Configuring CET Encryption with a GRE Tunnel
Available Languages
Contents
Introduction
To configure Cisco Encryption Technology (CET) encryption with a tunnel, you must configure encryption on the tunnel's interface. Additionally, you must configure encryption on the physical interface that heads toward the tunnel's eventual destination.
Note: CET encryption is now end-of-life. IPSec is the recommended encryption scheme for migration.
Prerequisites
Requirements
There are no specific requirements for this document.
Components Used
This document is not restricted to specific software and hardware versions.
Conventions
For more information on document conventions, refer to Cisco Technical Tips Conventions.
Configure
In this section, you are presented with the information to configure the features described in this document.
Note: To find additional information on the commands used in this document, use the Command Lookup Tool (registered customers only) .
Network Diagram
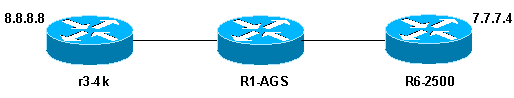
This document uses this network setup:
Network Diagram Notes
-
8.8.8.8, behind r3-4k, and 7.7.7.4, behind R6-2500, are end stations. When they ping each other, the traffic goes through the tunnel.
-
The generic routing encapsulation (GRE) tunnel is configured with loopback interfaces as the tunnel source and destination.
-
Traffic through the tunnel is also encrypted. The implementation of this feature requires that to encrypt tunnel traffic, the crypto map must be attached to both the tunnel interface and the physical outbound interface.
Configurations
This document uses these configurations:
| r3-4k |
|---|
hostname r3-4k
!
crypto public-key r6-2500 02014544
F3681B5D 32372A19 0C0CCC4B E707F829 D882CF30 A9B4DBE3 E1911E9C F6A9E162
732558DF A20FEFAD 2ACC400E 8DDB10B1 3566FA3A E55A9BBE 00916AAD 20A0C75C
quit
!
crypto map my_crypto_map 10
set algorithm 40-bit-des
set peer r6-2500
match address 128
!
interface Loopback0
ip address 1.1.6.1 255.255.255.0
!
interface Tunnel0
ip address 5.5.5.1 255.255.255.0
tunnel source Loopback0
tunnel destination 2.2.6.3
crypto map my_crypto_map
!
interface Ethernet0
ip address 1.1.1.1 255.255.255.0
description inside interface
media-type 10BaseT
crypto map my_crypto_map
!
!
interface Serial0
encapsulation frame-relay
no ip route-cache
!
interface Serial0.1 point-to-point
description outside interface
ip address 8.8.8.1 255.255.255.0
frame-relay interface-dlci 100
!
!ip classless
ip route 0.0.0.0 0.0.0.0 1.1.1.2
ip route 7.0.0.0 255.0.0.0 5.5.5.2
access-list 128 permit gre host 1.1.6.1 host 2.2.6.3
! |
| R1-AGS |
|---|
! hostname R1-AGS ! interface Ethernet0 ip address 1.1.1.2 255.255.255.0 ! interface Serial1 ip address 2.2.5.2 255.255.255.0 ! ip classless ip route 1.0.0.0 255.0.0.0 1.1.1.1 ip route 2.0.0.0 255.0.0.0 2.2.5.3 |
| R6-2500 |
|---|
hostname R6-2500 ! crypto public-key r3-4k 04D6265A 512A7D84 43C348B7 959D2FE2 3122B285 FDA2A362 7272A835 84D03134 DB160DE1 27CA2D24 D6C23EFE 3BE25A95 D62EA30B 0F2C3BA8 9AB6DB82 D8127238 266AC987 quit ! crypto map my_crypto_map 10 set algorithm 40-bit-des set peer r3-4k match address 128 ! interface Loopback0 ip address 2.2.6.3 255.255.255.0 ! interface Tunnel0 ip address 5.5.5.2 255.255.255.0 tunnel source Loopback0 tunnel destination 1.1.6.1 crypto map my_crypto_map ! interface Ethernet 0 description inside interface ip address 7.7.7.3 255.255.255.0 ! interface Serial0 description outside interface ip address 2.2.5.3 255.255.255.0 crypto map my_crypto_map ! ip classless ip route 0.0.0.0 0.0.0.0 2.2.5.2 ip route 7.0.0.0 255.0.0.0 7.7.7.0 ip route 8.0.0.0 255.0.0.0 5.5.5.1 ! access-list 128 permit gre host 2.2.6.3 host 1.1.6.1 |
Verify
There is currently no verification procedure available for this configuration.
Troubleshoot
There is currently no specific troubleshooting information available for this configuration.
Related Information
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
11-Dec-2001 |
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback