Configuring Basic AAA RADIUS for Dial-in Clients
Available Languages
Contents
Introduction
This document describes a sample configuration using an access server to accept incoming Analog and ISDN connections, and authenticate them using an authentication, authorization, and accounting (AAA) Remote Authentication Dial-in User Service (RADIUS) server. For more information on AAA and RADIUS, refer to the following documents:
Prerequisites
Requirements
This configuration assumes the RADIUS server is correctly set up. This configuration also works with most commercially available RADIUS servers. Refer to your RADIUS server documentation for further information on the proper server configuration.
Components Used
The information in this document is based on the software and hardware versions below.
-
Cisco AS5300 with a T1 PRI and 48 Digital modems. It is running Cisco IOS® Software Release 12.0(7)T.
-
CiscoSecure for Unix (CSU) server, Version 2.3(3).
The AAA specific configuration described here can be also used with any simple dial scenario. Ensure that the access server can accept incoming calls, then add the appropriate AAA commands, as shown in the configuration below.
The information presented in this document was created from devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If you are working in a live network, ensure that you understand the potential impact of any command before using it.
Conventions
For more information on document conventions, see the Cisco Technical Tips Conventions.
Configure
In this section, you are presented with the information to configure the features described in this document.
Note: To find additional information on the commands used in this document, use the Command Lookup Tool (registered customers only) .
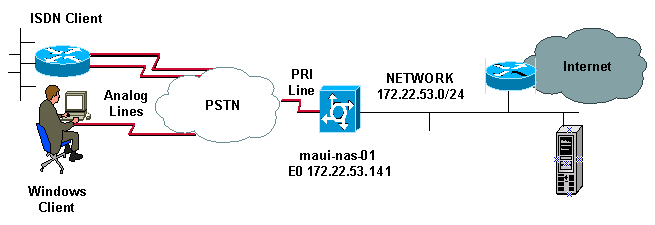
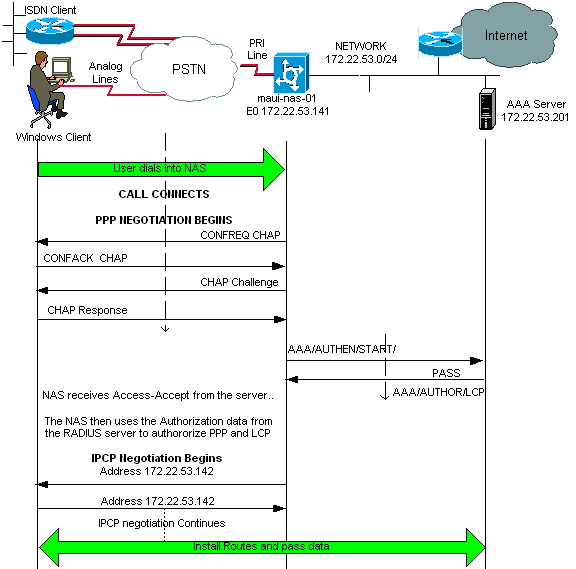
Network Diagram
This document uses the network setup shown in the diagram below.
Configurations
The CSU and CiscoSecure NT (CSNT) configuration, and network access server (NAS) configuration are provided below. Since this configuration depicts a simple dialin scenario, the CiscoSecure configuration for the ISDN and Async users are identical. The ISDN client configuration is not included as it is not relevant for this RADIUS configuration.
| CSU |
|---|
# ./ViewProfile -p 9900 -u async_client
User Profile Information
user = async_client{
profile_id = 110
profile_cycle = 2
radius=Cisco {
check_items= {
2=cisco
!--- Password(2) is "cisco"
}
reply_attributes= {
6=2
!--- Service-Type(6) is Framed (2)
7=1
!--- Frame
d-Protocol(7) is PPP (1)
}
}
}
# ./ViewProfile -p 9900 -u isdn_user
User Profile Information
user = isdn_user{
profile_id = 24
profile_cycle = 4
radius=Cisco {
check_items= {
2=cisco
! --- Password(2) is "cisco"
}
reply_attributes= {
6=2
! --- Service-Type(6) is Framed (2)
7=1
! --- Framed-Protocol(7) is PPP (1)
}
}
} |
Note: For this simple scenario, the configurations of the Async and ISDN users are identical.
CSNT RADIUS
To configure the CiscoSecure NT (CSNT) RADIUS:
-
Create new users named isdn_user and async_client.
-
Configure the appropriate password in the User Setup section
-
In the section for Internet Engineering Task Force (IETF) RADIUS Attributes, select the following items from the pulldown menu:
Service-type (attribute 6) = Framed and Framed-Protocol (attribute 7)=PPP
Note: You must click the checkbox located next to the attributes Service-Type and Framed-Protocol.
Note: For this simple scenario, the configurations of the Async and ISDN users are identical.
| maui-nas-01 |
|---|
maui-nas-01#show running-config Building configuration... Current configuration: ! version 12.0 service timestamps debug datetime msec service timestamps log datetime msec service password-encryption ! hostname maui-nas-01 ! aaa new-model !--- Initiates the AAA access control system. !--- This command immediately locks down login and PPP authentication. aaa authentication login default group radius local !--- Exec login (for the list default) is authenticated using methods !--- radius then local. The router uses RADIUS for authentication at the !--- login(exec) prompt. If RADIUS returns an error, the user is authenticated !--- using the local database. aaa authentication login NO_AUTHEN none !--- Exec login (for the list NO_AUTHEN) has authentication method none !--- (no authentication). Interfaces to which this list is applied will not have !--- authentication enabled. Refer to the console port (line con 0) configuration. aaa authentication ppp default if-needed group radius local !--- PPP authentication (for the list default) uses methods radius then local. !--- The if-needed keyword automatically permits ppp for users that have !--- successfully authenticated using exec mode. If the EXEC facility has !--- authenticated the user, RADIUS authentication for PPP is not performed. !----This is necessary for clients that use terminal window after dial. aaa authorization network default group radius local !--- Authorization of network services (PPP services) for the list default !--- uses methods radius then local. This is neccessary if you use RADIUS !--- for the client IP address, Access List assignment and so on. enable secret 5 <deleted> ! username admin password 7 <deleted> !--- This username allows for access to the router in situations where !--- connectivity to the RADIUS server is lost. This is because the AAA !--- configuration for exec login has the alternate method local. spe 2/0 2/7 firmware location system:/ucode/mica_port_firmware ! resource-pool disable ! ip subnet-zero no ip finger ! isdn switch-type primary-ni !--- Switch type is Primary NI-2. isdn voice-call-failure 0 mta receive maximum-recipients 0 ! ! controller T1 0 !--- T1 0 controller configuration. framing esf clock source line primary linecode b8zs pri-group timeslots 1-24 ! controller T1 1 !--- T1 1 is unused. clock source line secondary 1 ! controller T1 2 !--- T1 1 is unused. ! controller T1 3 !--- T1 1 is unused. ! interface Ethernet0 ip address 172.22.53.141 255.255.255.0 no ip directed-broadcast ! interface Serial0:23 !--- D-channel configuration for T1 0. no ip address no ip directed-broadcast encapsulation ppp dialer pool-member 23 !--- Assign Serial0:23 as member of dialer pool 23. !--- Dialer pool 23 is specified in interface Dialer 1. !--- Interface Dialer 1 will terminate the ISDN calls. isdn switch-type primary-ni isdn incoming-voice modem !--- Switch incoming analog calls to the internal digital modems. no cdp enable ! interface FastEthernet0 no ip address no ip directed-broadcast shutdown duplex auto speed auto ! interface Group-Async0 !--- Async Group Interface for the modems. ip unnumbered Ethernet0 !--- Unnumbered to the ethernet interface. no ip directed-broadcast encapsulation ppp async mode interactive !--- Configures interactive mode on the asynchronous interfaces. !--- This allows users to dial in and get to a shell or PPP session on !--- that line. If you want incoming users to only connect using PPP configure !--- async mode dedicated instead. peer default ip address pool ASYNC !--- Use the ip pool named "ASYNC" to assign ip address for !--- incoming connections. ppp authentication chap group-range 1 48 !--- Lines(modems) 1 through 48 are in this group async interface. ! interface Dialer1 !--- Dialer1 will terminate ISDN calls. ip unnumbered Ethernet0 no ip directed-broadcast encapsulation ppp dialer pool 23 !--- Dialer 1 uses dialer pool 23. Interface Serial0:23 is !--- a member of this pool. peer default ip address pool ISDN !--- Use the ip pool named "ISDN" to assign ip address for !--- incoming connections. no cdp enable ppp authentication chap ! ip local pool ISDN 172.22.53.142 172.22.53.145 !--- IP address pool named "ISDN". !--- This pool will be assigned to connections on interface Dialer 1. ip local pool ASYNC 172.22.53.146 172.22.53.149 !--- IP address pool named "ASYNC". !--- This pool will be assigned to incoming connections on Group-Async 0. !--- Note: This address pool only has 4 addresses and is not sufficient to !--- support all 48 modem lines. Configure your IP pool with the address range !--- to support all connections. ip classless no ip http server ! no cdp run ! radius-server host 172.22.53.201 auth-port 1645 acct-port 1646 key cisco !--- Radius-server host IP address and encryption key. !--- The encryption key must match the onbe configured on the RADIUS server. ! line con 0 exec-timeout 0 0 login authentication NO_AUTHEN !--- Specifies that the AAA list name assigned to the console is !--- NO_AUTHEN. From the AAA configuration above, the list NO_AUTHEN !--- does not use authentication. transport input none line 1 48 autoselect during-login !--- Displays the username:password prompt after modems connect. !--- Without this the user must press enter to receive a prompt. autoselect ppp !--- When the NAS detects incoming PPP packets, the PPP session !--- will be launched. modem InOut transport preferred none transport input all transport output none line aux 0 line vty 0 4 ! end |
Verify
This section provides information you can use to verify your configuration.
Sample show output
maui-nas-01#show caller user async_client detail
User: async_client, line tty 5, service Async
Active time 00:01:04, Idle time 00:00:22
Timeouts: Absolute Idle Idle
Session Exec
Limits: - - 00:10:00
Disconnect in: - - -
TTY: Line 5, running PPP on As5
Location: PPP: 172.22.53.148
!--- The IP address assigned from the the IP pool.
DS0: (slot/unit/channel)=0/0/7
Line: Baud rate (TX/RX) is 115200/115200, no parity, 1 stopbits, 8 databits
Status: Ready, Active, No Exit Banner, Async Interface Active
HW PPP Support Active
Capabilities: Hardware Flowcontrol In, Hardware Flowcontrol Out
Modem Callout, Modem RI is CD,
Line usable as async interface, Integrated Modem
Modem State: Ready
User: async_client, line As5, service PPP
Active time 00:00:54, Idle time 00:00:23
Timeouts: Absolute Idle
Limits: - -
Disconnect in: - -
PPP: LCP Open, CHAP (<- AAA), IPCP
!--- CHAP authentication was performed by AAA.
LCP: -> peer, ACCM, AuthProto, MagicNumber, PCompression, ACCompression
<- peer, ACCM, MagicNumber, PCompression, ACCompression
NCP: Open IPCP
IPCP: <- peer, Address
-> peer, Address
IP: Local 172.22.53.141, remote 172.22.53.148
Counts: 40 packets input, 2769 bytes, 0 no buffer
1 input errors, 1 CRC, 0 frame, 0 overrun
24 packets output, 941 bytes, 0 underruns
0 output errors, 0 collisions, 0 interface resets
maui-nas-01#show caller user isdn_user detail
User: isdn_user, line Se0:8, service PPP
Active time 00:01:22, Idle time 00:01:24
Timeouts: Absolute Idle
Limits: - 00:02:00
Disconnect in: - 00:00:35
PPP: LCP Open, CHAP (<- AAA), IPCP
!--- CHAP authentication was performed by AAA.
LCP: -> peer, AuthProto, MagicNumber
<- peer, MagicNumber
NCP: Open IPCP
IPCP: <- peer, Address
-> peer, Address
Dialer: Connected to , inbound
Idle timer 120 secs, idle 84 secs
Type is ISDN, group Dialer1
! -- The ISDN Call uses int Dialer1.
IP: Local 172.22.53.141, remote 172.22.53.142
! -- The IP address was obtained from the local pool.
Counts: 31 packets input, 872 bytes, 0 no buffer
0 input errors, 0 CRC, 0 frame, 0 overrun
34 packets output, 1018 bytes, 0 underruns
0 output errors, 0 collisions, 5 interface resets
Troubleshoot
This section provides information you can use to troubleshoot your configuration.
Troubleshooting Commands
Certain show commands are supported by the Output Interpreter Tool (registered customers only) , which allows you to view an analysis of show command output.
Note: Before issuing debug commands, please see Important Information on Debug Commands.
-
debug isdn q931 - This shows call setup and tear down of the ISDN network connection (Layer 3) between the router and ISDN switch.
-
debug modem - This shows modem line activity on an access server.
-
debug ppp negotiation - To display information on the PPP traffic and exchanges while negotiating Link Control Protocol (LCP), authentication, and Network Control Protocol (NCP). A successful PPP negotiation first opens the LCP state, then authenticates, and finally negotiates NCP.
-
debug ppp authentication - To display PPP authentication protocol messages, including Challenge Handshake Authentication Protocol (CHAP) packet exchanges and Password Authentication Protocol (PAP) exchanges.
-
debug aaa authentication - To display information on AAA/RADIUS authentication.
-
debug aaa authorization - To display information on AAA/RADIUS authorization.
-
debug radius - To display detailed debugging information associated with the RADIUS. Use the Ouput Interpreter Tool (registered customers only) on the Cisco Technical Support Website to decode the debug radius messages. For an example, refer to the debug output shown below. Use the information from debug radius to determine what attributes are negotiated. Note: As of 12.2(11)T the output of debug radius is already decoded and hence does NOT require the use of Output Interpreter to decode the output. Refer to the document RADIUS Debug Enhancements for more information
-
show caller user - To show parameters for the particular user such as the TTY line used, asynchronous interface (shelf, slot or port), DS0 channel number, modem number, IP address assigned, PPP and PPP bundle parameters, and so on. If your version of Cisco IOS Software does not support this command, use the show user command.
Sample Debug Output
If you have the output of a debug radius command from your Cisco device, you can use to display potential issues and fixes. To use , you must be a registered customer, be logged in, and have JavaScript enabled.
Note: As of 12.2(11)T the output of debug radius is already decoded and hence does NOT require the use of Output Interpreter to decode the output. Refer to the document RADIUS Debug Enhancements for more information
maui-nas-01#debug isdn q931 ISDN Q931 packets debugging is on maui-nas-01#debug ppp negotiation PPP protocol negotiation debugging is on maui-nas-01#debug ppp authentication PPP authentication debugging is on maui-nas-01#debug modem Modem control/process activation debugging is on maui-nas-01#debug aaa authentication AAA Authentication debugging is on maui-nas-01#debug aaa authorization AAA Authorization debugging is on maui-nas-01#debug radius RADIUS protocol debugging is on maui-nas-01# *Apr 5 11:05:07.031: ISDN Se0:23: RX <- SETUP pd = 8 callref = 0x20FC !--- Setup message for incoming call. *Apr 5 11:05:07.031: Bearer Capability i = 0x8890218F *Apr 5 11:05:07.031: Channel ID i = 0xA18387 *Apr 5 11:05:07.031: Called Party Number i = 0xA1, '81560' *Apr 5 11:05:07.035: %DIALER-6-BIND: Interface Serial0:6 bound to profile Dialer1 *Apr 5 11:05:07.035: ISDN Se0:23: TX -> CALL_PROC pd = 8 callref = 0xA0FC *Apr 5 11:05:07.035: Channel ID i = 0xA98387 *Apr 5 11:05:07.043: %LINK-3-UPDOWN: Interface Serial0:6, changed state to up *Apr 5 11:05:07.043: Se0:6 PPP: Treating connection as a callin *Apr 5 11:05:07.043: Se0:6 PPP: Phase is ESTABLISHING, Passive Open *Apr 5 11:05:07.043: Se0:6 LCP: State is Listen *Apr 5 11:05:07.047: ISDN Se0:23: TX -> CONNECT pd = 8 callref = 0xA0FC *Apr 5 11:05:07.047: Channel ID i = 0xA98387 *Apr 5 11:05:07.079: ISDN Se0:23: RX <- CONNECT_ACK pd = 8 callref = 0x20FC *Apr 5 11:05:07.079: ISDN Se0:23: CALL_PROGRESS: CALL_CONNECTED call id 0x2D, bchan -1, dsl 0 *Apr 5 11:05:07.499: Se0:6 LCP: I CONFREQ [Listen] id 28 len 10 *Apr 5 11:05:07.499: Se0:6 LCP: MagicNumber 0x5078A51F (0x05065078A51F) *Apr 5 11:05:07.499: Se0:6 AAA/AUTHOR/FSM: (0): LCP succeeds trivially *Apr 5 11:05:07.499: Se0:6 LCP: O CONFREQ [Listen] id 2 len 15 *Apr 5 11:05:07.499: Se0:6 LCP: AuthProto CHAP (0x0305C22305) *Apr 5 11:05:07.499: Se0:6 LCP: MagicNumber 0xE05213AA (0x0506E05213AA) *Apr 5 11:05:07.499: Se0:6 LCP: O CONFACK [Listen] id 28 len 10 *Apr 5 11:05:07.499: Se0:6 LCP: MagicNumber 0x5078A51F (0x05065078A51F) *Apr 5 11:05:07.555: Se0:6 LCP: I CONFACK [ACKsent] id 2 len 15 *Apr 5 11:05:07.555: Se0:6 LCP: AuthProto CHAP (0x0305C22305) *Apr 5 11:05:07.555: Se0:6 LCP: MagicNumber 0xE05213AA (0x0506E05213AA) *Apr 5 11:05:07.555: Se0:6 LCP: State is Open *Apr 5 11:05:07.555: Se0:6 PPP: Phase is AUTHENTICATING, by this end *Apr 5 11:05:07.555: Se0:6 CHAP: O CHALLENGE id 2 len 32 from "maui-nas-01" *Apr 5 11:05:07.631: Se0:6 CHAP: I RESPONSE id 2 len 30 from "isdn_user" !--- Incoming CHAP response from "isdn_user". *Apr 5 11:05:07.631: AAA: parse name=Serial0:6 idb type=12 tty=-1 *Apr 5 11:05:07.631: AAA: name=Serial0:6 flags=0x51 type=1 shelf=0 slot=0 adapter=0 port=0 channel=6 *Apr 5 11:05:07.631: AAA: parse name= idb type=-1 tty=-1 *Apr 5 11:05:07.631: AAA/MEMORY: create_user (0x619CEE28) user='isdn_user' ruser='' port='Serial0:6' rem_addr='isdn/81560' authen_type=CHAP service=PPP priv=1 *Apr 5 11:05:07.631: AAA/AUTHEN/START (2973699846): port='Serial0:6' list='' action=LOGIN service=PPP *Apr 5 11:05:07.631: AAA/AUTHEN/START (2973699846): using "default" list *Apr 5 11:05:07.631: AAA/AUTHEN (2973699846): status = UNKNOWN *Apr 5 11:05:07.631: AAA/AUTHEN/START (2973699846): Method=radius (radius) !--- AAA authentication method is RADIUS. *Apr 5 11:05:07.631: RADIUS: ustruct sharecount=1 *Apr 5 11:05:07.631: RADIUS: Initial Transmit Serial0:6 id 13 172.22.53.201:1645, Access-Request, len 87 !--- Access-Request from the NAS to the AAA server. !--- Note the IP address in the Access-Request matches the IP address !--- configured using the command: !--- radius-server host 172.22.53.201 key cisco *Apr 5 11:05:07.631: Attribute 4 6 AC16358D *Apr 5 11:05:07.631: Attribute 5 6 00004E26 *Apr 5 11:05:07.631: Attribute 61 6 00000002 *Apr 5 11:05:07.631: Attribute 1 11 6973646E *Apr 5 11:05:07.631: Attribute 30 7 38313536 *Apr 5 11:05:07.631: Attribute 3 19 0297959E *Apr 5 11:05:07.631: Attribute 6 6 00000002 *Apr 5 11:05:07.631: Attribute 7 6 00000001 *Apr 5 11:05:07.635: RADIUS: Received from id 13 172.22.53.201:1645, Access-Accept, len 32 *Apr 5 11:05:07.635: Attribute 6 6 00000002 *Apr 5 11:05:07.635: Attribute 7 6 00000001
The attribute value pairs (AVPs) from the debug radius command need to be decoded to better understand the transaction between the NAS and the RADIUS server.
Note: As of 12.2(11)T the output of debug radius is already decoded and hence does NOT require the use of Output Interpreter to decode the output. Refer to the document RADIUS Debug Enhancements for more information.
The Output Interpreter tool allows you to receive an analysis of the debug radius output.
The following output in italics is the result obtained from the Output Interpreter tool:
Access-Request 172.22.53.201:1645 id 13 Attribute Type 4: NAS-IP-Address is 172.22.53.141 Attribute Type 5: NAS-Port is 20006 Attribute Type 61: NAS-Port-Type is ISDN-Synchronous Attribute Type 1: User-Name is isdn Attribute Type 30: Called-Station-ID(DNIS) is 8156 Attribute Type 3: CHAP-Password is (encoded) Attribute Type 6: Service-Type is Framed Attribute Type 7: Framed-Protocol is PPP Access-Accept 172.22.53.201:1645 id 13 Attribute Type 6: Service-Type is Framed Attribute Type 7: Framed-Protocol is PPP
From the debug output decoded by the tool, verify that Attribute Type 6: Service-Type is Framed and Attribute Type 7: Framed-Protocol is PPP. If you observe that Attributes 6 or 7 are not as shown, correct the user profile on the RADIUS server (refer to the Configuration section). Also notice that debug radius shows an Access-Accept, which indicates that the RADIUS server successfully authenticated the user. If the output shows an Access-Reject, then the user was not authenticated and you should check the username and password configuration on the RADIUS server. Another attribute to verify is Attribute Type 4: NAS-IP-Address. Verify that the value displayed by the Output Interpreter Tool matches the NAS IP address configured on the RADIUS server.
Note: Due to Cisco IOS constraints and differences in debug output with different versions, some attributes may be truncated (for example, User-Name, Called-Station-ID(DNIS)).
*Apr 5 11:05:07.635: AAA/AUTHEN (2973699846): status = PASS !--- Authentication is successful *Apr 5 11:05:07.635: Se0:6 AAA/AUTHOR/LCP: Authorize LCP *Apr 5 11:05:07.635: Se0:6 AAA/AUTHOR/LCP (2783657211): Port='Serial0:6' list='' service=NET *Apr 5 11:05:07.635: AAA/AUTHOR/LCP: Se0:6 (2783657211) user='isdn_user' *Apr 5 11:05:07.635: Se0:6 AAA/AUTHOR/LCP (2783657211): send AV service=ppp *Apr 5 11:05:07.635: Se0:6 AAA/AUTHOR/LCP (2783657211): send AV protocol=lcp *Apr 5 11:05:07.635: Se0:6 AAA/AUTHOR/LCP (2783657211): found list "default" *Apr 5 11:05:07.635: Se0:6 AAA/AUTHOR/LCP (2783657211): Method=radius (radius) *Apr 5 11:05:07.635: Se0:6 AAA/AUTHOR (2783657211): Post authorization status = PASS_REPL *Apr 5 11:05:07.639: Se0:6 AAA/AUTHOR/LCP: Processing AV service=ppp *Apr 5 11:05:07.639: Se0:6 CHAP: O SUCCESS id 2 len 4 *Apr 5 11:05:07.639: Se0:6 PPP: Phase is UP *Apr 5 11:05:07.639: Se0:6 AAA/AUTHOR/FSM: (0): Can we start IPCP? *Apr 5 11:05:07.639: Se0:6 AAA/AUTHOR/FSM (3184893369): Port='Serial0:6' list='' service=NET *Apr 5 11:05:07.639: AAA/AUTHOR/FSM: Se0:6 (3184893369) user='isdn_user' *Apr 5 11:05:07.639: Se0:6 AAA/AUTHOR/FSM (3184893369): send AV service=ppp *Apr 5 11:05:07.639: Se0:6 AAA/AUTHOR/FSM (3184893369): send AV protocol=ip *Apr 5 11:05:07.639: Se0:6 AAA/AUTHOR/FSM (3184893369): found list "default" *Apr 5 11:05:07.639: Se0:6 AAA/AUTHOR/FSM (3184893369): Method=radius (radius) *Apr 5 11:05:07.639: Se0:6 AAA/AUTHOR (3184893369): Post authorization status = PASS_REPL *Apr 5 11:05:07.639: Se0:6 AAA/AUTHOR/FSM: We can start IPCP *Apr 5 11:05:07.639: Se0:6 IPCP: O CONFREQ [Not negotiated] id 2 len 10 *Apr 5 11:05:07.639: Se0:6 IPCP: Address 172.22.53.141 (0x0306AC16358D) *Apr 5 11:05:07.675: Se0:6 IPCP: I CONFREQ [REQsent] id 13 len 10 *Apr 5 11:05:07.675: Se0:6 IPCP: Address 0.0.0.0 (0x030600000000) *Apr 5 11:05:07.675: Se0:6 AAA/AUTHOR/IPCP: Start. Her address 0.0.0.0, we want 0.0.0.0 *Apr 5 11:05:07.675: Se0:6 AAA/AUTHOR/IPCP: Processing AV service=ppp *Apr 5 11:05:07.675: Se0:6 AAA/AUTHOR/IPCP: Authorization succeeded *Apr 5 11:05:07.675: Se0:6 AAA/AUTHOR/IPCP: Done. Her address 0.0.0.0, we want 0.0.0.0 *Apr 5 11:05:07.675: Se0:6 IPCP: Pool returned 172.22.53.142 !--- IP address for the peer obtained from the pool *Apr 5 11:05:07.675: Se0:6 IPCP: O CONFNAK [REQsent] id 13 len 10 *Apr 5 11:05:07.675: Se0:6 IPCP: Address 172.22.53.142 (0x0306AC16358E) *Apr 5 11:05:07.699: Se0:6 IPCP: I CONFACK [REQsent] id 2 len 10 *Apr 5 11:05:07.699: Se0:6 IPCP: Address 172.22.53.141 (0x0306AC16358D) *Apr 5 11:05:07.707: Se0:6 IPCP: I CONFREQ [ACKrcvd] id 14 len 10 *Apr 5 11:05:07.707: Se0:6 IPCP: Address 172.22.53.142 (0x0306AC16358E) *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR/IPCP: Start. Her address 172.22.53.142, we want 172.22.53.142 *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR/IPCP (3828612481): Port='Serial0:6' list='' service=NET *Apr 5 11:05:07.707: AAA/AUTHOR/IPCP: Se0:6 (3828612481) user='isdn_user' *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR/IPCP (3828612481): send AV service=ppp *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR/IPCP (3828612481): send AV protocol=ip *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR/IPCP (3828612481): send AV addr*172.22.53.142 *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR/IPCP (3828612481): found list "default" *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR/IPCP (3828612481): Method=radius (radius) *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR (3828612481): Post authorization status = PASS_REPL *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR/IPCP: Reject 172.22.53.142, using 172.22.53.142 *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR/IPCP: Processing AV service=ppp *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR/IPCP: Processing AV addr*172.22.53.142 *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR/IPCP: Authorization succeeded *Apr 5 11:05:07.707: Se0:6 AAA/AUTHOR/IPCP: Done. Her address 172.22.53.142, we want 172.22.53.142 *Apr 5 11:05:07.707: Se0:6 IPCP: O CONFACK [ACKrcvd] id 14 len 10 *Apr 5 11:05:07.707: Se0:6 IPCP: Address 172.22.53.142 (0x0306AC16358E) *Apr 5 11:05:07.707: Se0:6 IPCP: State is Open *Apr 5 11:05:07.711: Di1 IPCP: Install route to 172.22.53.142 !--- IPCP state is open. A route to the remote peer is installed *Apr 5 11:05:08.639: %LINEPROTO-5-UPDOWN: Line protocol on Interface Serial0:6, changed state to up *Apr 5 11:05:13.043: %ISDN-6-CONNECT: Interface Serial0:6 is now connected to isdn_user maui-nas-01#
This completes the negotiation for the ISDN client. The output shown below shows the negotiation for an an Async call (for example, a Windows client)
maui-nas-01# *Apr 5 11:05:53.527: ISDN Se0:23: RX <- SETUP pd = 8 callref = 0x21C5 !--- Incoming Setup message for Async Call. *Apr 5 11:05:53.527: Bearer Capability i = 0x9090A2 *Apr 5 11:05:53.527: Channel ID i = 0xA18388 *Apr 5 11:05:53.527: Progress Ind i = 0x8183 - Origination address is non-ISDN *Apr 5 11:05:53.527: Called Party Number i = 0xA1, '81560' *Apr 5 11:05:53.531: ISDN Se0:23: TX -> CALL_PROC pd = 8 callref = 0xA1C5 *Apr 5 11:05:53.531: Channel ID i = 0xA98388 *Apr 5 11:05:53.531: ISDN Se0:23: TX -> ALERTING pd = 8 callref = 0xA1C5 *Apr 5 11:05:53.667: ISDN Se0:23: TX -> CONNECT pd = 8 callref = 0xA1C5 *Apr 5 11:05:53.683: ISDN Se0:23: RX <- CONNECT_ACK pd = 8 callref = 0x21C5 *Apr 5 11:05:53.687: ISDN Se0:23: CALL_PROGRESS: CALL_CONNECTED call id 0x2E, bchan -1, dsl 0 *Apr 5 11:06:10.815: TTY5: DSR came up *Apr 5 11:06:10.815: tty5: Modem: IDLE->(unknown) *Apr 5 11:06:10.815: TTY5: EXEC creation *Apr 5 11:06:10.815: AAA: parse name=tty5 idb type=10 tty=5 *Apr 5 11:06:10.815: AAA: name=tty5 flags=0x11 type=4 shelf=0 slot=0 adapter=0 port=5 channel=0 *Apr 5 11:06:10.815: AAA: parse name=Serial0:7 idb type=12 tty=-1 *Apr 5 11:06:10.815: AAA: name=Serial0:7 flags=0x51 type=1 shelf=0 slot=0 adapter=0 port=0 channel=7 *Apr 5 11:06:10.815: AAA/MEMORY: create_user (0x614D4DBC) user='' ruser='' port='tty5' rem_addr='async/81560' authen_type=ASCII service=LOGIN priv=1 *Apr 5 11:06:10.815: AAA/AUTHEN/START (2673527044): port='tty5' list='' action=LOGIN service=LOGIN *Apr 5 11:06:10.815: AAA/AUTHEN/START (2673527044): using "default" list *Apr 5 11:06:10.815: AAA/AUTHEN/START (2673527044): Method=radius (radius) *Apr 5 11:06:10.815: AAA/AUTHEN (2673527044): status = GETUSER *Apr 5 11:06:10.815: TTY5: set timer type 10, 30 seconds *Apr 5 11:06:13.475: TTY5: Autoselect(2) sample 7E *Apr 5 11:06:13.475: TTY5: Autoselect(2) sample 7EFF *Apr 5 11:06:13.475: TTY5: Autoselect(2) sample 7EFF7D *Apr 5 11:06:13.475: TTY5: Autoselect(2) sample 7EFF7D23 *Apr 5 11:06:13.475: TTY5 Autoselect cmd: ppp negotiate !--- the router recongnizes the ppp packets and launches ppp. *Apr 5 11:06:13.475: AAA/AUTHEN/ABORT: (2673527044) because Autoselected. *Apr 5 11:06:13.475: AAA/MEMORY: free_user (0x614D4DBC) user='' ruser='' port='tty5' rem_addr='async/81560' authen_type=ASCII service=LOGIN priv=1 *Apr 5 11:06:13.479: TTY5: EXEC creation *Apr 5 11:06:13.479: TTY5: create timer type 1, 600 seconds *Apr 5 11:06:13.607: TTY5: destroy timer type 1 (OK) *Apr 5 11:06:13.607: TTY5: destroy timer type 0 *Apr 5 11:06:15.607: %LINK-3-UPDOWN: Interface Async5, changed state to up *Apr 5 11:06:15.607: As5 PPP: Treating connection as a dedicated line *Apr 5 11:06:15.607: As5 PPP: Phase is ESTABLISHING, Active Open !--- PPP negotiation begins. *Apr 5 11:06:15.607: As5 AAA/AUTHOR/FSM: (0): LCP succeeds trivially *Apr 5 11:06:15.607: As5 LCP: O CONFREQ [Closed] id 1 len 25 *Apr 5 11:06:15.607: As5 LCP: ACCM 0x000A0000 (0x0206000A0000) *Apr 5 11:06:15.607: As5 LCP: AuthProto CHAP (0x0305C22305) *Apr 5 11:06:15.607: As5 LCP: MagicNumber 0xE0531DB8 (0x0506E0531DB8) *Apr 5 11:06:15.607: As5 LCP: PFC (0x0702) *Apr 5 11:06:15.607: As5 LCP: ACFC (0x0802) *Apr 5 11:06:16.487: As5 LCP: I CONFREQ [REQsent] id 3 len 23 *Apr 5 11:06:16.487: As5 LCP: ACCM 0x000A0000 (0x0206000A0000) *Apr 5 11:06:16.487: As5 LCP: MagicNumber 0x65FFA5C7 (0x050665FFA5C7) *Apr 5 11:06:16.487: As5 LCP: PFC (0x0702) *Apr 5 11:06:16.487: As5 LCP: ACFC (0x0802) *Apr 5 11:06:16.487: As5 LCP: Callback 6 (0x0D0306) *Apr 5 11:06:16.487: Unthrottle 5 *Apr 5 11:06:16.487: As5 LCP: O CONFREJ [REQsent] id 3 len 7 *Apr 5 11:06:16.487: As5 LCP: Callback 6 (0x0D0306) *Apr 5 11:06:17.607: As5 LCP: TIMEout: State REQsent *Apr 5 11:06:17.607: As5 LCP: O CONFREQ [REQsent] id 2 len 25 *Apr 5 11:06:17.607: As5 LCP: ACCM 0x000A0000 (0x0206000A0000) *Apr 5 11:06:17.607: As5 LCP: AuthProto CHAP (0x0305C22305) *Apr 5 11:06:17.607: As5 LCP: MagicNumber 0xE0531DB8 (0x0506E0531DB8) *Apr 5 11:06:17.607: As5 LCP: PFC (0x0702) *Apr 5 11:06:17.607: As5 LCP: ACFC (0x0802) *Apr 5 11:06:17.735: As5 LCP: I CONFACK [REQsent] id 2 len 25 *Apr 5 11:06:17.735: As5 LCP: ACCM 0x000A0000 (0x0206000A0000) *Apr 5 11:06:17.735: As5 LCP: AuthProto CHAP (0x0305C22305) *Apr 5 11:06:17.735: As5 LCP: MagicNumber 0xE0531DB8 (0x0506E0531DB8) *Apr 5 11:06:17.735: As5 LCP: PFC (0x0702) *Apr 5 11:06:17.735: As5 LCP: ACFC (0x0802) *Apr 5 11:06:19.479: As5 LCP: I CONFREQ [ACKrcvd] id 4 len 23 *Apr 5 11:06:19.479: As5 LCP: ACCM 0x000A0000 (0x0206000A0000) *Apr 5 11:06:19.479: As5 LCP: MagicNumber 0x65FFA5C7 (0x050665FFA5C7) *Apr 5 11:06:19.479: As5 LCP: PFC (0x0702) *Apr 5 11:06:19.479: As5 LCP: ACFC (0x0802) *Apr 5 11:06:19.479: As5 LCP: Callback 6 (0x0D0306) *Apr 5 11:06:19.479: As5 LCP: O CONFREJ [ACKrcvd] id 4 len 7 *Apr 5 11:06:19.479: As5 LCP: Callback 6 (0x0D0306) *Apr 5 11:06:19.607: As5 LCP: TIMEout: State ACKrcvd *Apr 5 11:06:19.607: As5 LCP: O CONFREQ [ACKrcvd] id 3 len 25 *Apr 5 11:06:19.607: As5 LCP: ACCM 0x000A0000 (0x0206000A0000) *Apr 5 11:06:19.607: As5 LCP: AuthProto CHAP (0x0305C22305) *Apr 5 11:06:19.607: As5 LCP: MagicNumber 0xE0531DB8 (0x0506E0531DB8) *Apr 5 11:06:19.607: As5 LCP: PFC (0x0702) *Apr 5 11:06:19.607: As5 LCP: ACFC (0x0802) *Apr 5 11:06:19.607: As5 LCP: I CONFREQ [REQsent] id 5 len 20 *Apr 5 11:06:19.607: As5 LCP: ACCM 0x000A0000 (0x0206000A0000) *Apr 5 11:06:19.607: As5 LCP: MagicNumber 0x65FFA5C7 (0x050665FFA5C7) *Apr 5 11:06:19.607: As5 LCP: PFC (0x0702) *Apr 5 11:06:19.607: As5 LCP: ACFC (0x0802) *Apr 5 11:06:19.607: As5 LCP: O CONFACK [REQsent] id 5 len 20 *Apr 5 11:06:19.607: As5 LCP: ACCM 0x000A0000 (0x0206000A0000) *Apr 5 11:06:19.607: As5 LCP: MagicNumber 0x65FFA5C7 (0x050665FFA5C7) *Apr 5 11:06:19.607: As5 LCP: PFC (0x0702) *Apr 5 11:06:19.607: As5 LCP: ACFC (0x0802) *Apr 5 11:06:19.719: As5 LCP: I CONFACK [ACKsent] id 3 len 25 *Apr 5 11:06:19.719: As5 LCP: ACCM 0x000A0000 (0x0206000A0000) *Apr 5 11:06:19.719: As5 LCP: AuthProto CHAP (0x0305C22305) *Apr 5 11:06:19.719: As5 LCP: MagicNumber 0xE0531DB8 (0x0506E0531DB8) *Apr 5 11:06:19.719: As5 LCP: PFC (0x0702) *Apr 5 11:06:19.719: As5 LCP: ACFC (0x0802) *Apr 5 11:06:19.719: As5 LCP: State is Open *Apr 5 11:06:19.719: As5 PPP: Phase is AUTHENTICATING, by this end *Apr 5 11:06:19.719: As5 CHAP: O CHALLENGE id 1 len 32 from "maui-nas-01" *Apr 5 11:06:19.863: As5 CHAP: I RESPONSE id 1 len 33 from "async_client" !--- Incoming CHAP response from "async_client". *Apr 5 11:06:19.863: AAA: parse name=Async5 idb type=10 tty=5 *Apr 5 11:06:19.863: AAA: name=Async5 flags=0x11 type=4 shelf=0 slot=0 adapter=0 port=5 channel=0 *Apr 5 11:06:19.863: AAA: parse name=Serial0:7 idb type=12 tty=-1 *Apr 5 11:06:19.863: AAA: name=Serial0:7 flags=0x51 type=1 shelf=0 slot=0 adapter=0 port=0 channel=7 *Apr 5 11:06:19.863: AAA/MEMORY: create_user (0x6195AE40) user='async_client' ruser='' port='Async5' rem_addr='async/81560' authen_type=CHAP service=PPP priv=1 *Apr 5 11:06:19.863: AAA/AUTHEN/START (2673347869): port='Async5' list='' action=LOGIN service=PPP *Apr 5 11:06:19.863: AAA/AUTHEN/START (2673347869): using "default" list *Apr 5 11:06:19.863: AAA/AUTHEN (2673347869): status = UNKNOWN *Apr 5 11:06:19.863: AAA/AUTHEN/START (2673347869): Method=radius (radius) *Apr 5 11:06:19.863: RADIUS: ustruct sharecount=1 *Apr 5 11:06:19.867: RADIUS: Initial Transmit Async5 id 14 172.22.53.201:1645, Access-Request, len 90 *Apr 5 11:06:19.867: Attribute 4 6 AC16358D *Apr 5 11:06:19.867: Attribute 5 6 00000005 *Apr 5 11:06:19.867: Attribute 61 6 00000000 *Apr 5 11:06:19.867: Attribute 1 14 6173796E *Apr 5 11:06:19.867: Attribute 30 7 38313536 *Apr 5 11:06:19.867: Attribute 3 19 01B8292F *Apr 5 11:06:19.867: Attribute 6 6 00000002 *Apr 5 11:06:19.867: Attribute 7 6 00000001 *Apr 5 11:06:19.867: RADIUS: Received from id 14 172.22.53.201:1645, Access-Accept, len 32 *Apr 5 11:06:19.867: Attribute 6 6 00000002 *Apr 5 11:06:19.871: Attribute 7 6 00000001
The AVPs from the debug radius command need to be decoded to better understand the transaction between the NAS and the RADIUS server.
Note: As of 12.2(11)T the output of debug radius is already decoded and hence does NOT require the use of Output Interpreter to decode the output. Refer to the document RADIUS Debug Enhancements for more information
The Output Interpreter tool allows you to receive an analysis of the debug radius output.
The following output in italics is the result obtained from the Output Interpreter tool:
Access-Request 172.22.53.201:1645 id 14
Attribute Type 4: NAS-IP-Address is 172.22.53.141
Attribute Type 5: NAS-Port is 5
Attribute Type 61: NAS-Port-Type is Asynchronous
Attribute Type 1: User-Name is asyn
Attribute Type 30: Called-Station-ID(DNIS) is 8156
Attribute Type 3: CHAP-Password is (encoded)
Attribute Type 6: Service-Type is Framed
Attribute Type 7: Framed-Protocol is PPP
Access-Accept 172.22.53.201:1645 id 14
Attribute Type 6: Service-Type is Framed
Attribute Type 7: Framed-Protocol is PPP
From the debug output decoded by the tool, verify that Attribute Type 6: Service-Type is Framed and Attribute Type 7: Framed-Protocol is PPP. If you observe that Attributes 6 or 7 are not as shown, correct the user profile on the RADIUS server (refer to the Configuration section). Also notice that debug radius shows an Access-Accept, which indicates that the RADIUS server successfully authenticated the user. If the output shows an Access-Reject, then the user was not authenticated and you should check the username and password configuration on the RADIUS server. Another attribute to verify is Attribute Type 4: NAS-IP-Address. Verify that the value displayed by the Output Interpreter Tool matches the NAS IP address configured on the RADIUS server.
Note: Due to Cisco IOS constraints and differences in debug output with different versions, some attributes may be truncated (for example, User-Name, Called-Station-ID(DNIS)).
*Apr 5 11:06:19.871: AAA/AUTHEN (2673347869): status = PASS *Apr 5 11:06:19.871: As5 AAA/AUTHOR/LCP: Authorize LCP *Apr 5 11:06:19.871: As5 AAA/AUTHOR/LCP (3232903941): Port='Async5' list='' service=NET *Apr 5 11:06:19.871: AAA/AUTHOR/LCP: As5 (3232903941) user='async_client' *Apr 5 11:06:19.871: As5 AAA/AUTHOR/LCP (3232903941): send AV service=ppp *Apr 5 11:06:19.871: As5 AAA/AUTHOR/LCP (3232903941): send AV protocol=lcp *Apr 5 11:06:19.871: As5 AAA/AUTHOR/LCP (3232903941): found list "default" *Apr 5 11:06:19.871: As5 AAA/AUTHOR/LCP (3232903941): Method=radius (radius) *Apr 5 11:06:19.871: As5 AAA/AUTHOR (3232903941): Post authorization status = PASS_REPL *Apr 5 11:06:19.871: As5 AAA/AUTHOR/LCP: Processing AV service=ppp *Apr 5 11:06:19.871: As5 CHAP: O SUCCESS id 1 len 4 *Apr 5 11:06:19.871: As5 PPP: Phase is UP *Apr 5 11:06:19.871: As5 AAA/AUTHOR/FSM: (0): Can we start IPCP? *Apr 5 11:06:19.871: As5 AAA/AUTHOR/FSM (1882093345): Port='Async5' list='' service=NET *Apr 5 11:06:19.871: AAA/AUTHOR/FSM: As5 (1882093345) user='async_client' *Apr 