Configuring a PC as a PPPoA Client Using L3 SSG/SSD
Available Languages
Contents
Introduction
The sample configuration described in this document shows a remote client that accesses an Internet Service Provider (ISP) network using Point-to-Point Protocol over Asynchronous Transfer Mode (PPPoA).
The remote client wants to access a Layer 2 Tunneling Protocol (L2TP) service using Layer 3 Service Selection Gateway/Service Selection Dashboard (SSG/SSD). The L2TP service is represented in the configuration with a host IP address of 15.15.15.5. Using Dynamic Host Configuration Protocol (DHCP), the Cisco 677 provides an IP address to the PC from an IP address pool of 10.0.0.2 to 10.0.0.254, with a mask of 255.255.255.0. Also, Port Address Translation (PAT) is enabled on the Cisco 677.
There are three tests for this sample configuration:
-
The SSG-related debugs during different steps of the service logon by the remote client.
-
The single sign-on SSD 2.5.1 feature.
-
Enabling the SSD debugging.
Before You Begin
Conventions
For more information on document conventions, see the Cisco Technical Tips Conventions.
Prerequisites
There are no specific prerequisites for this document.
Components Used
The information in this document is based on the software and hardware versions below.
-
Cisco C6400R software (C6400R-G4P5-M), version 12.1(5)DC1
-
Cisco 7200 software (C7200-IS-M), version 12.2(1)
The information presented in this document was created from devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If you are working in a live network, ensure that you understand the potential impact of any command before using it.
Configure
In this section, you are presented with the information to configure the features described in this document.
Note: To find additional information on the commands used in this document, use the Command Lookup Tool (registered customers only) .
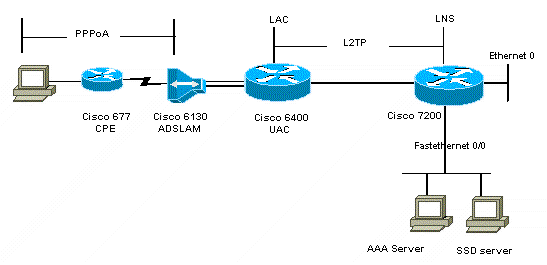
Network Diagram
This document uses the network setup shown in the diagram below.
Configurations
This document uses the configurations shown below.
| Cisco 6400 LAC (airelle_nrp3) |
|---|
Building configuration... Current configuration : 125008 bytes ! ! Last configuration change at 02:11:30 UTC Mon Jun 18 2001 ! NVRAM config last updated at 00:43:51 UTC Mon Jun 18 2001 ! version 12.1 no service single-slot-reload-enable service timestamps debug datetime msec service timestamps log uptime no service password-encryption ! hostname arielle_nrp3 ! boot system tftp c6400r-g4p5-mz.121-5.DC1 172.17.247.195 logging rate-limit console 10 except errors aaa new-model aaa authentication login default none aaa authentication login tty enable aaa authentication ppp ayman group radius aaa nas port extended enable password ww ! username ayman@cairo.com password 0 ayman redundancy main-cpu auto-sync standard no secondary console enable ip subnet-zero ip cef no ip finger no ip domain-lookup ! ! vpdn enable no vpdn logging vpdn search-order domain ! ! ssg enable ssg default-network 10.200.56.0 255.255.255.0 ssg service-password cisco ssg radius-helper auth-port 1645 acct-port 1646 ssg radius-helper key cisco ssg next-hop download nxthoptbl cisco ssg bind direction downlink Virtual-Template66 ssg service-search-order remote local ! ! interface Loopback3 ip address 200.200.200.1 255.255.255.252 ! ! interface ATM0/0/0.61 point-to-point description LAC L2TP connection to Ior ip address 14.14.14.6 255.255.255.252 pvc 61/61 broadcast encapsulation aal5snap ! ! ! interface ATM0/0/0.5555 multipoint pvc 66/66 encapsulation aal5mux ppp Virtual-Template66 ! ! ! interface Ethernet0/0/1 no ip address ! interface Ethernet0/0/0 ip address 3.0.0.2 255.255.255.0 no ip mroute-cache shutdown tag-switching ip ! interface FastEthernet0/0/0 ip address 10.200.56.6 255.255.255.0 no ip mroute-cache half-duplex ! ! interface Virtual-Template66 ip unnumbered Loopback3 peer default ip address pool ayman ppp authentication pap ayman ! ! router eigrp 5 network 14.14.14.4 0.0.0.3 no auto-summary no eigrp log-neighbor-changes ! ip local pool ayman 212.93.193.114 212.93.193.126 ip route 10.0.0.0 255.255.255.0 212.93.193.114 ! radius-server host 10.200.56.16 auth-port 1645 acct-port 1646 radius-server retransmit 3 radius-server attribute 25 nas-port format d radius-server attribute nas-port format d radius-server key cisco ! ! line con 0 exec-timeout 0 0 login authentication tty transport input none line aux 0 line vty 0 4 exec-timeout 0 0 password ww login authentication tty ! end |
| Cisco 7204 LNS (hostname ior) |
|---|
Building configuration... Current configuration : 6769 bytes ! version 12.2 no service single-slot-reload-enable service timestamps debug datetime msec localtime show-timezone service timestamps log datetime localtime show-timezone no service password-encryption ! hostname ior ! boot system flash c7200-is-mz.122-1.bin logging buffered 16384 debugging logging rate-limit console 10 except errors aaa new-model aaa authentication login default none aaa authentication login tty enable aaa authentication ppp ayman local aaa nas port extended enable password 7 03134C ! username ayman@cairo.com password 0 ayman clock timezone GMT+1 1 clock summer-time PDT recurring ip subnet-zero no ip source-route ip cef ! ! no ip finger ip tcp window-size 8192 ip ftp username tftp ip ftp password 7 061118 ip host rund 172.17.247.195 ip host PAGENT-SECURITY-V3 57.63.30.76 95.26.0.0 ! ! ! ! ! vpdn enable no vpdn logging vpdn search-order domain ! vpdn-group 1 accept-dialin protocol l2tp virtual-template 24 terminate-from hostname nap local name cairo l2tp tunnel password 7 052827261363 ! ! interface Loopback1 ip address 212.93.194.5 255.255.255.252 ! interface Loopback2 ip address 15.15.15.5 255.255.255.252 ! ! interface FastEthernet0/0 ip address 10.200.56.2 255.255.255.0 ip ospf network point-to-multipoint no ip mroute-cache load-interval 60 duplex half no cdp enable ! interface ATM2/0 no ip mroute-cache atm pvc 1 0 5 qsaal atm pvc 2 0 16 ilmi no atm ilmi-keepalive ! ! ! ! ! interface ATM2/0.61 point-to-point description L2TP tunnel link ip address 14.14.14.5 255.255.255.252 pvc 61/61 broadcast encapsulation aal5snap ! ! interface ATM2/0.5555 multipoint pvc 55/55 encapsulation aal5mux ppp Virtual-Template24 ! ! ! interface Virtual-Template24 ip unnumbered Loopback1 peer default ip address pool SSG-L2TP ppp authentication pap ayman ! ! router eigrp 5 network 14.14.14.4 0.0.0.3 network 15.15.15.4 0.0.0.3 no auto-summary no eigrp log-neighbor-changes ! ! ip route 212.93.193.112 255.255.255.252 14.14.14.6 ip local pool SSG-L2TP 212.93.197.114 212.93.197.126 radius-server host 10.200.56.16 auth-port 1645 acct-port 1646 radius-server retransmit 3 radius-server attribute 25 nas-port format d radius-server attribute nas-port format d radius-server key cisco radius-server vsa send accounting radius-server vsa send authentication ! ! ! ! line con 0 exec-timeout 0 0 password 7 010411 login authentication tty transport input none line aux 0 password 7 021113 line vty 0 4 exec-timeout 0 0 password 7 010411 login authentication tty line vty 5 15 ! end ! |
You must reset the Cisco 677 to its default configuration before you implement the new configuration. To restore the default configuration use the set nvram erase command; for example:
cbos#set nvram erase Erasing running configuration. You must use "write" for changes to be permanent. cbos#write NVRAM written. cbos#reboot
Enabling the DHCP server feature on the Cisco 677 Cisco Broadband Operating System (CBOS) automatically creates a pool named "pool0" and assigns a subnet of 10.0.0.0 with a mask of 255.255.255.0. By default, the IP address of the Cisco 677 Ethernet interface is assigned the address of 10.0.0.1, and the "pool0" is then able to lease IP addresses between 10.0.0.2 and 10.0.0.254 for the local LAN clients/PC.
