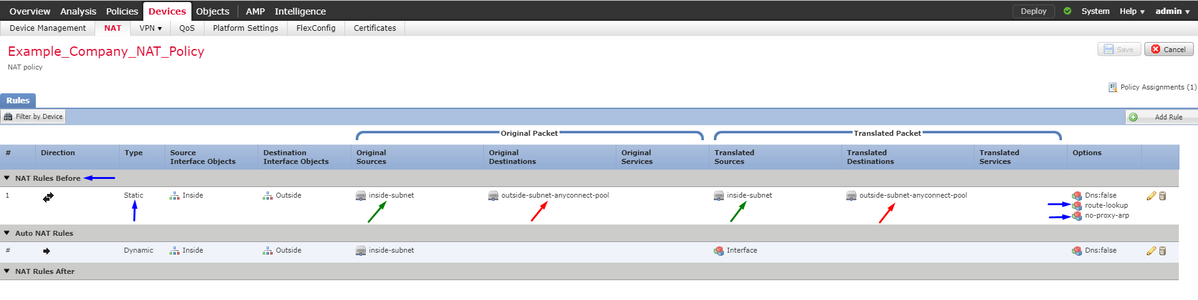
Configure FTD NAT rule to exempt the VPN traffic from NAT since it will be decrypted anyway and create Access Control Policy/Rules
Create a static NAT rule to make sure the VPN traffic does not get NAT'd (FTD already decrypts the AnyConnect packets as they come to the Outside interface, so it is as if that PC is already behind the inside interface, and they already have a private IP address - we still need to configure a NAT-Exempt (No-NAT) rule for that VPN traffic):
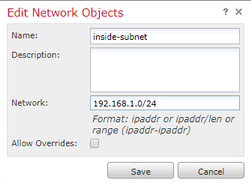
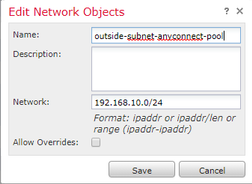
Go to Objects > click Add Network > click Add Object
Additionally, you must Allow the data traffic to flow after the user VPN's in. You have two choices for this:
a. Create Allow or Deny rules to Allow or Deny VPN users to access certain resources
b. Enable 'Bypass Access Control Policy for decrypted traffic' - this lets anyone who is able to successfully connect to the FTD via VPN bypass ACL's and access anything behind the FTD without going through Allow or Deny rules in Access Control Policy
Enable Bypass Access Control Policy for decrypted traffic under: Devices > VPN > Remote Access > VPN Profile > Access Interfaces:
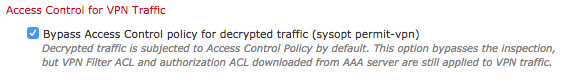
Note: If you do not enable this option, you will need to go to Policies > Access Control Policy and create Allow rules for the VPN users to be able to access things behind inside or dmz
ClickDeployin the top-right of the FirePOWER Management Center
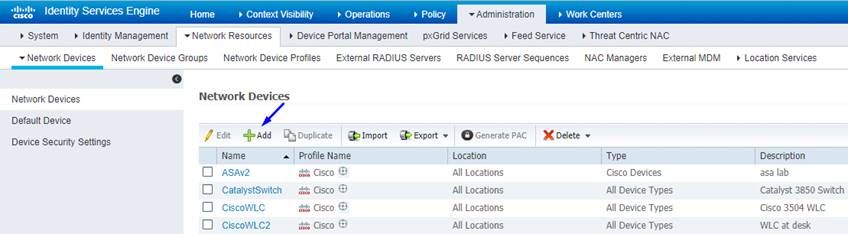
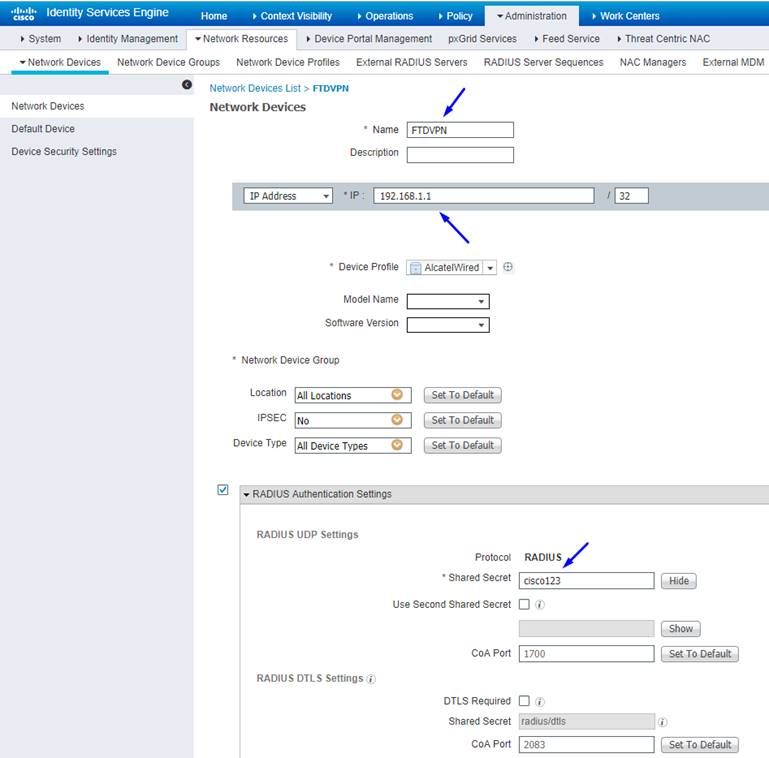
Add FTD as Network Device and configure policy set on Cisco ISE(use RADIUS shared secret)
Login to Cisco Identity Services Engine and click Administration > Network Devices > click Add
Type a Name, type the IP Address of your FTD, and type your RADIUS Shared Secret from the steps above
Caution: This must be the interface/ip address out which the FTD can reach your Cisco ISE (RADIUS Server) i.e. the FTD interface which your Cisco ISE can reach the FTD over
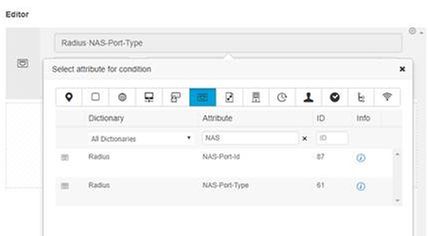
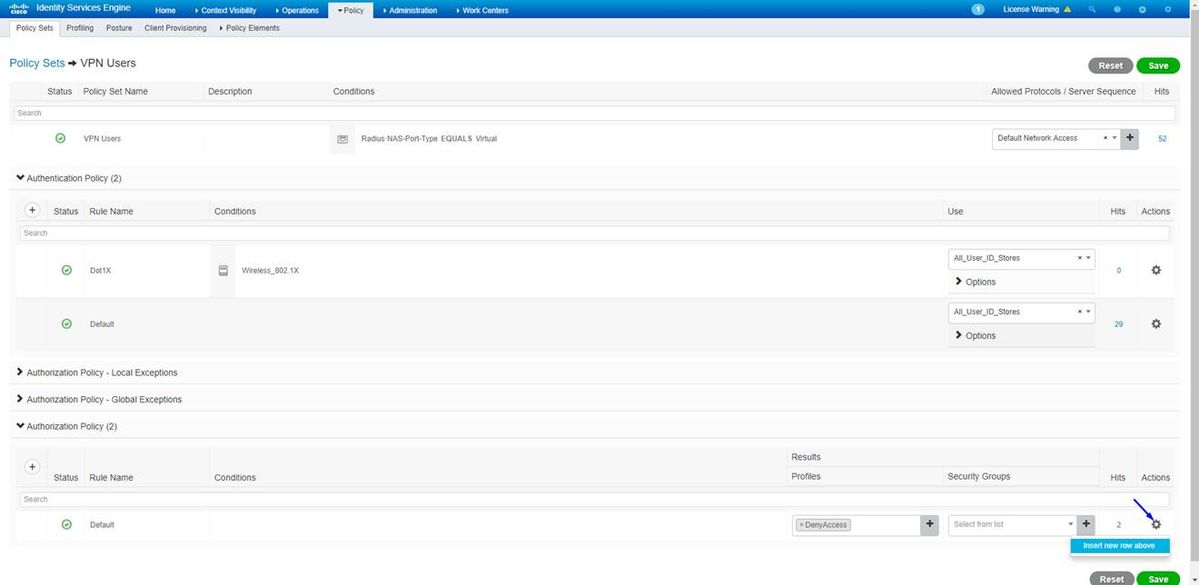
Click Policy > Policy Set > create a Policy Set for any authentication requests that come in of the following type:
Radius-NAS-Port-Type EQUALS Virtual
This means if any RADIUS requests that come into ISE that look like VPN connections, they will hit this Policy Set
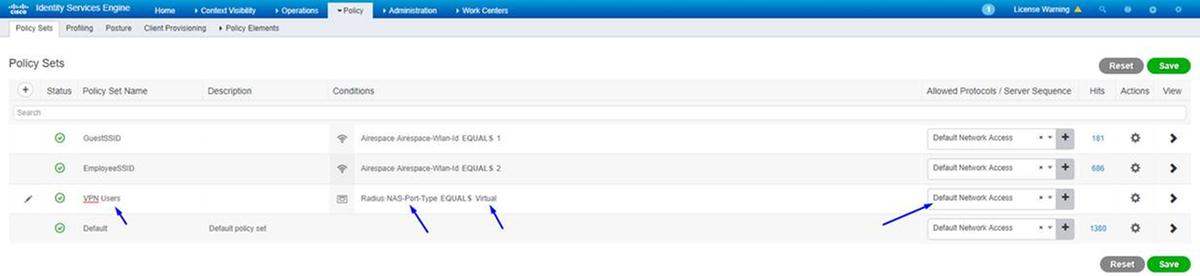
Here's where you can find that condition in Cisco ISE:
Edit the Policy Set you created above
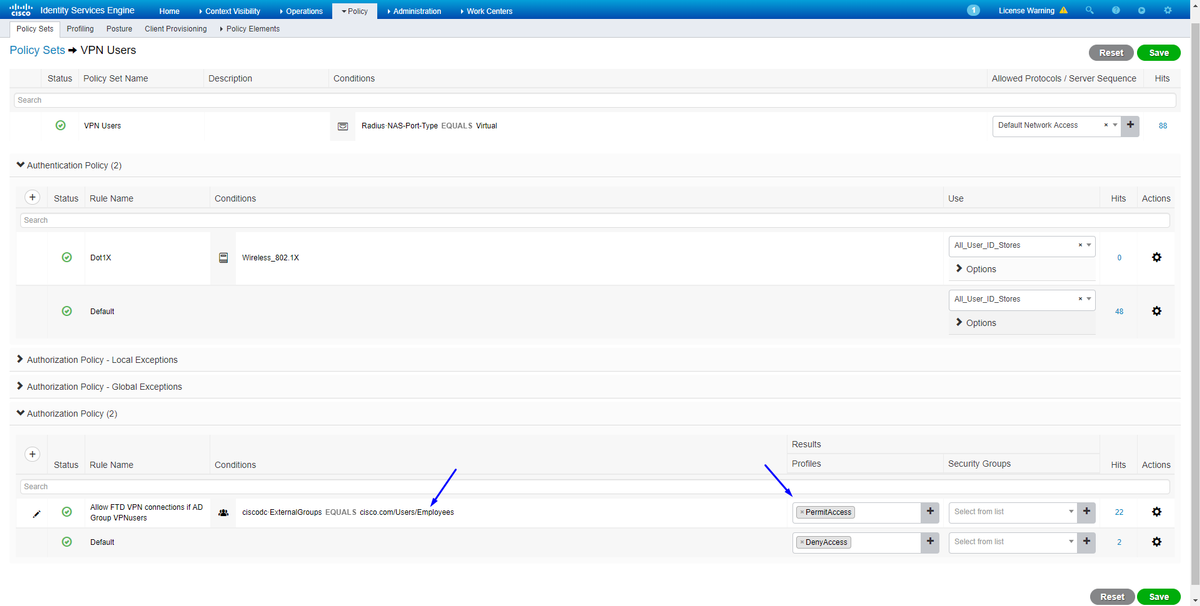
Add a rule above the default block rule to give people 'Permit Access' authorization profile only if they are in the Active Directory Group called 'Employees':
Below is how your rule will look once complete
Download, install and connect to the FTD using AnyConnect VPN Client on employee Windows/Mac PCs
Open your browser on the employee Windows/Mac PC, and go to the outside address of your FTD in your browser

Type your Active Directory username and password
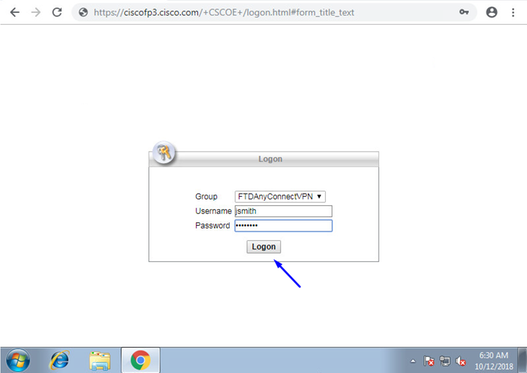
Click Download
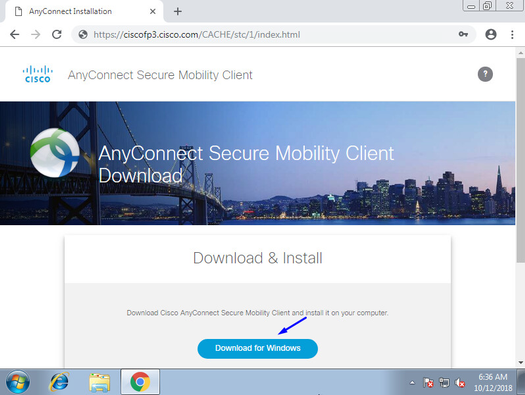
Install and Run AnyConnect VPN Secure Mobility Client on Windows/Mac PC
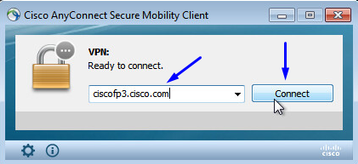
Type your Active Directory username and password when prompted
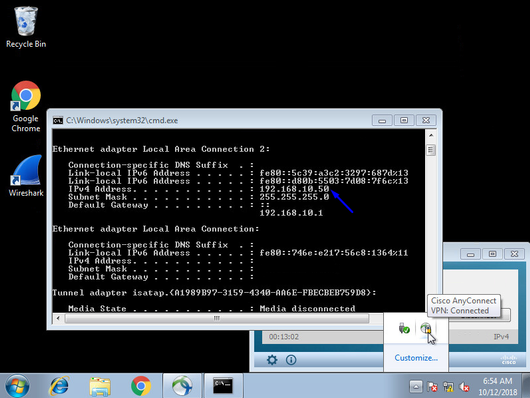
You will be given an IP address from the IP Address Pool created above in step 5 and a Default Gateway of the .1 in that subnet
Verify
FTD
Show Commands
Verify on FTD that end user is connected to AnyConnect VPN:
> show ip System IP Addresses: Interface Name IP address Subnet mask Method GigabitEthernet0/0 inside 192.168.1.1 255.255.255.240 CONFIG GigabitEthernet0/1 outside 203.0.113.2 255.255.255.240 CONFIG Current IP Addresses: Interface Name IP address Subnet mask Method GigabitEthernet0/0 inside 192.168.1.1 255.255.255.240 CONFIG GigabitEthernet0/1 outside 203.0.113.2 255.255.255.240 CONFIG
> show vpn-sessiondb detail anyconnect Session Type: AnyConnect Detailed Username : jsmith Index : 2 Assigned IP : 192.168.10.50 Public IP : 198.51.100.2 Protocol : AnyConnect-Parent SSL-Tunnel DTLS-Tunnel License : AnyConnect Premium Encryption : AnyConnect-Parent: (1)none SSL-Tunnel: (1)AES-GCM-256 DTLS-Tunnel: (1)AES256 Hashing : AnyConnect-Parent: (1)none SSL-Tunnel: (1)SHA384 DTLS-Tunnel: (1)SHA1 Bytes Tx : 18458 Bytes Rx : 2706024 Pkts Tx : 12 Pkts Rx : 50799 Pkts Tx Drop : 0 Pkts Rx Drop : 0 Group Policy : DfltGrpPolicy Tunnel Group : FTDAnyConnectVPN Login Time : 15:08:19 UTC Wed Oct 10 2018 Duration : 0h:30m:11s Inactivity : 0h:00m:00s VLAN Mapping : N/A VLAN : none Audt Sess ID : 0ac9d68a000020005bbe15e3 Security Grp : none Tunnel Zone : 0 AnyConnect-Parent Tunnels: 1 SSL-Tunnel Tunnels: 1 DTLS-Tunnel Tunnels: 1 AnyConnect-Parent: Tunnel ID : 2.1 Public IP : 198.51.100.2 Encryption : none Hashing : none TCP Src Port : 53956 TCP Dst Port : 443 Auth Mode : userPassword Idle Time Out: 30 Minutes Idle TO Left : 0 Minutes Client OS : win Client OS Ver: 6.1.7601 Service Pack 1 Client Type : AnyConnect Client Ver : Cisco AnyConnect VPN Agent for Windows 4.6.03049 Bytes Tx : 10572 Bytes Rx : 289 Pkts Tx : 6 Pkts Rx : 0 Pkts Tx Drop : 0 Pkts Rx Drop : 0 SSL-Tunnel: Tunnel ID : 2.2 Assigned IP : 192.168.10.50 Public IP : 198.51.100.2 Encryption : AES-GCM-256 Hashing : SHA384 Ciphersuite : ECDHE-RSA-AES256-GCM-SHA384 Encapsulation: TLSv1.2 TCP Src Port : 54634 TCP Dst Port : 443 Auth Mode : userPassword Idle Time Out: 30 Minutes Idle TO Left : 29 Minutes Client OS : Windows Client Type : SSL VPN Client Client Ver : Cisco AnyConnect VPN Agent for Windows 4.6.03049 Bytes Tx : 7886 Bytes Rx : 2519 Pkts Tx : 6 Pkts Rx : 24 Pkts Tx Drop : 0 Pkts Rx Drop : 0 DTLS-Tunnel: Tunnel ID : 2.3 Assigned IP : 192.168.10.50 Public IP : 198.51.100.2 Encryption : AES256 Hashing : SHA1 Ciphersuite : DHE-RSA-AES256-SHA Encapsulation: DTLSv1.0 UDP Src Port : 61113 UDP Dst Port : 443 Auth Mode : userPassword Idle Time Out: 30 Minutes Idle TO Left : 30 Minutes Client OS : Windows Client Type : DTLS VPN Client Client Ver : Cisco AnyConnect VPN Agent for Windows 4.6.03049 Bytes Tx : 0 Bytes Rx : 2703216 Pkts Tx : 0 Pkts Rx : 50775 Pkts Tx Drop : 0 Pkts Rx Drop : 0
Once you go on the Windows 7 PC and click 'Disconnect' on Cisco AnyConnect client, you'll get:
> show vpn-sessiondb detail anyconnect INFO: There are presently no active sessions
Captures
How a working capture looks like on Outside interface when you hit connect on AnyConnect Client
Example:
End user's public IP will be the public IP of their router at home for example
ciscofp3# capture capin interface outside trace detail trace-count 100 match ip any host <enduser'sPublicIPAddress> <now hit Connect on AnyConnect Client from employee PC> ciscofp3# show cap capture capin type raw-data trace detail trace-count 100 interface outside [Buffer Full - 524153 bytes] match ip any host 198.51.100.2
View the packets that came to the Outside interface of the FTD from the end user's PC to make sure they arrive on our Outside FTD interface:
ciscofp3# show cap capin 2375 packets captured 1: 17:05:56.580994 198.51.100.2.55928 > 203.0.113.2.443: S 2933933902:2933933902(0) win 8192 <mss 1460,nop,wscale 8,nop,nop,sackOK> 2: 17:05:56.581375 203.0.113.2.443 > 198.51.100.2.55928: S 430674106:430674106(0) ack 2933933903 win 32768 <mss 1460> 3: 17:05:56.581757 198.51.100.2.55928 > 203.0.113.2.443: . ack 430674107 win 64240 4: 17:05:56.582382 198.51.100.2.55928 > 203.0.113.2.443: P 2933933903:2933934036(133) ack 430674107 win 64240 5: 17:05:56.582458 203.0.113.2.443 > 198.51.100.2.55928: . ack 2933934036 win 32768 6: 17:05:56.582733 203.0.113.2.443 > 198.51.100.2.55928: P 430674107:430675567(1460) ack 2933934036 win 32768 7: 17:05:56.790211 198.51.100.2.55928 > 203.0.113.2.443: . ack 430675567 win 64240 8: 17:05:56.790349 203.0.113.2.443 > 198.51.100.2.55928: P 430675567:430676672(1105) ack 2933934036 win 32768 9: 17:05:56.791691 198.51.100.2.55928 > 203.0.113.2.443: P 2933934036:2933934394(358) ack 430676672 win 63135 10: 17:05:56.794911 203.0.113.2.443 > 198.51.100.2.55928: P 430676672:430676763(91) ack 2933934394 win 32768 11: 17:05:56.797077 198.51.100.2.55928 > 203.0.113.2.443: P 2933934394:2933934703(309) ack 430676763 win 63044 12: 17:05:56.797169 203.0.113.2.443 > 198.51.100.2.55928: . ack 2933934703 win 32768 13: 17:05:56.797199 198.51.100.2.55928 > 203.0.113.2.443: P 2933934703:2933935524(821) ack 430676763 win 63044 14: 17:05:56.797276 203.0.113.2.443 > 198.51.100.2.55928: . ack 2933935524 win 32768 15: 17:05:56.798634 203.0.113.2.443 > 198.51.100.2.55928: P 430676763:430677072(309) ack 2933935524 win 32768 16: 17:05:56.798786 203.0.113.2.443 > 198.51.100.2.55928: P 430677072:430677829(757) ack 2933935524 win 32768 17: 17:05:56.798817 203.0.113.2.443 > 198.51.100.2.55928: P 430677829:430677898(69) ack 2933935524 win 32768 18: 17:05:56.799397 198.51.100.2.55928 > 203.0.113.2.443: . ack 430677898 win 64240 19: 17:05:56.810215 198.51.100.2.55928 > 203.0.113.2.443: P 2933935524:2933935593(69) ack 430677898 win 64240 20: 17:05:56.810398 203.0.113.2.443 > 198.51.100.2.55928: . ack 2933935593 win 32768 21: 17:05:56.810428 198.51.100.2.55928 > 203.0.113.2.443: F 2933935593:2933935593(0) ack 430677898 win 64240 22: 17:05:56.810489 203.0.113.2.443 > 198.51.100.2.55928: . ack 2933935594 win 32768 23: 17:05:56.810627 203.0.113.2.443 > 198.51.100.2.55928: FP 430677898:430677898(0) ack 2933935594 win 32768 24: 17:05:56.811008 198.51.100.2.55928 > 203.0.113.2.443: . ack 430677899 win 64240 25: 17:05:59.250566 198.51.100.2.56228 > 203.0.113.2.443: S 2614357960:2614357960(0) win 8192 <mss 1460,nop,wscale 8,nop,nop,sackOK> 26: 17:05:59.250963 203.0.113.2.443 > 198.51.100.2.56228: S 3940915253:3940915253(0) ack 2614357961 win 32768 <mss 1460> 27: 17:05:59.251406 198.51.100.2.56228 > 203.0.113.2.443: . ack 3940915254 win 64240 28: 17:05:59.252062 198.51.100.2.56228 > 203.0.113.2.443: P 2614357961:2614358126(165) ack 3940915254 win 64240 29: 17:05:59.252138 203.0.113.2.443 > 198.51.100.2.56228: . ack 2614358126 win 32768 30: 17:05:59.252458 203.0.113.2.443 > 198.51.100.2.56228: P 3940915254:3940915431(177) ack 2614358126 win 32768 31: 17:05:59.253450 198.51.100.2.56228 > 203.0.113.2.443: P 2614358126:2614358217(91) ack 3940915431 win 64063 32: 17:05:59.253679 203.0.113.2.443 > 198.51.100.2.56228: . ack 2614358217 win 32768 33: 17:05:59.255235 198.51.100.2.56228 > 203.0.113.2.443: P 2614358217:2614358526(309) ack 3940915431 win 64063 34: 17:05:59.255357 203.0.113.2.443 > 198.51.100.2.56228: . ack 2614358526 win 32768 35: 17:05:59.255388 198.51.100.2.56228 > 203.0.113.2.443: P 2614358526:2614359555(1029) ack 3940915431 win 64063 36: 17:05:59.255495 203.0.113.2.443 > 198.51.100.2.56228: . ack 2614359555 win 32768 37: 17:05:59.400110 203.0.113.2.443 > 198.51.100.2.56228: P 3940915431:3940915740(309) ack 2614359555 win 32768 38: 17:05:59.400186 203.0.113.2.443 > 198.51.100.2.56228: P 3940915740:3940917069(1329) ack 2614359555 win 32768 39: 17:05:59.400675 198.51.100.2.56228 > 203.0.113.2.443: . ack 3940917069 win 64240 40: 17:05:59.400736 203.0.113.2.443 > 198.51.100.2.56228: P 3940917069:3940918529(1460) ack 2614359555 win 32768 41: 17:05:59.400751 203.0.113.2.443 > 198.51.100.2.56228: P 3940918529:3940919979(1450) ack 2614359555 win 32768 42: 17:05:59.401544 198.51.100.2.56228 > 203.0.113.2.443: . ack 3940919979 win 64240 43: 17:05:59.401605 203.0.113.2.443 > 198.51.100.2.56228: P 3940919979:3940921439(1460) ack 2614359555 win 32768 44: 17:05:59.401666 203.0.113.2.443 > 198.51.100.2.56228: P 3940921439:3940922899(1460) ack 2614359555 win 32768 45: 17:05:59.401727 203.0.113.2.443 > 198.51.100.2.56228: P 3940922899:3940923306(407) ack 2614359555 win 32768 46: 17:05:59.401743 203.0.113.2.443 > 198.51.100.2.56228: P 3940923306:3940923375(69) ack 2614359555 win 32768 47: 17:05:59.402185 198.51.100.2.56228 > 203.0.113.2.443: . ack 3940923375 win 64240 48: 17:05:59.402475 198.51.100.2.56228 > 203.0.113.2.443: P 2614359555:2614359624(69) ack 3940923375 win 64240 49: 17:05:59.402597 203.0.113.2.443 > 198.51.100.2.56228: . ack 2614359624 win 32768 50: 17:05:59.402628 198.51.100.2.56228 > 203.0.113.2.443: F 2614359624:2614359624(0) ack 3940923375 win 64240 51: 17:05:59.402673 203.0.113.2.443 > 198.51.100.2.56228: . ack 2614359625 win 32768 52: 17:05:59.402765 203.0.113.2.443 > 198.51.100.2.56228: FP 3940923375:3940923375(0) ack 2614359625 win 32768 53: 17:05:59.413384 198.51.100.2.56228 > 203.0.113.2.443: . ack 3940923376 win 64240 54: 17:05:59.555665 198.51.100.2.56280 > 203.0.113.2.443: S 1903869753:1903869753(0) win 8192 <mss 1460,nop,wscale 8,nop,nop,sackOK> 55: 17:05:59.556154 203.0.113.2.443 > 198.51.100.2.56280: S 2583094766:2583094766(0) ack 1903869754 win 32768 <mss 1460> 56: 17:05:59.556627 198.51.100.2.56280 > 203.0.113.2.443: . ack 2583094767 win 64240 57: 17:05:59.560502 198.51.100.2.56280 > 203.0.113.2.443: P 1903869754:1903869906(152) ack 2583094767 win 64240 58: 17:05:59.560578 203.0.113.2.443 > 198.51.100.2.56280: . ack 1903869906 win 32768 59: 17:05:59.563996 203.0.113.2.443 > 198.51.100.2.56280: P 2583094767:2583096227(1460) ack 1903869906 win 32768 60: 17:05:59.780034 198.51.100.2.56280 > 203.0.113.2.443: . ack 2583096227 win 64240 61: 17:05:59.780141 203.0.113.2.443 > 198.51.100.2.56280: P 2583096227:2583097673(1446) ack 1903869906 win 32768 62: 17:05:59.998376 198.51.100.2.56280 > 203.0.113.2.443: . ack 2583097673 win 62794 63: 17:06:14.809253 198.51.100.2.56280 > 203.0.113.2.443: P 1903869906:1903870032(126) ack 2583097673 win 62794 64: 17:06:14.809970 203.0.113.2.443 > 198.51.100.2.56280: P 2583097673:2583097724(51) ack 1903870032 win 32768 65: 17:06:14.815768 198.51.100.2.56280 > 203.0.113.2.443: P 1903870032:1903870968(936) ack 2583097724 win 64240 66: 17:06:14.815860 203.0.113.2.443 > 198.51.100.2.56280: . ack 1903870968 win 32768 67: 17:06:14.816913 203.0.113.2.443 > 198.51.100.2.56280: P 2583097724:2583099184(1460) ack 1903870968 win 32768 68: 17:06:14.816928 203.0.113.2.443 > 198.51.100.2.56280: P 2583099184:2583099306(122) ack 1903870968 win 32768 69: 17:06:14.816959 203.0.113.2.443 > 198.51.100.2.56280: P 2583099306:2583100766(1460) ack 1903870968 win 32768 70: 17:06:14.816974 203.0.113.2.443 > 198.51.100.2.56280: P 2583100766:2583100888(122) ack 1903870968 win 32768 71: 17:06:14.816989 203.0.113.2.443 > 198.51.100.2.56280: P 2583100888:2583102142(1254) ack 1903870968 win 32768 72: 17:06:14.817554 198.51.100.2.56280 > 203.0.113.2.443: . ack 2583102142 win 64240 73: 17:06:14.817615 203.0.113.2.443 > 198.51.100.2.56280: P 2583102142:2583103602(1460) ack 1903870968 win 32768 74: 17:06:14.817630 203.0.113.2.443 > 198.51.100.2.56280: P 2583103602:2583103930(328) ack 1903870968 win 32768 75: 17:06:14.817630 203.0.113.2.443 > 198.51.100.2.56280: P 2583103930:2583104052(122) ack 1903870968 win 32768 76: 17:06:14.817645 203.0.113.2.443 > 198.51.100.2.56280: P 2583104052:2583105512(1460) ack 1903870968 win 32768 77: 17:06:14.817645 203.0.113.2.443 > 198.51.100.2.56280: P 2583105512:2583105634(122) ack 1903870968 win 32768 78: 17:06:14.817660 203.0.113.2.443 > 198.51.100.2.56280: P 2583105634:2583105738(104) ack 1903870968 win 32768 79: 17:06:14.818088 198.51.100.2.56280 > 203.0.113.2.443: . ack 2583105512 win 64240 80: 17:06:14.818530 198.51.100.2.56280 > 203.0.113.2.443: . ack 2583105738 win 64014 81: 17:06:18.215122 198.51.100.2.58944 > 203.0.113.2.443: udp 99 82: 17:06:18.215610 203.0.113.2.443 > 198.51.100.2.58944: udp 48 83: 17:06:18.215671 198.51.100.2.56280 > 203.0.113.2.443: P 1903870968:1903872025(1057) ack 2583105738 win 64014 84: 17:06:18.215763 203.0.113.2.443 > 198.51.100.2.56280: . ack 1903872025 win 32768 85: 17:06:18.247011 198.51.100.2.58944 > 203.0.113.2.443: udp 119 86: 17:06:18.247728 203.0.113.2.443 > 198.51.100.2.58944: udp 188 87: 17:06:18.249285 198.51.100.2.58944 > 203.0.113.2.443: udp 93 88: 17:06:18.272309 198.51.100.2.58944 > 203.0.113.2.443: udp 93 89: 17:06:18.277680 198.51.100.2.58944 > 203.0.113.2.443: udp 93 90: 17:06:18.334501 198.51.100.2.58944 > 203.0.113.2.443: udp 221 91: 17:06:18.381541 198.51.100.2.58944 > 203.0.113.2.443: udp 109 92: 17:06:18.443565 198.51.100.2.58944 > 203.0.113.2.443: udp 109 93: 17:06:18.786702 198.51.100.2.58944 > 203.0.113.2.443: udp 157 94: 17:06:18.786870 198.51.100.2.58944 > 203.0.113.2.443: udp 157 95: 17:06:18.786931 198.51.100.2.58944 > 203.0.113.2.443: udp 157 96: 17:06:18.952755 198.51.100.2.58944 > 203.0.113.2.443: udp 109 97: 17:06:18.968272 198.51.100.2.58944 > 203.0.113.2.443: udp 109 98: 17:06:18.973902 198.51.100.2.58944 > 203.0.113.2.443: udp 109 99: 17:06:18.973994 198.51.100.2.58944 > 203.0.113.2.443: udp 109 100: 17:06:18.989267 198.51.100.2.58944 > 203.0.113.2.443: udp 109
View the details of what happens to that packet that comes in from the end user within the firewall
ciscofp3# show cap capin packet-number 1 trace detail 2943 packets captured 1: 17:05:56.580994 006b.f1e7.6c5e 000c.294f.ac84 0x0800 Length: 66 198.51.100.2.55928 > 203.0.113.2.443: S [tcp sum ok] 2933933902:2933933902(0) win 8192 <mss 1460,nop,wscale 8,nop,nop,sackOK> (DF) (ttl 127, id 31008) Phase: 1 Type: CAPTURE Subtype: Result: ALLOW Config: Additional Information: Forward Flow based lookup yields rule: in id=0x2ace13beec90, priority=13, domain=capture, deny=false hits=2737, user_data=0x2ace1232af40, cs_id=0x0, l3_type=0x0 src mac=0000.0000.0000, mask=0000.0000.0000 dst mac=0000.0000.0000, mask=0000.0000.0000 input_ifc=outside, output_ifc=any Phase: 2 Type: ACCESS-LIST Subtype: Result: ALLOW Config: Implicit Rule Additional Information: Forward Flow based lookup yields rule: in id=0x2ace107c8480, priority=1, domain=permit, deny=false hits=183698, user_data=0x0, cs_id=0x0, l3_type=0x8 src mac=0000.0000.0000, mask=0000.0000.0000 dst mac=0000.0000.0000, mask=0100.0000.0000 input_ifc=outside, output_ifc=any Phase: 3 Type: ROUTE-LOOKUP Subtype: Resolve Egress Interface Result: ALLOW Config: Additional Information: found next-hop 203.0.113.2 using egress ifc identity Phase: 4 Type: ACCESS-LIST Subtype: Result: ALLOW Config: Implicit Rule Additional Information: Forward Flow based lookup yields rule: in id=0x2ace1199f680, priority=119, domain=permit, deny=false hits=68, user_data=0x0, cs_id=0x0, flags=0x0, protocol=6 src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any dst ip/id=0.0.0.0, mask=0.0.0.0, port=443, tag=any, dscp=0x0 input_ifc=outside, output_ifc=identity Phase: 5 Type: CONN-SETTINGS Subtype: Result: ALLOW Config: Additional Information: Forward Flow based lookup yields rule: in id=0x2ace1199efd0, priority=8, domain=conn-set, deny=false hits=68, user_data=0x2ace1199e5d0, cs_id=0x0, reverse, flags=0x0, protocol=6 src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any dst ip/id=0.0.0.0, mask=0.0.0.0, port=443, tag=any, dscp=0x0 input_ifc=outside, output_ifc=identity Phase: 6 Type: NAT Subtype: per-session Result: ALLOW Config: Additional Information: Forward Flow based lookup yields rule: in id=0x2ace0fa81330, priority=0, domain=nat-per-session, deny=false hits=178978, user_data=0x0, cs_id=0x0, reverse, use_real_addr, flags=0x0, protocol=6 src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0 input_ifc=any, output_ifc=any Phase: 7 Type: IP-OPTIONS Subtype: Result: ALLOW Config: Additional Information: Forward Flow based lookup yields rule: in id=0x2ace107cdb00, priority=0, domain=inspect-ip-options, deny=true hits=174376, user_data=0x0, cs_id=0x0, reverse, flags=0x0, protocol=0 src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0 input_ifc=outside, output_ifc=any Phase: 8 Type: CLUSTER-REDIRECT Subtype: cluster-redirect Result: ALLOW Config: Additional Information: Forward Flow based lookup yields rule: in id=0x2ace107c90c0, priority=208, domain=cluster-redirect, deny=false hits=78, user_data=0x0, cs_id=0x0, flags=0x0, protocol=0 src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0 input_ifc=outside, output_ifc=identity Phase: 9 Type: TCP-MODULE Subtype: webvpn Result: ALLOW Config: Additional Information: Forward Flow based lookup yields rule: in id=0x2ace1199df20, priority=13, domain=soft-np-tcp-module, deny=false hits=58, user_data=0x2ace061efb00, cs_id=0x0, reverse, flags=0x0, protocol=6 src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any dst ip/id=0.0.0.0, mask=0.0.0.0, port=443, tag=any, dscp=0x0 input_ifc=outside, output_ifc=identity Phase: 10 Type: VPN Subtype: ipsec-tunnel-flow Result: ALLOW Config: Additional Information: Forward Flow based lookup yields rule: in id=0x2ace11d455e0, priority=13, domain=ipsec-tunnel-flow, deny=true hits=87214, user_data=0x0, cs_id=0x0, flags=0x0, protocol=0 src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0 input_ifc=outside, output_ifc=any Phase: 11 Type: CAPTURE Subtype: Result: ALLOW Config: Additional Information: Forward Flow based lookup yields rule: in id=0x2ace11da7000, priority=13, domain=capture, deny=false hits=635, user_data=0x2ace1232af40, cs_id=0x2ace11f21620, reverse, flags=0x0, protocol=0 src ip/id=198.51.100.2, mask=255.255.255.255, port=0, tag=any dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0 input_ifc=outside, output_ifc=any Phase: 12 Type: CAPTURE Subtype: Result: ALLOW Config: Additional Information: Reverse Flow based lookup yields rule: out id=0x2ace10691780, priority=13, domain=capture, deny=false hits=9, user_data=0x2ace1232af40, cs_id=0x2ace11f21620, reverse, flags=0x0, protocol=0 src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any dst ip/id=198.51.100.2, mask=255.255.255.255, port=0, tag=any, dscp=0x0 input_ifc=any, output_ifc=outside Phase: 13 Type: FLOW-CREATION Subtype: Result: ALLOW Config: Additional Information: New flow created with id 87237, packet dispatched to next module Module information for forward flow ... snp_fp_inspect_ip_options snp_fp_tcp_normalizer snp_fp_tcp_mod snp_fp_adjacency snp_fp_fragment snp_fp_drop Module information for reverse flow ... snp_fp_inspect_ip_options snp_fp_tcp_normalizer snp_fp_adjacency snp_fp_fragment snp_ifc_stat Result: input-interface: outside input-status: up input-line-status: up output-interface: NP Identity Ifc Action: allow 1 packet shown ciscofp3#
Copy the capture to disk0: of your FTD. You can then download it via SCP, FTP, or TFTP
(or from FirePOWER Management Center Web UI >> System >> Health >> Health Monitor >> click Advanced Troubleshooting >> click Download File tab)
ciscofp3# copy /pcap capture:capin disk0:/capin.pcap Source capture name [capin]? <hit Enter> Destination filename [capin.pcap]? <hit Enter> !!!!!!!!!!!!!!! 207 packets copied in 0.0 secs ciscofp3# dir Directory of disk0:/ 122 -rwx 198 05:13:44 Apr 01 2018 lina_phase1.log 49 drwx 4096 21:42:20 Jun 30 2018 log 53 drwx 4096 21:42:36 Jun 30 2018 coredumpinfo 110 drwx 4096 14:59:51 Oct 10 2018 csm 123 -rwx 21074 01:26:44 Oct 10 2018 backup-config.cfg 124 -rwx 21074 01:26:44 Oct 10 2018 startup-config 125 -rwx 20354 01:26:44 Oct 10 2018 modified-config.cfg 160 -rwx 60124 17:06:22 Oct 10 2018 capin.pcap
ciscofp3# copy disk0:/capin.pcap tftp:/
Source filename [capin.pcap]? <hit Enter>
Address or name of remote host []? 192.168.1.25 (your TFTP server IP address (your PC if using tftpd32 or Solarwinds TFTP Server))
Destination filename [capin.pcap]? <hit Enter>
113645 bytes copied in 21.800 secs (5411 bytes/sec)
ciscofp3#
(or from FirePOWER Management Center Web GUI >> System >> Health >> Health Monitor >> click Advanced Troubleshooting >> click Download File tab)
Verify NAT rule is correctly configured:
ciscofp3# packet-tracer input outside tcp 192.168.10.50 1234 192.168.1.30 443 detailed Phase: 1 Type: CAPTURE Subtype: Result: ALLOW Config: Additional Information: Forward Flow based lookup yields rule: in id=0x2ace0fa90e70, priority=13, domain=capture, deny=false hits=11145169, user_data=0x2ace120c4910, cs_id=0x0, l3_type=0x0 src mac=0000.0000.0000, mask=0000.0000.0000 dst mac=0000.0000.0000, mask=0000.0000.0000 input_ifc=outside, output_ifc=any Phase: 2 Type: ACCESS-LIST Subtype: Result: ALLOW Config: Implicit Rule Additional Information: Forward Flow based lookup yields rule: in id=0x2ace107c8480, priority=1, domain=permit, deny=false hits=6866095, user_data=0x0, cs_id=0x0, l3_type=0x8 src mac=0000.0000.0000, mask=0000.0000.0000 dst mac=0000.0000.0000, mask=0100.0000.0000 input_ifc=outside, output_ifc=any Phase: 3 Type: ROUTE-LOOKUP Subtype: Resolve Egress Interface Result: ALLOW Config: Additional Information: found next-hop 192.168.1.30 using egress ifc inside Phase: 4 Type: UN-NAT Subtype: static Result: ALLOW Config: nat (inside,outside) source static inside-subnet inside-subnet destination static outside-subnet-anyconnect-po ol outside-subnet-anyconnect-pool no-proxy-arp route-lookup Additional Information: NAT divert to egress interface inside Untranslate 192.168.1.30/443 to 192.168.1.30/443 Phase: 5 Type: ACCESS-LIST Subtype: log Result: ALLOW Config: access-group CSM_FW_ACL_ global access-list CSM_FW_ACL_ advanced trust ip ifc outside any any rule-id 268436481 event-log flow-end access-list CSM_FW_ACL_ remark rule-id 268436481: PREFILTER POLICY: Example_Company_Prefilter_Policy access-list CSM_FW_ACL_ remark rule-id 268436481: RULE: AllowtoVPNOutsideinterface Additional Information: Forward Flow based lookup yields rule: in id=0x2ace0fa8f4e0, priority=12, domain=permit, trust hits=318637, user_data=0x2ace057b9a80, cs_id=0x0, use_real_addr, flags=0x0, protocol=0 src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, ifc=outside dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, ifc=any, vlan=0, dscp=0x0 input_ifc=any, output_ifc=any ... Phase: 7 Type: NAT Subtype: Result: ALLOW Config: nat (inside,outside) source static inside-subnet inside-subnet destination static outside-subnet-anyconnect-po ol outside-subnet-anyconnect-pool no-proxy-arp route-lookup Additional Information: Static translate 192.168.10.50/1234 to 192.168.10.50/1234 Forward Flow based lookup yields rule: in id=0x2ace11975cb0, priority=6, domain=nat, deny=false hits=120, user_data=0x2ace0f29c4a0, cs_id=0x0, flags=0x0, protocol=0 src ip/id=192.168.10.0, mask=255.255.255.0, port=0, tag=any dst ip/id=10.201.214.128, mask=255.255.255.240, port=0, tag=any, dscp=0x0 input_ifc=outside, output_ifc=inside ...
Phase: 10 Type: VPN Subtype: ipsec-tunnel-flow Result: ALLOW Config: Additional Information: Forward Flow based lookup yields rule: in id=0x2ace11d455e0, priority=13, domain=ipsec-tunnel-flow, deny=true hits=3276174, user_data=0x0, cs_id=0x0, flags=0x0, protocol=0 src ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any dst ip/id=0.0.0.0, mask=0.0.0.0, port=0, tag=any, dscp=0x0 input_ifc=outside, output_ifc=any Phase: 11 Type: NAT Subtype: rpf-check Result: ALLOW Config: nat (inside,outside) source static inside-subnet inside-subnet destination static outside-subnet-anyconnect-po ol outside-subnet-anyconnect-pool no-proxy-arp route-lookup Additional Information: Forward Flow based lookup yields rule: out id=0x2ace0d5a9800, priority=6, domain=nat-reverse, deny=false hits=121, user_data=0x2ace1232a4c0, cs_id=0x0, use_real_addr, flags=0x0, protocol=0 src ip/id=192.168.10.0, mask=255.255.255.0, port=0, tag=any dst ip/id=10.201.214.128, mask=255.255.255.240, port=0, tag=any, dscp=0x0 input_ifc=outside, output_ifc=inside ... Phase: 14 Type: FLOW-CREATION Subtype: Result: ALLOW Config: Additional Information: New flow created with id 3279248, packet dispatched to next module Module information for reverse flow ... ... Phase: 15 Type: ROUTE-LOOKUP Subtype: Resolve Egress Interface Result: ALLOW Config: Additional Information: found next-hop 192.168.1.30 using egress ifc inside Result: input-interface: outside input-status: up input-line-status: up output-interface: inside output-status: up output-line-status: up Action: allow ciscofp3#
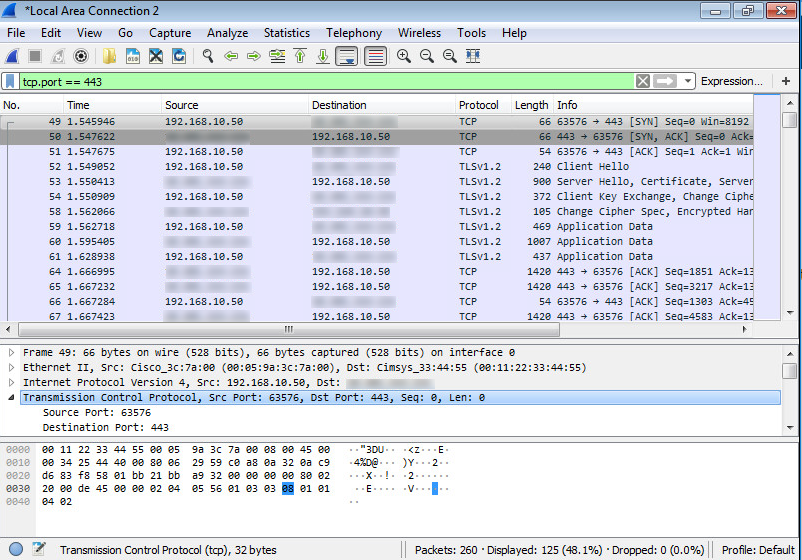
Capture taken on the employee PC of the PC successfully connecting to the FTD via AnyConnect VPN
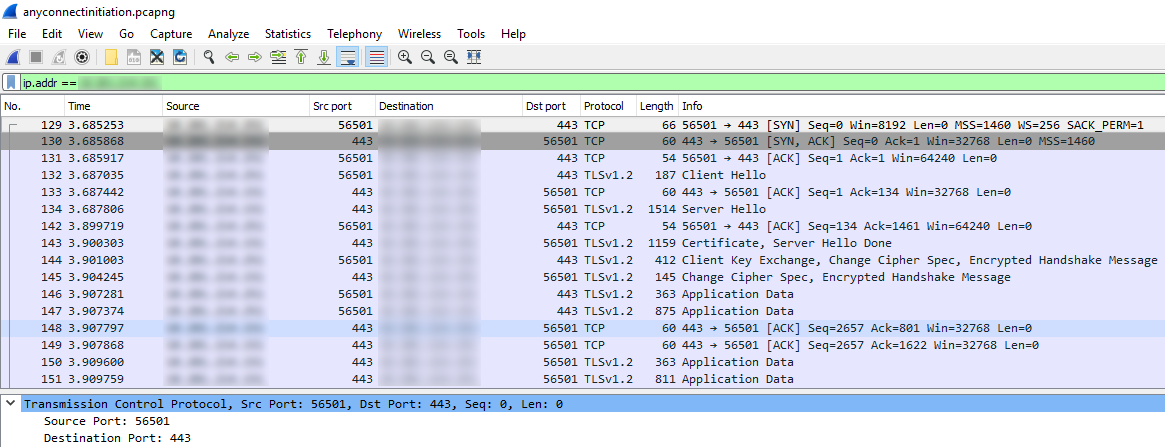
You can also see the DTLS tunnel forming later in this same capture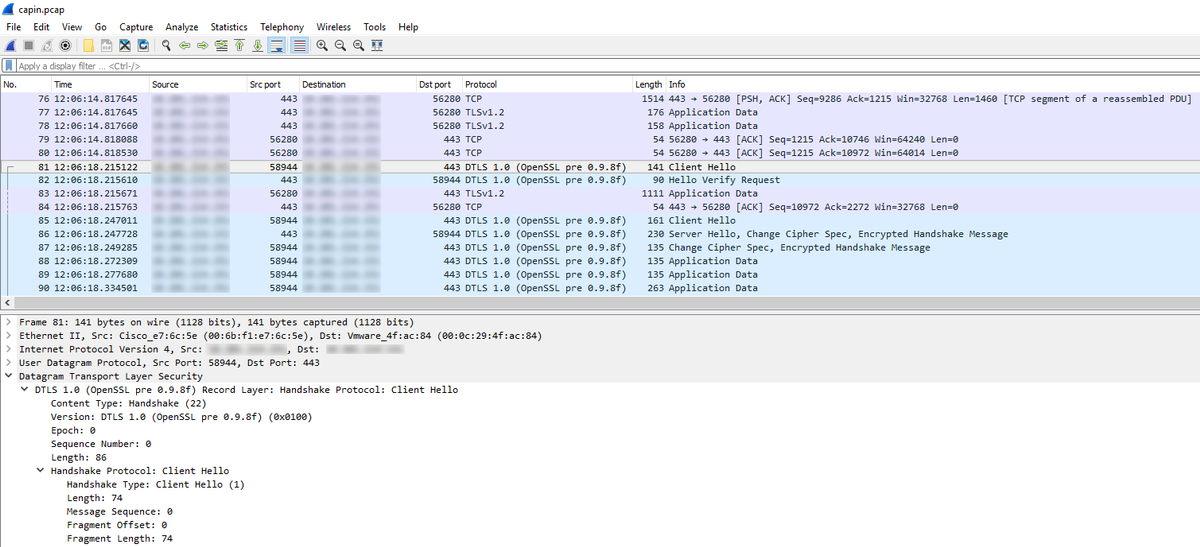
Capture taken on the Outside interface of the FTD showing the AnyConnect PC successfully connects to VPN
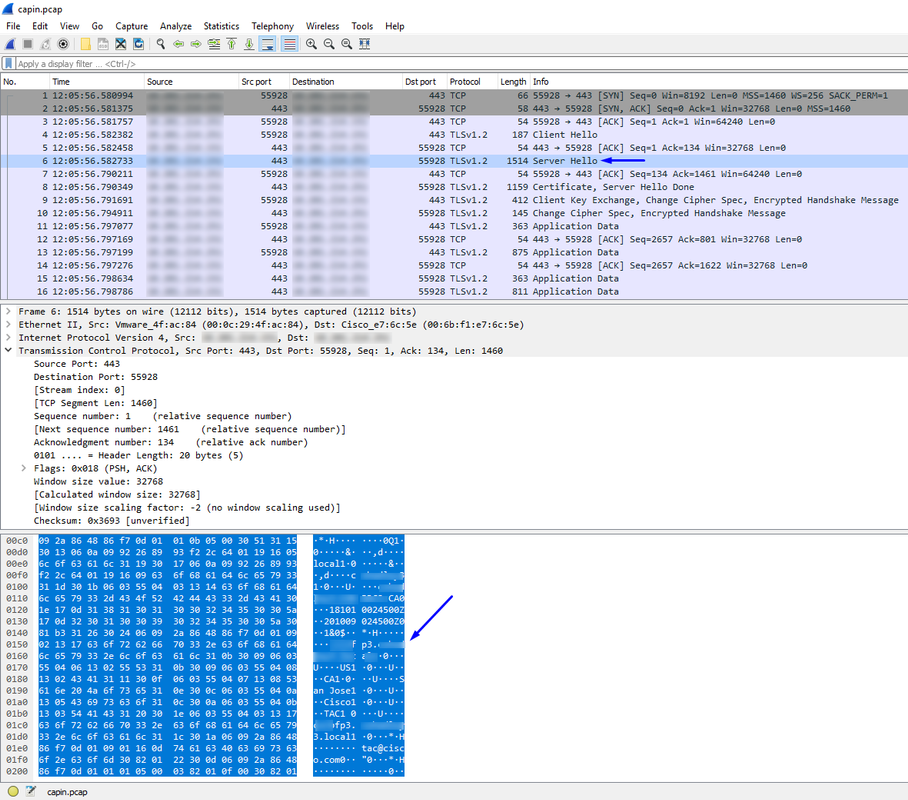
Note: you can see the FTD VPN Server certificate in the 'Server Hello' packet as we connect to the outside interface of the FTD via VPN. The employee PC will trust this certificate because the employee PC has the Root CA certificate on it, and the FTD VPN Server certificate was signed by that same Root CA.
Capture taken on the FTD of the FTD asking RADIUS Server if username + password are correct (Cisco ISE)
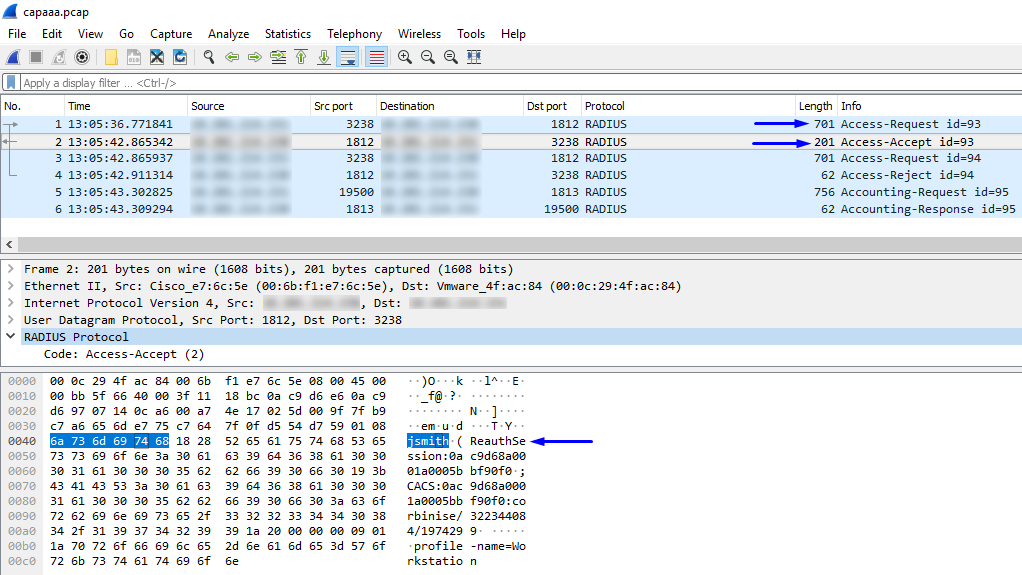
As you can see above, our VPN connection gets an Access-Accept, and our AnyConnect VPN Client successfully connects to the FTD via VPN
Capture (CLI) of FTD asking Cisco ISE if username + password are valid (i.e. make sure RADIUS requests are successfully going between FTD and ISE and verify out which interface are they leaving)
ciscofp3# capture capout interface inside trace detail trace-count 100 [Capturing - 35607 bytes] ciscofp3# show cap ciscofp3# show cap capout | i 192.168.1.10 37: 01:23:52.264512 192.168.1.1.3238 > 192.168.1.10.1812: udp 659 38: 01:23:52.310210 192.168.1.10.1812 > 192.168.1.1.3238: udp 159 39: 01:23:52.311064 192.168.1.1.3238 > 192.168.1.10.1812: udp 659 40: 01:23:52.326734 192.168.1.10.1812 > 192.168.1.1.3238: udp 20 82: 01:23:52.737663 192.168.1.1.19500 > 192.168.1.10.1813: udp 714 85: 01:23:52.744483 192.168.1.10.1813 > 192.168.1.1.19500: udp 20
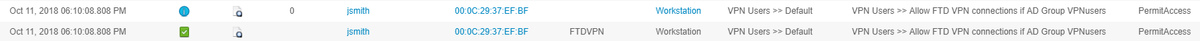
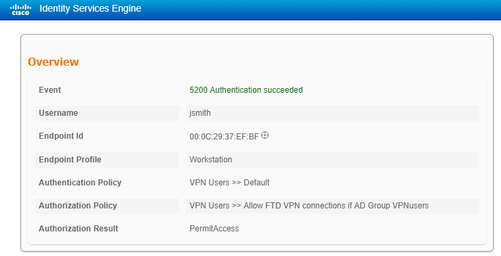
Below the Cisco ISE RADIUS Server shows that successful authentication. Click the magnifying glass to see the details of the successful authentication
Capture on the AnyConnect adapter of the employee PC of the employee PC going to an Inside website via HTTPS (i.e. while it is successfully VPN'd in):
Debugs
debug radius all
debug webvpn anyconnect 255
Run 'debug radius all' command on FTD diagnostic CLI (>system support diagnostic-cli) and hit 'Connect' on Windows/Mac PC on Cisco Anyconnect Client
> system support diagnostic-cli
Attaching to Diagnostic CLI ... Press 'Ctrl+a then d' to detach.
ciscofp3> enable
Password: <hit enter>
ciscofp3# terminal monitor
ciscofp3# debug radius all
<hit Connect on Anyconnect client on PC>
radius mkreq: 0x15
alloc_rip 0x00002ace10875428
new request 0x15 --> 16 (0x00002ace10875428)
got user 'jsmith'
got password
add_req 0x00002ace10875428 session 0x15 id 16
RADIUS_REQUEST
radius.c: rad_mkpkt
rad_mkpkt: ip:source-ip=198.51.100.2
RADIUS packet decode (authentication request)
--------------------------------------
Raw packet data (length = 659).....
01 10 02 93 fb 19 19 df f6 b1 c7 3e 34 fc 88 ce | ...........>4...
75 38 2d 55 01 08 6a 73 6d 69 74 68 02 12 a0 83 | u8-U..jsmith....
c9 bd ad 72 07 d1 bc 24 34 9e 63 a1 f5 93 05 06 | ...r...$4.c.....
00 00 50 00 1e 10 31 30 2e 32 30 31 2e 32 31 34 | ..P...198.51.100.2
2e 31 35 31 1f 10 31 30 2e 32 30 31 2e 32 31 34 | .151..198.51.100.2
2e 32 35 31 3d 06 00 00 00 05 42 10 31 30 2e 32 | .4=.....B.198.
30 31 2e 32 31 34 2e 32 35 31 1a 23 00 00 00 09 | 51.100.2#....
01 1d 6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 | ..mdm-tlv=device
2d 70 6c 61 74 66 6f 72 6d 3d 77 69 6e 1a 2c 00 | -platform=win.,.
00 00 09 01 26 6d 64 6d 2d 74 6c 76 3d 64 65 76 | ....&mdm-tlv=dev
69 63 65 2d 6d 61 63 3d 30 30 2d 30 63 2d 32 39 | ice-mac=00-0c-29
2d 33 37 2d 65 66 2d 62 66 1a 33 00 00 00 09 01 | -37-ef-bf.3.....
2d 6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d | -mdm-tlv=device-
70 75 62 6c 69 63 2d 6d 61 63 3d 30 30 2d 30 63 | public-mac=00-0c
2d 32 39 2d 33 37 2d 65 66 2d 62 66 1a 3a 00 00 | -29-37-ef-bf.:..
00 09 01 34 6d 64 6d 2d 74 6c 76 3d 61 63 2d 75 | ...4mdm-tlv=ac-u
73 65 72 2d 61 67 65 6e 74 3d 41 6e 79 43 6f 6e | ser-agent=AnyCon
6e 65 63 74 20 57 69 6e 64 6f 77 73 20 34 2e 36 | nect Windows 4.6
2e 30 33 30 34 39 1a 3f 00 00 00 09 01 39 6d 64 | .03049.?.....9md
6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 70 6c 61 | m-tlv=device-pla
74 66 6f 72 6d 2d 76 65 72 73 69 6f 6e 3d 36 2e | tform-version=6.
31 2e 37 36 30 31 20 53 65 72 76 69 63 65 20 50 | 1.7601 Service P
61 63 6b 20 31 1a 40 00 00 00 09 01 3a 6d 64 6d | ack 1.@.....:mdm
2d 74 6c 76 3d 64 65 76 69 63 65 2d 74 79 70 65 | -tlv=device-type
3d 56 4d 77 61 72 65 2c 20 49 6e 63 2e 20 56 4d | =VMware, Inc. VM
77 61 72 65 20 56 69 72 74 75 61 6c 20 50 6c 61 | ware Virtual Pla
74 66 6f 72 6d 1a 5b 00 00 00 09 01 55 6d 64 6d | tform.[.....Umdm
2d 74 6c 76 3d 64 65 76 69 63 65 2d 75 69 64 3d | -tlv=device-uid=
33 36 39 33 43 36 34 30 37 43 39 32 35 32 35 31 | 3693C6407C925251
46 46 37 32 42 36 34 39 33 42 44 44 38 37 33 31 | FF72B6493BDD8731
38 41 42 46 43 39 30 43 36 32 31 35 34 32 43 33 | 8ABFC90C621542C3
38 46 41 46 38 37 38 45 46 34 39 36 31 34 41 31 | 8FAF878EF49614A1
04 06 00 00 00 00 1a 31 00 00 00 09 01 2b 61 75 | .......1.....+au
64 69 74 2d 73 65 73 73 69 6f 6e 2d 69 64 3d 30 | dit-session-id=0
61 63 39 64 36 38 61 30 30 30 30 35 30 30 30 35 | ac9d68a000050005
62 62 65 31 66 39 31 1a 23 00 00 00 09 01 1d 69 | bbe1f91.#......i
70 3a 73 6f 75 72 63 65 2d 69 70 3d 31 30 2e 32 | p:source-ip=192.1
30 31 2e 32 31 34 2e 32 35 31 1a 18 00 00 0c 04 | 68.10.50........
92 12 46 54 44 41 6e 79 43 6f 6e 6e 65 63 74 56 | ..FTDAnyConnectV
50 4e 1a 0c 00 00 0c 04 96 06 00 00 00 02 1a 15 | PN..............
00 00 00 09 01 0f 63 6f 61 2d 70 75 73 68 3d 74 | ......coa-push=t
72 75 65 | rue
Parsed packet data.....
Radius: Code = 1 (0x01)
Radius: Identifier = 16 (0x10)
Radius: Length = 659 (0x0293)
Radius: Vector: FB1919DFF6B1C73E34FC88CE75382D55
Radius: Type = 1 (0x01) User-Name
Radius: Length = 8 (0x08)
Radius: Value (String) =
6a 73 6d 69 74 68 | jsmith
Radius: Type = 2 (0x02) User-Password
Radius: Length = 18 (0x12)
Radius: Value (String) =
a0 83 c9 bd ad 72 07 d1 bc 24 34 9e 63 a1 f5 93 | .....r...$4.c...
Radius: Type = 5 (0x05) NAS-Port
Radius: Length = 6 (0x06)
Radius: Value (Hex) = 0x5000
Radius: Type = 30 (0x1E) Called-Station-Id
Radius: Length = 16 (0x10)
Radius: Value (String) =
31 30 2e 32 30 31 2e 32 31 34 2e 31 35 31 | 203.0.113.2
Radius: Type = 31 (0x1F) Calling-Station-Id
Radius: Length = 16 (0x10)
Radius: Value (String) =
31 30 2e 32 30 31 2e 32 31 34 2e 32 35 31 | 198.51.100.2
Radius: Type = 61 (0x3D) NAS-Port-Type
Radius: Length = 6 (0x06)
Radius: Value (Hex) = 0x5
Radius: Type = 66 (0x42) Tunnel-Client-Endpoint
Radius: Length = 16 (0x10)
Radius: Value (String) =
31 30 2e 32 30 31 2e 32 31 34 2e 32 35 31 | 198.51.100.2
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 35 (0x23)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 29 (0x1D)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 70 | mdm-tlv=device-p
6c 61 74 66 6f 72 6d 3d 77 69 6e | latform=win
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 44 (0x2C)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 38 (0x26)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 6d | mdm-tlv=device-m
61 63 3d 30 30 2d 30 63 2d 32 39 2d 33 37 2d 65 | ac=00-0c-29-37-e
66 2d 62 66 | f-bf
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 51 (0x33)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 45 (0x2D)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 70 | mdm-tlv=device-p
75 62 6c 69 63 2d 6d 61 63 3d 30 30 2d 30 63 2d | ublic-mac=00-0c-
32 39 2d 33 37 2d 65 66 2d 62 66 | 29-37-ef-bf
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 58 (0x3A)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 52 (0x34)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 61 63 2d 75 73 65 72 2d | mdm-tlv=ac-user-
61 67 65 6e 74 3d 41 6e 79 43 6f 6e 6e 65 63 74 | agent=AnyConnect
20 57 69 6e 64 6f 77 73 20 34 2e 36 2e 30 33 30 | Windows 4.6.030
34 39 | 49
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 63 (0x3F)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 57 (0x39)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 70 | mdm-tlv=device-p
6c 61 74 66 6f 72 6d 2d 76 65 72 73 69 6f 6e 3d | latform-version=
36 2e 31 2e 37 36 30 31 20 53 65 72 76 69 63 65 | 6.1.7601 Service
20 50 61 63 6b 20 31 | Pack 1
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 64 (0x40)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 58 (0x3A)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 74 | mdm-tlv=device-t
79 70 65 3d 56 4d 77 61 72 65 2c 20 49 6e 63 2e | ype=VMware, Inc.
20 56 4d 77 61 72 65 20 56 69 72 74 75 61 6c 20 | VMware Virtual
50 6c 61 74 66 6f 72 6d | Platform
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 91 (0x5B)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 85 (0x55)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 75 | mdm-tlv=device-u
69 64 3d 33 36 39 33 43 36 34 30 37 43 39 32 35 | id=3693C6407C925
32 35 31 46 46 37 32 42 36 34 39 33 42 44 44 38 | 251FF72B6493BDD8
37 33 31 38 41 42 46 43 39 30 43 36 32 31 35 34 | 7318ABFC90C62154
32 43 33 38 46 41 46 38 37 38 45 46 34 39 36 31 | 2C38FAF878EF4961
34 41 31 | 4A1
Radius: Type = 4 (0x04) NAS-IP-Address
Radius: Length = 6 (0x06)
Radius: Value (IP Address) = 0.0.0.0 (0x00000000)
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 49 (0x31)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 43 (0x2B)
Radius: Value (String) =
61 75 64 69 74 2d 73 65 73 73 69 6f 6e 2d 69 64 | audit-session-id
3d 30 61 63 39 64 36 38 61 30 30 30 30 35 30 30 | =0ac9d68a0000500
30 35 62 62 65 31 66 39 31 | 05bbe1f91
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 35 (0x23)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 29 (0x1D)
Radius: Value (String) =
69 70 3a 73 6f 75 72 63 65 2d 69 70 3d 31 30 2e | ip:source-ip=192.
32 30 31 2e 32 31 34 2e 32 35 31 | 168.10.50
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 24 (0x18)
Radius: Vendor ID = 3076 (0x00000C04)
Radius: Type = 146 (0x92) Tunnel-Group-Name
Radius: Length = 18 (0x12)
Radius: Value (String) =
46 54 44 41 6e 79 43 6f 6e 6e 65 63 74 56 50 4e | FTDAnyConnectVPN
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 12 (0x0C)
Radius: Vendor ID = 3076 (0x00000C04)
Radius: Type = 150 (0x96) Client-Type
Radius: Length = 6 (0x06)
Radius: Value (Integer) = 2 (0x0002)
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 21 (0x15)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 15 (0x0F)
Radius: Value (String) =
63 6f 61 2d 70 75 73 68 3d 74 72 75 65 | coa-push=true
send pkt 192.168.1.10/1812
rip 0x00002ace10875428 state 7 id 16
rad_vrfy() : response message verified
rip 0x00002ace10875428
: chall_state ''
: state 0x7
: reqauth:
fb 19 19 df f6 b1 c7 3e 34 fc 88 ce 75 38 2d 55
: info 0x00002ace10875568
session_id 0x15
request_id 0x10
user 'jsmith'
response '***'
app 0
reason 0
skey 'cisco123'
sip 192.168.1.10
type 1
RADIUS packet decode (response)
--------------------------------------
Raw packet data (length = 159).....
02 10 00 9f 39 45 43 cf 05 be df 2f 24 d5 d7 05 | ....9EC..../$...
47 67 b4 fd 01 08 6a 73 6d 69 74 68 18 28 52 65 | Gg....jsmith.(Re
61 75 74 68 53 65 73 73 69 6f 6e 3a 30 61 63 39 | authSession:0ac9
64 36 38 61 30 30 30 30 35 30 30 30 35 62 62 65 | d68a000050005bbe
31 66 39 31 19 3b 43 41 43 53 3a 30 61 63 39 64 | 1f91.;CACS:0ac9d
36 38 61 30 30 30 30 35 30 30 30 35 62 62 65 31 | 68a000050005bbe1
66 39 31 3a 63 6f 72 62 69 6e 69 73 65 2f 33 32 | f91:corbinise/32
32 33 34 34 30 38 34 2f 31 39 33 31 36 38 32 1a | 2344084/1931682.
20 00 00 00 09 01 1a 70 72 6f 66 69 6c 65 2d 6e | ......profile-n
61 6d 65 3d 57 6f 72 6b 73 74 61 74 69 6f 6e | ame=Workstation
Parsed packet data.....
Radius: Code = 2 (0x02)
Radius: Identifier = 16 (0x10)
Radius: Length = 159 (0x009F)
Radius: Vector: 394543CF05BEDF2F24D5D7054767B4FD
Radius: Type = 1 (0x01) User-Name
Radius: Length = 8 (0x08)
Radius: Value (String) =
6a 73 6d 69 74 68 | jsmith
Radius: Type = 24 (0x18) State
Radius: Length = 40 (0x28)
Radius: Value (String) =
52 65 61 75 74 68 53 65 73 73 69 6f 6e 3a 30 61 | ReauthSession:0a
63 39 64 36 38 61 30 30 30 30 35 30 30 30 35 62 | c9d68a000050005b
62 65 31 66 39 31 | be1f91
Radius: Type = 25 (0x19) Class
Radius: Length = 59 (0x3B)
Radius: Value (String) =
43 41 43 53 3a 30 61 63 39 64 36 38 61 30 30 30 | CACS:0ac9d68a000
30 35 30 30 30 35 62 62 65 31 66 39 31 3a 63 6f | 050005bbe1f91:co
72 62 69 6e 69 73 65 2f 33 32 32 33 34 34 30 38 | rbinise/32234408
34 2f 31 39 33 31 36 38 32 | 4/1931682
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 32 (0x20)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 26 (0x1A)
Radius: Value (String) =
70 72 6f 66 69 6c 65 2d 6e 61 6d 65 3d 57 6f 72 | profile-name=Wor
6b 73 74 61 74 69 6f 6e | kstation
rad_procpkt: ACCEPT
Got AV-Pair with value profile-name=Workstation
RADIUS_ACCESS_ACCEPT: normal termination
radius mkreq: 0x16
alloc_rip 0x00002ace10874b80
new request 0x16 --> 17 (0x00002ace10874b80)
got user 'jsmith'
got password
add_req 0x00002ace10874b80 session 0x16 id 17
RADIUS_DELETE
remove_req 0x00002ace10875428 session 0x15 id 16
free_rip 0x00002ace10875428
RADIUS_REQUEST
radius.c: rad_mkpkt
rad_mkpkt: ip:source-ip=198.51.100.2
RADIUS packet decode (authentication request)
--------------------------------------
Raw packet data (length = 659).....
01 11 02 93 c6 fc 11 c1 0e c4 81 ac 09 a7 85 a8 | ................
83 c1 e4 88 01 08 6a 73 6d 69 74 68 02 12 79 41 | ......jsmith..yA
0e 71 13 38 ae 9f 49 be 3c a9 e4 81 65 93 05 06 | .q.8..I.<...e...
00 00 50 00 1e 10 31 30 2e 32 30 31 2e 32 31 34 | ..P...203.0.113
2e 31 35 31 1f 10 31 30 2e 32 30 31 2e 32 31 34 | .2..203.0.113
2e 32 35 31 3d 06 00 00 00 05 42 10 31 30 2e 32 | .2=.....<ip addr
30 31 2e 32 31 34 2e 32 35 31 1a 23 00 00 00 09 | ess>.#....
01 1d 6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 | ..mdm-tlv=device
2d 70 6c 61 74 66 6f 72 6d 3d 77 69 6e 1a 2c 00 | -platform=win.,.
00 00 09 01 26 6d 64 6d 2d 74 6c 76 3d 64 65 76 | ....&mdm-tlv=dev
69 63 65 2d 6d 61 63 3d 30 30 2d 30 63 2d 32 39 | ice-mac=00-0c-29
2d 33 37 2d 65 66 2d 62 66 1a 33 00 00 00 09 01 | -37-ef-bf.3.....
2d 6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d | -mdm-tlv=device-
70 75 62 6c 69 63 2d 6d 61 63 3d 30 30 2d 30 63 | public-mac=00-0c
2d 32 39 2d 33 37 2d 65 66 2d 62 66 1a 3a 00 00 | -29-37-ef-bf.:..
00 09 01 34 6d 64 6d 2d 74 6c 76 3d 61 63 2d 75 | ...4mdm-tlv=ac-u
73 65 72 2d 61 67 65 6e 74 3d 41 6e 79 43 6f 6e | ser-agent=AnyCon
6e 65 63 74 20 57 69 6e 64 6f 77 73 20 34 2e 36 | nect Windows 4.6
2e 30 33 30 34 39 1a 3f 00 00 00 09 01 39 6d 64 | .03049.?.....9md
6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 70 6c 61 | m-tlv=device-pla
74 66 6f 72 6d 2d 76 65 72 73 69 6f 6e 3d 36 2e | tform-version=6.
31 2e 37 36 30 31 20 53 65 72 76 69 63 65 20 50 | 1.7601 Service P
61 63 6b 20 31 1a 40 00 00 00 09 01 3a 6d 64 6d | ack 1.@.....:mdm
2d 74 6c 76 3d 64 65 76 69 63 65 2d 74 79 70 65 | -tlv=device-type
3d 56 4d 77 61 72 65 2c 20 49 6e 63 2e 20 56 4d | =VMware, Inc. VM
77 61 72 65 20 56 69 72 74 75 61 6c 20 50 6c 61 | ware Virtual Pla
74 66 6f 72 6d 1a 5b 00 00 00 09 01 55 6d 64 6d | tform.[.....Umdm
2d 74 6c 76 3d 64 65 76 69 63 65 2d 75 69 64 3d | -tlv=device-uid=
33 36 39 33 43 36 34 30 37 43 39 32 35 32 35 31 | 3693C6407C925251
46 46 37 32 42 36 34 39 33 42 44 44 38 37 33 31 | FF72B6493BDD8731
38 41 42 46 43 39 30 43 36 32 31 35 34 32 43 33 | 8ABFC90C621542C3
38 46 41 46 38 37 38 45 46 34 39 36 31 34 41 31 | 8FAF878EF49614A1
04 06 00 00 00 00 1a 31 00 00 00 09 01 2b 61 75 | .......1.....+au
64 69 74 2d 73 65 73 73 69 6f 6e 2d 69 64 3d 30 | dit-session-id=0
61 63 39 64 36 38 61 30 30 30 30 35 30 30 30 35 | ac9d68a000050005
62 62 65 31 66 39 31 1a 23 00 00 00 09 01 1d 69 | bbe1f91.#......i
70 3a 73 6f 75 72 63 65 2d 69 70 3d 31 30 2e 32 | p:source-ip=192.1
30 31 2e 32 31 34 2e 32 35 31 1a 18 00 00 0c 04 | 68.10.50......
92 12 46 54 44 41 6e 79 43 6f 6e 6e 65 63 74 56 | ..FTDAnyConnectV
50 4e 1a 0c 00 00 0c 04 96 06 00 00 00 02 1a 15 | PN..............
00 00 00 09 01 0f 63 6f 61 2d 70 75 73 68 3d 74 | ......coa-push=t
72 75 65 | rue
Parsed packet data.....
Radius: Code = 1 (0x01)
Radius: Identifier = 17 (0x11)
Radius: Length = 659 (0x0293)
Radius: Vector: C6FC11C10EC481AC09A785A883C1E488
Radius: Type = 1 (0x01) User-Name
Radius: Length = 8 (0x08)
Radius: Value (String) =
6a 73 6d 69 74 68 | jsmith
Radius: Type = 2 (0x02) User-Password
Radius: Length = 18 (0x12)
Radius: Value (String) =
79 41 0e 71 13 38 ae 9f 49 be 3c a9 e4 81 65 93 | yA.q.8..I.<...e.
Radius: Type = 5 (0x05) NAS-Port
Radius: Length = 6 (0x06)
Radius: Value (Hex) = 0x5000
Radius: Type = 30 (0x1E) Called-Station-Id
Radius: Length = 16 (0x10)
Radius: Value (String) =
31 30 2e 32 30 31 2e 32 31 34 2e 31 35 31 | 203.0.113.2
Radius: Type = 31 (0x1F) Calling-Station-Id
Radius: Length = 16 (0x10)
Radius: Value (String) =
31 30 2e 32 30 31 2e 32 31 34 2e 32 35 31 | 198.51.100.2
Radius: Type = 61 (0x3D) NAS-Port-Type
Radius: Length = 6 (0x06)
Radius: Value (Hex) = 0x5
Radius: Type = 66 (0x42) Tunnel-Client-Endpoint
Radius: Length = 16 (0x10)
Radius: Value (String) =
31 30 2e 32 30 31 2e 32 31 34 2e 32 35 31 | 198.51.100.2
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 35 (0x23)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 29 (0x1D)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 70 | mdm-tlv=device-p
6c 61 74 66 6f 72 6d 3d 77 69 6e | latform=win
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 44 (0x2C)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 38 (0x26)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 6d | mdm-tlv=device-m
61 63 3d 30 30 2d 30 63 2d 32 39 2d 33 37 2d 65 | ac=00-0c-29-37-e
66 2d 62 66 | f-bf
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 51 (0x33)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 45 (0x2D)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 70 | mdm-tlv=device-p
75 62 6c 69 63 2d 6d 61 63 3d 30 30 2d 30 63 2d | ublic-mac=00-0c-
32 39 2d 33 37 2d 65 66 2d 62 66 | 29-37-ef-bf
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 58 (0x3A)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 52 (0x34)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 61 63 2d 75 73 65 72 2d | mdm-tlv=ac-user-
61 67 65 6e 74 3d 41 6e 79 43 6f 6e 6e 65 63 74 | agent=AnyConnect
20 57 69 6e 64 6f 77 73 20 34 2e 36 2e 30 33 30 | Windows 4.6.030
34 39 | 49
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 63 (0x3F)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 57 (0x39)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 70 | mdm-tlv=device-p
6c 61 74 66 6f 72 6d 2d 76 65 72 73 69 6f 6e 3d | latform-version=
36 2e 31 2e 37 36 30 31 20 53 65 72 76 69 63 65 | 6.1.7601 Service
20 50 61 63 6b 20 31 | Pack 1
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 64 (0x40)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 58 (0x3A)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 74 | mdm-tlv=device-t
79 70 65 3d 56 4d 77 61 72 65 2c 20 49 6e 63 2e | ype=VMware, Inc.
20 56 4d 77 61 72 65 20 56 69 72 74 75 61 6c 20 | VMware Virtual
50 6c 61 74 66 6f 72 6d | Platform
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 91 (0x5B)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 85 (0x55)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 75 | mdm-tlv=device-u
69 64 3d 33 36 39 33 43 36 34 30 37 43 39 32 35 | id=3693C6407C925
32 35 31 46 46 37 32 42 36 34 39 33 42 44 44 38 | 251FF72B6493BDD8
37 33 31 38 41 42 46 43 39 30 43 36 32 31 35 34 | 7318ABFC90C62154
32 43 33 38 46 41 46 38 37 38 45 46 34 39 36 31 | 2C38FAF878EF4961
34 41 31 | 4A1
Radius: Type = 4 (0x04) NAS-IP-Address
Radius: Length = 6 (0x06)
Radius: Value (IP Address) = 0.0.0.0 (0x00000000)
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 49 (0x31)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 43 (0x2B)
Radius: Value (String) =
61 75 64 69 74 2d 73 65 73 73 69 6f 6e 2d 69 64 | audit-session-id
3d 30 61 63 39 64 36 38 61 30 30 30 30 35 30 30 | =0ac9d68a0000500
30 35 62 62 65 31 66 39 31 | 05bbe1f91
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 35 (0x23)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 29 (0x1D)
Radius: Value (String) =
69 70 3a 73 6f 75 72 63 65 2d 69 70 3d 31 30 2e | ip:source-ip=192.
32 30 31 2e 32 31 34 2e 32 35 31 | 168.10.50
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 24 (0x18)
Radius: Vendor ID = 3076 (0x00000C04)
Radius: Type = 146 (0x92) Tunnel-Group-Name
Radius: Length = 18 (0x12)
Radius: Value (String) =
46 54 44 41 6e 79 43 6f 6e 6e 65 63 74 56 50 4e | FTDAnyConnectVPN
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 12 (0x0C)
Radius: Vendor ID = 3076 (0x00000C04)
Radius: Type = 150 (0x96) Client-Type
Radius: Length = 6 (0x06)
Radius: Value (Integer) = 2 (0x0002)
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 21 (0x15)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 15 (0x0F)
Radius: Value (String) =
63 6f 61 2d 70 75 73 68 3d 74 72 75 65 | coa-push=true
send pkt 192.168.1.10/1812
rip 0x00002ace10874b80 state 7 id 17
rad_vrfy() : response message verified
rip 0x00002ace10874b80
: chall_state ''
: state 0x7
: reqauth:
c6 fc 11 c1 0e c4 81 ac 09 a7 85 a8 83 c1 e4 88
: info 0x00002ace10874cc0
session_id 0x16
request_id 0x11
user 'jsmith'
response '***'
app 0
reason 0
skey 'cisco123'
sip 192.168.1.10
type 1
RADIUS packet decode (response)
--------------------------------------
Raw packet data (length = 20).....
03 11 00 14 15 c3 44 44 7d a6 07 0d 7b 92 f2 3b | ......DD}...{..;
0b 06 ba 74 | ...t
Parsed packet data.....
Radius: Code = 3 (0x03)
Radius: Identifier = 17 (0x11)
Radius: Length = 20 (0x0014)
Radius: Vector: 15C344447DA6070D7B92F23B0B06BA74
rad_procpkt: REJECT
RADIUS_DELETE
remove_req 0x00002ace10874b80 session 0x16 id 17
free_rip 0x00002ace10874b80
radius: send queue empty
radius mkreq: 0x18
alloc_rip 0x00002ace10874b80
new request 0x18 --> 18 (0x00002ace10874b80)
add_req 0x00002ace10874b80 session 0x18 id 18
ACCT_REQUEST
radius.c: rad_mkpkt
RADIUS packet decode (accounting request)
--------------------------------------
Raw packet data (length = 714).....
04 12 02 ca be a0 6e 46 71 af 5c 65 82 77 c7 b5 | ......nFq.\e.w..
50 78 61 d7 01 08 6a 73 6d 69 74 68 05 06 00 00 | Pxa...jsmith....
50 00 06 06 00 00 00 02 07 06 00 00 00 01 08 06 | P...............
c0 a8 0a 32 19 3b 43 41 43 53 3a 30 61 63 39 64 | ...2.;CACS:0ac9d
36 38 61 30 30 30 30 35 30 30 30 35 62 62 65 31 | 68a000050005bbe1
66 39 31 3a 63 6f 72 62 69 6e 69 73 65 2f 33 32 | f91:corbinise/32
32 33 34 34 30 38 34 2f 31 39 33 31 36 38 32 1e | 2344084/1931682.
10 31 30 2e 32 30 31 2e 32 31 34 2e 31 35 31 1f | .203.0.113.2.
10 31 30 2e 32 30 31 2e 32 31 34 2e 32 35 31 28 | .198.51.100.2(
06 00 00 00 01 29 06 00 00 00 00 2c 0a 43 31 46 | .....).....,.C1F
30 30 30 30 35 2d 06 00 00 00 01 3d 06 00 00 00 | 00005-.....=....
05 42 10 31 30 2e 32 30 31 2e 32 31 34 2e 32 35 | .B.203.0.113.2
31 1a 18 00 00 0c 04 92 12 46 54 44 41 6e 79 43 | ........FTDAnyC
6f 6e 6e 65 63 74 56 50 4e 1a 0c 00 00 0c 04 96 | onnectVPN.......
06 00 00 00 02 1a 0c 00 00 0c 04 97 06 00 00 00 | ................
01 1a 0c 00 00 0c 04 98 06 00 00 00 03 1a 23 00 | ..............#.
00 00 09 01 1d 6d 64 6d 2d 74 6c 76 3d 64 65 76 | .....mdm-tlv=dev
69 63 65 2d 70 6c 61 74 66 6f 72 6d 3d 77 69 6e | ice-platform=win
1a 2c 00 00 00 09 01 26 6d 64 6d 2d 74 6c 76 3d | .,.....&mdm-tlv=
64 65 76 69 63 65 2d 6d 61 63 3d 30 30 2d 30 63 | device-mac=00-0c
2d 32 39 2d 33 37 2d 65 66 2d 62 66 1a 31 00 00 | -29-37-ef-bf.1..
00 09 01 2b 61 75 64 69 74 2d 73 65 73 73 69 6f | ...+audit-sessio
6e 2d 69 64 3d 30 61 63 39 64 36 38 61 30 30 30 | n-id=0ac9d68a000
30 35 30 30 30 35 62 62 65 31 66 39 31 1a 33 00 | 050005bbe1f91.3.
00 00 09 01 2d 6d 64 6d 2d 74 6c 76 3d 64 65 76 | ....-mdm-tlv=dev
69 63 65 2d 70 75 62 6c 69 63 2d 6d 61 63 3d 30 | ice-public-mac=0
30 2d 30 63 2d 32 39 2d 33 37 2d 65 66 2d 62 66 | 0-0c-29-37-ef-bf
1a 3a 00 00 00 09 01 34 6d 64 6d 2d 74 6c 76 3d | .:.....4mdm-tlv=
61 63 2d 75 73 65 72 2d 61 67 65 6e 74 3d 41 6e | ac-user-agent=An
79 43 6f 6e 6e 65 63 74 20 57 69 6e 64 6f 77 73 | yConnect Windows
20 34 2e 36 2e 30 33 30 34 39 1a 3f 00 00 00 09 | 4.6.03049.?....
01 39 6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 | .9mdm-tlv=device
2d 70 6c 61 74 66 6f 72 6d 2d 76 65 72 73 69 6f | -platform-versio
6e 3d 36 2e 31 2e 37 36 30 31 20 53 65 72 76 69 | n=6.1.7601 Servi
63 65 20 50 61 63 6b 20 31 1a 40 00 00 00 09 01 | ce Pack 1.@.....
3a 6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d | :mdm-tlv=device-
74 79 70 65 3d 56 4d 77 61 72 65 2c 20 49 6e 63 | type=VMware, Inc
2e 20 56 4d 77 61 72 65 20 56 69 72 74 75 61 6c | . VMware Virtual
20 50 6c 61 74 66 6f 72 6d 1a 5b 00 00 00 09 01 | Platform.[.....
55 6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d | Umdm-tlv=device-
75 69 64 3d 33 36 39 33 43 36 34 30 37 43 39 32 | uid=3693C6407C92
35 32 35 31 46 46 37 32 42 36 34 39 33 42 44 44 | 5251FF72B6493BDD
38 37 33 31 38 41 42 46 43 39 30 43 36 32 31 35 | 87318ABFC90C6215
34 32 43 33 38 46 41 46 38 37 38 45 46 34 39 36 | 42C38FAF878EF496
31 34 41 31 04 06 00 00 00 00 | 14A1......
Parsed packet data.....
Radius: Code = 4 (0x04)
Radius: Identifier = 18 (0x12)
Radius: Length = 714 (0x02CA)
Radius: Vector: BEA06E4671AF5C658277C7B5507861D7
Radius: Type = 1 (0x01) User-Name
Radius: Length = 8 (0x08)
Radius: Value (String) =
6a 73 6d 69 74 68 | jsmith
Radius: Type = 5 (0x05) NAS-Port
Radius: Length = 6 (0x06)
Radius: Value (Hex) = 0x5000
Radius: Type = 6 (0x06) Service-Type
Radius: Length = 6 (0x06)
Radius: Value (Hex) = 0x2
Radius: Type = 7 (0x07) Framed-Protocol
Radius: Length = 6 (0x06)
Radius: Value (Hex) = 0x1
Radius: Type = 8 (0x08) Framed-IP-Address
Radius: Length = 6 (0x06)
Radius: Value (IP Address) = 192.168.10.50 (0xC0A80A32)
Radius: Type = 25 (0x19) Class
Radius: Length = 59 (0x3B)
Radius: Value (String) =
43 41 43 53 3a 30 61 63 39 64 36 38 61 30 30 30 | CACS:0ac9d68a000
30 35 30 30 30 35 62 62 65 31 66 39 31 3a 63 6f | 050005bbe1f91:co
72 62 69 6e 69 73 65 2f 33 32 32 33 34 34 30 38 | rbinise/32234408
34 2f 31 39 33 31 36 38 32 | 4/1931682
Radius: Type = 30 (0x1E) Called-Station-Id
Radius: Length = 16 (0x10)
Radius: Value (String) =
31 30 2e 32 30 31 2e 32 31 34 2e 31 35 31 | 203.0.113.2
Radius: Type = 31 (0x1F) Calling-Station-Id
Radius: Length = 16 (0x10)
Radius: Value (String) =
31 30 2e 32 30 31 2e 32 31 34 2e 32 35 31 | 198.51.100.2
Radius: Type = 40 (0x28) Acct-Status-Type
Radius: Length = 6 (0x06)
Radius: Value (Hex) = 0x1
Radius: Type = 41 (0x29) Acct-Delay-Time
Radius: Length = 6 (0x06)
Radius: Value (Hex) = 0x0
Radius: Type = 44 (0x2C) Acct-Session-Id
Radius: Length = 10 (0x0A)
Radius: Value (String) =
43 31 46 30 30 30 30 35 | C1F00005
Radius: Type = 45 (0x2D) Acct-Authentic
Radius: Length = 6 (0x06)
Radius: Value (Hex) = 0x1
Radius: Type = 61 (0x3D) NAS-Port-Type
Radius: Length = 6 (0x06)
Radius: Value (Hex) = 0x5
Radius: Type = 66 (0x42) Tunnel-Client-Endpoint
Radius: Length = 16 (0x10)
Radius: Value (String) =
31 30 2e 32 30 31 2e 32 31 34 2e 32 35 31 | 198.51.100.2
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 24 (0x18)
Radius: Vendor ID = 3076 (0x00000C04)
Radius: Type = 146 (0x92) Tunnel-Group-Name
Radius: Length = 18 (0x12)
Radius: Value (String) =
46 54 44 41 6e 79 43 6f 6e 6e 65 63 74 56 50 4e | FTDAnyConnectVPN
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 12 (0x0C)
Radius: Vendor ID = 3076 (0x00000C04)
Radius: Type = 150 (0x96) Client-Type
Radius: Length = 6 (0x06)
Radius: Value (Integer) = 2 (0x0002)
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 12 (0x0C)
Radius: Vendor ID = 3076 (0x00000C04)
Radius: Type = 151 (0x97) VPN-Session-Type
Radius: Length = 6 (0x06)
Radius: Value (Integer) = 1 (0x0001)
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 12 (0x0C)
Radius: Vendor ID = 3076 (0x00000C04)
Radius: Type = 152 (0x98) VPN-Session-Subtype
Radius: Length = 6 (0x06)
Radius: Value (Integer) = 3 (0x0003)
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 35 (0x23)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 29 (0x1D)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 70 | mdm-tlv=device-p
6c 61 74 66 6f 72 6d 3d 77 69 6e | latform=win
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 44 (0x2C)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 38 (0x26)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 6d | mdm-tlv=device-m
61 63 3d 30 30 2d 30 63 2d 32 39 2d 33 37 2d 65 | ac=00-0c-29-37-e
66 2d 62 66 | f-bf
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 49 (0x31)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 43 (0x2B)
Radius: Value (String) =
61 75 64 69 74 2d 73 65 73 73 69 6f 6e 2d 69 64 | audit-session-id
3d 30 61 63 39 64 36 38 61 30 30 30 30 35 30 30 | =0ac9d68a0000500
30 35 62 62 65 31 66 39 31 | 05bbe1f91
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 51 (0x33)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 45 (0x2D)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 70 | mdm-tlv=device-p
75 62 6c 69 63 2d 6d 61 63 3d 30 30 2d 30 63 2d | ublic-mac=00-0c-
32 39 2d 33 37 2d 65 66 2d 62 66 | 29-37-ef-bf
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 58 (0x3A)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 52 (0x34)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 61 63 2d 75 73 65 72 2d | mdm-tlv=ac-user-
61 67 65 6e 74 3d 41 6e 79 43 6f 6e 6e 65 63 74 | agent=AnyConnect
20 57 69 6e 64 6f 77 73 20 34 2e 36 2e 30 33 30 | Windows 4.6.030
34 39 | 49
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 63 (0x3F)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 57 (0x39)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 70 | mdm-tlv=device-p
6c 61 74 66 6f 72 6d 2d 76 65 72 73 69 6f 6e 3d | latform-version=
36 2e 31 2e 37 36 30 31 20 53 65 72 76 69 63 65 | 6.1.7601 Service
20 50 61 63 6b 20 31 | Pack 1
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 64 (0x40)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 58 (0x3A)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 74 | mdm-tlv=device-t
79 70 65 3d 56 4d 77 61 72 65 2c 20 49 6e 63 2e | ype=VMware, Inc.
20 56 4d 77 61 72 65 20 56 69 72 74 75 61 6c 20 | VMware Virtual
50 6c 61 74 66 6f 72 6d | Platform
Radius: Type = 26 (0x1A) Vendor-Specific
Radius: Length = 91 (0x5B)
Radius: Vendor ID = 9 (0x00000009)
Radius: Type = 1 (0x01) Cisco-AV-pair
Radius: Length = 85 (0x55)
Radius: Value (String) =
6d 64 6d 2d 74 6c 76 3d 64 65 76 69 63 65 2d 75 | mdm-tlv=device-u
69 64 3d 33 36 39 33 43 36 34 30 37 43 39 32 35 | id=3693C6407C925
32 35 31 46 46 37 32 42 36 34 39 33 42 44 44 38 | 251FF72B6493BDD8
37 33 31 38 41 42 46 43 39 30 43 36 32 31 35 34 | 7318ABFC90C62154
32 43 33 38 46 41 46 38 37 38 45 46 34 39 36 31 | 2C38FAF878EF4961
34 41 31 | 4A1
Radius: Type = 4 (0x04) NAS-IP-Address
Radius: Length = 6 (0x06)
Radius: Value (IP Address) = 0.0.0.0 (0x00000000)
send pkt 192.168.1.10/1813
rip 0x00002ace10874b80 state 6 id 18
rad_vrfy() : response message verified
rip 0x00002ace10874b80
: chall_state ''
: state 0x6
: reqauth:
be a0 6e 46 71 af 5c 65 82 77 c7 b5 50 78 61 d7
: info 0x00002ace10874cc0
session_id 0x18
request_id 0x12
user 'jsmith'
response '***'
app 0
reason 0
skey 'cisco123'
sip 192.168.1.10
type 3
RADIUS packet decode (response)
--------------------------------------
Raw packet data (length = 20).....
05 12 00 14 e5 fd b1 6d fb ee 58 f0 89 79 73 8e | .......m..X..ys.
90 dc a7 20 | ...
Parsed packet data.....
Radius: Code = 5 (0x05)
Radius: Identifier = 18 (0x12)
Radius: Length = 20 (0x0014)
Radius: Vector: E5FDB16DFBEE58F08979738E90DCA720
rad_procpkt: ACCOUNTING_RESPONSE
RADIUS_DELETE
remove_req 0x00002ace10874b80 session 0x18 id 18
free_rip 0x00002ace10874b80
radius: send queue empty
ciscofp3#
Run 'debug webvpn anyconnect 255' command on FTD diagnostic CLI (>system support diagnostic-cli) and hit 'Connect' on Windows/Mac PC on Cisco Anyconnect Client
> system support diagnostic-cli Attaching to Diagnostic CLI ... Press 'Ctrl+a then d' to detach. ciscofp3> enable Password: <hit enter> ciscofp3# terminal monitor ciscofp3# debug webvpn anyconnect 255 <hit Connect on Anyconnect client on PC> http_parse_cstp_method() ...input: 'CONNECT /CSCOSSLC/tunnel HTTP/1.1' webvpn_cstp_parse_request_field() ...input: 'Host: ciscofp3.cisco.com' Processing CSTP header line: 'Host: ciscofp3.cisco.com' webvpn_cstp_parse_request_field() ...input: 'User-Agent: Cisco AnyConnect VPN Agent for Windows 4.6.03049' Processing CSTP header line: 'User-Agent: Cisco AnyConnect VPN Agent for Windows 4.6.03049' Setting user-agent to: 'Cisco AnyConnect VPN Agent for Windows 4.6.03049' webvpn_cstp_parse_request_field() ...input: 'Cookie: webvpn=2B0E85@28672@6501@2FF4AE4D1F69B98F26E8CAD62D5496E5E6AE5282' Processing CSTP header line: 'Cookie: webvpn=2B0E85@28672@6501@2FF4AE4D1F69B98F26E8CAD62D5496E5E6AE5282' Found WebVPN cookie: 'webvpn=2B0E85@28672@6501@2FF4AE4D1F69B98F26E8CAD62D5496E5E6AE5282' WebVPN Cookie: 'webvpn=2B0E85@28672@6501@2FF4AE4D1F69B98F26E8CAD62D5496E5E6AE5282' webvpn_cstp_parse_request_field() ...input: 'X-CSTP-Version: 1' Processing CSTP header line: 'X-CSTP-Version: 1' webvpn_cstp_parse_request_field() ...input: 'X-CSTP-Hostname: jsmith-PC' Processing CSTP header line: 'X-CSTP-Hostname: jsmith-PC' Setting hostname to: 'jsmith-PC' webvpn_cstp_parse_request_field() ...input: 'X-CSTP-MTU: 1399' Processing CSTP header line: 'X-CSTP-MTU: 1399' webvpn_cstp_parse_request_field() ...input: 'X-CSTP-Address-Type: IPv6,IPv4' Processing CSTP header line: 'X-CSTP-Address-Type: IPv6,IPv4' webvpn_cstp_parse_request_field() ...input: 'X-CSTP-Local-Address-IP4: 198.51.100.2' Processing CSTP header line: 'X-CSTP-Local-Address-IP4: 198.51.100.2' webvpn_cstp_parse_request_field() ...input: 'X-CSTP-Base-MTU: 1500' Processing CSTP header line: 'X-CSTP-Base-MTU: 1500' webvpn_cstp_parse_request_field() ...input: 'X-CSTP-Remote-Address-IP4: 203.0.113.2' Processing CSTP header line: 'X-CSTP-Remote-Address-IP4: 203.0.113.2' webvpn_cstp_parse_request_field() ...input: 'X-CSTP-Full-IPv6-Capability: true' Processing CSTP header line: 'X-CSTP-Full-IPv6-Capability: true' webvpn_cstp_parse_request_field() ...input: 'X-DTLS-Master-Secret: 1FA92A96D5E82C13CB3A5758F11371EE6B54C6F36F0A8DCE8F4DECB73A034EEF4FE95DA614A5872E1EE5557C3BF4765A' Processing CSTP header line: 'X-DTLS-Master-Secret: 1FA92A96D5E82C13CB3A5758F11371EE6B54C6F36F0A8DCE8F4DECB73A034EEF4FE95DA614A5872E1EE5557C3BF4765A' webvpn_cstp_parse_request_field() ...input: 'X-DTLS-CipherSuite: DHE-RSA-AES256-GCM-SHA384:DHE-RSA-AES256-SHA256:DHE-RSA-AES256-SHA:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:AES256-SHA:AES128-SHA:DES-CBC3-SHA' Processing CSTP header line: 'X-DTLS-CipherSuite: DHE-RSA-AES256-GCM-SHA384:DHE-RSA-AES256-SHA256:DHE-RSA-AES256-SHA:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:AES256-SHA:AES128-SHA:DES-CBC3-SHA' webvpn_cstp_parse_request_field() ...input: 'X-DTLS-Accept-Encoding: lzs' Processing CSTL header line: 'X-DTLS-Accept-Encoding: lzs' webvpn_cstp_parse_request_field() ...input: 'X-DTLS-Header-Pad-Length: 0' webvpn_cstp_parse_request_field() ...input: 'X-CSTP-Accept-Encoding: lzs,deflate' Processing CSTP header line: 'X-CSTP-Accept-Encoding: lzs,deflate' webvpn_cstp_parse_request_field() ...input: 'X-CSTP-Protocol: Copyright (c) 2004 Cisco Systems, Inc.' Processing CSTP header line: 'X-CSTP-Protocol: Copyright (c) 2004 Cisco Systems, Inc.' cstp_util_address_ipv4_accept: address asigned: 192.168.10.50 cstp_util_address_ipv6_accept: No IPv6 Address np_svc_create_session(0x7000, 0x00002acdff1d6440, TRUE) webvpn_svc_np_setup SVC ACL Name: NULL SVC ACL ID: -1 vpn_put_uauth success for ip 192.168.10.50! No SVC ACL Iphdr=20 base-mtu=1500 def-mtu=1500 conf-mtu=1406 tcp-mss = 1460 path-mtu = 1460(mss) TLS Block size = 16, version = 0x303 mtu = 1460(path-mtu) - 0(opts) - 5(ssl) - 16(iv) = 1439 mod-mtu = 1439(mtu) & 0xfff0(complement) = 1424 tls-mtu = 1424(mod-mtu) - 8(cstp) - 48(mac) - 1(pad) = 1367 DTLS Block size = 16 mtu = 1500(base-mtu) - 20(ip) - 8(udp) - 13(dtlshdr) - 16(dtlsiv) = 1443 mod-mtu = 1443(mtu) & 0xfff0(complement) = 1440 dtls-mtu = 1440(mod-mtu) - 1(cdtp) - 20(mac) - 1(pad) = 1418 computed tls-mtu=1367 dtls-mtu=1418 conf-mtu=1406 DTLS enabled for intf=3 (outside) overide computed dtls-mtu=1418 with conf-mtu=1406 tls-mtu=1367 dtls-mtu=1406 SVC: adding to sessmgmt Sending X-CSTP-MTU: 1367 Sending X-DTLS-MTU: 1406 Sending X-CSTP-FW-RULE msgs: Start Sending X-CSTP-FW-RULE msgs: Done Sending X-CSTP-Quarantine: false Sending X-CSTP-Disable-Always-On-VPN: false Sending X-CSTP-Client-Bypass-Protocol: false
Cisco ISE
Cisco ISE > Operations > RADIUS > Live Logs > click details of each authentication
Verify on Cisco ISE your VPN login and the ACL result 'PermitAccess' is given
Live Logs show jsmith authenticated to FTD via VPN successfully
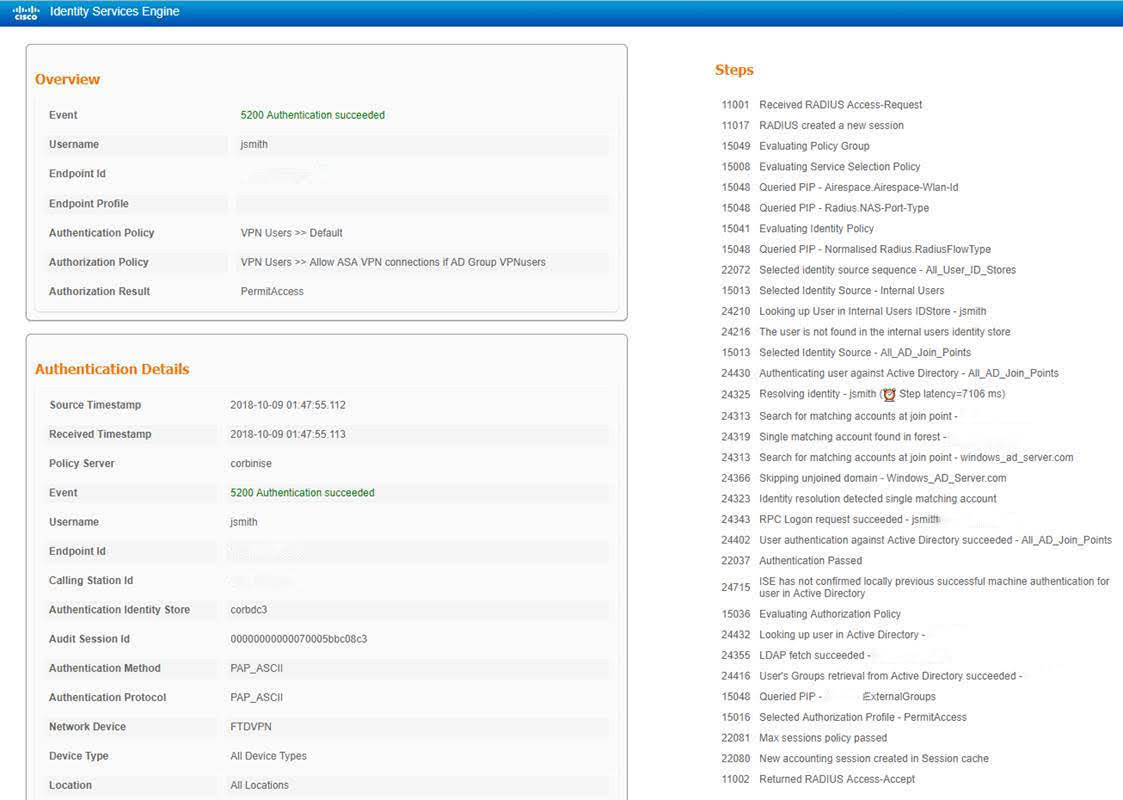
AnyConnect VPN Client
DART bundle
How to collect the DART bundle for AnyConnect
Troubleshoot
DNS
Verify Cisco ISE, FTD, Windows Server 2012, and Windows/Mac PCs can all resolve eachother forward and reverse (check DNS on all devices)
Windows PC
Launch a command prompt, and make sure you can perform an 'nslookup' on the hostname of the FTD
FTD CLI
>show network
> nslookup 192.168.1.10 Server: 192.168.1.10 Address: 192.168.1.10#53 10.1.168.192.in-addr.arpa name = ciscoise.cisco.com
ISE CLI:
ciscoise/admin# nslookup 192.168.1.20 Trying "20.1.168.192.in-addr.arpa" ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 56529 ;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0 ;; QUESTION SECTION: ;20.1.168.192.in-addr.arpa. IN PTR ;; ANSWER SECTION: 20.1.168.192.in-addr.arpa. 1200 IN PTR ciscodc.cisco.com
Windows Server 2012
Launch a command prompt, and make sure you can perform an 'nslookup' on the hostname/FQDN of the FTD
Certificate strength (for browser compatibility)
Verify Windows Server 2012 signs certificates as SHA256 or higher. Double-click your Root CA certificate in Windows and check the 'Signature algorithm' fields
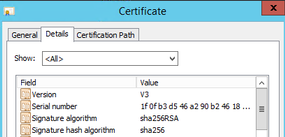
If they are SHA1, most browsers will show a browser warning for those certificates. To change it, you can check here:
How to Upgrade Windows Server Certification Authority to SHA256
Verify the FTD VPN Server Certificate has the following fields correct (when you connect in browser to FTD)
Common Name = <FTDFQDN>
Subject Alternative Name (SAN) = <FTDFQDN>
Example:
Common Name: ciscofp3.cisco.com
Subject Alternative Name (SAN): DNS Name=cicscofp3.cisco.com
Connectivity and firewall configuration
Verify using captures on FTD CLI and captures on employee PC using Wireshark to verify that packets are coming over TCP+UDP 443 to the Outside IP of the FTD. Verify that those packets are sourced from the employee's home router's public IP address
ciscofp3# capture capin interface outside trace detail trace-count 100 match ip any host <enduser'sPublicIPAddress> <now hit Connect on AnyConnect Client from employee PC>
ciscofp3# show cap capture capin type raw-data trace detail trace-count 100 interface outside [Buffer Full - 524153 bytes] match ip any host 198.51.100.2
ciscofp3# show cap capin
2375 packets captured
1: 17:05:56.580994 198.51.100.2.55928 > 203.0.113.2.443: S 2933933902:2933933902(0) win 8192 <mss 1460,nop,wscale 8,nop,nop,sackOK>
2: 17:05:56.581375 203.0.113.2.443 > 198.51.100.2.55928: S 430674106:430674106(0) ack 2933933903 win 32768 <mss 1460>
3: 17:05:56.581757 198.51.100.2.55928 > 203.0.113.2.443: . ack 430674107 win 64240
...
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
14-Nov-2018 |
Initial Release |
Contributed by Cisco Engineers
- Corbin HadleyCisco TAC
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
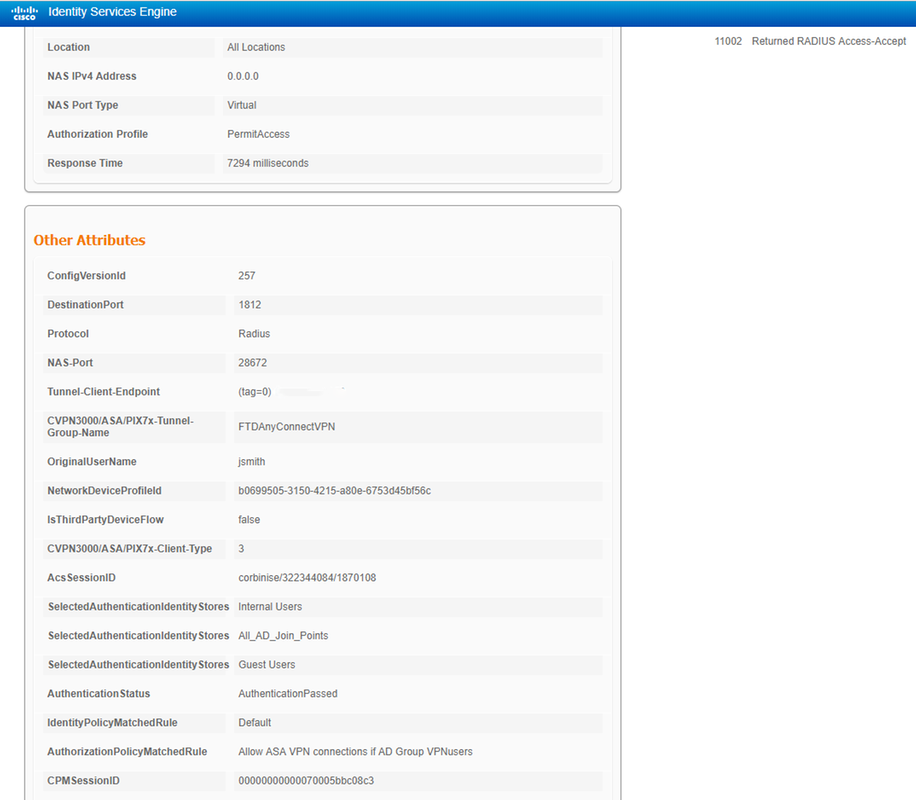
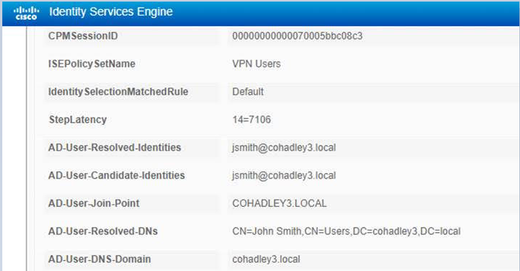
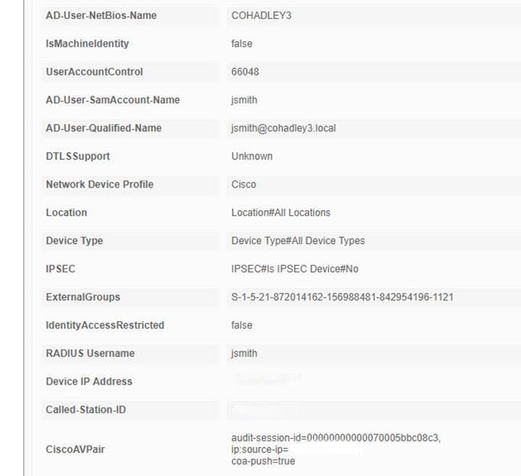
 Feedback
Feedback