5 11:06:19.871: As5 AAA/AUTHOR/FSM (1882093345): send AV service=ppp *Apr 5 11:06:19.871: As5 AAA/AUTHOR/FSM (1882093345): send AV protocol=ip *Apr 5 11:06:19.871: As5 AAA/AUTHOR/FSM (1882093345): found list "default" *Apr 5 11:06:19.871: As5 AAA/AUTHOR/FSM (1882093345): Method=radius (radius) *Apr 5 11:06:19.871: As5 AAA/AUTHOR (1882093345): Post authorization status = PASS_REPL *Apr 5 11:06:19.871: As5 AAA/AUTHOR/FSM: We can start IPCP *Apr 5 11:06:19.875: As5 IPCP: O CONFREQ [Closed] id 1 len 10 *Apr 5 11:06:19.875: As5 IPCP: Address 172.22.53.141 (0x0306AC16358D) *Apr 5 11:06:19.991: As5 IPCP: I CONFREQ [REQsent] id 1 len 34 *Apr 5 11:06:19.991: As5 IPCP: Address 0.0.0.0 (0x030600000000) *Apr 5 11:06:19.991: As5 IPCP: PrimaryDNS 0.0.0.0 (0x810600000000) *Apr 5 11:06:19.991: As5 IPCP: PrimaryWINS 0.0.0.0 (0x820600000000) *Apr 5 11:06:19.991: As5 IPCP: SecondaryDNS 0.0.0.0 (0x830600000000) *Apr 5 11:06:19.991: As5 IPCP: SecondaryWINS 0.0.0.0 (0x840600000000) *Apr 5 11:06:19.991: As5 AAA/AUTHOR/IPCP: Start. Her address 0.0.0.0, we want 172.22.53.148 !--- The address for the peer obtained from the pool. *Apr 5 11:06:19.991: As5 AAA/AUTHOR/IPCP: Processing AV service=ppp *Apr 5 11:06:19.991: As5 AAA/AUTHOR/IPCP: Authorization succeeded *Apr 5 11:06:19.991: As5 AAA/AUTHOR/IPCP: Done. Her address 0.0.0.0, we want 172.22.53.148 *Apr 5 11:06:19.991: As5 IPCP: O CONFREJ [REQsent] id 1 len 22 *Apr 5 11:06:19.991: As5 IPCP: PrimaryWINS 0.0.0.0 (0x820600000000) *Apr 5 11:06:19.995: As5 IPCP: SecondaryDNS 0.0.0.0 (0x830600000000) *Apr 5 11:06:19.995: As5 IPCP: SecondaryWINS 0.0.0.0 (0x840600000000) *Apr 5 11:06:20.007: As5 IPCP: I CONFACK [REQsent] id 1 len 10 *Apr 5 11:06:20.007: As5 IPCP: Address 172.22.53.141 (0x0306AC16358D) *Apr 5 11:06:20.119: As5 IPCP: I CONFREQ [ACKrcvd] id 2 len 16 *Apr 5 11:06:20.119: As5 IPCP: Address 0.0.0.0 (0x030600000000) *Apr 5 11:06:20.119: As5 IPCP: PrimaryDNS 0.0.0.0 (0x810600000000) *Apr 5 11:06:20.119: As5 AAA/AUTHOR/IPCP: Start. Her address 0.0.0.0, we want 172.22.53.148 *Apr 5 11:06:20.119: As5 AAA/AUTHOR/IPCP: Processing AV service=ppp *Apr 5 11:06:20.119: As5 AAA/AUTHOR/IPCP: Authorization succeeded *Apr 5 11:06:20.119: As5 AAA/AUTHOR/IPCP: Done. Her address 0.0.0.0, we want 172.22.53.148 *Apr 5 11:06:20.119: As5 IPCP: O CONFNAK [ACKrcvd] id 2 len 16 *Apr 5 11:06:20.119: As5 IPCP: Address 172.22.53.148 (0x0306AC163594) *Apr 5 11:06:20.119: As5 IPCP: PrimaryDNS 172.22.53.210 (0x8106AC1635D2) *Apr 5 11:06:20.231: As5 IPCP: I CONFREQ [ACKrcvd] id 3 len 16 *Apr 5 11:06:20.231: As5 IPCP: Address 172.22.53.148 (0x0306AC163594) *Apr 5 11:06:20.231: As5 IPCP: PrimaryDNS 172.22.53.210 (0x8106AC1635D2) *Apr 5 11:06:20.231: As5 AAA/AUTHOR/IPCP: Start. Her address 172.22.53.148, we want 172.22.53.148 *Apr 5 11:06:20.231: As5 AAA/AUTHOR/IPCP (3727543204): Port='Async5' list='' service=NET *Apr 5 11:06:20.231: AAA/AUTHOR/IPCP: As5 (3727543204) user='async_client' *Apr 5 11:06:20.231: As5 AAA/AUTHOR/IPCP (3727543204): send AV service=ppp *Apr 5 11:06:20.231: As5 AAA/AUTHOR/IPCP (3727543204): send AV protocol=ip *Apr 5 11:06:20.231: As5 AAA/AUTHOR/IPCP (3727543204): send AV addr*172.22.53.148 *Apr 5 11:06:20.231: As5 AAA/AUTHOR/IPCP (3727543204): found list "default" *Apr 5 11:06:20.231: As5 AAA/AUTHOR/IPCP (3727543204): Method=radius (radius) *Apr 5 11:06:20.235: As5 AAA/AUTHOR (3727543204): Post authorization status = PASS_REPL *Apr 5 11:06:20.235: As5 AAA/AUTHOR/IPCP: Reject 172.22.53.148, using 172.22.53.148 *Apr 5 11:06:20.235: As5 AAA/AUTHOR/IPCP: Processing AV service=ppp *Apr 5 11:06:20.235: As5 AAA/AUTHOR/IPCP: Processing AV addr*172.22.53.148 *Apr 5 11:06:20.235: As5 AAA/AUTHOR/IPCP: Authorization succeeded *Apr 5 11:06:20.235: As5 AAA/AUTHOR/IPCP: Done. Her address 172.22.53.148, we want 172.22.53.148 *Apr 5 11:06:20.235: As5 IPCP: O CONFACK [ACKrcvd] id 3 len 16 *Apr 5 11:06:20.235: As5 IPCP: Address 172.22.53.148 (0x0306AC163594) *Apr 5 11:06:20.235: As5 IPCP: PrimaryDNS 172.22.53.210 (0x8106AC1635D2) *Apr 5 11:06:20.235: As5 IPCP: State is Open *Apr 5 11:06:20.235: As5 IPCP: Install route to 172.22.53.148 !--- Route to remote peer is installed. *Apr 5 11:06:20.871: %LINEPROTO-5-UPDOWN: Line protocol on Interface Async5, changed state to up
Related Information
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
09-Sep-2005 |
Initial Release |
 Feedback
Feedback