| Cisco 677 |
|---|
!--- This configuration must be done !--- after NVRAM has been erased. set ppp wanipcp 0.0.0.0 set ppp wan0-0 login hisham set ppp wan0-0 passward hisham set dhcp server enabled set nat enabled set int wan0-0 close set int wan0-0 vpi 1 set int wan0-0 vci 60 set int wan0-0 open write reboot |
RADIUS Profiles
The following Remote Dial-In User Service (RADIUS) profiles are for the remote user and for the services.
| Profile of Remote User hisham |
|---|
root@canonball[/opt/csecure/CLI]ViewProfile -p 9900 -u hisham
User Profile Information
user = hisham{
profile_id = 119
profile_cycle = 11
member = ayman
radius=SSG-6400 {
check_items= {
2=hisham
}
reply_attributes= {
6=2
7=1
9,250="GTravelling"
}
}
} |
| Profile of Service Group Travelling |
|---|
root@canonball[/opt/csecure/CLI]ViewProfile -p 9900 -u Travelling
User Profile Information
user = Travelling{
profile_id = 165
profile_cycle = 3
member = Services
radius=SSG-6400 {
check_items= {
2=cisco
}
reply_attributes= {
6=5
9,250="IMiddle East"
9,250="GCities"
}
}
}
|
| Profile of Service Group Cities |
|---|
User Profile Information
user = Cities{
profile_id = 167
profile_cycle = 3
member = Services
radius=SSG-6400 {
check_items= {
2=cisco
}
reply_attributes= {
6=5
9,250="ICairo"
9,250="Ncairo.com"
}
}
} |
| Profile of cairo.com Service |
|---|
root@canonball[/opt/csecure/CLI]ViewProfile -p 9900 -u cairo.com
User Profile Information
user = cairo.com{
profile_id = 144
profile_cycle = 17
member = Services
radius=SSG-6400 {
check_items= {
2=cisco
}
reply_attributes= {
6=5
9,1="vpdn:tunnel-id=nap"
9,1="vpdn:l2tp-tunnel-password=CAIRO"
9,1="vpdn:tunnel-type=l2tp"
9,1="vpdn:ip-addresses=15.15.15.5"
9,251="Ocairo.com"
9,251="R15.15.15.4;255.255.255.252"
9,251="TT"
9,251="IEgyptian Capital"
9,251="Gcairo.com_key"
}
}
} |
| Profile of Next Hop Table |
|---|
root@canonball[/opt/csecure/CLI]ViewProfile -p 9900 -u nxthoptbl
User Profile Information
user = nxthoptbl{
profile_id = 168
profile_cycle = 2
member = Services
radius=SSG-6400 {
check_items= {
2=cisco
}
reply_attributes= {
6=5
9,253="Gcairo.com_key;14.14.14.5"
}
}
} |
Verify
There is currently no verification procedure available for this configuration.
Troubleshoot
What is the single sign-on SSD 2.5.1 feature?
This feature applies to an SSD server. When the SSD server cannot find a host object in its cache database for a remote client sending HTTP traffic, it sends an access request to the SSG. If the SSG has a host object, it sends an access accept message to the SSD. The user can then grant access to the services.
If there is no host object on the SSD or SSG, then the user should authenticate on the SSD with normal SSD logon authentication procedures.
What do I need to know before I configure SSG and SSD?
Before you configure SSD or SSG, you have to verify the following:
-
SSD, SSG, and Authentication, Authorization, and Accounting (AAA) are all running, and all network entities can ping one another.
-
The remote user can ping any host in the default network (SSG, SSD, AAA) before logging on to the SSD server.
-
The Network Access Provider (NAP), in this case the Cisco 6400 NRP1, can ping the service destination network.
-
The remote client cannot ping the remote service destination network.
What do I do after the PPPoA session is initiated but before an SSD logon is set?
After all the SSG commands are configured, you must verify that the next hop table for the user's services has been successfully downloaded. Issue the show ssg binding command.
arielle_nrp3# show ssg binding cairo.com_key -> 14.14.14.5 (NHT) arielle_nrp3# show ssg next-hop Next hop table loaded from profile nxthoptbl: cairo.com_key -> 14.14.14.5 End of next hop table.
Check that all your direction bindings are active on the SSG.
arielle_nrp3# show ssg direction Virtual-Template66: Downlink !--- You can verify this by enabling debug ssg ctrl-events after the !--- remote user tries to initiate its PPPoA session to access the NRP. Jun 18 02:13:12.791: SSG-CTL-EVN: Handling PPP logon for user hisham. Jun 18 02:13:12.791: SSG-CTL-EVN: Locate/create SSG sub-block from/for Virtual-Access3. Jun 18 02:13:12.791: SSG-CTL-EVN: Checking for old HostObject in the sub-block. Jun 18 02:13:12.791: SSG-CTL-EVN: SSG: pppterm: NO extra data for PPP logon Jun 18 02:13:12.791: SSG-CTL-EVN: Authenticating user hisham for PPP logon. Jun 18 02:13:12.799: SSG-CTL-EVN: Creating HostObject for the PPP user hisham. Jun 18 02:13:12.799: SSG-CTL-EVN: Set Host Mac Address . Jun 18 02:13:12.799: SSG-CTL-EVN: ** attr->type = 6 Jun 18 02:13:12.799: SSG-CTL-EVN: ATTR_LOOP = 1 Jun 18 02:13:12.799: SSG-CTL-EVN: ** attr->type = 7 Jun 18 02:13:12.799: SSG-CTL-EVN: ATTR_LOOP = 2 Jun 18 02:13:12.799: SSG-CTL-EVN: ATTR_LOOP = 3 Jun 18 02:13:12.799: SSG-CTL-EVN: ATTR_LOOP = 4 Jun 18 02:13:12.799: SSG-CTL-EVN: PPP logon for user hisham is accepted. The link is Virtual-Access3 Jun 18 02:13:12.799: SSG-CTL-EVN: Bind the HostObject to Virtual-Access3. !--- Downlink binding success. Jun 18 02:13:12.867: SSG-CTL-EVN: IPCP is up. Locate SSG sub-block from Virtual-Access3. Jun 18 02:13:12.871: SSG-CTL-EVN: Locate HostObject from the sub-block. Jun 18 02:13:12.871: SSG-CTL-EVN: Set Host IP 212.93.193.114. !--- Host object is created. Jun 18 02:13:12.879: SSG-CTL-EVN: Host Mac Address lookup failed Jun 18 02:13:12.879: SSG-CTL-EVN: Activate the HostObject. Link=Virtual-Access3 !--- Host object is active. Jun 18 02:13:12.879: SSG-CTL-EVN: ##### ssg_l2tp_ip_up: 03:49:01: %LINEPROTO-5-UPDOWN: Line protocol on Interface Virtual-Access3, changed state to up
When a client is initiating an HTTP session to the SSD server, the user sees the SSD server logon home page.
Note: Remember to start the SSD server operation by issuing the UNIX shell command root@crazyball[/export/home/ssd251/ssd]startSSD.sh.
How do I test the SSD single sign-on feature?
-
Configure the parameter (REAUTHENTICATE=off) in the dashboard.conf file. The default value is REAUTHENTICATE=on.
-
Log on to any Web page on the SSD. For example, while you are logged on to the cairo.com service home page, close your browser, and then open it again with http://10.200.56.40:8080.
The host object on the SSD is still in the cache, so you should be able to log on again to the SSD service page that you were logged onto previously. The default behavior is to re-authenticate on the SSD; that is, you have to get to the SSD logon home page.
How do I run SSD debugging?
-
Type https://10.200.56.40:8443/log in the address bar of the browser.
-
Click Set Option. All the debugs you selected run, and the output is logged in a log file. The format for the log file name is yy_mm_dd.request.log.
-
Navigate to the directory on the SSD server where the log files reside.
-
Using a UNIX editor, open the file /export/home/ssd251/ssd/logs]vi yy_mm_dd.request.log to view the debug output.
Sample debug Output
NRP1 Output
arielle_nrp3# show debugging SSG: SSG data path packets debugging is on SSG control path events debugging is on SSG control path packets debugging is on SSG packets debugging is on Radius protocol debugging is on Just before the SSD logon, the output of these debugs are : Jun 18 23:30:08.414: SSG-DATA:CEF-SSGSubBlock=0(AT0/0/0.61:0.0.0.0->0.0.0.0) Jun 18 23:30:09.530: SSG-DATA:CEF-FIB_FLAG_RECEIVE=1(Vi3:212.93.193.114->10.200.56.6) Jun 18 23:30:11.142: SSG-DATA:CEF-SSGSubBlock=0(AT0/0/0.61:0.0.0.0->0.0.0.0) Jun 18 23:30:11.494: SSG-DATA:CEF-FIB_FLAG_RECEIVE=1(Vi3:212.93.193.114->10.200.56.6) Jun 18 23:30:12.482: SSG-DATA:CEF-FIB_FLAG_RECEIVE=1(Vi3:212.93.193.114->10.200.56.6) Jun 18 23:30:13.310: SSG-DATA:CEF-SSGSubBlock=0(AT0/0/0.61:0.0.0.0->0.0.0.0) Jun 18 23:30:14.462: Jun 18 23:39:39.610: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 18 23:39:39.638: SSG-DATA:CEF-UP-DefaultNetwork=1(Vi3:212.93.193.114->10.200.56.40) Jun 18 23:39:39.638: SSG-DATA:CEF-UP-DefaultNetwork=1(Vi3:212.93.193.114->10.200.56.40) Jun 18 23:39:39.642: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 18 23:39:39.642: SSG-DATA:CEF-UP-DefaultNetwork=1(Vi3:212.93.193.114->10.200.56.40) Jun 18 23:39:39.646: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 18 23:39:39.674: SSG-DATA:CEF-UP-DefaultNetwork=1(Vi3:212.93.193.114->10.200.56.40) Jun 18 23:39:39.678: SSG-DATA:CEF-UP-DefaultNetwork=1(Vi3:212.93.193.114->10.200.56.40) Jun 18 23:39:39.678: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 18 23:39:39.682: SSG-DATA:CEF-UP-DefaultNetwork=1(Vi3:212.93.193.114->10.200.56.40) Jun 18 23:39:39.686: SSG-DATA:CEF-UP-DefaultNetwork=1(Vi3:212.93.193.114->10.200.56.40) Jun 18 23:39:39.686: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 18 23:39:39.698: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 18 23:39:39.742: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 18 23:39:39.926: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 18 23:39:39.926: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 18 23:39:39.926: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 18 23:39:39.926: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 19 00:39:17.477: RADIUS: Initial Transmit id 18 10.200.56.16:1645, Access-Request, len 58 Jun 19 00:39:17.477: Attribute 4 6 D45DC301 Jun 19 00:39:17.477: Attribute 61 6 00000000 Jun 19 00:39:17.477: Attribute 1 8 68697368 Jun 19 00:39:17.477: Attribute 2 18 31B0CDC2 Jun 19 00:39:17.481: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 19 00:39:17.481: RADIUS: Received from id 18 10.200.56.16:1645, Access-Accept, len 70 Jun 19 00:39:17.481: Attribute 6 6 00000002 Jun 19 00:39:17.481: Attribute 7 6 00000001 Jun 19 00:39:17.481: Attribute 26 20 00000009FA0E4754 Jun 19 00:39:17.481: Attribute 26 18 00000009FA0C4742 Jun 19 00:39:17.481: RADIUS: saved authorization data for user 61E73934 at 61E72A58 Jun 19 00:39:17.481: SSG-CTL-EVN: Creating HostObject for host 212.93.193.114. Jun 19 00:39:17.489: SSG-CTL-EVN: Set Host Mac Address . Jun 19 00:39:17.489: SSG-CTL-EVN: ** attr->type = 6 Jun 19 00:39:17.489: SSG-CTL-EVN: ATTR_LOOP = 1 Jun 19 00:39:17.489: SSG-CTL-EVN: ** attr->type = 7 Jun 19 00:39:17.493: SSG-CTL-EVN: ATTR_LOOP = 2 Jun 19 00:39:17.493: SSG-CTL-EVN: ATTR_LOOP = 3 Jun 19 00:39:17.493: SSG-CTL-EVN: ATTR_LOOP = 4 Jun 19 00:39:17.493: SSG-CTL-EVN: Account logon is accepted (212.93.193.114,hisham). arielle_nrp3# show ssg host 212.93.193.114 ------------------------ HostObject Content ----------------------- Activated: TRUE Interface: Virtual-Access3 User Name: hisham Host IP: 212.93.193.114 Msg IP: 10.200.56.40 (9902) Host DNS IP: 0.0.0.0 Maximum Session Timeout: 0 seconds Host Idle Timeout: 0 seconds Class Attr: NONE User logged on since: 01:54:33.000 UTC Tue Jun 19 2001 User last activity at: 01:54:33.000 UTC Tue Jun 19 2001 Default Service: NONE DNS Default Service: NONE Active Services: NONE !--- No Services are active yet. AutoService: NONE Subscribed Services: The following output also results from the debug commands that are turned on before the SSD logon. Jun 19 02:06:39.529: SSG-DATA:CEF-FIB_FLAG_RECEIVE=1(Vi3:212.93.193.114->10.200.56.6) Jun 19 02:06:40.789: SSG-DATA:CEF-MulticastDest=1(AT0/0/0.61:14.14.14.5->224.0.0.10) Jun 19 02:06:41.581: SSG-DATA:CEF-FIB_FLAG_RECEIVE=1(Vi3:212.93.193.114->10.200.56.6) Jun 19 02:06:42.509: SSG-DATA:CEF-FIB_FLAG_RECEIVE=1(Vi3:212.93.193.114->10.200.56.6) Jun 19 02:06:43.313: SSG-DATA:CEF-UP-DefaultNetwork=1(Vi3:212.93.193.114->10.200.56.40) Jun 19 02:06:43.313: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 19 02:06:43.349: SSG-DATA:CEF-UP-DefaultNetwork=1(Vi3:212.93.193.114->10.200.56.40) Jun 19 02:06:43.353: arielle_nrp3# show ssg host 212.93.193.114 ------------------------ HostObject Content ----------------------- Activated: TRUE Interface: Virtual-Access3 User Name: hisham Host IP: 212.93.193.114 Msg IP: 10.200.56.40 (9902) !--- Message server IP & port adddress, and TCP port used. !--- This is configured in the dashboard.conf file. Host DNS IP: 0.0.0.0 Maximum Session Timeout: 0 seconds Host Idle Timeout: 0 seconds Class Attr: NONE User logged on since: 01:54:33.000 UTC Tue Jun 19 2001 User last activity at: 01:54:33.000 UTC Tue Jun 19 2001 Default Service: NONE DNS Default Service: NONE Active Services: NONE AutoService: NONE Subscribed Services: arielle_nrp3#
At this point the user hasn't logged on to any service. The client first sees MiddleEast, Cairo, then Egyptian Capital in the service list on the SSD Web page. After the client clicks Egyptian Capital, the username and password fields appear on the page. No active service has been associated to the client yet. The username and password that the client provides to gain access to cairo.com service must match those that are configured by the L2TP Network Server (LNS). In this setup, LNS is authenticating the users locally. The username is ayman@cairo.com, and the password is ayman.
L2TP Access Concentrator (LAC) Output
arielle_nrp3# show debugging SSG: SSG data path packets debugging is on SSG control path events debugging is on SSG control path packets debugging is on SSG packets debugging is on VPN: L2X protocol events debugging is on L2X data packets debugging is on L2X control packets debugging is on L2TP data sequencing debugging is on Radius protocol debugging is on Jun 19 02:34:48.121: SSG-DATA:CEF-FIB_FLAG_RECEIVE=1(Vi3:212.93.193.114->10.200.56.6) Jun 19 02:34:48.157: SSG-DATA:CEF-FIB_FLAG_RECEIVE=1(Vi3:212.93.193.114->10.200.56.6) Jun 19 02:34:49.681: SSG-DATA:CEF-UP-DefaultNetwork=1(Vi3:212.93.193.114->10.200.56.40) Jun 19 02:34:49.685: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 19 02:34:49.717: SSG-DATA:CEF-UP-DefaultNetwork=1(Vi3:212.93.193.114->10.200.56.40) Jun 19 02:34:49.725: SSG-DATA:CEF-UP-DefaultNetwork=1(Vi3:212.93.193.114->10.200.56.40) Jun 19 02:34:49.725: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 19 02:34:49.777: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 19 02:34:49.777: SSG-CTL-PAK: Received Packet: sIP=10.200.56.40 sPort=37638 dIP=10.200.56.6 dPort=1645 Jun 19 02:34:49.777: header: code=1, id=19, len=102, auth=3F53BB3F2939DAA1E5D9435792491CD3 Jun 19 02:34:49.777: attr: type=1, len=17, val=ayman@cairo.com Jun 19 02:34:49.777: attr: type=2, len=18, val=(89)(C4)/}(BB)(8F) Jun 19 02:34:49.777: attr: type=6, len=6, val=(00)(00)(00)(02) Jun 19 02:34:49.777: attr: type=26, len=23, Jun 19 02:34:49.777: SSG-CTL-EVN: Downloading service profile for service cairo.com. Jun 19 02:34:49.777: RADIUS: ustruct sharecount=1 Jun 19 02:34:49.777: RADIUS: Initial Transmit id 73 10.200.56.16:1645, Access-Request, len 67 Jun 19 02:34:49.777: Attribute 4 6 D45DC301 Jun 19 02:34:49.777: Attribute 61 6 00000000 Jun 19 02:34:49.777: Attribute 1 11 63616972 Jun 19 02:34:49.777: Attribute 2 18 51CF64B7 Jun 19 02:34:49.777: Attribute 6 6 00000005 Jun 19 02:34:49.785: SSG-DATA:CEF-SSGSubBlock=0(Fa0/0/0:0.0.0.0->0.0.0.0) Jun 19 02:34:49.785: RADIUS: Received from id 73 10.200.56.16:1645, Access-Accept, len 275 Jun 19 02:34:49.785: Attribute 6 6 00000005 Jun 19 02:34:49.785: Attribute 26 27 0000000901157670 Jun 19 02:34:49.785: Attribute 26 40 0000000901227670 Jun 19 02:34:49.785: Attribute 26 30 0000000901187670 Jun 19 02:34:49.785: Attribute 26 37 00000009011F7670 Jun 19 02:34:49.789: SSG-CTL-EVN: ##### ssg_l2tp_disc_cause: termCause=1026 Jun 19 02:34:49.789: SSG-CTL-EVN: ssg_l2tp_disc_routine: Jun 19 02:34:49.801: SSG-CTL-EVN: Checking service mode. Jun 19 02:34:49.801: SSG-CTL-EVN: ServiceLogon: Enqueue request of service cairo.com arielle_nrp3# show ssg host 212.93.193.114 ------------------------ HostObject Content ----------------------- Activated: TRUE Interface: Virtual-Access3 User Name: hisham Host IP: 212.93.193.114 Msg IP: 10.200.56.40 (9902) Host DNS IP: 0.0.0.0 Maximum Session Timeout: 0 seconds Host Idle Timeout: 0 seconds Class Attr: NONE User logged on since: 01:54:33.000 UTC Tue Jun 19 2001 User last activity at: 02:34:49.000 UTC Tue Jun 19 2001 Default Service: NONE DNS Default Service: NONE Active Services: cairo.com !--- A service is active. AutoService: NONE Subscribed Services: arielle_nrp3# show ssg service cairo.com ------------------------ ServiceInfo Content ----------------------- Uplink IDB: Name: cairo.com Type: TUNNEL Mode: CONCURRENT Service Session Timeout: 0 seconds Service Idle Timeout: 0 seconds Authentication Type: CHAP Next Hop Gateway Key: cairo.com_key DNS Server(s): TunnelId: nap TunnelPassword: CAIRO HomeGateway Addresses: 15.15.15.5 Included Network Segments: 15.15.15.4/255.255.255.252 Excluded Network Segments: ConnectionCount 1 Full User Name not used Domain List: cairo.com; Active Connections: 1 : RealIP=212.93.197.114, Subscriber=212.93.193.114 ------------------------ End of ServiceInfo Content ----------------
In the output above, RealIP is the IP address given by the service network to user hisham. The subscriber field shows the IP address user hisham was given by the SSG NRP access network.
arielle_nrp3# show ssg connection 212.93.193.114 cairo.com ------------------------ ConnectionObject Content ----------------------- User Name: ayman@cairo.com Owner Host: 212.93.193.114 Associated Service: cairo.com Connection State: 0 (UP) Connection Started since: 02:34:51.000 UTC Tue Jun 19 2001 User last activity at: 02:34:51.000 UTC Tue Jun 19 2001 Connection Real IP: 212.93.197.114 L2TP VIDB: Virtual-Access4 L2TP Session Key: 0 Connection Traffic Statistics: Input Bytes = 0 (HI = 0), Input packets = 0 Output Bytes = 0 (HI = 0), Output packets = 0
LNS Output
ior# show debugging VPN L2X protocol events debugging is on L2X data packets debugging is on L2X control packets debugging is on L2TP data sequencing debugging is on *Jun 18 19:27:09.851 PDT: L2X: Parse AVP 0, len 8, flag 0x8000 (M) *Jun 18 19:27:09.851 PDT: L2X: Parse SCCRQ *Jun 18 19:27:09.851 PDT: L2X: Parse AVP 2, len 8, flag 0x8000 (M) *Jun 18 19:27:09.851 PDT: L2X: Protocol Ver 256 *Jun 18 19:27:09.851 PDT: L2X: Parse AVP 3, len 10, flag 0x8000 (M) *Jun 18 19:27:09.851 PDT: L2X: Framing Cap 0x0 *Jun 18 19:27:09.851 PDT: L2X: Parse AVP 4, len 10, flag 0x8000 (M) *Jun 18 19:27:09.851 PDT: L2X: Bearer Cap 0x0 *Jun 18 19:27:09.855 PDT: L2X: Parse AVP 6, len 8, flag 0x0 *Jun 18 19:27:09.855 PDT: L2X: I SCCRQ, flg TLS, ver 2, len 128, tnl 0, cl 0, ns 0, nr 0 C8 02 00 80 00 00 00 00 00 00 00 00 80 08 00 00 00 00 00 01 80 08 00 00 00 02 01 00 80 0A 00 00 00 03 00 00 00 00 80 0A 00 00 00 04 00 00 00 ... *Jun 18 19:27:09.855 PDT: L2TP: I SCCRQ from nap tnl 13552 *Jun 18 19:27:09.855 PDT: Tnl 4818 L2TP: Got a challenge in SCCRQ, nap *Jun 18 19:27:09.855 PDT: Tnl 4818 L2TP: New tunnel created for remote nap,
Related Information
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
24-Sep-2001 |
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback